1:1 NAT / Firewall Rules Conflict?
-
Hi,
First - I'm not sure where to post this - if it's a NAT issue, Firewall issue, or totally unrelated! Some IPs changed to protect the innocent!

I have a relatively complicated setup, on an SG-3100. I've used VLANs and switch port VIDs on the firewall to separate traffic to/from different networks:
WAN2: 11.22.33.232/29 subnet
WAN1: /32 static IP (DHCP)
LAN: 192.168.4.0/24
GUEST (VLAN tag 10 on LAN): 192.168.40.0/24
DMZ (VLAN tag 400 on LAN): 10.0.42.0/24LAN and GUEST networks use a failover gateway group for all outbound traffic, via WAN1 and WAN2.
Inbound NAT rules are configured on both WAN1 and WAN2 for some services I run on the LAN (e.g. Slingbox, ResilioSync, CloudStation on my Synology NAS, etc) - typically enabled for a small set of source IP(s).
The DMZ currently has a single host in the subnet, and a 1:1 NAT on a VIP of WAN1 is supposed to route traffic to it.
So:
- 11.2233.237 is pfSense gateway IP for WAN1 (and outbound NAT rule for traffic originating on LAN or GUEST networks)
- 11.22.33.236 (WAN1) --> 1:1 NAT --> 10.0.42.236 (DMZ)
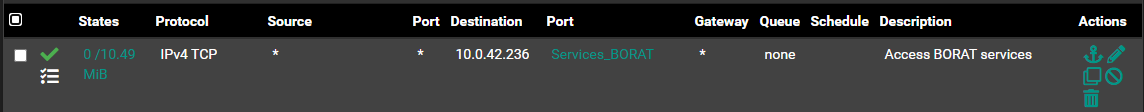
Via firewall rules, DMZ can't access any services in LAN or GUEST networks (but can access everything outbound on WAN1). Certain services are allowed to connect to DMZ IP on WAN1. GUEST can access specific IPs/ports on LAN, and everything else outbound on WAN1/WAN2.
Not shown here are some IPSec and OpenVPN (both client and server) connections I have.
I recently went through a bit of a kerfuffle when I recently upgraded from 2.4.5 to 21.02.x (and subsequently to 21.02-p1 and then 21.02.2-RC to fix problems with DNS resolver and pfBlockerNG), and since then inbound traffic to the DMZ via the 11.22.33.236 WAN1 IP is being blocked outbound by the default WAN1 rule.
Any DMZ-to-WAN traffic that's initiated on the DMZ server works fine, and resolves as being sourced from the correct IP, for instance:
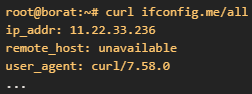
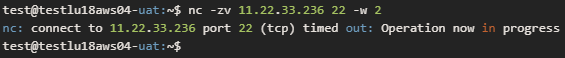
However, when I try to connect to the DMZ public IP from the outside, although I see traffic reaching the DMZ host (via tcpdump), and responses going out, the firewall seems to be blocking those responses?
Remote host:
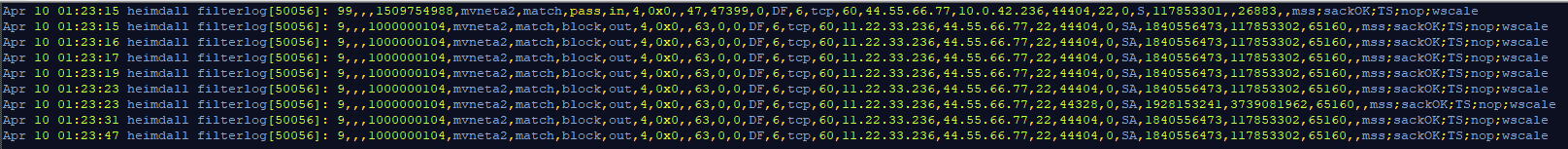
SG-3100 firewall logs (filtered)
DMZ host (tcpdump, filtered):
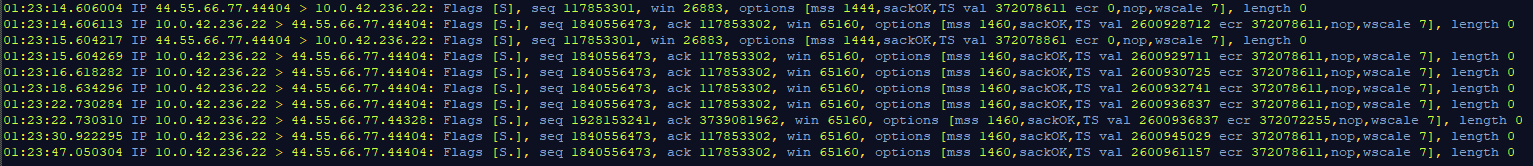
The first "pass" rule (on interface mvneta2 - WAN1),
1509754988:
As far as I can tell, rule
1000000104is the "default deny" rule. Adding an explicit rule on WAN1 interface to allow all traffic from 11.22.33.236 outbound has done nothing.I have tried a few other things, like switching from 1:1 NAT to port forward, but that completely messed up other things which forced me to revert back.
I should stress - everything worked fine prior to the upgrade, and I'm not sure if I inadvertently broke something while trying to fix/troubleshoot issues introduced by the upgrade, or it's a new bug in the upgraded software itself.
Unfortunately when I performed the upgrade I realised too late that I don't have a recent backup of my full configuration, and the limited auto-backup configurations I had saved with Netgate had already overwritten the last known working 2.4.x config
 ... so reverting back is no longer an option, and neither is starting from scratch, as I fear I'll end up with more broken things just to fix one problem!
... so reverting back is no longer an option, and neither is starting from scratch, as I fear I'll end up with more broken things just to fix one problem!Any assistance/guidance would be appreciated!
-MR
-
If anyone has had this issue - updating to the release version of 21.02.2 seems to have fixed it! I think it's related to this reported ticket: Regression #11436
Will report back if I see any further related glitches.