IPSEC VPN connects from iOS, but does not route traffic
-
Hi,
I've followed the guide at https://docs.netgate.com/pfsense/en/latest/recipes/ipsec-mobile-ikev2-eap-mschapv2.html and I've setup a IPSEC IKEv2 VPN.
However, I can't access anything on the local LAN.
Strangely enough, I can ping my iPhone from the LAN, but the iPhone can't reach any LAN device.
I've tried to setup a route, but that gets me no where, conflicting with the existing route.
Thanks
P
-
So I've been able to progress this. Turns out some network changes from swapping out my old router caused the bulk of the problems, I can now see a webpage remotely over the VPN.
However, I can't seem to RDP to my windows server.
I've tried various combinations of firewall rules and that's getting me no where.
-
A further update, my tests so far have been from an iPhone with an IPv6 address.
As a VPN client, it's getting strange results. http and https traffic seems to route fine, but anything else fails.
When I hot-spotted my iPad and used it as a VPN client, everything worked fine. The only difference, my iPad received a class B private ipv4 address with a /28 subnet.
My iPhone get ipv6 address from my service provider.
Interestingly, the ip address that is set under VPN / Mobile Clients does not seem to honour the subnet. For example, I've set 10.10.40.0 as the network address and 24 as the subnet. However, My ipad has ignored that subnet and has run with a /8 subnet, ie: 255.0.0.0
-
We've enountered a lot of Issues with VPN on iOS devices.
A core-point is Apple's DNS-Privacy: When connected to a wifi, apple by default is ignoring the assigned dns servers (and therefore any dns assigned by the tunnel) and instead is using the apple cloud dns, "to protect your privacy" (at least that's the reason they claim)
You can set the dns-server for a particular wifi to manual to resolve this. Just becomes very unhandy, if you have hundrets of clients dealing with that "feature".
Your observation about the IPV6 / IPV4 difference might be the problem:
Your iPhones provider is using IPV6, and your ipv4-connection is then only an ipv4 over ipv6 tunnel (In our country referred to as "Dual-Stack-Lite / DS-Lite").
Here you'll have limits on the usable ports - depending on the provider. He might have decided, that a common user needs to use port 80 and 443, therefore created the proper rules for that, but everything else well not be forwarded.
(Your Phone would be the router here, IPV4 only over nat'd IPV6)
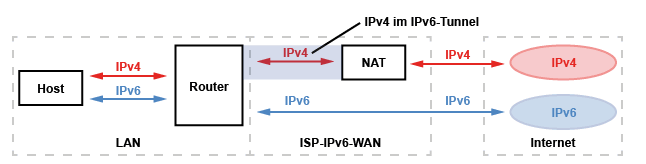
Your best option here would be to make your vpn-server ipv6 capable , OR (that's what we did): Use Port 143 - that's IMAPS - nobody is using imap nowadays, but that port is most likely served by your isp.