prevent forwarding of non public suffix domains
-
I use NextDNS as my upstream DNS provider and I've noticed in my logs on their service that some non-public suffix domain entries end up being forwarded to them. Is there a way to block any invalid public suffix'd name lookups from escaping my network?
I'm thinking there could be a situation where sensitive name lookups could be leaked out to a public resolver.
-
https://www.theregister.com/2018/02/12/icann_corp_home_mail_gtlds/
I have lookups from my pfsense box > NextDNS upstream for
app.adjust.com.home
app-measurement.com.home
beacons.gcp.gvt2.com.home
beacons.gvt2.com.home
beacons3.gvt2.com.home
cloud1.linksyssmartwifi.com.home
connectivitycheck.gstatic.com.home
device-api.urbanairship.com.home
firebase-settings.crashlytics.com.home
juke.api.247e.com.home
mads.amazon-adsystem.com.home
manifest.localytics.com.home
profile.localytics.com.home
s.amazon-adsystem.com.home
ssl.google-analytics.com.home
www.google.com.home
www.gstatic.com.home -
@jawz101 so clients quite often will add their local suffix to something they are looking up.
There are some things you could do on the client to stop that.. Stop using suffix searches..
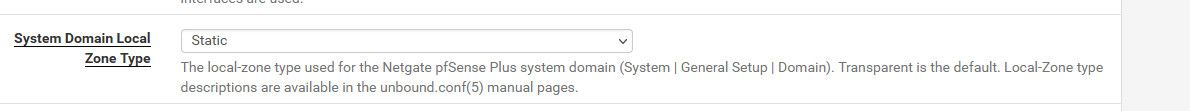
But simple solution if unbound is asking for stuff in your local domain upstream, that you don't want it too.. Is change your type from transparent to static..
In the resolver gui
https://nlnetlabs.nl/documentation/unbound/unbound.conf/
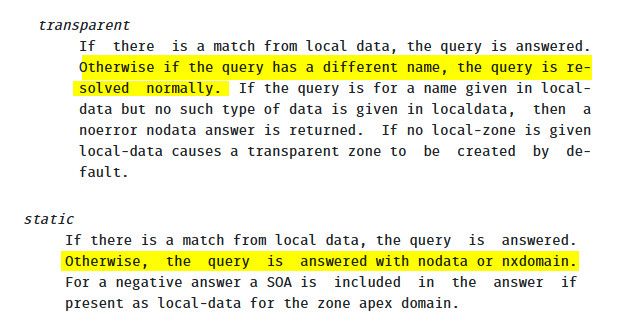
When a client asks for something.home, and there is no local record for that for example www.google.com.home with transparent unbound will try to resolve that.
With static since unbound has local resources for .home - and if there is no www.google.com.home - then you would get back a nx and nothing would be asked upstream.
on a side note, use of single label is normally a bad idea.. use maybe network.home or the new recommended local domain is home.arpa as your local domain.
https://datatracker.ietf.org/doc/html/rfc8375
Special-Use Domain 'home.arpa.' -
@johnpoz thanks! I've noticed it a bit too when sifting through Cisco's Umbrella top 1million lists.
I think I'd not want to forward anything that isn't a public suffix'd record regardless of whatever suffix used for my internal network.
-
@jawz101 well you could create blocks for all non public tlds that you would like to block - but what on your network would be looking for those, if wasn't in your search suffix..
The possibilities are pretty infinite for non actual tlds ;) But only those in your search suffix would be added by clients.