IPsec Tunnel P1 and P2 comes up, but cannot ping the other side
-
Hello!
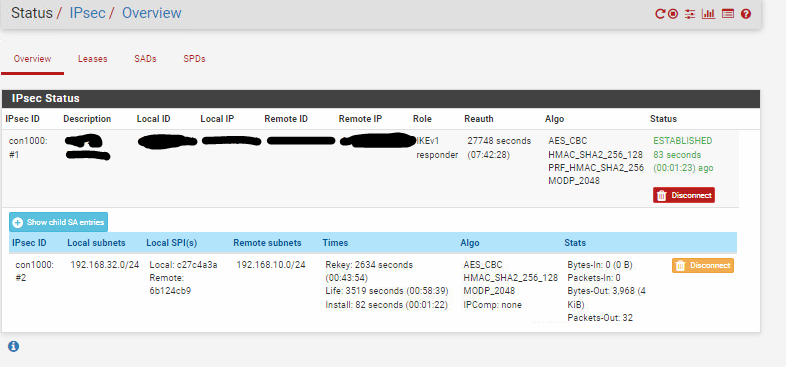
I have a IPsec tunnel between a Pfsense and another big firewall vendor . The Phase1 and Phase2 comes up, and is showing that the tunnel is up. But i cannot ping the host on the network on the other side (and the remote side cannot ping me as well). As you see in the screenshot, it seems that packets go out but I get nothing back.
The company on the other side says i should screw myself, because "I would not use a business firewall", like cisco, sophos etc... I feel like a complete idiot, because I am the one who is troubleshooting and reading logs and so on.... I doubt that they have ever looked inside their logs.
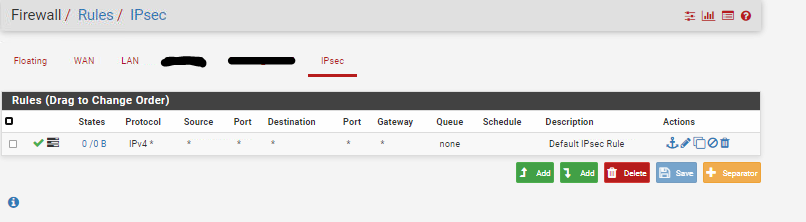
Here are the rules:
Could someone maybe take a look at this if I am doing something wrong:
Apr 13 17:43:45 ipsec_starter 40379 charon stopped after 200 ms
Apr 13 17:43:45 ipsec_starter 40379 ipsec starter stopped
Apr 13 17:45:39 ipsec_starter 51766 Starting strongSwan 5.7.1 IPsec [starter]...
Apr 13 17:45:39 ipsec_starter 51766 no netkey IPsec stack detected
Apr 13 17:45:39 ipsec_starter 51766 no KLIPS IPsec stack detected
Apr 13 17:45:39 ipsec_starter 51766 no known IPsec stack detected, ignoring!
Apr 13 17:45:39 charon 00[DMN] Starting IKE charon daemon (strongSwan 5.7.1, FreeBSD 11.2-RELEASE-p10, amd64)
Apr 13 17:45:39 charon 00[KNL] unable to set UDP_ENCAP: Invalid argument
Apr 13 17:45:39 charon 00[NET] enabling UDP decapsulation for IPv6 on port 4500 failed
Apr 13 17:45:39 charon 00[CFG] loading unbound resolver config from '/etc/resolv.conf'
Apr 13 17:45:39 charon 00[CFG] loading unbound trust anchors from '/usr/local/etc/ipsec.d/dnssec.keys'
Apr 13 17:45:39 charon 00[CFG] ipseckey plugin is disabled
Apr 13 17:45:39 charon 00[CFG] loading ca certificates from '/usr/local/etc/ipsec.d/cacerts'
Apr 13 17:45:39 charon 00[CFG] loading aa certificates from '/usr/local/etc/ipsec.d/aacerts'
Apr 13 17:45:39 charon 00[CFG] loading ocsp signer certificates from '/usr/local/etc/ipsec.d/ocspcerts'
Apr 13 17:45:39 charon 00[CFG] loading attribute certificates from '/usr/local/etc/ipsec.d/acerts'
Apr 13 17:45:39 charon 00[CFG] loading crls from '/usr/local/etc/ipsec.d/crls'
Apr 13 17:45:39 charon 00[CFG] loading secrets from '/var/etc/ipsec/ipsec.secrets'
Apr 13 17:45:39 charon 00[CFG] loaded IKE secret for %any IP ADRESS REMOTE SIDE
Apr 13 17:45:39 charon 00[CFG] opening triplet file /usr/local/etc/ipsec.d/triplets.dat failed: No such file or directory
Apr 13 17:45:39 charon 00[CFG] loaded 0 RADIUS server configurations
Apr 13 17:45:39 charon 00[LIB] loaded plugins: charon unbound aes des blowfish rc2 sha2 sha1 md4 md5 random nonce x509 revocation constraints pubkey pkcs1 pkcs7 pkcs8 pkcs12 pgp dnskey sshkey ipseckey pem openssl fips-prf curve25519 xcbc cmac hmac curl attr kernel-pfkey kernel-pfroute resolve socket-default stroke vici updown eap-identity eap-sim eap-md5 eap-mschapv2 eap-dynamic eap-radius eap-tls eap-ttls eap-peap xauth-generic xauth-eap whitelist addrblock counters
Apr 13 17:45:39 charon 00[JOB] spawning 16 worker threads
Apr 13 17:45:39 ipsec_starter 53283 charon (53528) started after 100 ms
Apr 13 17:45:39 charon 08[CFG] received stroke: add connection 'bypasslan'
Apr 13 17:45:39 charon 08[CFG] conn bypasslan
Apr 13 17:45:39 charon 08[CFG] left=%any
Apr 13 17:45:39 charon 08[CFG] leftsubnet=192.168.0.0/24
Apr 13 17:45:39 charon 08[CFG] right=%any
Apr 13 17:45:39 charon 08[CFG] rightsubnet=192.168.0.0/24
Apr 13 17:45:39 charon 08[CFG] dpddelay=30
Apr 13 17:45:39 charon 08[CFG] dpdtimeout=150
Apr 13 17:45:39 charon 08[CFG] sha256_96=no
Apr 13 17:45:39 charon 08[CFG] mediation=no
Apr 13 17:45:39 charon 08[CFG] added configuration 'bypasslan'
Apr 13 17:45:39 charon 16[CFG] received stroke: route 'bypasslan'
Apr 13 17:45:39 ipsec_starter 53283 'bypasslan' shunt PASS policy installed
Apr 13 17:45:39 charon 14[CFG] received stroke: add connection 'con1000'
Apr 13 17:45:39 charon 14[CFG] conn con1000
Apr 13 17:45:39 charon 14[CFG] left=IP ADRESS PFsense
Apr 13 17:45:39 charon 14[CFG] leftsubnet=192.168.32.0/24
Apr 13 17:45:39 charon 14[CFG] leftauth=psk
Apr 13 17:45:39 charon 14[CFG] leftid=IP ADRESS PFsense
Apr 13 17:45:39 charon 14[CFG] right=IP ADRESS REMOTE SIDE
Apr 13 17:45:39 charon 14[CFG] rightsubnet=192.168.10.0/24
Apr 13 17:45:39 charon 14[CFG] rightauth=psk
Apr 13 17:45:39 charon 14[CFG] rightid=IP ADRESS REMOTE SIDE
Apr 13 17:45:39 charon 14[CFG] ike=aes128-sha256-modp2048!
Apr 13 17:45:39 charon 14[CFG] esp=aes128-sha256-modp2048!
Apr 13 17:45:39 charon 14[CFG] dpddelay=10
Apr 13 17:45:39 charon 14[CFG] dpdtimeout=60
Apr 13 17:45:39 charon 14[CFG] dpdaction=3
Apr 13 17:45:39 charon 14[CFG] sha256_96=no
Apr 13 17:45:39 charon 14[CFG] mediation=no
Apr 13 17:45:39 charon 14[CFG] keyexchange=ikev1
Apr 13 17:45:39 charon 14[CFG] added configuration 'con1000'
Apr 13 17:45:39 charon 13[CFG] received stroke: route 'con1000'
Apr 13 17:45:39 charon 13[CFG] configured proposals: ESP:AES_CBC_128/HMAC_SHA2_256_128/NO_EXT_SEQ
Apr 13 17:45:39 charon 13[CHD] CHILD_SA con1000{1} state change: CREATED => ROUTED
Apr 13 17:45:39 ipsec_starter 53283 'con1000' routed
Apr 13 17:45:40 charon 14[NET] <1> received packet: from IP ADRESS REMOTE SIDE[500] to IP ADRESS PFsense[500] (288 bytes)
Apr 13 17:45:40 charon 14[ENC] <1> parsed ID_PROT request 0 [ SA V V V V V V V V V V ]
Apr 13 17:45:40 charon 14[CFG] <1> looking for an IKEv1 config for IP ADRESS PFsense...IP ADRESS REMOTE SIDE
Apr 13 17:45:40 charon 14[CFG] <1> candidate: %any...%any, prio 24
Apr 13 17:45:40 charon 14[CFG] <1> candidate: IP ADRESS PFsense...IP ADRESS REMOTE SIDE, prio 3100
Apr 13 17:45:40 charon 14[CFG] <1> found matching ike config: IP ADRESS PFsense...IP ADRESS REMOTE SIDE with prio 3100
Apr 13 17:45:40 charon 14[IKE] <1> received NAT-T (RFC 3947) vendor ID
Apr 13 17:45:40 charon 14[IKE] <1> received draft-ietf-ipsec-nat-t-ike-03 vendor ID
Apr 13 17:45:40 charon 14[IKE] <1> received draft-ietf-ipsec-nat-t-ike-02 vendor ID
Apr 13 17:45:40 charon 14[IKE] <1> received draft-ietf-ipsec-nat-t-ike-02\n vendor ID
Apr 13 17:45:40 charon 14[ENC] <1> received unknown vendor ID: 16:f6:ca:16:e4:a4:06:6d:83:82:1a:0f:0a:ea:a8:62
Apr 13 17:45:40 charon 14[IKE] <1> received draft-ietf-ipsec-nat-t-ike-00 vendor ID
Apr 13 17:45:40 charon 14[IKE] <1> received DPD vendor ID
Apr 13 17:45:40 charon 14[IKE] <1> received FRAGMENTATION vendor ID
Apr 13 17:45:40 charon 14[IKE] <1> received FRAGMENTATION vendor ID
Apr 13 17:45:40 charon 14[ENC] <1> received unknown vendor ID: 82:99:03:17:57:a3:60:82:c6:a6:21 00:00:00:00
00:00:00:00
Apr 13 17:45:40 charon 14[IKE] <1> IP ADRESS REMOTE SIDE is initiating a Main Mode IKE_SA
Apr 13 17:45:40 charon 14[IKE] <1> IKE_SA (unnamed)[1] state change: CREATED => CONNECTING
Apr 13 17:45:40 charon 14[CFG] <1> selecting proposal:
Apr 13 17:45:40 charon 14[CFG] <1> proposal matches
Apr 13 17:45:40 charon 14[CFG] <1> received proposals: IKE:AES_CBC_128/HMAC_SHA2_256_128/PRF_HMAC_SHA2_256/MODP_2048
Apr 13 17:45:40 charon 14[CFG] <1> configured proposals: IKE:AES_CBC_128/HMAC_SHA2_256_128/PRF_HMAC_SHA2_256/MODP_2048
Apr 13 17:45:40 charon 14[CFG] <1> selected proposal: IKE:AES_CBC_128/HMAC_SHA2_256_128/PRF_HMAC_SHA2_256/MODP_2048
Apr 13 17:45:40 charon 14[IKE] <1> sending XAuth vendor ID
Apr 13 17:45:40 charon 14[IKE] <1> sending DPD vendor ID
Apr 13 17:45:40 charon 14[IKE] <1> sending FRAGMENTATION vendor ID
Apr 13 17:45:40 charon 14[IKE] <1> sending NAT-T (RFC 3947) vendor ID
Apr 13 17:45:40 charon 14[ENC] <1> generating ID_PROT response 0 [ SA V V V V ]
Apr 13 17:45:40 charon 14[NET] <1> sending packet: from IP ADRESS PFsense[500] to IP ADRESS REMOTE SIDE[500] (160 bytes)
Apr 13 17:45:40 charon 14[NET] <1> received packet: from IP ADRESS REMOTE SIDE[500] to IP ADRESS PFsense[500] (380 bytes)
Apr 13 17:45:40 charon 14[ENC] <1> parsed ID_PROT request 0 [ KE No NAT-D NAT-D ]
Apr 13 17:45:40 charon 14[CFG] <1> candidate "bypasslan", match: 1/1/24 (me/other/ike)
Apr 13 17:45:40 charon 14[CFG] <1> candidate "con1000", match: 1/1/3100 (me/other/ike)
Apr 13 17:45:40 charon 14[ENC] <1> generating ID_PROT response 0 [ KE No NAT-D NAT-D ]
Apr 13 17:45:40 charon 14[NET] <1> sending packet: from IP ADRESS PFsense[500] to IP ADRESS REMOTE SIDE[500] (396 bytes)
Apr 13 17:45:40 charon 14[NET] <1> received packet: from IP ADRESS REMOTE SIDE[500] to IP ADRESS PFsense[500] (108 bytes)
Apr 13 17:45:40 charon 14[ENC] <1> parsed ID_PROT request 0 [ ID HASH N(INITIAL_CONTACT) ]
Apr 13 17:45:40 charon 14[CFG] <1> looking for pre-shared key peer configs matching IP ADRESS PFsense...IP ADRESS REMOTE SIDE[IP ADRESS REMOTE SIDE]
Apr 13 17:45:40 charon 14[CFG] <1> candidate "bypasslan", match: 1/1/24 (me/other/ike)
Apr 13 17:45:40 charon 14[CFG] <1> candidate "con1000", match: 1/20/3100 (me/other/ike)
Apr 13 17:45:40 charon 14[CFG] <1> selected peer config "con1000"
Apr 13 17:45:40 charon 14[IKE] <con1000|1> IKE_SA con1000[1] established between IP ADRESS PFsense[IP ADRESS PFsense]...IP ADRESS REMOTE SIDE[IP ADRESS REMOTE SIDE]
Apr 13 17:45:40 charon 14[IKE] <con1000|1> IKE_SA con1000[1] state change: CONNECTING => ESTABLISHED
Apr 13 17:45:40 charon 14[IKE] <con1000|1> scheduling reauthentication in 27831s
Apr 13 17:45:40 charon 14[IKE] <con1000|1> maximum IKE_SA lifetime 28371s
Apr 13 17:45:40 charon 14[ENC] <con1000|1> generating ID_PROT response 0 [ ID HASH ]
Apr 13 17:45:40 charon 14[NET] <con1000|1> sending packet: from IP ADRESS PFsense[500] to IP ADRESS REMOTE SIDE[500] (92 bytes)
Apr 13 17:45:41 charon 12[KNL] creating acquire job for policy IP ADRESS PFsense/32|/0 === IP ADRESS REMOTE SIDE/32|/0 with reqid {1}
Apr 13 17:45:41 charon 12[IKE] <con1000|1> queueing QUICK_MODE task
Apr 13 17:45:41 charon 12[IKE] <con1000|1> activating new tasks
Apr 13 17:45:41 charon 12[IKE] <con1000|1> activating QUICK_MODE task
Apr 13 17:45:41 charon 12[CFG] <con1000|1> configured proposals: ESP:AES_CBC_128/HMAC_SHA2_256_128/MODP_2048/NO_EXT_SEQ
Apr 13 17:45:41 charon 12[CFG] <con1000|1> configured proposals: ESP:AES_CBC_128/HMAC_SHA2_256_128/MODP_2048/NO_EXT_SEQ
Apr 13 17:45:41 charon 12[CFG] <con1000|1> proposing traffic selectors for us:
Apr 13 17:45:41 charon 12[CFG] <con1000|1> 192.168.32.0/24|/0
Apr 13 17:45:41 charon 12[CFG] <con1000|1> proposing traffic selectors for other:
Apr 13 17:45:41 charon 12[CFG] <con1000|1> 192.168.10.0/24|/0
Apr 13 17:45:41 charon 12[ENC] <con1000|1> generating QUICK_MODE request 1168194453 [ HASH SA No KE ID ID ]
Apr 13 17:45:41 charon 12[NET] <con1000|1> sending packet: from IP ADRESS PFsense[500] to IP ADRESS REMOTE SIDE[500] (460 bytes)
Apr 13 17:45:41 charon 12[NET] <con1000|1> received packet: from IP ADRESS REMOTE SIDE[500] to IP ADRESS PFsense[500] (444 bytes)
Apr 13 17:45:41 charon 12[ENC] <con1000|1> parsed QUICK_MODE response 1168194453 [ HASH SA No KE ID ID ]
Apr 13 17:45:41 charon 12[CFG] <con1000|1> selecting proposal:
Apr 13 17:45:41 charon 12[CFG] <con1000|1> proposal matches
Apr 13 17:45:41 charon 12[CFG] <con1000|1> received proposals: ESP:AES_CBC_128/HMAC_SHA2_256_128/MODP_2048/NO_EXT_SEQ
Apr 13 17:45:41 charon 12[CFG] <con1000|1> configured proposals: ESP:AES_CBC_128/HMAC_SHA2_256_128/MODP_2048/NO_EXT_SEQ
Apr 13 17:45:41 charon 12[CFG] <con1000|1> selected proposal: ESP:AES_CBC_128/HMAC_SHA2_256_128/MODP_2048/NO_EXT_SEQ
Apr 13 17:45:41 charon 12[CHD] <con1000|1> CHILD_SA con1000{2} state change: CREATED => INSTALLING
Apr 13 17:45:41 charon 12[CHD] <con1000|1> using AES_CBC for encryption
Apr 13 17:45:41 charon 12[CHD] <con1000|1> using HMAC_SHA2_256_128 for integrity
Apr 13 17:45:41 charon 12[CHD] <con1000|1> adding inbound ESP SA
Apr 13 17:45:41 charon 12[CHD] <con1000|1> SPI 0xc27c4a3a, src IP ADRESS REMOTE SIDE dst IP ADRESS PFsense
Apr 13 17:45:41 charon 12[CHD] <con1000|1> adding outbound ESP SA
Apr 13 17:45:41 charon 12[CHD] <con1000|1> SPI 0x6b124cb9, src IP ADRESS PFsense dst IP ADRESS REMOTE SIDE
Apr 13 17:45:41 charon 12[IKE] <con1000|1> CHILD_SA con1000{2} established with SPIs c27c4a3a_i 6b124cb9_o and TS 192.168.32.0/24|/0 === 192.168.10.0/24|/0
Apr 13 17:45:41 charon 12[CHD] <con1000|1> CHILD_SA con1000{2} state change: INSTALLING => INSTALLED
Apr 13 17:45:41 charon 12[IKE] <con1000|1> reinitiating already active tasks
Apr 13 17:45:41 charon 12[IKE] <con1000|1> QUICK_MODE task
Apr 13 17:45:41 charon 12[ENC] <con1000|1> generating QUICK_MODE request 1168194453 [ HASH ]
Apr 13 17:45:41 charon 12[NET] <con1000|1> sending packet: from IP ADRESS PFsense[500] to IP ADRESS REMOTE SIDE[500] (76 bytes)
Apr 13 17:45:41 charon 12[IKE] <con1000|1> activating new tasks
Apr 13 17:45:41 charon 12[IKE] <con1000|1> nothing to initiate
Apr 13 17:45:43 charon 11[CFG] vici client 1 connected
Apr 13 17:45:43 charon 10[CFG] vici client 1 registered for: list-sa
Apr 13 17:45:43 charon 09[CFG] vici client 1 requests: list-sas
Apr 13 17:45:43 charon 10[CFG] vici client 1 disconnected
Apr 13 17:45:48 charon 10[CFG] vici client 2 connected
Apr 13 17:45:48 charon 11[CFG] vici client 2 registered for: list-sa
Apr 13 17:45:48 charon 09[CFG] vici client 2 requests: list-sas
Apr 13 17:45:48 charon 02[CFG] vici client 2 disconnected
Apr 13 17:45:51 charon 02[IKE] <con1000|1> sending DPD request
Apr 13 17:45:51 charon 02[IKE] <con1000|1> queueing ISAKMP_DPD task
Apr 13 17:45:51 charon 02[IKE] <con1000|1> activating new tasks
Apr 13 17:45:51 charon 02[IKE] <con1000|1> activating ISAKMP_DPD task
Apr 13 17:45:51 charon 02[ENC] <con1000|1> generating INFORMATIONAL_V1 request 3857815992 [ HASH N(DPD) ]
Apr 13 17:45:51 charon 02[NET] <con1000|1> sending packet: from IP ADRESS PFsense[500] to IP ADRESS REMOTE SIDE[500] (108 bytes)
Apr 13 17:45:51 charon 02[IKE] <con1000|1> activating new tasks
Apr 13 17:45:51 charon 02[IKE] <con1000|1> nothing to initiate
Apr 13 17:45:51 charon 02[NET] <con1000|1> received packet: from IP ADRESS REMOTE SIDE[500] to IP ADRESS PFsense[500] (108 bytes)
Apr 13 17:45:51 charon 02[ENC] <con1000|1> parsed INFORMATIONAL_V1 request 981891894 [ HASH N(DPD_ACK) ]
Apr 13 17:45:51 charon 02[IKE] <con1000|1> activating new tasks
Apr 13 17:45:51 charon 02[IKE] <con1000|1> nothing to initiate
Apr 13 17:46:01 charon 02[IKE] <con1000|1> sending DPD request
Apr 13 17:46:01 charon 02[IKE] <con1000|1> queueing ISAKMP_DPD task
Apr 13 17:46:01 charon 02[IKE] <con1000|1> activating new tasks
Apr 13 17:46:01 charon 02[IKE] <con1000|1> activating ISAKMP_DPD task
Apr 13 17:46:01 charon 02[ENC] <con1000|1> generating INFORMATIONAL_V1 request 875302120 [ HASH N(DPD) ]
Apr 13 17:46:01 charon 02[NET] <con1000|1> sending packet: from IP ADRESS PFsense[500] to IP ADRESS REMOTE SIDE[500] (108 bytes)
Apr 13 17:46:01 charon 02[IKE] <con1000|1> activating new tasks
Apr 13 17:46:01 charon 02[IKE] <con1000|1> nothing to initiate
Apr 13 17:46:01 charon 09[NET] <con1000|1> received packet: from IP ADRESS REMOTE SIDE[500] to IP ADRESS PFsense[500] (108 bytes)
Apr 13 17:46:01 charon 09[ENC] <con1000|1> parsed INFORMATIONAL_V1 request 4236662059 [ HASH N(DPD_ACK) ]
Apr 13 17:46:01 charon 09[IKE] <con1000|1> activating new tasks
Apr 13 17:46:01 charon 09[IKE] <con1000|1> nothing to initiate
Apr 13 17:46:11 charon 09[IKE] <con1000|1> sending DPD request
Apr 13 17:46:11 charon 09[IKE] <con1000|1> queueing ISAKMP_DPD task
Apr 13 17:46:11 charon 09[IKE] <con1000|1> activating new tasks
Apr 13 17:46:11 charon 09[IKE] <con1000|1> activating ISAKMP_DPD task
Apr 13 17:46:11 charon 09[ENC] <con1000|1> generating INFORMATIONAL_V1 request 2018817643 [ HASH N(DPD) ]
Apr 13 17:46:11 charon 09[NET] <con1000|1> sending packet: from IP ADRESS PFsense[500] to IP ADRESS REMOTE SIDE[500] (108 bytes)
Apr 13 17:46:11 charon 09[IKE] <con1000|1> activating new tasks
Apr 13 17:46:11 charon 09[IKE] <con1000|1> nothing to initiate
Apr 13 17:46:11 charon 09[NET] <con1000|1> received packet: from IP ADRESS REMOTE SIDE[500] to IP ADRESS PFsense[500] (108 bytes)
Apr 13 17:46:11 charon 09[ENC] <con1000|1> parsed INFORMATIONAL_V1 request 61630031 [ HASH N(DPD_ACK) ]
Apr 13 17:46:11 charon 09[IKE] <con1000|1> activating new tasks
Apr 13 17:46:11 charon 09[IKE] <con1000|1> nothing to initiate
Apr 13 17:46:21 charon 09[IKE] <con1000|1> sending DPD request
Apr 13 17:46:21 charon 09[IKE] <con1000|1> queueing ISAKMP_DPD task
Apr 13 17:46:21 charon 09[IKE] <con1000|1> activating new tasks
Apr 13 17:46:21 charon 09[IKE] <con1000|1> activating ISAKMP_DPD task
Apr 13 17:46:21 charon 09[ENC] <con1000|1> generating INFORMATIONAL_V1 request 176546351 [ HASH N(DPD) ]
Apr 13 17:46:21 charon 09[NET] <con1000|1> sending packet: from IP ADRESS PFsense[500] to IP ADRESS REMOTE SIDE[500] (108 bytes)
Apr 13 17:46:21 charon 09[IKE] <con1000|1> activating new tasks
Apr 13 17:46:21 charon 09[IKE] <con1000|1> nothing to initiate
Apr 13 17:46:21 charon 09[NET] <con1000|1> received packet: from IP ADRESS REMOTE SIDE[500] to IP ADRESS PFsense[500] (108 bytes)
Apr 13 17:46:21 charon 09[ENC] <con1000|1> parsed INFORMATIONAL_V1 request 3878839537 [ HASH N(DPD_ACK) ]
Apr 13 17:46:21 charon 09[IKE] <con1000|1> activating new tasks
Apr 13 17:46:21 charon 09[IKE] <con1000|1> nothing to initiate
Apr 13 17:46:31 charon 09[IKE] <con1000|1> sending DPD request
Apr 13 17:46:31 charon 09[IKE] <con1000|1> queueing ISAKMP_DPD task
Apr 13 17:46:31 charon 09[IKE] <con1000|1> activating new tasks
Apr 13 17:46:31 charon 09[IKE] <con1000|1> activating ISAKMP_DPD task
Apr 13 17:46:31 charon 09[ENC] <con1000|1> generating INFORMATIONAL_V1 request 2811654413 [ HASH N(DPD) ]
Apr 13 17:46:31 charon 09[NET] <con1000|1> sending packet: from IP ADRESS PFsense[500] to IP ADRESS REMOTE SIDE[500] (108 bytes)
Apr 13 17:46:31 charon 09[IKE] <con1000|1> activating new tasks
Apr 13 17:46:31 charon 09[IKE] <con1000|1> nothing to initiate
Apr 13 17:46:31 charon 09[NET] <con1000|1> received packet: from IP ADRESS REMOTE SIDE[500] to IP ADRESS PFsense[500] (108 bytes)
Apr 13 17:46:31 charon 09[ENC] <con1000|1> parsed INFORMATIONAL_V1 request 1789320126 [ HASH N(DPD_ACK) ]
Apr 13 17:46:31 charon 09[IKE] <con1000|1> activating new tasks
Apr 13 17:46:31 charon 09[IKE] <con1000|1> nothing to initiate
Apr 13 17:46:41 charon 09[IKE] <con1000|1> sending DPD request
Apr 13 17:46:41 charon 09[IKE] <con1000|1> queueing ISAKMP_DPD task
Apr 13 17:46:41 charon 09[IKE] <con1000|1> activating new tasks
Apr 13 17:46:41 charon 09[IKE] <con1000|1> activating ISAKMP_DPD task
Apr 13 17:46:41 charon 09[ENC] <con1000|1> generating INFORMATIONAL_V1 request 3483270434 [ HASH N(DPD) ]
Apr 13 17:46:41 charon 09[NET] <con1000|1> sending packet: from IP ADRESS PFsense[500] to IP ADRESS REMOTE SIDE[500] (108 bytes)
Apr 13 17:46:41 charon 09[IKE] <con1000|1> activating new tasks
Apr 13 17:46:41 charon 09[IKE] <con1000|1> nothing to initiate
Apr 13 17:46:41 charon 09[NET] <con1000|1> received packet: from IP ADRESS REMOTE SIDE[500] to IP ADRESS PFsense[500] (108 bytes)
Apr 13 17:46:41 charon 09[ENC] <con1000|1> parsed INFORMATIONAL_V1 request 3445788844 [ HASH N(DPD_ACK) ]
Apr 13 17:46:41 charon 09[IKE] <con1000|1> activating new tasks
Apr 13 17:46:41 charon 09[IKE] <con1000|1> nothing to initiate
Apr 13 17:46:47 charon 10[CFG] vici client 3 connected
Apr 13 17:46:47 charon 10[CFG] vici client 3 registered for: list-sa
Apr 13 17:46:47 charon 06[CFG] vici client 3 requests: list-sas
Apr 13 17:46:47 charon 10[CFG] vici client 3 disconnected
Apr 13 17:46:51 charon 10[IKE] <con1000|1> sending DPD request
Apr 13 17:46:51 charon 10[IKE] <con1000|1> queueing ISAKMP_DPD task
Apr 13 17:46:51 charon 10[IKE] <con1000|1> activating new tasks
Apr 13 17:46:51 charon 10[IKE] <con1000|1> activating ISAKMP_DPD task
Apr 13 17:46:51 charon 10[ENC] <con1000|1> generating INFORMATIONAL_V1 request 3300756618 [ HASH N(DPD) ]
Apr 13 17:46:51 charon 10[NET] <con1000|1> sending packet: from IP ADRESS PFsense[500] to IP ADRESS REMOTE SIDE[500] (108 bytes)
Apr 13 17:46:51 charon 10[IKE] <con1000|1> activating new tasks
Apr 13 17:46:51 charon 10[IKE] <con1000|1> nothing to initiate
Apr 13 17:46:51 charon 10[NET] <con1000|1> received packet: from IP ADRESS REMOTE SIDE[500] to IP ADRESS PFsense[500] (108 bytes)
Apr 13 17:46:51 charon 10[ENC] <con1000|1> parsed INFORMATIONAL_V1 request 579051746 [ HASH N(DPD_ACK) ]
Apr 13 17:46:51 charon 10[IKE] <con1000|1> activating new tasks
Apr 13 17:46:51 charon 10[IKE] <con1000|1> nothing to initiate
Apr 13 17:46:52 charon 07[CFG] vici client 4 connected
Apr 13 17:46:52 charon 06[CFG] vici client 4 registered for: list-sa
Apr 13 17:46:52 charon 08[CFG] vici client 4 requests: list-sas
Apr 13 17:46:52 charon 06[CFG] vici client 4 disconnected
Apr 13 17:46:57 charon 08[CFG] vici client 5 connected
Apr 13 17:46:57 charon 08[CFG] vici client 5 registered for: list-sa
Apr 13 17:46:57 charon 06[CFG] vici client 5 requests: list-sas
Apr 13 17:46:57 charon 06[CFG] vici client 5 disconnected
Apr 13 17:47:01 charon 07[IKE] <con1000|1> sending DPD request
Apr 13 17:47:01 charon 07[IKE] <con1000|1> queueing ISAKMP_DPD task
Apr 13 17:47:01 charon 07[IKE] <con1000|1> activating new tasks
Apr 13 17:47:01 charon 07[IKE] <con1000|1> activating ISAKMP_DPD task
Apr 13 17:47:01 charon 07[ENC] <con1000|1> generating INFORMATIONAL_V1 request 2690005531 [ HASH N(DPD) ]
Apr 13 17:47:01 charon 07[NET] <con1000|1> sending packet: from IP ADRESS PFsense[500] to IP ADRESS REMOTE SIDE[500] (108 bytes)
Apr 13 17:47:01 charon 07[IKE] <con1000|1> activating new tasks
Apr 13 17:47:01 charon 07[IKE] <con1000|1> nothing to initiate
Apr 13 17:47:01 charon 07[NET] <con1000|1> received packet: from IP ADRESS REMOTE SIDE[500] to IP ADRESS PFsense[500] (108 bytes)
Apr 13 17:47:01 charon 07[ENC] <con1000|1> parsed INFORMATIONAL_V1 request 3488501246 [ HASH N(DPD_ACK) ]
Apr 13 17:47:01 charon 07[IKE] <con1000|1> activating new tasks
Apr 13 17:47:01 charon 07[IKE] <con1000|1> nothing to initiate
Apr 13 17:47:02 charon 06[CFG] vici client 6 connected
Apr 13 17:47:02 charon 06[CFG] vici client 6 registered for: list-sa
Apr 13 17:47:02 charon 07[CFG] vici client 6 requests: list-sas
Apr 13 17:47:02 charon 15[CFG] vici client 6 disconnected
Apr 13 17:47:07 charon 07[CFG] vici client 7 connected
Apr 13 17:47:07 charon 07[CFG] vici client 7 registered for: list-sa
Apr 13 17:47:07 charon 07[CFG] vici client 7 requests: list-sas
Apr 13 17:47:07 charon 13[CFG] vici client 7 disconnected
Apr 13 17:47:12 charon 13[IKE] <con1000|1> sending DPD request
Apr 13 17:47:12 charon 13[IKE] <con1000|1> queueing ISAKMP_DPD task
Apr 13 17:47:12 charon 13[IKE] <con1000|1> activating new tasks
Apr 13 17:47:12 charon 13[IKE] <con1000|1> activating ISAKMP_DPD task -
Which pfsense version?
Looks like the other site isn't sending anything into the tunnel.
P2 matches on both sides? -
@nocling
Pfsense Version 2.4.4 - but I have already tried it with another pfsense with version 2.6.0 - same behaviour.
As far as I can tell, P2 matches. The Pfsense-log on my side is not saying anything like it would not... -
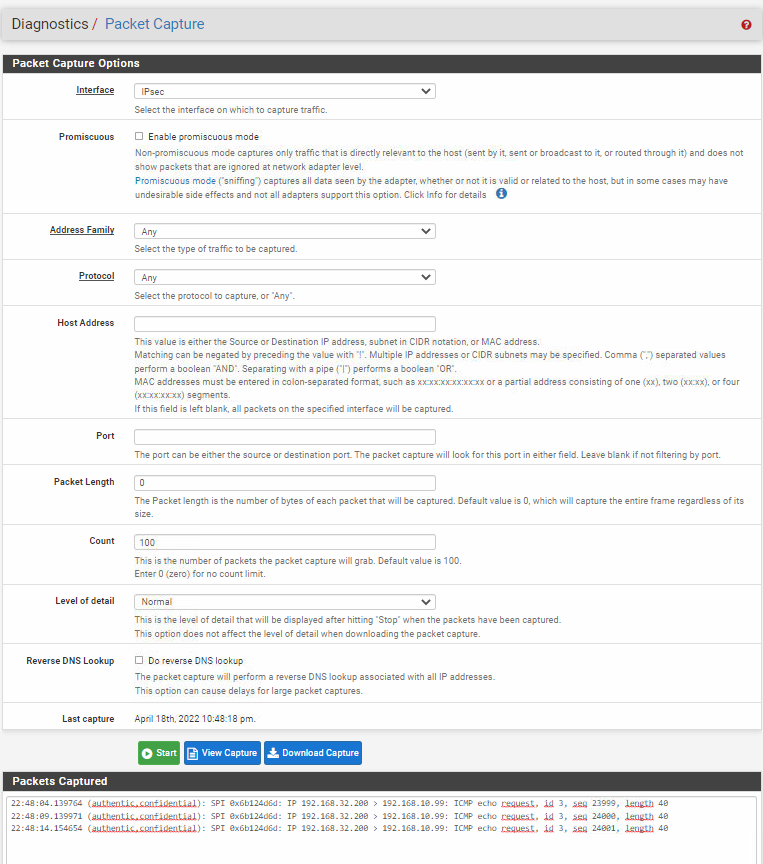
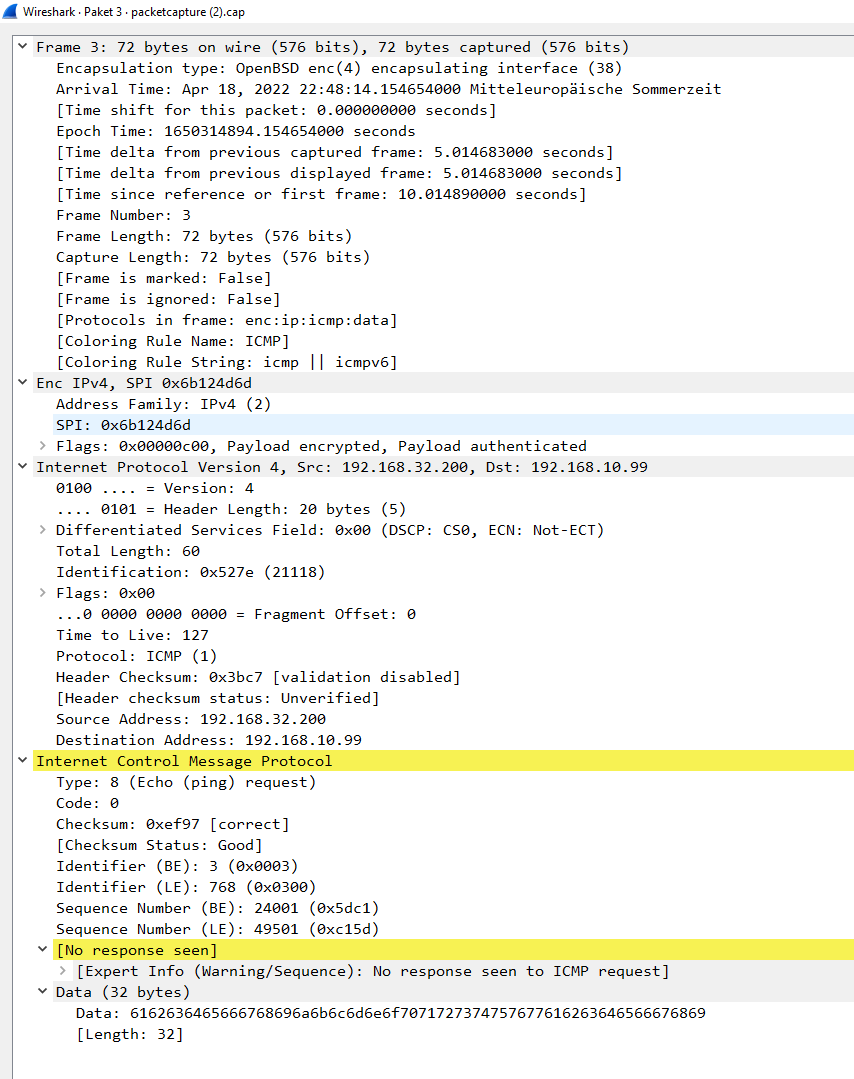
@pelikanruban Can they ping your firewall? Run a packet capture on the IPsec interface and verify the traffic is routing through.
I don't see where in the logs you provided the P2 is being established, only the P1.
-
they tried to ping the firewall but they say, that they would not get an answer.
I made a packet capture and during this, i did a ping on the printer on the other side (that should be reachable). I am the 192.168.32.200does this help?
-
you mean if they can ping the public ip form my firewall or you mean the local gateway in the subnet (192.168.32.1)
-
@pelikanruban This.
If you had a pcap going at the same time there's no evidence the pings ever came through.What is the "other" platform? Have they shared their config file with you so you can verify your settings match theirs?