pfsense, web server and VLAN's
-
Hello Everyone,
I am a complete newbie when it comes to pfsense but I am very tenacious to getting things up and running the way I need it. So, I have finally today after some late nights finally have my pfsense up and running. I am a couple of issues I would like some help and advice with if possible please. To say this has been a difficult journey get this up and running would be an understatement!A brief outline of my setup
Plusnet Fibre with Static IP
BT Openreach Huawei EchoLife HG612 3B FTTC VDSL Fibre Modem
Fujitsu Futro S900 with Dual Nic Card
NETGEAR GS105E 5-portSo, I have a web server with a static Lan IP but when I connect it to my switch is will not get detected?
All my other hardware gets detected fine but just not my web server with the static lan ip and yes its all on the same subnet etc. Does anyone know why I will not get picked up by pfsense?
I would also like to know how to successfully setup VLANS with my pfsense and NETGEAR GS105E to separate everything on the network. But before I do this I really need to understand why pfsense will not detect my web server.
Thanks
Rockyuk
-
This post is deleted! -
How are you expecting it to get 'detected'? How are you testing?
Does it appear in the ARP table? (Diag > ARP)
Can you ping it from some other LAN side device?
Is the switch configured at all, is it still in the default setup?
Steve
-
Like this rest of the network devices that I connected assumed it would be detected like them like it is on my current network setup. I basically mirrored it just using pfsense as the router and installing a switch.
It does not appear in the ARP table, so I did not bother pinging it.
The switch itself is default setup and I have noticed it had its own DHCP setup on it. Not sure if that would be causing the issue due to pfsense also being a DHCP server.
Before I even looking into VLAN's I wanted to make sure everything worked on the network first before moving into that.
@stephenw10 said in pfsense, web server and VLAN's:
How are you expecting it to get 'detected'? How are you testing?
Does it appear in the ARP table? (Diag > ARP)
Can you ping it from some other LAN side device?
Is the switch configured at all, is it still in the default setup?
Steve
-
If it's static and not trying to connect it won't appear in the ARP table until you try to ping it or connect to it some other way.
If you connect to it from some other LAN client that traffic goes directly, it does not pass through pfSense, so it cannot be filtered by pfSense. If that is failing too it must be either something in the switch or a mismatch between the dynamic and static subnet config.
Steve
-
@stephenw10 I will try abit later with the Switch I do think it is to do with that some how.
-
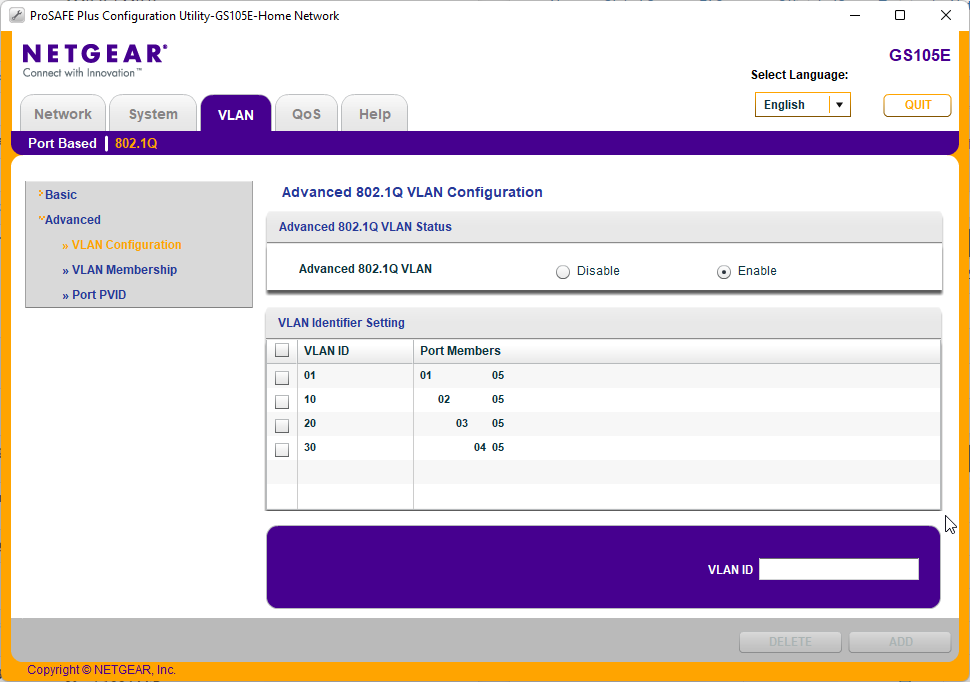
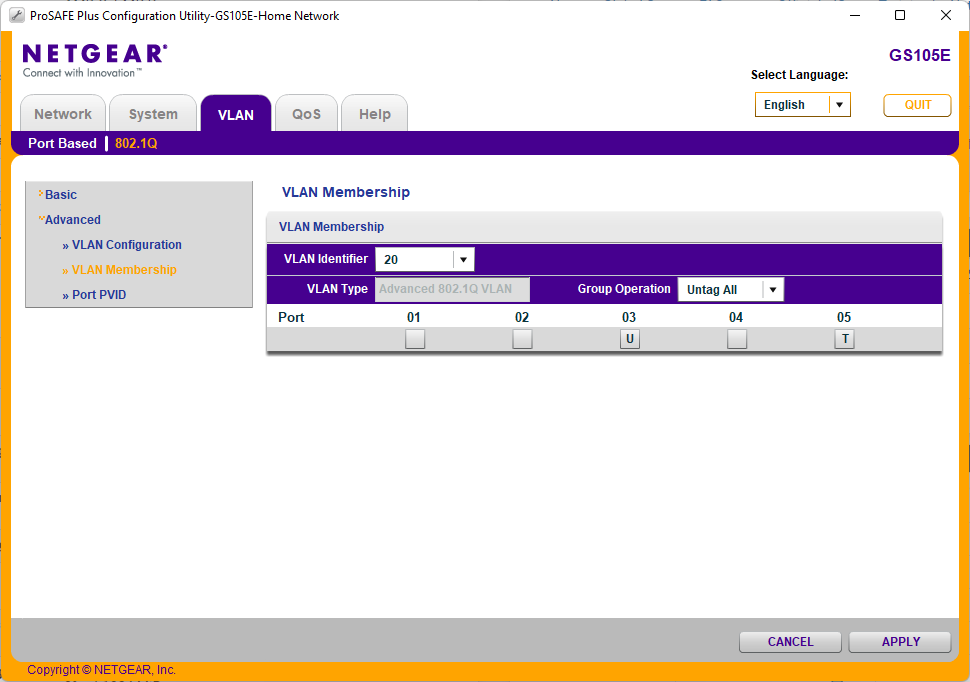
@stephenw10 Ok, I am trying to figure out my VLAN configuration on my Netgear ProSafe Gs105E
Pfsense/Internet is coming in on port 5
I have tagged port 2, 3 and 4 with VLAN ID’s
Under Memberships on the Switch I have put u under port 2 & 5? But it is not bringing up the DHCP range from pfsense on port 2?
Under Port PVID I have added the VLAN ID for the appropriate port is that correct?
I am trying to do this offline while I configure everything to reduce downtime before the switch over i.e without a live WAN connection, will that impact the DHCP assignment coming from pfsense?
Thanks
Rockyuk
-
What VLAN(s) are configured in pfSense? They all have DHCP active?
Probably going to need screenshots of the switch config to offer any advise there.
I expect to see port 5 tagged and the access port(s) untagged on whatever vlan you are trying to use.
Steve
-
@stephenw10 Hi Stephen, Ok here are the VLAN's configured
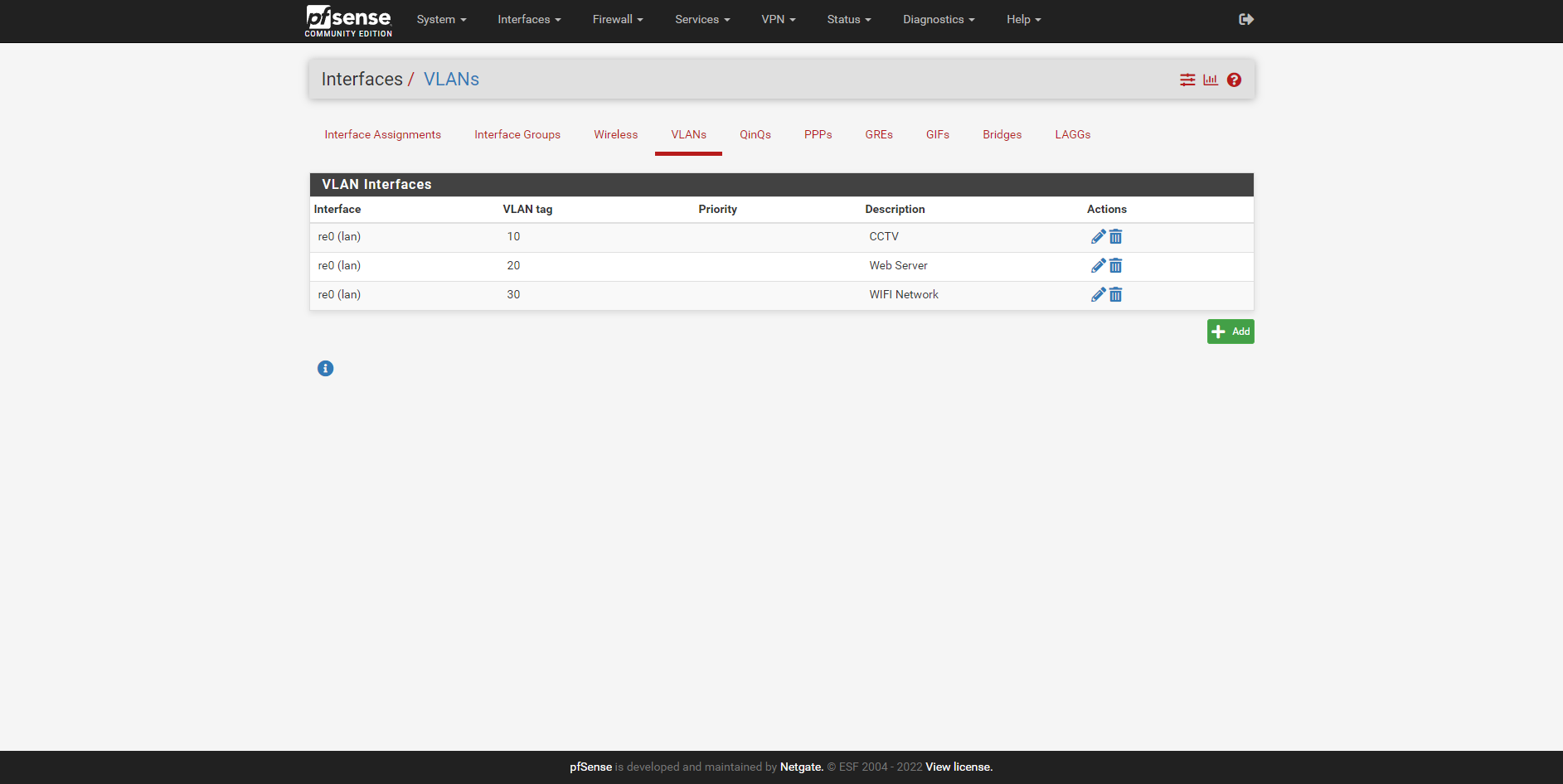
DHCP for one of the VLAN's
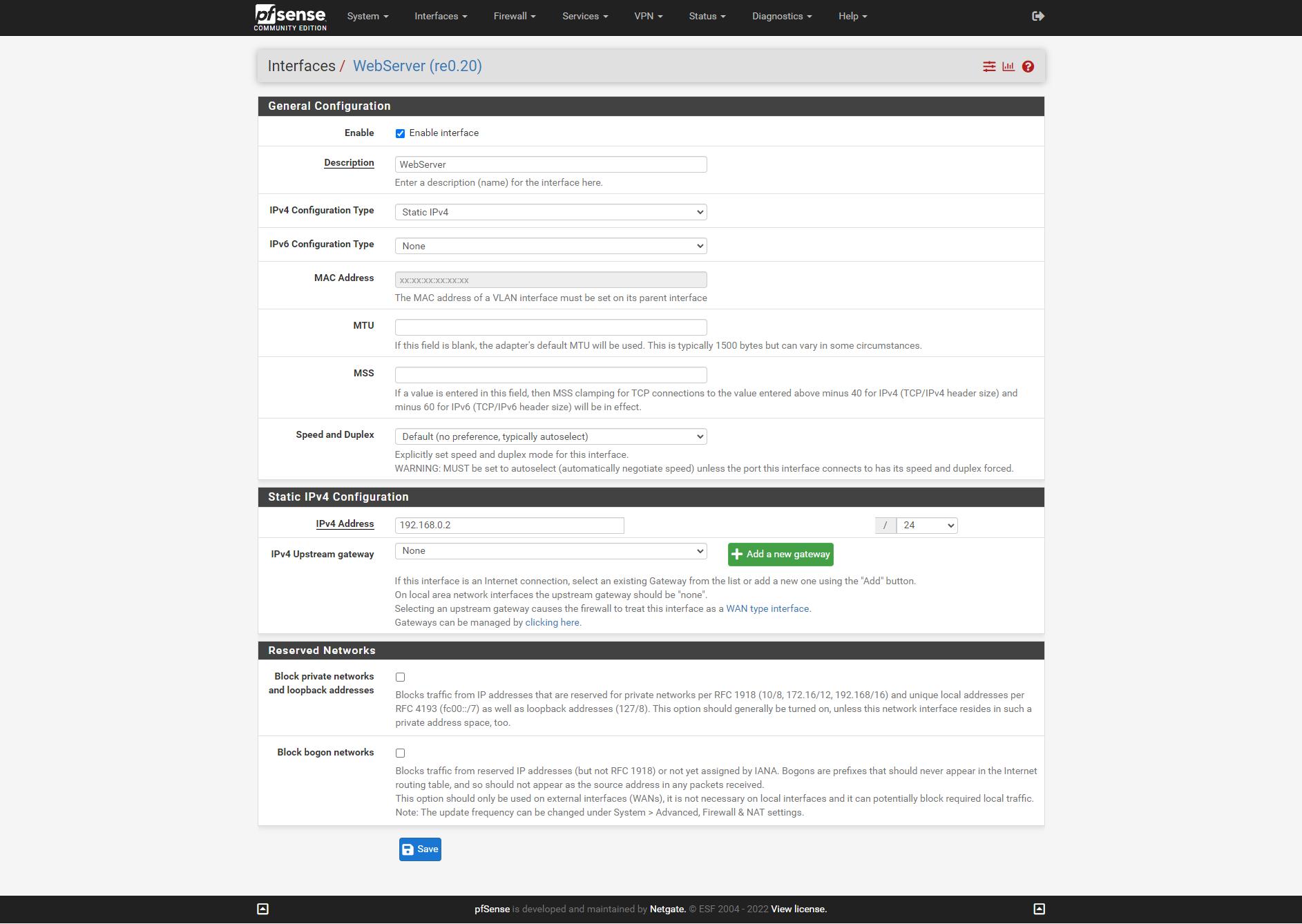
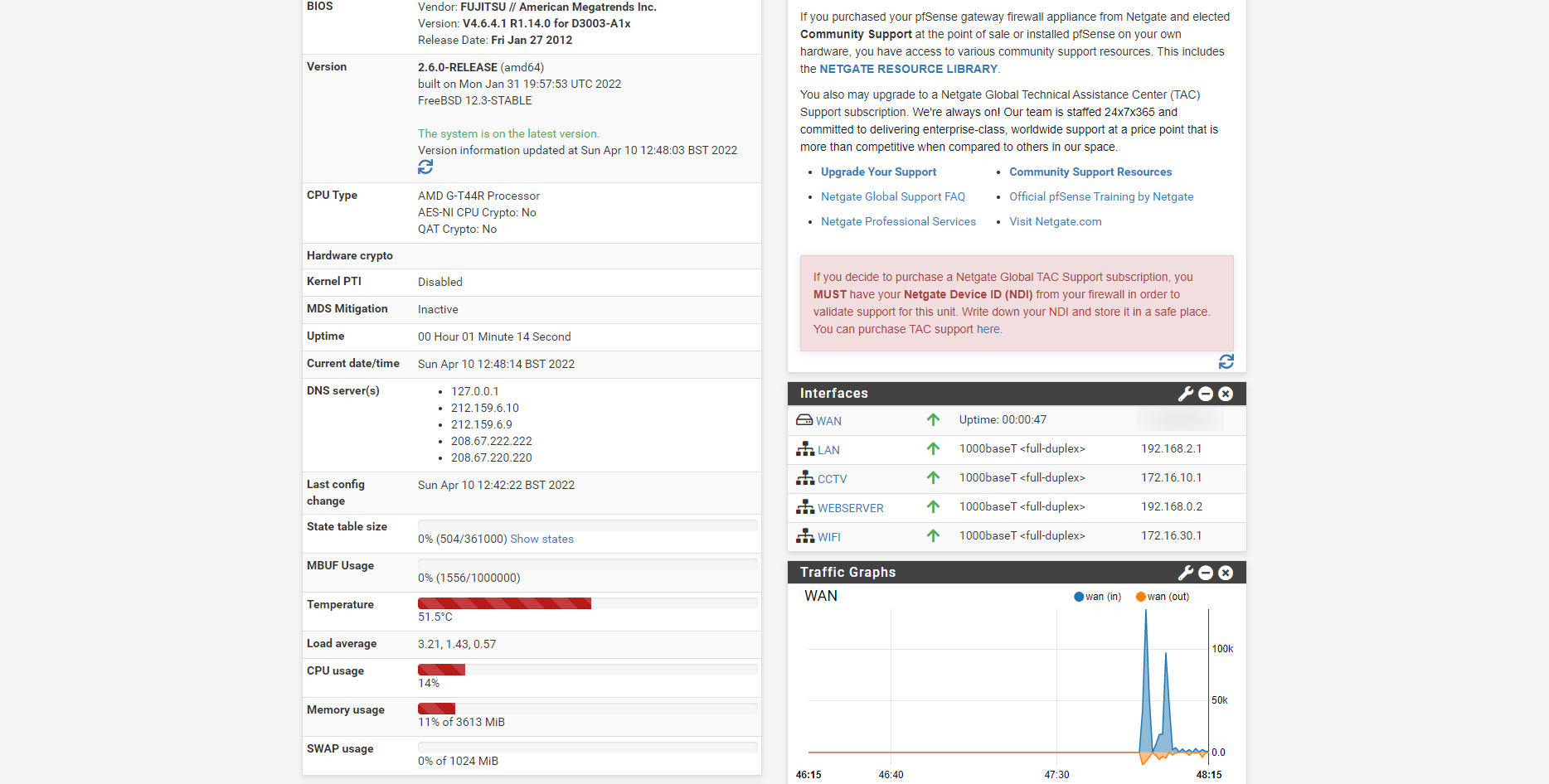
Dashboard
Switch
I am now getting the correct DHCP served on each port but no internet connection now?
Thanks
Rockyuk
-
You probably need to add firewall rules to the 'webserver' interface. Only LAN is given a pass rule by default. Any additional interfaces need rules to be added to pass traffic.
Steve
-
@stephenw10 Could you provide an example please?
-
Something like:
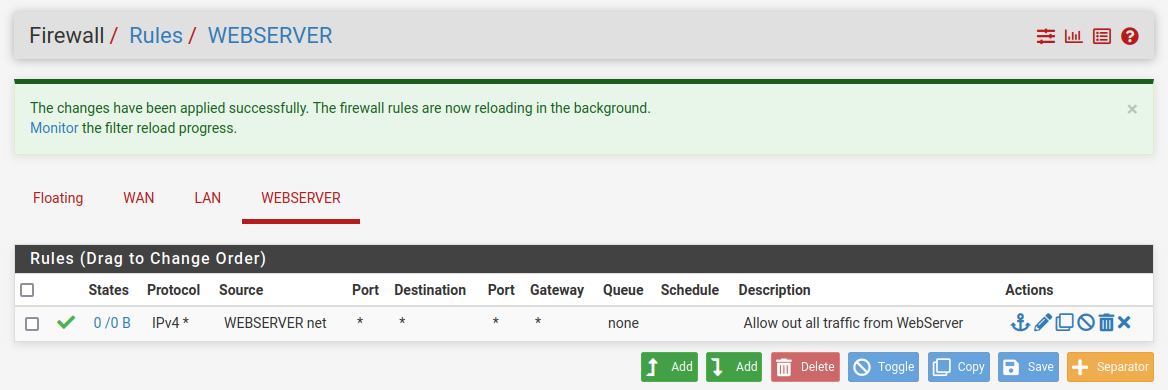
Though you may want to get more refined. It depends what subnets need access to one another.
Steve
-
@stephenw10 Thank you, I will give it a go and let you know.
-
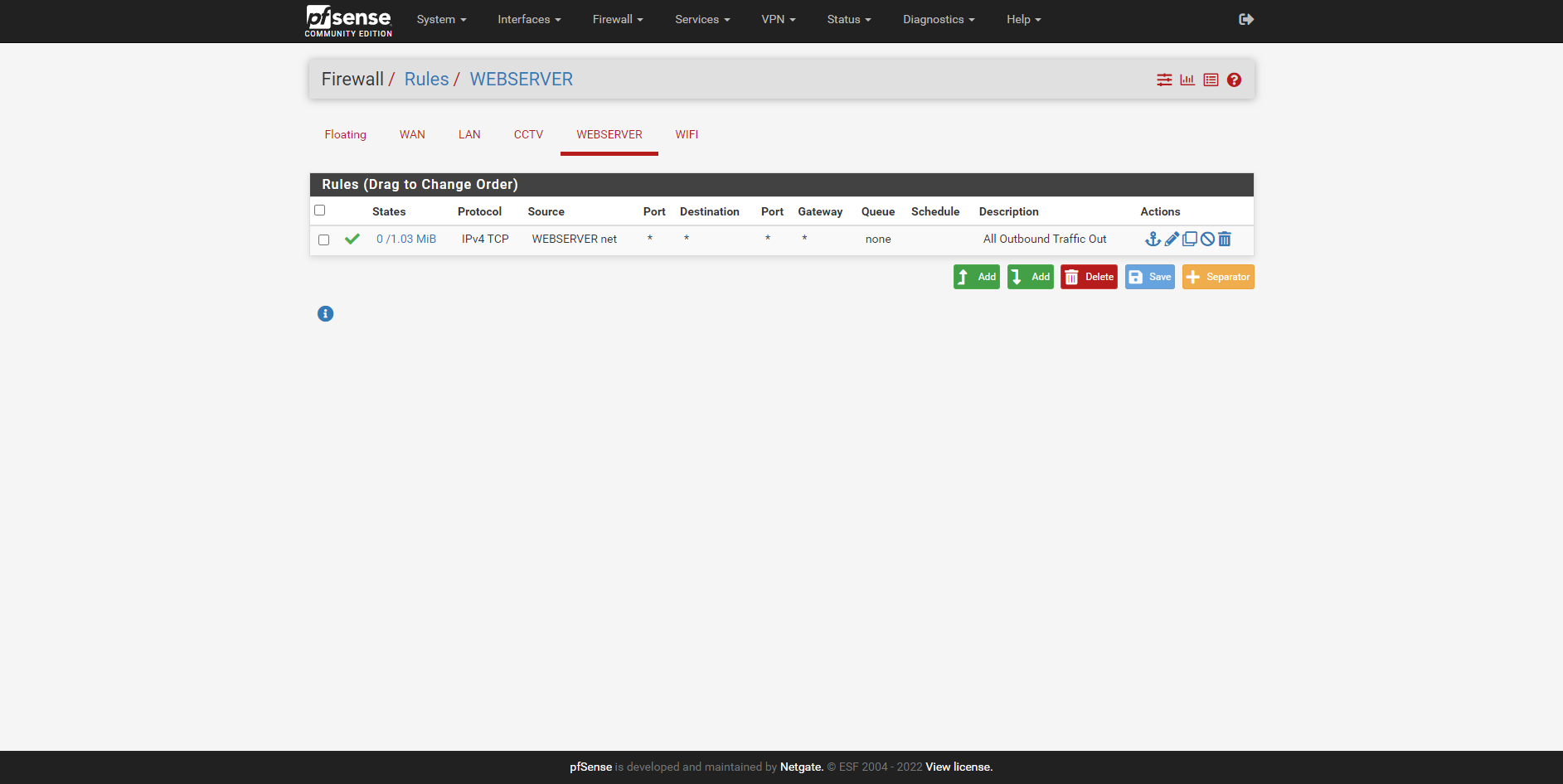
@stephenw10 Hi Stephen, I tried that and it worked briefly then stopped and started to stop resolving websites. Tried to bring up google and duckduckgo and nothing it did work for a few seconds then stopped.
-
That rule is passing TCP only, so DNS is not passed because it mainly uses DNS.
Set the protocol to 'any' as my example rule shows.
Steve
-
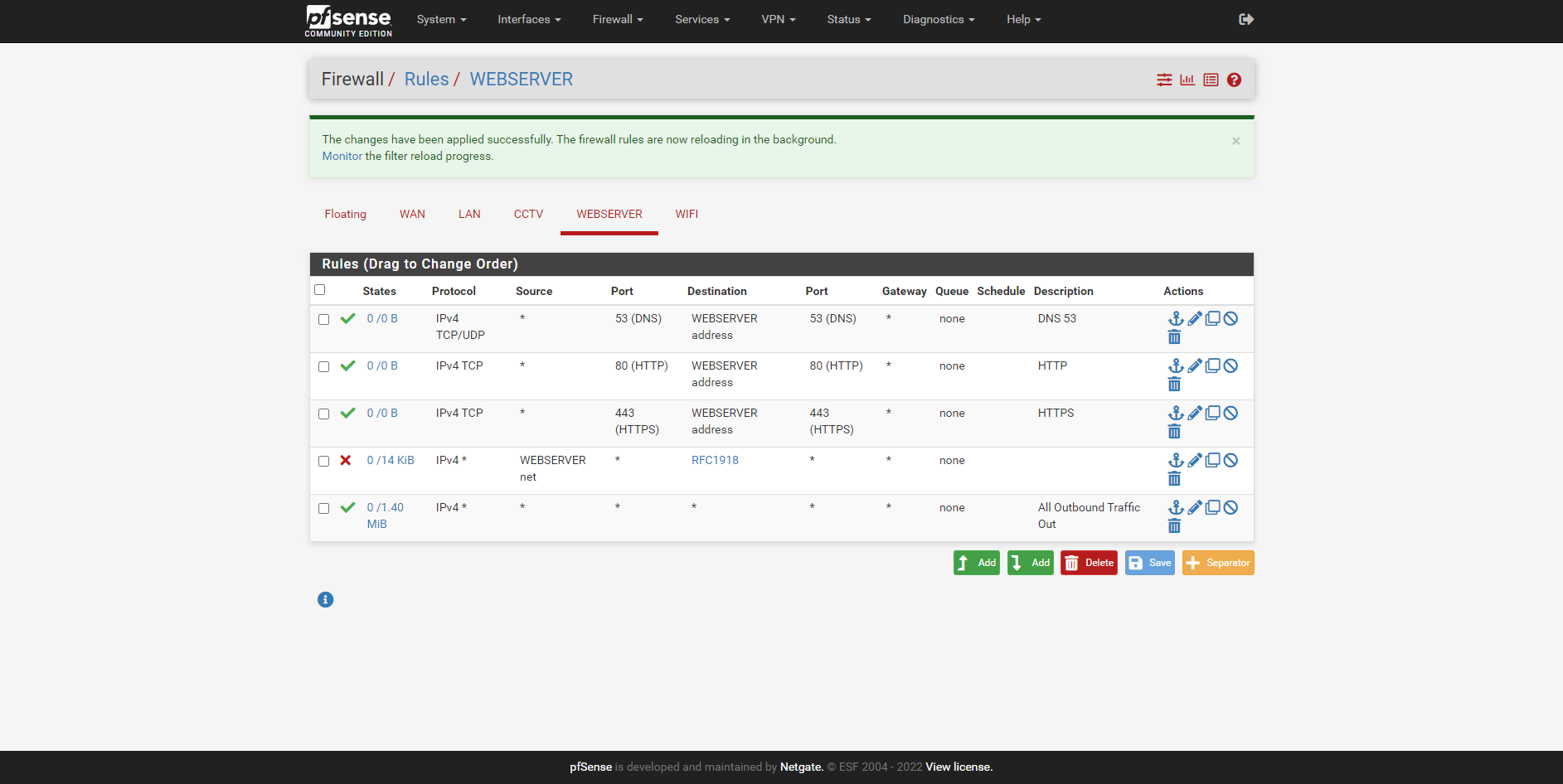
@stephenw10 You are a star that worked thank you, last thing. With regards to the web server for incoming firewall rules for HTTPS, HTTP and DNS etc, as my websites SSL does not seem to be loading. Is the below rules correct for incoming on the web server?
-
@rockyuk said in pfsense, web server and VLAN's:
Is the below rules correct for incoming on the web server?
Huh? Those are not "incoming" to your webserver - those are incoming to the pfsense interface your calling webserver.
They would not have anything to do with something talking to some webserver on this network, from some other network.
-
Indeed for incoming traffic to the webserver from some external address the rules would need to be on the WAN interface.
If the WEBSERVER subnet is private you would also need port forward rules to allow that. By default the port forwards will add appropriate firewall rules when you add them anyway.
The source port on rules like that should almost always be 'any'. Only the destination port is the known value for the traffic you are passing.In pfSense firewall rules apply to traffic coming into an interface. So for internal subnets that means traffic coming into the interface is from the hosts on that subnet to some other location outside the subnet.
Steve
-
@stephenw10 Apologies, I am new to all of this and probably not the easiest firewall for me to setup. So, I apologise if what I am doing does not make sense as I am learning as I go along. I have followed a lot of YouTube videos to get this far but I need a little more guidance on the Incoming Firewall rules for the web server.
Could you post an example for a rule for either incoming DNS (53) or HTTPS please. As I am clearly stuck on this part. Thank you
-
Add a port forward like this:
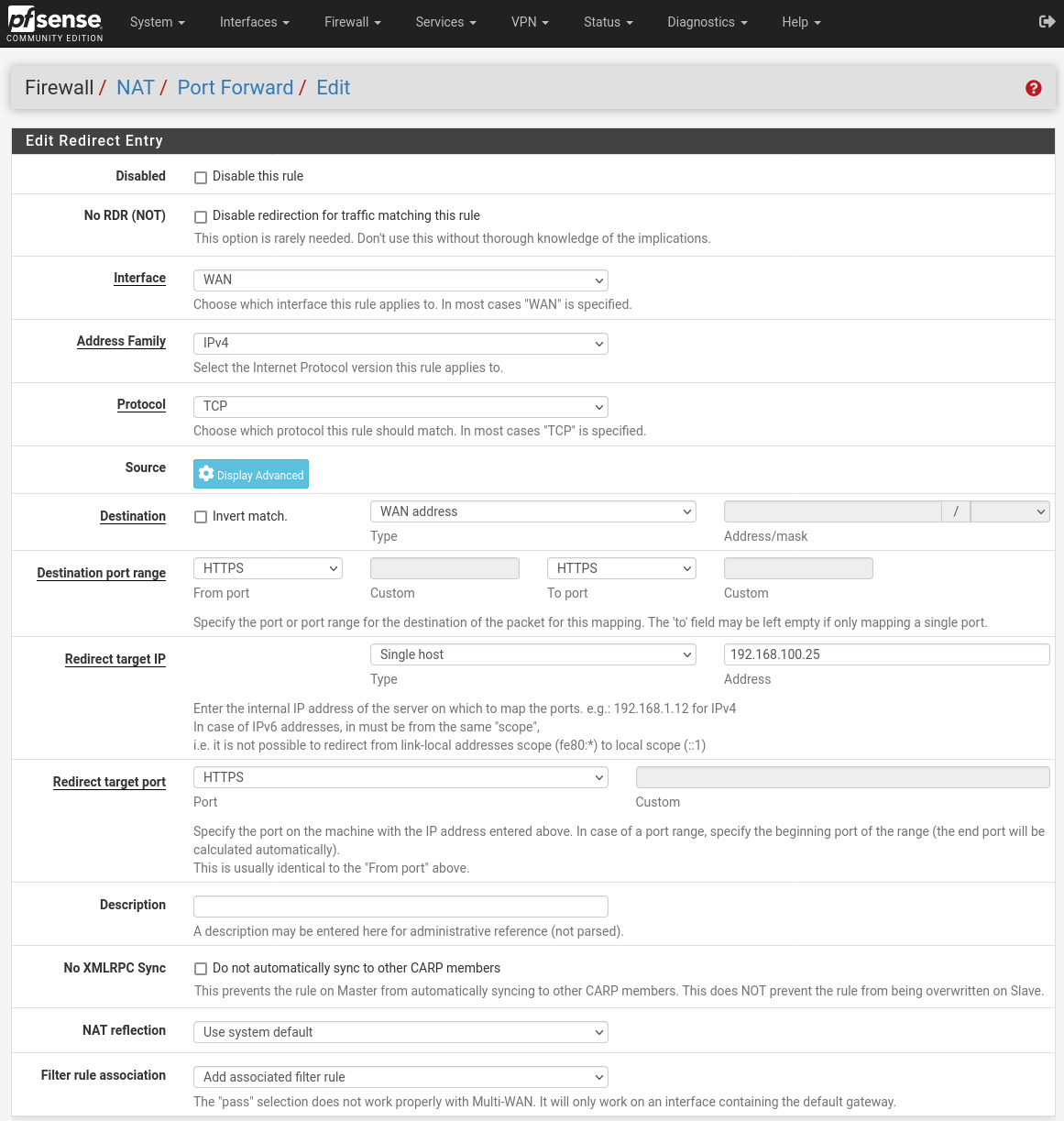
Obviously change the 'Redirect target IP' to the internal address of your webserver.
The 'Filter Rule Association' value there will create a matching firewall rule on WAN you will be able to see.
Are you sure you want to allow external access to DNS on that machine? That's almost always a bad idea!
Steve