@ PFSNSE
-
Hi techs,
I got 2 PFSENSE appliance testing, PFSENSE1 has internet from my isp modem and PFSENSE2 connect to the internet through PFSENSE1
PFSENSE1 WAN ip: 61.15.15.20
PFSENSE1 LAN IP: 192.168.100.1PFSENSE2 WAN IP: 192.168.100.2 GW 192.168.100.1
pfsense2LAN ip: 192.168.200.1I can get internet from pfsense2 through, I would like to allow a server connected from pfsense 2 access from the wan on pfsense1
I appreciate any advice o recommendation
Thank you -
So your server say on 192.168.200.X
So forward whatever port Y on pfsense1 to 192.168.100.2
Then on pfsense 2, forward port Y to 192.168.200.X
-
-
There are many many users behind double nat.. While its not optimal, and can be problematic for some protocols.
Normally it is not a problem..
With any port forwarding be it through single nat, double nat or even triple+ etc. Troubleshooting is exactly the same.
First step is just validate your traffic is even hitting your public wan.. Then validate your forward on your edge is sending to your 2nd router.. Simple packet capture and use of say can you see me . org should take you like 30 seconds to figure out where your problem is.
Your not trying to test this from inside your own network are you?
https://docs.netgate.com/pfsense/en/latest/troubleshooting/nat.html
https://docs.netgate.com/pfsense/en/latest/troubleshooting/nat-port-forwards.html -
Thanks for your prompt response. I am not testing from inside my network. I will remove all rule and retry.
-
First step I would do, before you even do any rules is just test that whatever port your trying to forward is seen on your public wan via test with can you see me . org and packet capture..
No ports required to be open even to validate you can see the traffic at your edge..
example.. Say you wanted to forward 4444 (just some random port out of thin air)
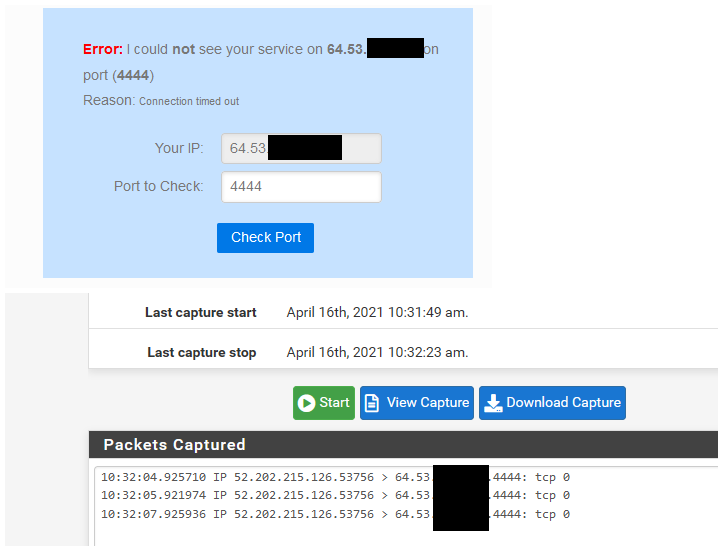
Now I know my wan sees traffic to that port.. Then do your forward to second pfsense wan port.. Do sniff on its wan.. Do you see the traffic?
For me there is zero point in doing anything until you first validate traffic actually gets to pfsense wan.. Since if its not - you can not forward what it never sees.
I take it your wanting to forward some tcp port.. UDP can be problematic to test, not an issue sniffing.. But many of the online sites like can you see me . org don't allow for testing udp... So you need some other way to generate the udp traffic to the port your wanting to use.
-
@johnpoz
I recreated the Nat rule i was successful in getting this to work, currently monitoring the connection.Thanks for your effort, Thanks