IPSEC internet conection by tunnel
-
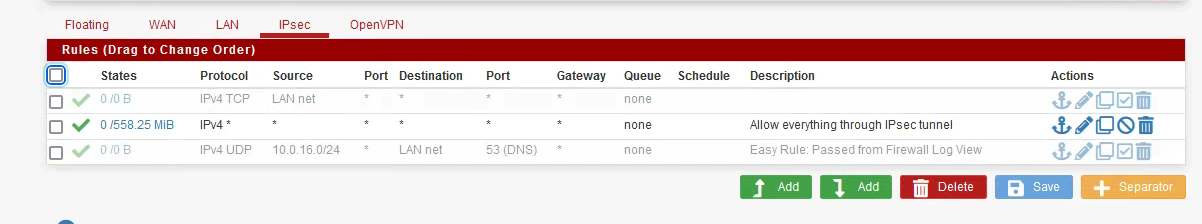
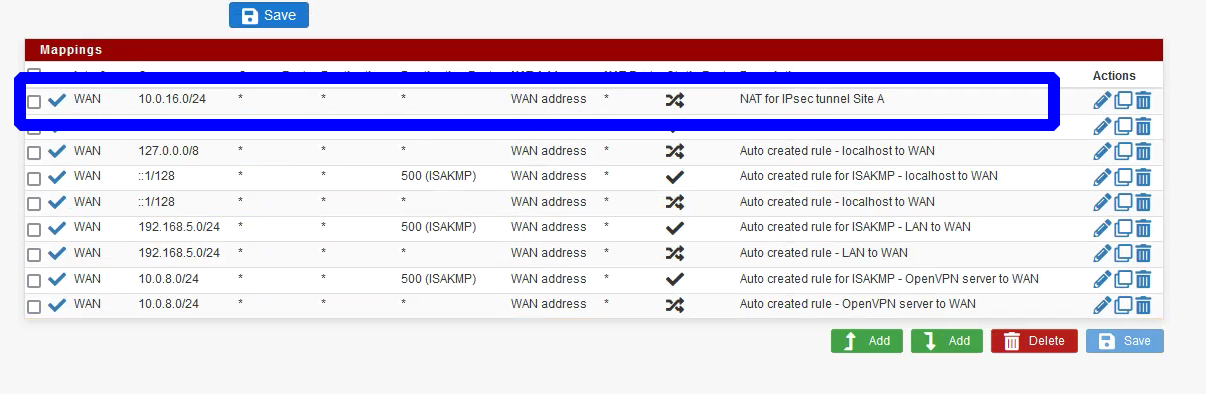
@atreyumu I’ve followed those instructions few times and it’s always worked for me. Did you create an outbound NAT rule on the B side for side A IP subnet? In your P2 settings did you set site A remote network to 0.0.0.0/0 and site B local network to 0.0.0.0/0. To further troubleshoot, will need you to post screenshots of your P1 and P2 settings for both sides, as well as firewall rules and NAT rules on side B through which the internet is supposed to be accessed.
-
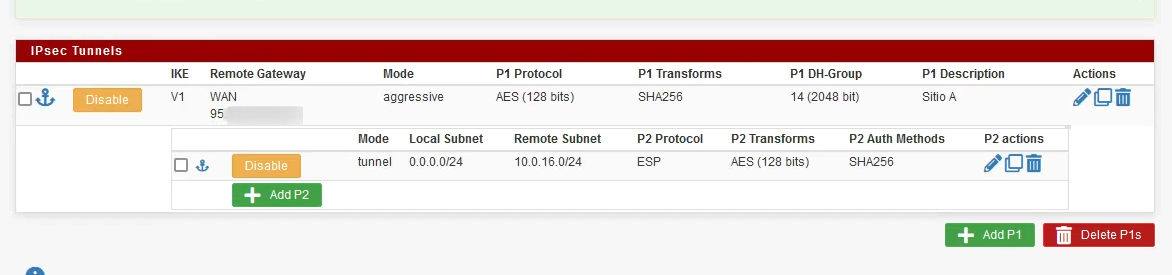
@gabacho4
Site A
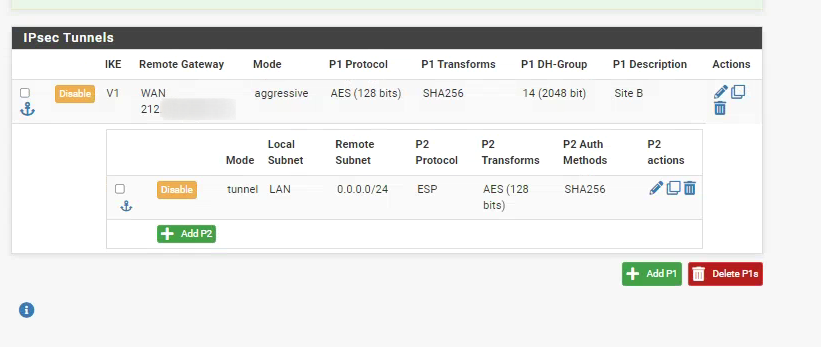
Site B
-
@atreyumu ok so right away, it should be 0.0.0.0/0 not 0.0.0.0/24. Change that. Need to see the firewall rule for side A as well. Everything else looks good. You can get getter performance using GCM ciphers btw but that’s an optimization thing more than an actual connectivity issue. Make the change to 0.0.0.0/0 in both sides and make sure the firewall rule for A and B sides is a permit all and things should connect based on what I see.
-
@gabacho4 Thank you!!
It worked!!!
With this configuration, would it be possible to connect Site A computers to a Site B Windows domain? -
@atreyumu that’s something I personally haven’t tried but I would guess it should be doable?? I did find the following thread which indicates you should be able to.
https://forum.netgate.com/topic/110066/site-to-site-vpn-works-but-can-t-join-domain-on-other-side
Can’t recommend a good Google search enough for a lot of things as you are most definitely not the first to want to try something new.
Perhaps there is someone smarter than me on that particular matter who can provide more details.
-
@gabacho4 Thanks so much. Iĺl looking more info about this.
-
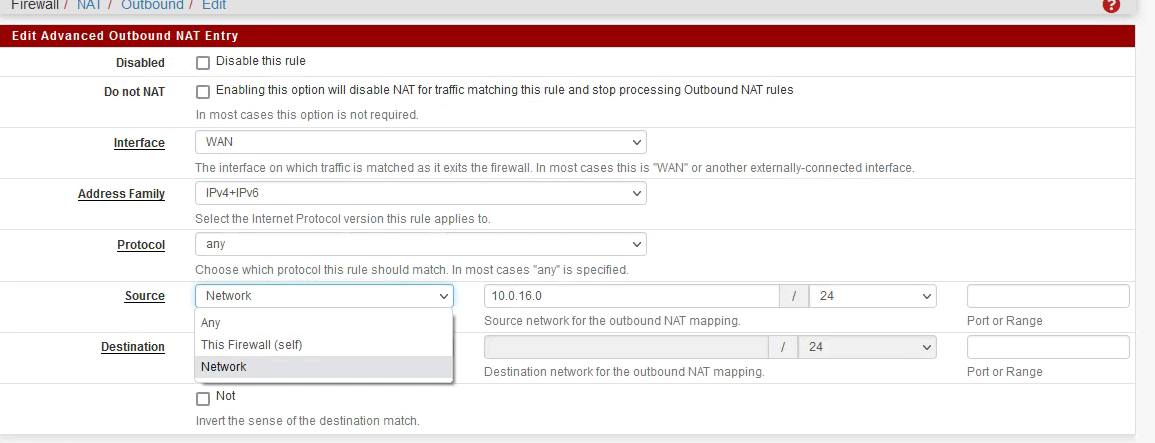
@atreyumu Hi. If I wanted only one host on the LAN to go to the internet through the tunnel, should I only switch outbound
-
@atreyumu believe you’d create a firewall rule that would allow the desired IP through but nothing else. The key with IPSec is that access is controlled by the firewall rules on the other side. So if you want a side A device to pass through side B, the firewall rule to permit that is created on side B.
Edit: my rule would be something like “deny all if source !<desired side A IP> to any destination”
Edit 2: rereading your post, I may have misunderstood. If all you want is the one IP to have internet access, but all other IPs to transit the IPSec connection, then yes, just change your outbound NAT rule to reflect the specific IP instead of the whole subnet.
-
@gabacho4 the problem is that it does not let me indicate only a host, if not a network
-
@atreyumu interesting. I wonder if it works if you leave it as network but then put in the device IP address with a /32. Basically you’re saying let out this network of 1 device. I’d have to dig around a bit if that doesn’t work. @jimp seems to be the IPSec guru on the Netgate side but can’t speak to his availability/interest in commenting. He keeps himself busy from what I see.