Unable to get to Amazon web site
-
I am hoping someone can point me in the right direction. I am a novice when it comes to networking, having until recently relied on basic home routers (e.g. Asus RT-AC3100), but over the holidays got pfSense up and running.
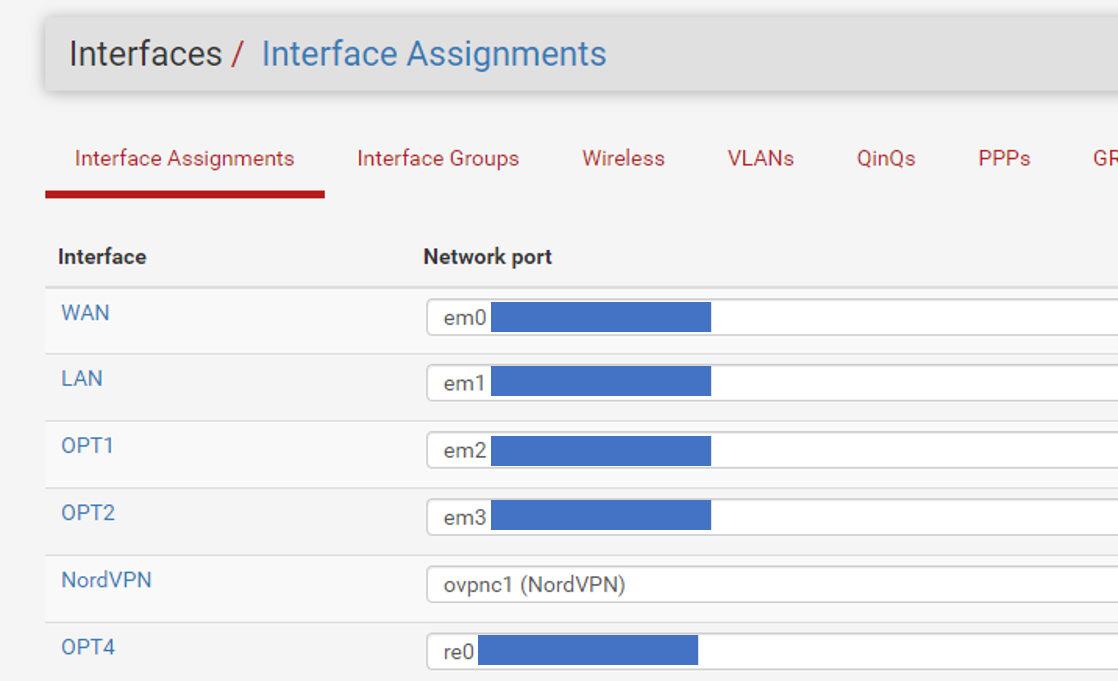
I have a simple set-up with a computer that has 5 NIC's, set up with 4 subnets. When I startup everything works fine, but about 12-24 hours after starting up pfSense i lose the ability to connect to amazon.com! Other web sites work fine; my speed is just where I expect it to be (using Speedtest.net), and accessing a server and printer that are on different sub-nets works fine.
Currently I am fine allowing all traffic between subnets - at a future time I may put in restrictions. Right now my main goal is to set up subnets for different things I do, one for WiFi connections (with various home automation connections); one for the server & printer, HTPC's, gaming and work computers; one for the computer lab where I play around with different things and at some point the last sub-net will be for a web server running on a Raspberry PI.
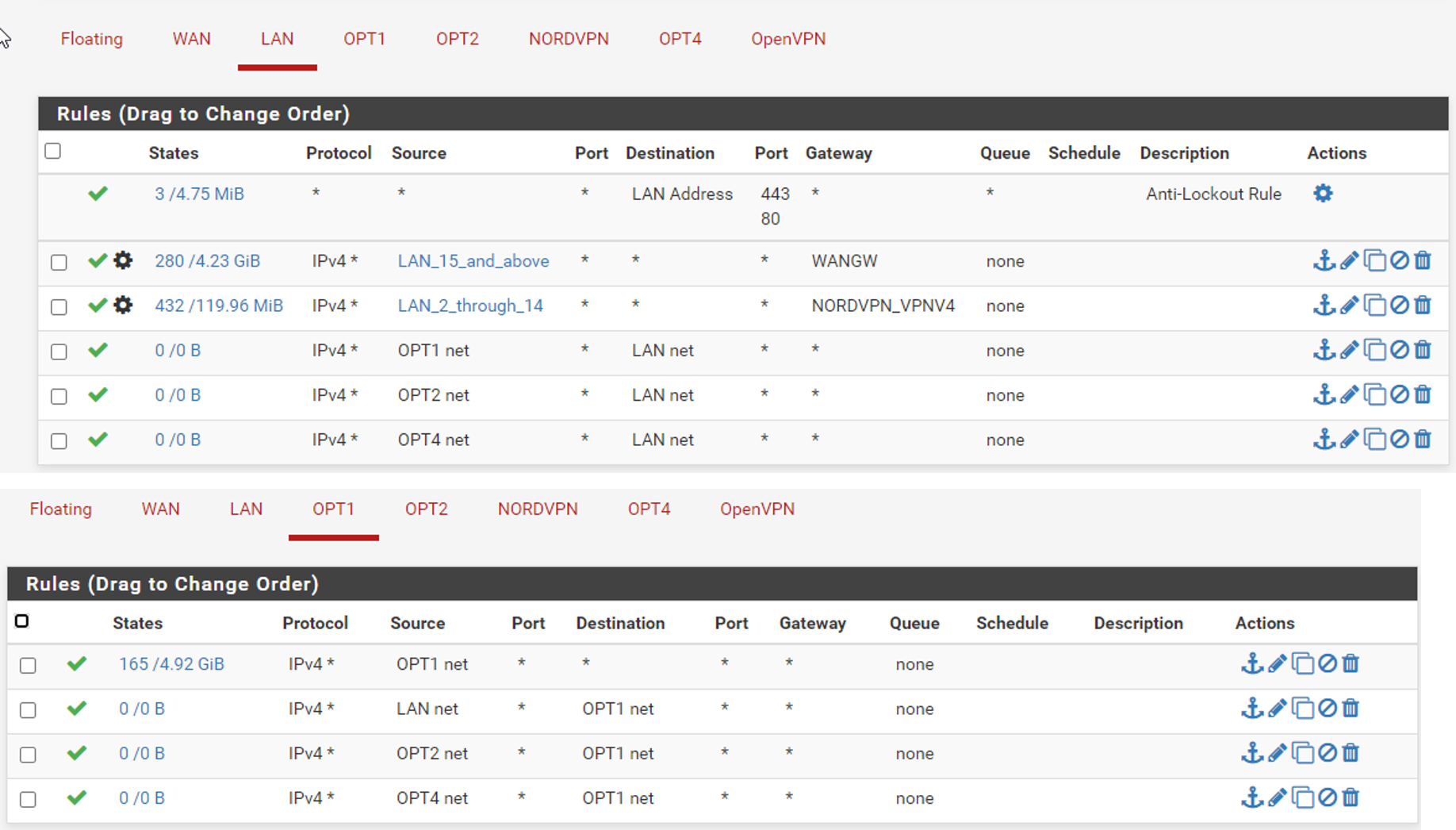
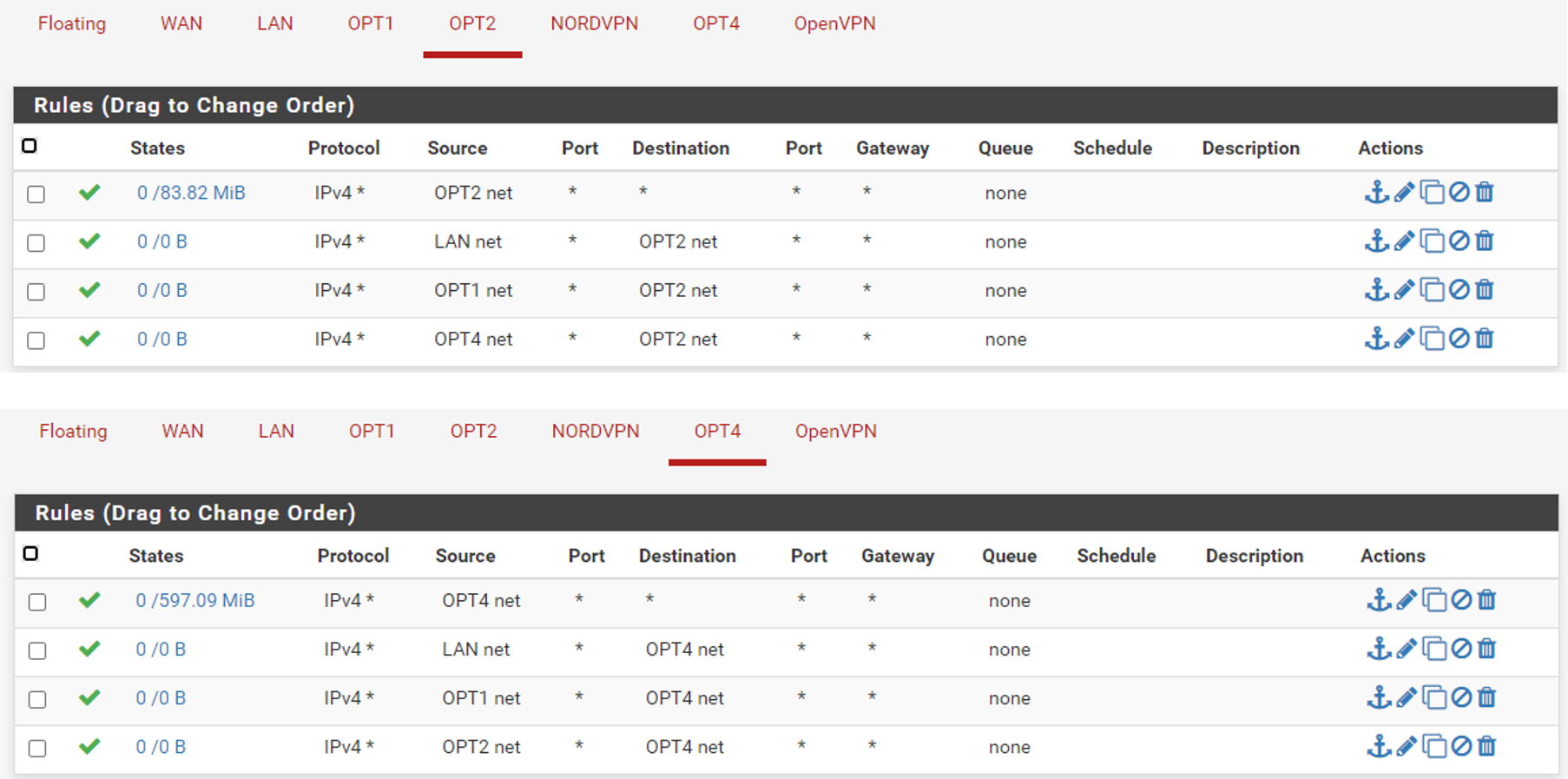
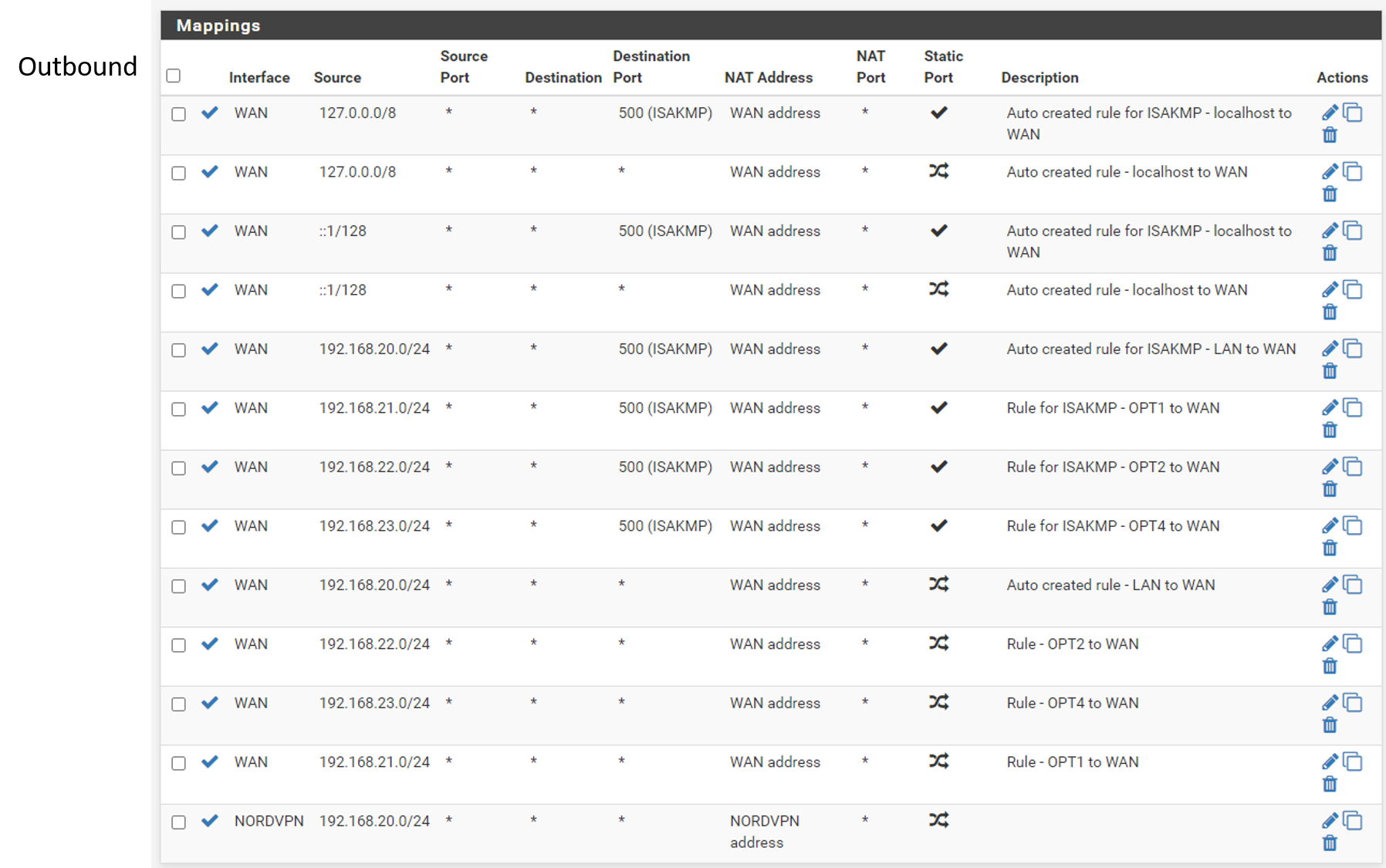
Everything works as intended right now, except for the fact that I lose connection to Amazon. Below I have included screenshots of my Firewall settings. I am wondering if potentially the setup I have for my VPN could create this issue, even though I am not accessing through the VPN? I followed the instructions I found online for setting up the NordVPN, but I have little idea what the settings do.
I appreciate any ideas of guidance where to start looking.
Thanks!!
-
Has nothing to do with whatever your issue is... But why do you have source of your other vlans on the different vlans.
For example how would opt1,2 or 3 ever be the source of traffic entering your LAN interface?
Your rules wouldn't allow traffic from lan to any of your opt networks, because your forcing traffic out either wan or vpn.
When you loose access to amazon - does it still resolve? Can you ping its ip?
-
@johnpoz
Thanks for your feedback.
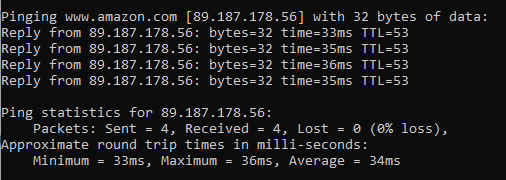
I can still ping amazon! (see below).
As for your first question, I do not have a good answer ... I set up rules best I could based on how I understood things, but I am a neophyte as it relates to networking. I followed some instructions I found online, and thought I got things set up right.
My goal is for each subnet to be able to get out to the Internet, as well as to be able to access resources on each of the subnets (LAN. OPT1, OPT2 and OPT3). Would appreciate your input / recommendations on what I need to change.
-
Well remove those rules... vlan X would never or could never be a source of traffic into vlan Y.
If you want lan to reach opt X network, then you have have a rule that allows that before you force traffic out a gateway.
So for example put a rule above those those rules that allows lan net to opt 1 net, then another that allows lan net to opt 2 net.
Or you could just create a alias that contains the opt networks and do it in one rule.
Well if you can ping amazon, then your getting there.. your problem is not pfsense. Sure you browser not using a proxy, or doh for dns that is failing.. What sort of error do you get in your browser..
With such rules - how do you even talk to pfsense for dns? When your forcing traffic out wan or vpn.. Unless your client is using something other than pfsense for dns - not even sure how you could resolve anything.
You should have a rule above those rules as well that allows your lan net to talk to pfsense for dns tcp/udp 53 lan address
-
@johnpoz
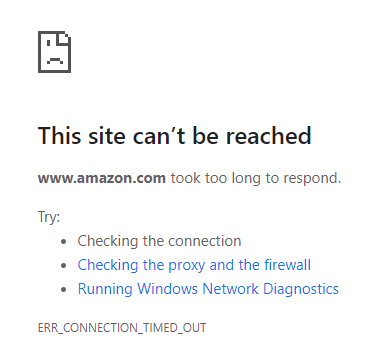
The error I get from Amazon is timeout:
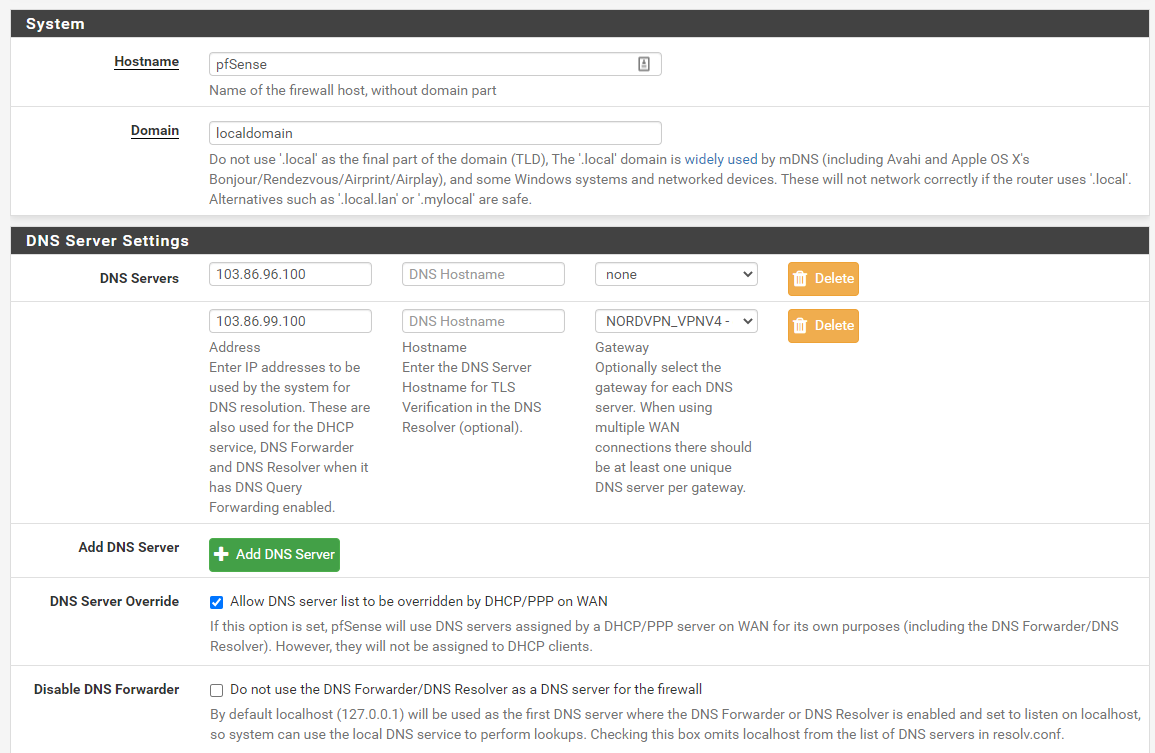
No other DNS anywhere in the network, as far as I can tell.Could the issue be related to settings in the General setup .... when setting up the VPN connection the instructions I followed directed me to make edits in the DNS Server fields - see below:
-
@johnpoz said in Unable to get to Amazon web site:
doh
Concur, disable DNS over HTTPS in your browser and test, or try a browser like IE that doesn't support it. Like he said if ping is working then the connection is fine and DNS is working.
-
@teamits
Just tried disabling DNS over HTTPS, and same result, cannot get to amazon.com. Using MS Edge, same result.In Edge, running Windows Network Diagnostics the identifies the problem as: "resouce (www.amazon.com) is online but isn't responding to connection attempts."
-
@aswede said in Unable to get to Amazon web site:
"resouce (www.amazon.com) is online but isn't responding to connection attempts."
Well are you going through the vpn or not?
Do a traceroute.. Does the path go out your normal wan or your vpn..
Those dns changes are pointless if your just pointing your clients to pfsense.
Your not even letting pfsense use it self for dns - so how do you resolve any of your local resources?
What I would suggest you do is disable all of the vpn stuff.. do you have problems then - I mean unless your isp is going to send the black helicopters to your house when they see you going to amazon.com ;)
Are you using proxy or or ips/ids on pfsense?
-
@johnpoz
I think you are right about the VPN stuff ... my intent was to have a few static IP's that go through the VPN. Most of the traffic, including amazon.com should bypass the VPN .... :)Did the traceroute and got an interesting result ... the first hop was not to the pfsense.localdomain - it was to 10.211.32.1
Then decided to go back to an earlier configuration (that also has the VPN client set up), as this has in the past restored my access to Amazon. Worked this time too, did the tracerroute again, and low and behold, this time pfsense.localdomain is the first hop. We will have to see if it still is working tomorrow ...
So, clearly I have something screwy going on, and I know I am not skilled enough to figure it out. Over the week-end I will do a clean install of pfSense, set up my subnets etc. make sure it all works, and then try to get the VPN up and running.
-
I would make sure your default gateway in System > Routing > Gateways is set the WAN_GW. If it's still set to automatic it may switch the VPN gateway. That would affect all traffic that does not have a gateway set including DNS traffic from the firewall itself if you're still using Unbound in resolving mode.
Steve