Difference between ????
-
@teamits witch one is better when set DNS rules for BIND package
-
It depends on what you're trying to do...does the firewall rule need to apply to just LAN or LAN/WAN/etc.?
-
@teamits I just want hosts on the LAN to resolve with BIND DNS package on pfsense
-
The "this firewall" would normally be used in a block rule... Say you want to make sure that dmz devices can not talk to firewall on any of its IP, like its wan which is normally public.. When you have an any rule for any for internet..
The lan address as destination would be fine for dns.. For your lan clients. Not sure why your including 853 there. Do you have bind doing TLS for your own local clients?? This seems pointless to me.. Who would be sniffing traffic on your lan that it would make sense to encrypt your local dns traffic.
Keep in mind that rules are evaluated top down, first rule to trigger wins, not other rules are evaluated. Would really suggest if you have questions of rules, that you post up the actual rules you have in place on that interface. And any rules you might have on floating.
-
@johnpoz for a floating rule I have only block IPv6 for logging only
Sorry this is off the topic, but I am currently in a loop thinking how to begin
Just question:
I have 2 firewalls on 2 different sites connected via site-to-site openvpn
both have BIND package installed.
they are in the zone
site1 - site1.domain.local - primary server
site2 - site2.domain.local - Secondary server---Primary DNS Settings
IP Version : IPv4 only
Listen on : all of my LAN interfaces without a WAN and loopback
---Primary DNS ACLs
I left All default ACLs
---Primary DNS VIEWS
View Name : internalview
Recursion : YES
match-clients : ANY
allow-recursion : localnets (I am not sure witch one is best for local DNS only)--- Primary DNS Zones:
Question : Should I have domain.local zone at all
P.S. Currently I am giving an example with 1 domain only just to understand the basics of BIND and how to set proper rules on pfsense but in fact I am planning to host more then 1 domainI already set the zone
Domain zone configuration:
Zone Name : site1.domain.local
Zone type : Master
View : internalviewDNSSEC:
Left all default
--- Master Zone Configuration:
P.S Here where my loop begin
Name Server: In this simple case site1.domain.local is going to be for all my hosts on all my interfaces on this firewall so I set it to 127.0.0.1 and Base Domain IP to my LAN interface 192.168.5.2
but.....
If this zone is site2.domain.local witch is on my other site of the VPN how should I setup "Name Server" and "Base Domain IP"
OK ...
allow-update : because is my primary DNS I set to none
allow-query : ANY
allow-transfer : ?????? I need to set and ACL for my Secondary DNS server but witch IP should I include into the ACL the LAN IP of site2.domain.localZone Domain records:
I have added a few records just for testing
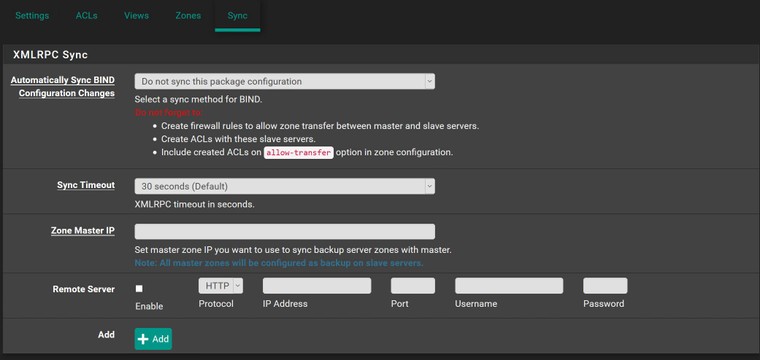
----Sync Tab on BINDAutomatically sync BIND configuration Changes : Sync to configured system backup server
Sync Timeout: Default 30 Seconds
Zone Master IP : ?????????
Remote Server: ????????????Now the rules .....
I have no idea how and where to set the rules so the Secondary DNS server can update!!!!
Here is what it says:
Do not forget to:
Create firewall rules to allow zone transfer between master and slave servers.
Create ACLs with these slave servers.
Include created ACLs on allow-transfer option in zone configuration.??????????????????????????????????????????????????????????????????
Should I add Slave zones on the secondary DNS Server or with this option it will sync automatically and convert them to slave zones
On my VM LAB site witch is site3 I have setup a bind witch host only 1 zone and all working fine but I am tired of adding each host on 3 different sites and when I start adding more domains into my network there where I am going to mess up everything I hope you understand how much I need to learn the basics of bind and then I am sure I can take care of more complicated configuration.
I understand the basic DNS tree in theory, but actually the configurations are little confusing. Most of the articles I find are not GUI related so many configurations on this package, but I don't think I need most of them for my internal network
Thank you
-
@xlameee said in Difference between ????:
site1.domain.local
Sorry I didn't get past .local - you are not actually using that as your tld are you?
-
@johnpoz No this is not my actual domain just an example
-
@johnpoz anyone
-
Horrible example :) if you don't want to give out your tld, then use say .tld ;)
So you want your 2 servers to be slave for the zone in the other NS?
So you have zone site1.domain.tld on NS1, and you want NS2 to be slave to this.
And then for site2.domain.tld on NS2, you want NS1 to slave this?
Or you want NS1 to be SOA for both zones and slave them to NS2?
Maybe I need more coffee, let me have some and then will reread your post..
-
@johnpoz hello
I have 2 pfsense with bind connected via site to site openvpn :)
I need my site 1 to be the master and site 2 to be the secondary
I need site 1 to have all the zones on site 1 and site 2 as master zones
The point is to add hosts only on site 1 witch is the master and those entry to be synced to site 2 so I don't have to enter them on site 2 also to be able to resolve them there as well. Like the build in resolver on pfsense (if I want to resolve host on site witch is actually host on site 2 I have to put entry into the resolver on site 1) Right.
:)
and ... the rules witch are confusing me
What rules should I set so both sites can sync with this function or in any other way