Split DNS still loading pfsense instead of server
-
I have pfSense setup to forward
:80and:443from WAN to a device on my LAN. It works fine when I access my WAN IP (or domain name) from outside my home.But if I access it from home, it loads pfSense configuration.
I read https://docs.netgate.com/pfsense/en/latest/nat/reflection.html which said to use Split DNS. So I added a host override for my domain to point to my server IP.
If I ping my external URL from my machine (Windows), it resolves to the IP of my server. But if I try to open it from a browser, it looks like it is trying to load pfSense.
What am I doing wrong?
I know I could change the port that the pfSense UI listens on but I'd rather not do that. I'd rather have it so if I go to my domain.com then it acts just like if I was accessing it from the internet.
-
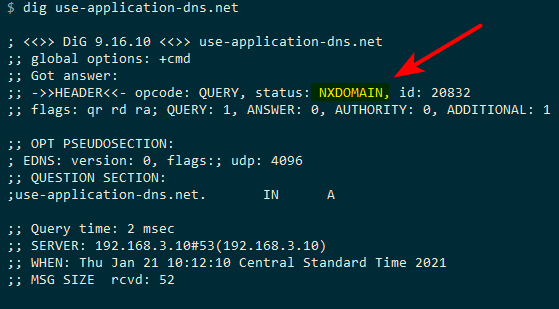
Is your browser using your local dns - or is it set to use doh.. If your using doh, then the browser would not resolve the local IP for your server.
In Mozilla's infinite wisdom and their belief that their users are too stupid to enable doh on their own if that is what they wanted. They have taken upon themselves to make doh the default..
If your not loading the server, even if you can ping it from cmd line and returns your local IP. You need to make sure your browser is using your local dns.
Another thing is browsers cache, so restarting your browser would reset its dns cache.
-
OH. EMM. GEE!
You are right. I confirmed by going to about:networking#dnslookuptool to see what IP Firefox is getting.
Now the question is how to redirect client DoT/DoH back to my pfSense. I am not doing DoT/DoH on pfSense so I don't know if a simple DoT/DoH port forward back to router :53 will work?
I don't want to have to change each client and would rather handle it at the router level.
-
Well that is on Mozilla - they are saying FU to the corp setups.. Here jump through these hoops to stop YOUR clients from using US.. Because you clearly are too stupid to control your own dns ;)
So we are going to have all your users use our dns.
You can set your local dns to respond NX to the canary domain.
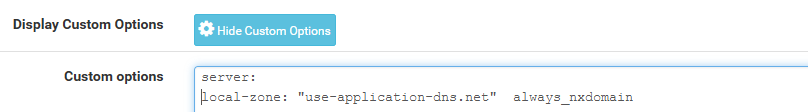
server: local-zone: "use-application-dns.net" always_nxdomainThere actually been quite a few threads around here about the nonsense that is Mozilla and their DOH.. I can feel your pain.. Complain to Mozilla would be my suggestion.
https://support.mozilla.org/en-US/kb/configuring-networks-disable-dns-over-https
I am not a fan of doh or dot.. UNLESS!!! it is explicitly enabled by the user on purpose!! And it should be easy and simple for corps or home setups to block this, en masse - .. DOT is easy, because it uses a specific port that can just be blocked 853... But hiding dns inside a normal https tunnel 443 can be quite difficult to stop actually..
-
@johnpoz Well I got to thinking about other devices/clients using DoT/DoH. What is to stop an IoT device to use DoH.
That setting you shared, where would I put it?
-
That is in the custom options box in resolver (unbound) on pfsense.