Strange routing error
-
Hope someone can help me here. I'm new to pfSense and just trying it out. I am currently using an XG Firewall at home and wanted to run a pfSense alongside it to check into it to see if it fits my needs better (built in Lets Encrypt support is pulling me in....)
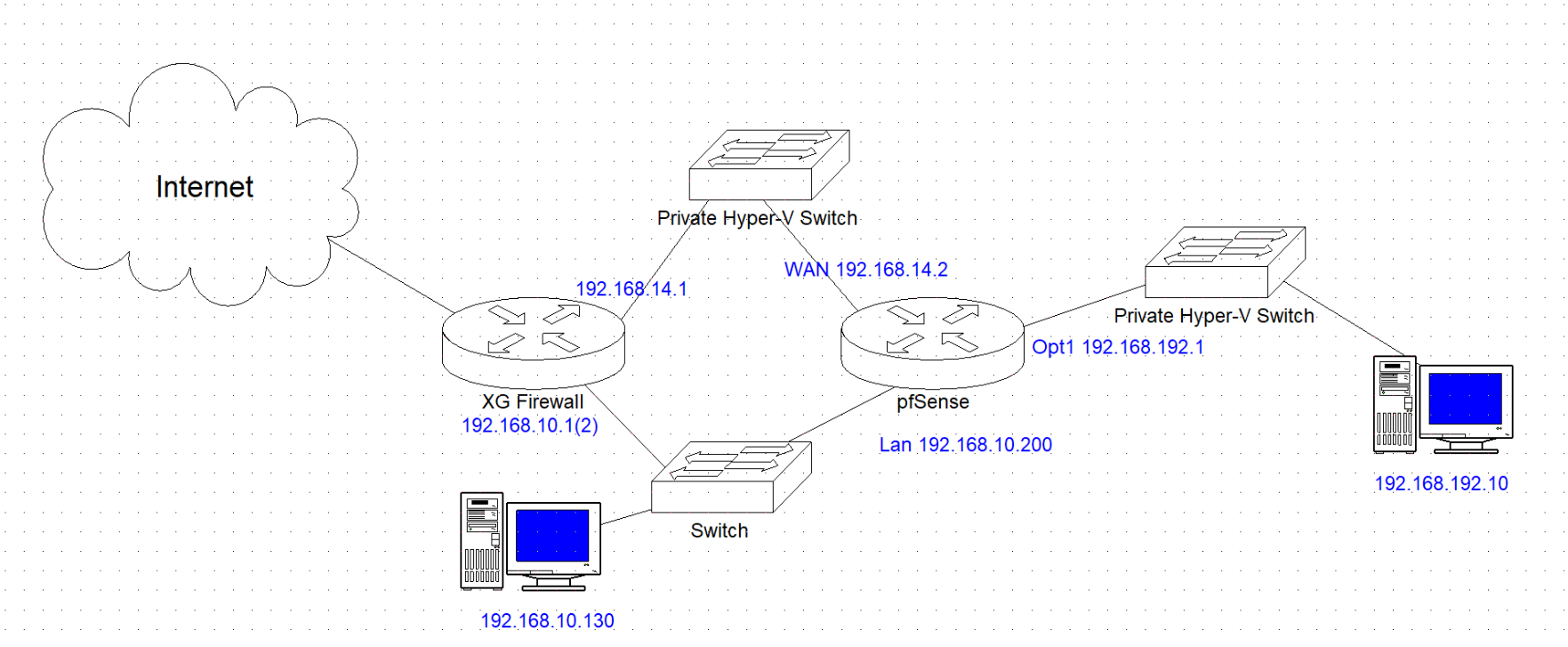
Anyway, I have the setup shown and am getting a strange issue.
I setup a static route on my XG that says 192.168.192.0/24 via 192.168.10.200. This seems to work fine and pings from 192.168.10.x network to the PC at 192.168.192.10 replies as normal.
DHCP is all handled on my normal network (192.168.10.x) with a relay on the pfSense and this works fine too with the static route above on the XG. Likewise, the DNS server is also on the 192.168.10.x network and, that too, works fine from the 192.168.192.10 PC (no DNS forwarding is setup).
However, pings from the 192.168.192.10 PC do not get any reply unless I specifically add a route to the routing table on the target PC (so: route add 192.168.192.0 MASK 255.255.255.0 192.168.10.200). Once I add that, it works fines.. but it pings the other way normally so it knows the route anyway (well ,the XG does...).
Rules on the pfSense are the default Allow ALL lan and a clone on the OPT1 interface. Default auto ANT rules in place.
I simple cannot understand why this setup does not work.
Access to the internet from 192.168.192.10 goes via the 192.168.14.x network and works fine. The pings DO NOT take this route (I have disconnected it and the internet breaks, but the pings still act the same).
Hope people can understand what I trying to do. Does anybody have any idea why this is working like this and what is specifically incorrect?
Note, this is not going to be a final setup, of course, I just wanted to setup the pfSense internally and get a chance to look at it in action.
-
@FillDee said in Strange routing error:
Anyway, I have the setup shown and am getting a strange issue.
Networks are stars.
You made a circle :even experts stay away from such a situation.
Why does the upper left Private Hyper V switch even exist ? remove it, and your network becomes basic == easy to configure.
O are you fast forwarding to some double WAN test bed ?The right "Private Hyper V switch" : what about a switch ?
pfSense :is just an 'ordinary router', as you can find in nearly every home on planet earth right now : basic setup so your WAN and only one local LAN network works takes ..... 5 minutes ?
It's like : define the WAN interface (typically DHCP so the default is ok) - define the LAN interface and accept all the default values. Done. That it.
Because there are a lot of possibilities stashed into pfSense it looks complicated.
It isn't.
See the official Youtube > Netgate videos, they have a lot of videos that explain nearly all the usage cases. -
The upper left switch exists because that is the WAN default gateway for the pfSense (out to the internet via the XG). How can I test it as a firewall properly, if there is no WAN link? (Genuine question)
I just want to test it all without taking down my current XG firewall. I have external rules, a few VLANs and a VPN setup, so that all needs to be put in place before I can switch over to pfSense, so I need to learn it. My internal setup is not a 5 minute setup I'm a fiddler by nature, so I'm fiddling.

I get your circle comment, but, as I said, I've tested the routes and they all seem to go the correct route. I just can't understand why pings to the 192.168.192.x network work, but pings from it to the internal network don't.
For the right switch, both the pfSense and the 192.168.192.10 PC are Hyper-V VMs, so that was the easiest way to connect them.
-
@FillDee said in Strange routing error:
if there is no WAN link?
A router can replace any other router within 5 minutes.
Within 5 minutes it can replace a .... whatever - also your XG.
Running routers in parallel is feasible, but problematic.Another way of testing is : a router, pfSense in this case, it's WAN interface can be hooked up to any existing LAN network. The default DHCP (client) on it's WAN will ask an IP from the upstream DHCP server, probably a router too. As any other device already present in your exting LAN. Just make sure that the LAN network of your upstream router isn't the same as the pfSense LAN , example, if the upstream is 192.168.1.0/24, make the pfSense LAN like 192.168.2.0/24. Now you can hook up a PC (or any other devices) to the LAN of pfSense, and start testing.
-
Thanks for your input.
I guess the 5 minute rule might apply to someone who is skilled in this area. For me, it would take longer just to work out my WAF and SSL VPN rules.
I think see what you're saying here. Basically, change the LAN address to a different subnet that my internal network uses, and break that link. The .14.x network is in the LAN zone of my current firewall, so it passes any traffic that need routing that way. Only Internet traffic using the pfSense as the gateway uses the .14.x network currently. Of course, if the pfSense is then on a network leg with no connection to my current LAN, I would then need rules to allow my current setup to access it, as they would be on the WAN from it's point of view. Not too much of an issue, I guess. My testing procedure would need changing, but I could do that with a new VM.
I was really after the reason why this was happening, as I can't see any reason for it. It's pretty much working as it is, with the exception of the pings.
I'll keep digging...
-
@FillDee said in Strange routing error:
who is skilled in this area
I wasn't counting the preparation of things : watching the official Netgate video's , that presents and explain things at the same time.
Exampe : the "Lets Encrypt" support doesn't really talk about pfSense, but more about DNS, certificates, Lets enscrypt etc.
-
I'll have a watch of those videos at some point. Thanks.