Certificate problems with HTTPS traffic
-
Hi all,
I just installed the latest pfSense (using pfSense-CE-2.5.2-RELEASE-amd64.iso), and set up amongst others outgoing HTTPS connections.
Now, no matter what kind of HTTPS traffic I generate, I get certificate errors.
Two examples:apt update wget https://google.beIt's like pfSense replaces the certificates. I have no packages installed.
What could be the cause of this?Cheers,
BC
-
@bcnx Are the hostnames resolving to the correct IP? I mean, if there was a proxy of some sort then the proxy would be receiving the connection. Otherwise the client device should connect through pfSense. Any NAT rules intercepting traffic? Can you tell from the certificate presented where it is connecting?
-
For the apt command the IPs seem correct. Not sure how they could be incorrect?
I don't use any proxy presently.
I do use SNAT rules, not sure about NAT rules that intercept anything, what do you mean by that?
My client is a Debian install without desktop, so I cannot look at certificates in a browser.
I did find this page: https://serverfault.com/questions/139728/how-to-download-the-ssl-certificate-from-a-website, allowing to download a certificate with openssl. I will try that tomorrow,BC
-
I connected a Windows 10 VM to the pfSense and when browsing to https://google.be I get a warning about the certificate. While investigating the certificate it becomes clear that the original Google certificate was replaced by pfSense.
I'm not sure why this happens and also how to disable it.Any tips are welcome,
BC
-
@bcnx said in Certificate problems with HTTPS traffic:
clear that the original Google certificate was replaced by pfSense.
Pfsense can not do that unless you tell it too - did yo setup some port forward? To redirect traffic to the pfsense IP?
I have no packages installed.
Then there is no way pfsense would do this - without a port forward stating send https (443) to pfsense IP.. Please post screenshot of your port forwards.
Or for whatever reason your resolving where your trying to go to the pfsense IP.
-
Cheers for your answer!
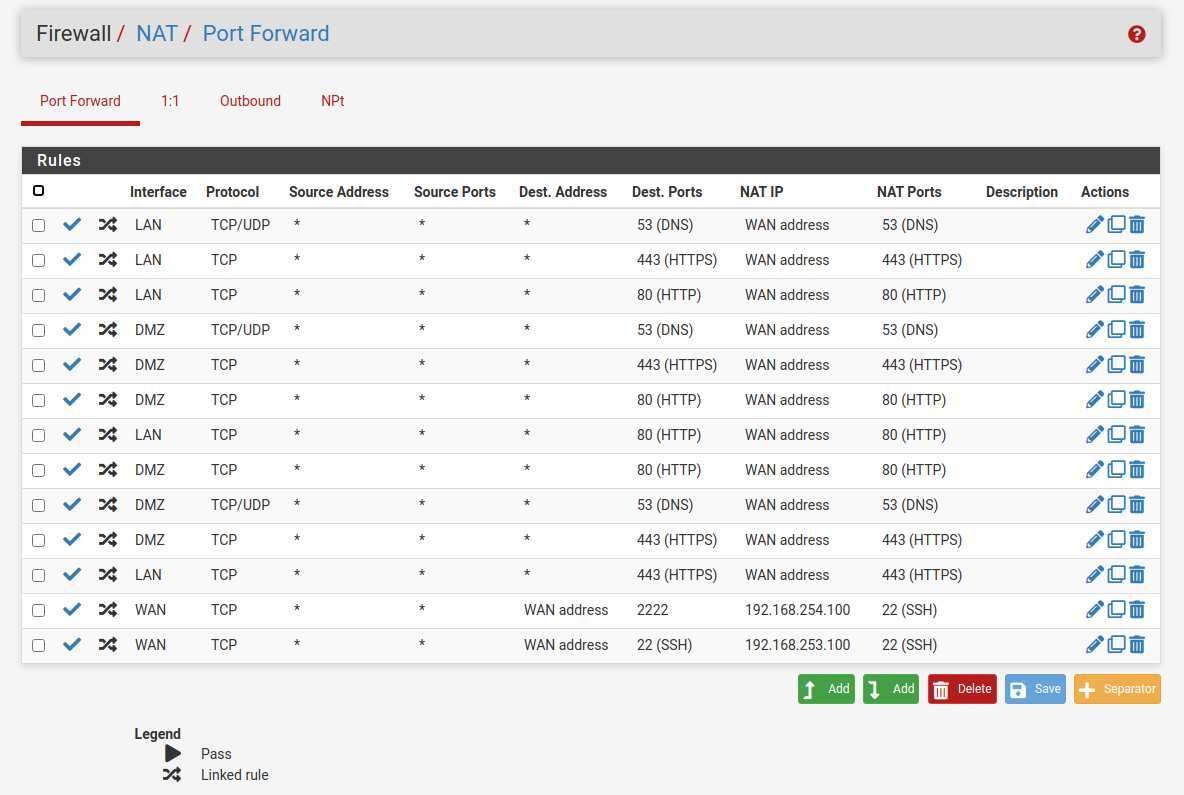
I configured NAT from LAN to Any for port HTTPS and had pfSense automatically create the corresponding firewall rule. Port forwarding, as I understand it, forwards traffic to a certain port from WAN to LAN. I'm not doing that for HTTPS.Here's the screenshot for my LAN NAT config:
Did I configure my source NAT wrongly?
Cheers,
BC
-
Why would you do that?? There is ZERO reason to do that - delete ALL of those
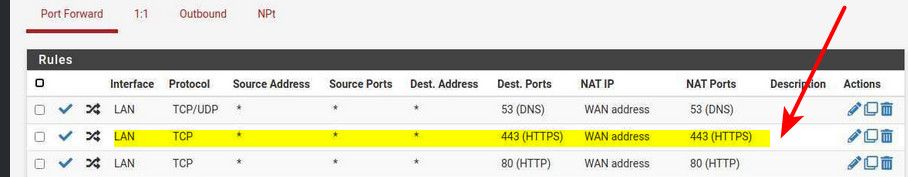
This is the specific rule that would be doing what your seeing. You have zero reason to do any port forwards like that.. Your sending all your traffic to pfsense wan.. Nothing would work!
For stuff to get to the internet - outbound nat is what is used, and it would auto be setup.. You shouldn't have to touch it.
-
I think I created the source NAT-ing in the wrong place. I did it on NAT/Port Forward, but shouldn't it be on the Outgoing tab?
Cheers,
BC
-
No port forwarding is where you would do port fowarding (redirection) - but none of those make any sense
Out of the box pfsense would nat your lan traffic to the internet to wan IP. Via outbound nat
-
so it seems we are posting over each other and now I'm a bit confused: to be able to go from LAN to the internet, should I use the Port Forward tab or the Outgoing tab?
If it is the Outgoing tab, should that be automatically configured? This is what I have now: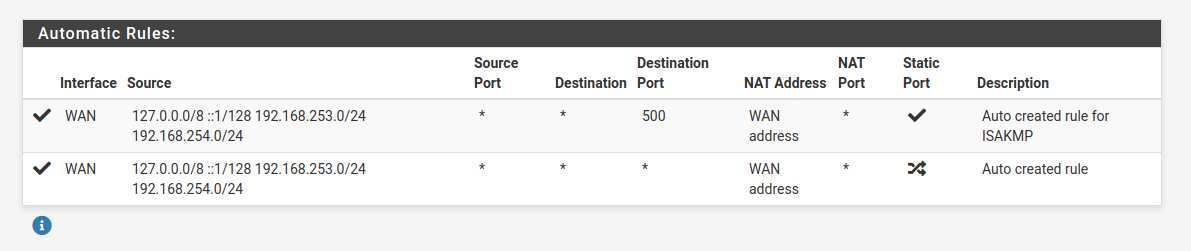
cheers!
BC
-
@bcnx said in Certificate problems with HTTPS traffic:
to be able to go from LAN to the internet, should I use the Port Forward tab
No - those nats would be done on the outbound tab - but you shouldn't have to touch it. Out of the box auto would nat anything from lan to your wan IP.
delete all those port forwards you setup.. Other than those ssh ones you might want - those forward traffic from internet to your stuff on 192.168.x.100
what are you trying to source nat? That is not a common thing to do - and only really needed to circumvent a local devices firewall, that doesn't allow access from other IP ranges other than its local network. Or to talk to a device that has no gateway setup.
Traffic to the internet from your lan to the internet will be auto "source" natted to look like it came from your public wan IP out of the box with the auto outbound nat rules.
-
So I deleted the port forwarding rules and host in the LAN are working fine now. Those from my DMZ network still don't but I suppose no automatic outbound NAT configs were created? And so I need to create those manually?
Cheers,
BC
-
@bcnx sure looks like they were I see 192.168.253 and 192.168.254 listed there. Did you put any rules on your dmz interface to allow traffic?
Out of the box lan would have an any any rule - but new interfaces would have no rules..
Pfsense will auto create outbound nat for any interface you bring up - but rules would not be there until you create them.. Only the lan interface gets the default any any rule to start with.
-
Thanks to your advice I was able to get things working, thanks a lot for that!
I'm familiar with Sophos and Fortigate firewalls, but this one has its particularities, but I'm happy to learn about them.
Cheers,
BC
-
@bcnx Glad you got it sorted.. Here all the time if you have questions - happy to help!