Route via L3 switch not working
-
I have a small multi LAN environment with an L3 switch. I'm not able to route via the L3 switch to my pfsense fw but if go direct to the pfsense fw it works.
Here's what doesn't work:
computer0(10.2.0.50) -> switch(10.2.0.2) -> pfsense(10.1.0.1,10.2.0.1) computer1(10.3.0.33) -> switch(10.3.0.2) -> pfsense(10.1.0.1)In this case computer0 has default route 10.2.0.2 and switch has default route of 10.1.0.1. computer1 has default route of 10.3.0.2. switch is the same in both cases.
On computer{0,1} if I "ping 10.1.0.1" or "ping google.com" no packets are received. I can ping 10.{2,3}.0.1 (switch) from computer{0,1} just fine. Multiple computers exhibit the same behavior. OSs vary from Windows 10 to RHEL Linux, etc.
switch can ping 10.1.0.1 and google.com just fine.
If I change default route on computer0 to 10.2.0.1 routing works:
computer(10.2.0.50) -> pfsense(10.2.0.1)The switch is a cisco SG300-28 in L3 mode running latest cisco firmware.
The pfsense is custom x86 pc running latest pfsense. The ports are:
WAN - connects to cable modem LAN_10_1 - Net 10.1.x.x LAN_10_2 - Net 10.2.x.xRules:
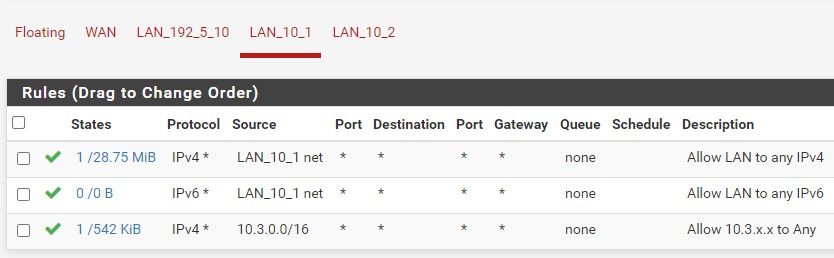
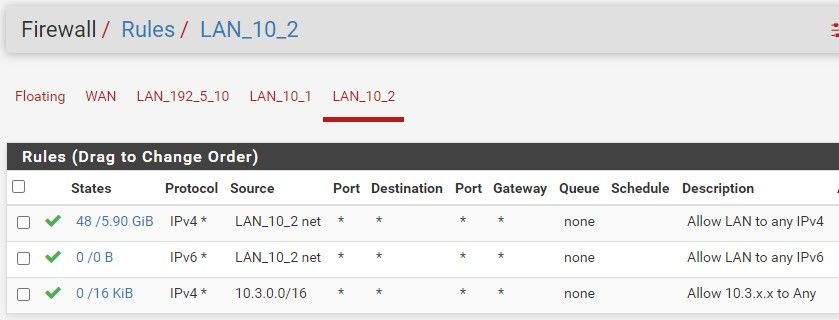
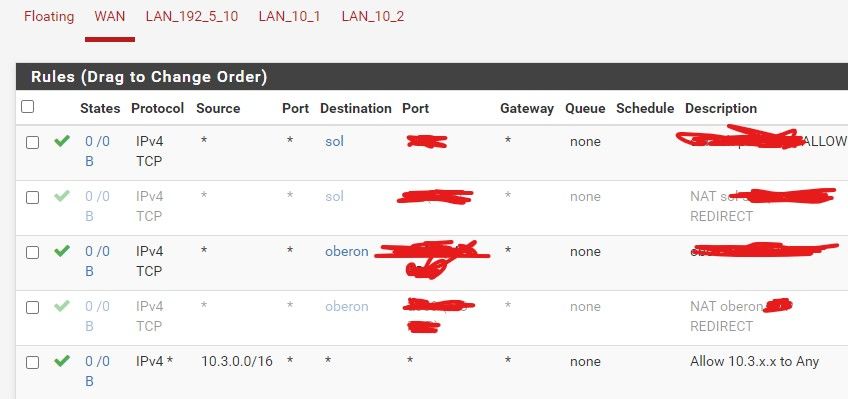
-
Sorry but having a hard time understanding your setup.
If your computer is connected to a downstream L3 switch that is actually routing... Pfsense wouldn't also have that downstream network on any of its interfaces..
A downstream switch would be connected via transit network.
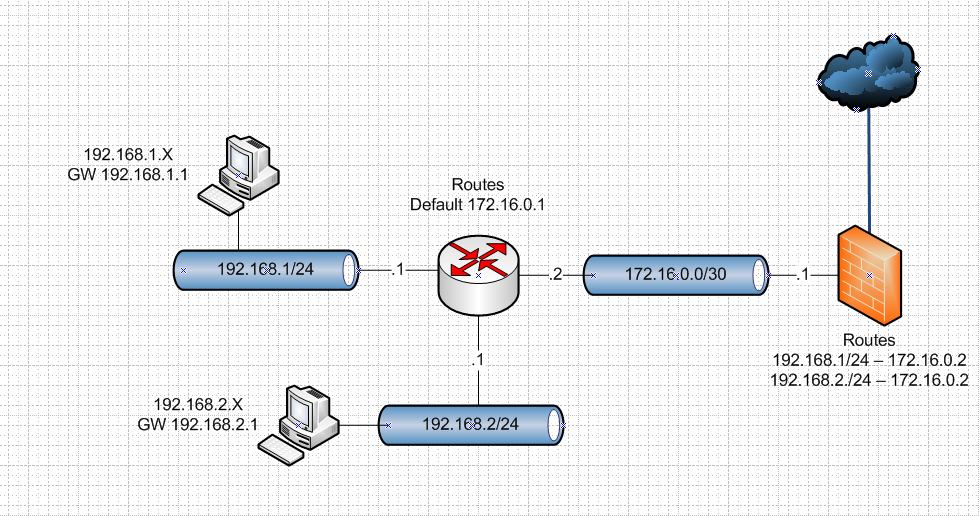
You would need to also setup a gateway on pfsense pointing to 172.16.0.2, and yes on this transit network interface firewall rules you would allow your downstream networks.
Also just because you have your switch in L3 mode doesn't mean it has to route.. I have a sg300-28 as well, and its in L3 mode.. But I only use it L2 connections, it doesn't do any routing. You placing that 10.2 network on pfsense would point to your just wanting to do L2 on your sg300?
Also confused by
10.1.x.x
10.2.x.x
So those using a /16 mask?? Why would you use such a large mask? do you have some 65K devices on these networks?Use a more realistic mask, /24 /23 or hey ok a /22 even... But a /16 isn't a mask that should really ever actually be on interface. It fine for a summary route, or even a firewall rule when you have a lot of downstream networks.. But on an interface it really has no place.. You would never have anything close to 65k devices on the same L2 network.
-
@johnpoz Thank you John! I was able to get things working based on your diagram. You rock!
In my case I needed to setup a transit net and also a static route on the pfsense fw to route to the downstream net via the switch/router. I then needed to add the proper pfsense rules to the LAN interface to allow traffic from each interior network.