Wireless with VLAN not allowing traffic
-
@dridhas yeah it doesn't work that way.. There is nothing in pfsense that would say hey lets block this site because this interface is tagged vs untagged.
Not saying your not having issues, just that there is a piece of the puzzle missing because tagged vs untagged has zero to do with the problem.
-
@johnpoz seems to be that the main issue is with the VLANs rather than pfsense.
-
@dridhas well again if your vlans were broken - they would be broken.. Not sure how it could work at all for example..
The vlan being tagged or not tagged has nothing to do with website x working while website y doesn't
-
@johnpoz yup, confirmed... if VLAN is enabled on the WAP and the single port, the traffic flows normally.
If VLAN is enabled on WAP, the port where the WAP is connected on the switch with TAG and the uplink port with TAG, some sites are inaccessible (i.e uber and duckduckgo)
-
@dridhas said in Wireless with VLAN not allowing traffic:
switch with TAG and the uplink port with TAG, some sites are inaccessible
Your going to have to show what your doing.. But again vlan being tagged or not taqged has ZERO to do with some website working or not working..
I am on tagged vlan on my phone and those websites work just fine..
-
@johnpoz this is my setup:
WAP:
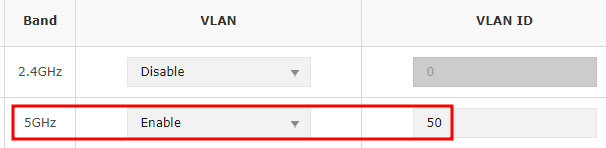
Switch:
With this setup, wifi works normally with correct subnet (x.x.50.x), duckduckgo times out.
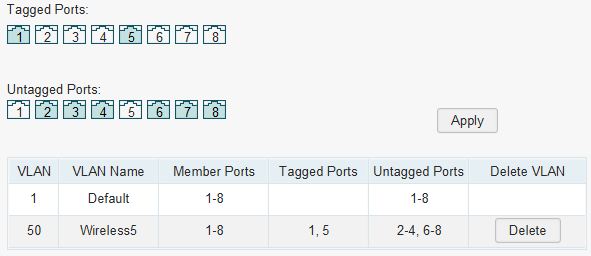
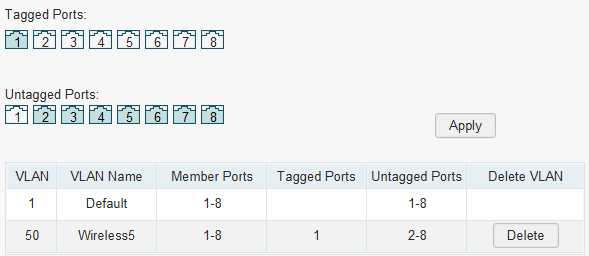
and with the below setup on the switch, duckduckgo works normally, but it does not reach the correct subnet (x.x.50.x) as it goes to the default vlan (x.x.20.x)
-
@dridhas What is plugged into what exactly?
And what are you changing on pfsense.. You can not just send tagged or untagged traffic to an interface in pfsense x.x.50.x or x.x.20.x those are different interfaces, etc.
Flipping something back and forth between networks could have issues.. But again going to say this 1 last time.. Be it your network tagged or not tagged has ZERO to do with pfsense blocking it.. ZERO!! Pfsense either sees the traffic via the tag or it doesn't It doesn't say oh traffic tagged block uber.com
But doesn't look like to me your changing anything on pfsense.. And x.x.50.x and x.x.20.x sure an the hell not the same interface, etc.
edit: one thing that SCREAMS BORKED is this
You can not run multiple vlans untagged on the same interface - its borked!!
If your going to run an untagged vlan be it 1 or 50.. You can not also have the other vlan on that port also untagged.. If your going to put something in vlan 50 untagged, then vlan 1 needs to be removed from that port. if your going to run something untagged on vlan 1, then you can not also have vlan 50 on that port untagged.
You can only run 1 untagged vlan on a port at a time.. While sure you can run multiple layer 3 on the same layer 2 - its BORKED and sure you could have all kinds of odd things happening.
-
@johnpoz im getting a bit confused now...
is it supposed to run them untagged?
if i use the tag i get the WAP to get to the correct subnet, otherwise it goes to the default lan -
@johnpoz said in Wireless with VLAN not allowing traffic:
@dridhas What is plugged into what exactly?
WAN to pfsense machine
pfsense machine to port 6 on the switch (LAN)
WAP is plugged in to port 1 on the switch.And what are you changing on pfsense.. You can not just send tagged or untagged traffic to an interface in pfsense x.x.50.x or x.x.20.x those are different interfaces, etc.
im not changing anything on pfsense... all changes are being made on WAP/Switch
-
@dridhas going to need to see the setup in pfSense for VLAN interface assignments. Which interface is trunk to switch?
Port 6 of switch is setup as a trunk?
-
@ahking19 so, the LAN cable from pfsense is going to port 5, not 6 (my bad).
WAP is connected to poe port 1 -
Since you have the 5GHz AP tagged to VLAN 50 you should be trunking that through the switch to a VLAN 50 interface defined in pfSense. That means VLAN 50 should be tagged on ports 1 and 5 in the switch.
That is the situation where you are seeing issues accessing sites so it's probably working since it's connecting via a different logical interface in pfSense.However all of that is not the actual issue you're facing. You say that in that situation those sites do not resolve, so it's probably a DNS issue.
You also said the DNS was the same on LAN and VLAN 50 but clearly it isn't. So how is the DNS configured for clients on VLAN 50?Steve
-
You create additional SSIDs and connect them to the VLANs.
-
I wonder if VLANs over WiFi are supported in the specs. The only significant difference is the content of the Ethertype/length field, though an AP could easily be designed to block VLANs. These days, WiFi links are often used to connect different sites and you'd want the WiFi to be transparent to everything, including VLANs. I guess I'll have to do some experiments some time.
-
@jknott Yes, SSID for 5g and 2.4g were created on the WAP and the corresponding VLAN in pfsense
-
@jknott after created the VLANs in pfsense with their own dhcp/dns server and tagging the ports where the WAP and the main LAN cable are, the devices get connected successfully, but some websites are not accessible, like duckduckgo, if i untag the ports, duckduckgo works normally.
-
@dridhas said in Wireless with VLAN not allowing traffic:
if i untag the ports, duckduckgo works normally.
Sorry it doesn't work that way! You must be filtering differently on this interface then.. A network being tagged or untagged has ZERO to do with if a website is allowed or not, or works or not, etc. It just doesn't - PERIOD!!
Not sure what rabbit hole you have lead yourself down - but tagged or not tagged has nothing to do with it.. If website works on network A, but not network B - then you have something different with dns, or filtering or firewall rules - it has zero to do with if the network is tagged or untagged.
-
@johnpoz yeah, i mightve done something to mess up that particular vlan...
after i nuked pfsense im planning on recreating one VLAN and test it and go from there.
ideal layout would be to have a vlan for IoT devices, one for 2.4g and one for 5g wifi
-
@dridhas if something isn't working on vlan X or network Y.. Then troubleshoot that thing - not that its tagged or not tagged.
If there was something wrong with the tagging - then nothing would work.. There is no possible way the tag could effect some websites not working while others do - just not possible.
If you had your tagging messed up - then you wouldn't be on that network..
You flipping your client to network Y and works, but move it to network X and something doesn't work - then troubleshoot that something. Firewall rule, dns - something, zero to do with X being a tagged vlan or untagged network/vlan.
-
@johnpoz based on that comment:
ive seen these 2 options:
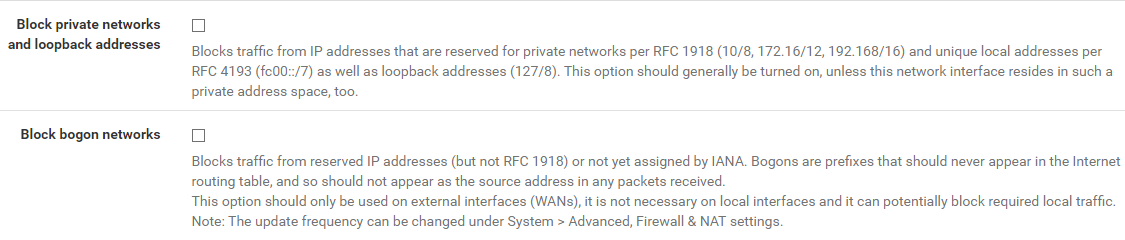
i have those enabled on the WAN interface, would they also need to be on the LAN + additional VLANs?
im unsure if i had them there before.