VLAN on D-link
-
@fireix I don't understand what you're saying. It's done. You have vlan 40 tagged on port 1. That's what you want
-
I have no clue why it refuse to set port 1 as Tagged in this interface. In evey other GUI for other vendors, it would allow me to set port 1 as tagged member of VLAN40. It just jumps back to "Not Member" after pushing Save.
-
@fireix It is tagged. I don't know what you're saying. It's done.
-
@jarhead Is there any term called "VLAN untagged" or "VLAN tagged"? I have heard of ports that are tagged or untagged - but never VLAN itself as it can have any combination of untagged and tagged members. So it sounds wrong in my ears ;) (and the server in port 43 doesn't get any IP from pfSense, so I know it doesn't work).
All my intuition says that the "VLAN 40" to the rigth in that list is actually Port 40. Based on several things, but specially that above.
I'll continue trying tomorrow, thanks for trying to help :)
-
Or maybe I'm wrong.. to tired, time to find bed and look at it with fresh eyes tomorrow ;)
-
Trunk on a D-Link means "Port-Channel in Cisco language"
I don't recommend to fiddle with multi IF trunking, for starters.A port can have one of three "vlan membership states"
Untagged
Tagged
Not Member.Only one of them can be active.
On any port:
Untagged - can only be active on ONE vlan.
Tagged - can be active on many vlans.
Not Member - can be active on many vlans.I have never seen hybrid mode on my switches (not 15xx series) , but sounds like not for starters.
My advice is to :
1:
Decide for a management vlan (could be vlan1 .. if you insist) , make the "last port" an untagged member of that vlan. Move your PC to the newly made mgmt port.2:
Make ALL other ports NOT member of Vlan1 (Usually the default) , to start with a clean membership database.3:
Make & Name the vlans you want to use.4:
Go to the desired vlan , and set the desired port to Tagged/Untagged/Not-Member.
Repeat for all Vlans in use.Done.
Remember a port can only be untagged in ONE vlan.
/Bingo
-
@bingo600 said in VLAN on D-link:
Go to the desired vlan , and set the desired port to Tagged/Untagged/Not-Member.
Repeat for all Vlans in use.I haven't made it work, the GUI is so super confusing and considering just upgrade the switch so I can understand it..
Just a quick stupid question: Is it in easy/possible to have a "dumb" switch (I assume VLAN-tags are just passed on in most cases) and just configure the actual server/PC in a normal port to be on the same VLAN as configured in pfSense?
I see that some windows-server lets you set the network card to a spesific VLAN (under hardware-settings on the network card). So that could be a quicker way for me. The server will run free hypver-v, so I think it would be little administration on it even? Or will it be super complicated? The idea is limit the access/noise to this single server.
-
Where is your issue ??
Vlans on the pfSense ?
Se here
https://forum.netgate.com/post/944383or
Vlans on the D-Link ?
Do as i described above ...or
Both ?
Don't give up ....
We have "talked a lot of people through this"Ohh ... Please tell me you have a pysical pfSense Box , and not a Virtual one.
That's another layer of troubles .... -
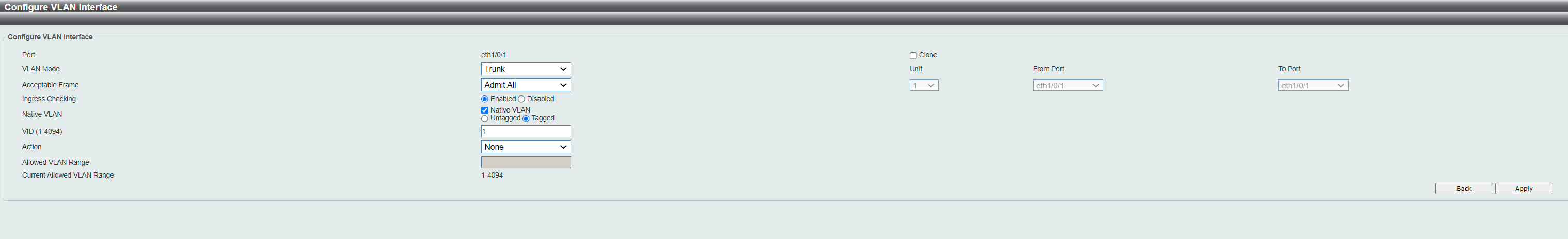
@bingo600 Vlans on pfSense Supermicro-server with 4 ports (physical yes) was easy and no problems at all. Followed tutorial to the letter and it looks just fine. Connection from a LAN-port (that has 3 VLANs I set up on it) directly to D-Link port 1.
The problem is D-Link. switch and to do the thing you describe under 4. (choosing tagged, non-tagged, non-member) in the interface. I understand your instructions , but the GUI simply doesn't let me to do it easy as I can see all other GUIs let you do (even on cheaper switches). It is at least 4-5 different places and it isn't always clear what each setting will do. What I can do in the "Member" interface depens on all those 4-5 other places and even then it doesn't let me to do a tag 1 port and untagged 43 port (it refuse to let me have port 1 tagged/member, even thougth the option is active).
The easy part is to create the VLANs and their naming, that was super easy everywhere.
Not giving up yet, just taking a break.. maybe try to read up on how to do it from terminal/shell instead. But requires som learning of dlink syntax.
I will create a small lab at home just to see if I can do it on other switches.
-
Did you remember to select vlan1 , and make all ports except the one you use right now on PC for manage , NOT MEMBER.
That bit me more than once , that D-Link defaults all ports to be untagged in Vlan1. Then you're locked with a lot of other selections.
I have 1100 & 1210 series.
What model do you have ?
If you have a 15xx then it seems like Trunk is like "Cisco Trunk" , and not Port-Channel"
https://eu.dlink.com/uk/en/support/faq/switches/layer-2-gigabit/dgs-series/es_dgs_1510_escenario_config_vlan_por_gui_y_cliThere seems to be an error in the D-Link example
http://forums.dlink.com/index.php?topic=73651.0Makes sense ...
A switchport would not be able to do both tagged & untagged VlanX (here 2)
So the range 1-3 should be 1,3 , as 2 is untagged.I do agree it looks rather confusing , with :
Access
Hybrid
TrunkTo me it seems like :
Access is "access" single untagged vlan membership .
Hybrid can have one Native/Untagged Vlan , and multiple tagged vlans.
Trunk seems to be for just "tagged" vlans.I would use a Tagged port towards the pfS interface.
But on my D-Links where i have no ingress control, i use what they call hybrid.
I made a Vlan XXX as a Dummy Native Vlan , and set all my Native Vlans on my "Trunk ports" to Vlan XXX , to "blackhole" untagged traffic on my trunkports.
I have NO untagged Vlan on my pfS trunk interfaces.As i see it Trunk is "Hybrid" with untagged frames filtered away in ingress (entry).
/Bingo
-
@bingo600 DGS1510 52X is the switch I have.
I agree that port 1 should be tagged (pfSense). I assume setting Trunk would mostly do the same. I wanted to keep vlan1 for all current traffic except the port of the server I want on the different vlan. That port should be untagged. Here I assume Access-port do the work automatically and removes some options. But a bit complicated to know the difference.
But is there something called "untagged VLAN" and "tagged vlan"? I know untagged/tagged ports in a VLAN, but actually hole vlans?
-
@fireix said in VLAN on D-link:
But is there something called "untagged VLAN" and "tagged vlan"? I know untagged/tagged ports in a VLAN, but actually hole vlans?
A Port cant be tagged or untagged , only a Vlan can (tags belongs to Vlans).
A Port can be :Member of (Carry traffic for) one or more Vlans (tagged), One Port can only carry untagged traffic for ONE vlan.
If a port is member of "Untagged Vlan X" , then it can't also be member of "tagged Vlan X".
Untagged ports are usually used for "normal devices" PC's , APPLE-TV's etc , that has a "Normal networkcard setup" .
Tagged traffic is used between devices that carry traffic containing several vlans.
pfSense to switches , switches to switches , Hypervisors to switches , and is also often used to connect to accesspoints that runs several ssid's.You would 95% of time make a standard PC switchport , an untagged member of VlanX
When a port is "Untagged member of VlanX" , it just refers to the frames sent between the "device ie. PC" and the port , here untagged means the port communicates with the end device , with normal ethernet frames, plain network card setup.
The traffic received on that untagged (Vlan X) port , will be tagged (with Vlan X id) and sent to all other ports that are tagged members of VlanX , that's how ie. pfSense sees the data from an untagged port , via the tagged connection from the switch to the pfSense.The traffic received on that untagged (Vlan X) port , will also be replicated to all Ports that are "Untagged members of VlanX" , here it will be sent put as "untagged" aka. normal ethernet frames.
Edit:
You should really read the post i made here , about tagging (envelopes)
https://forum.netgate.com/post/944383/Bingo
-
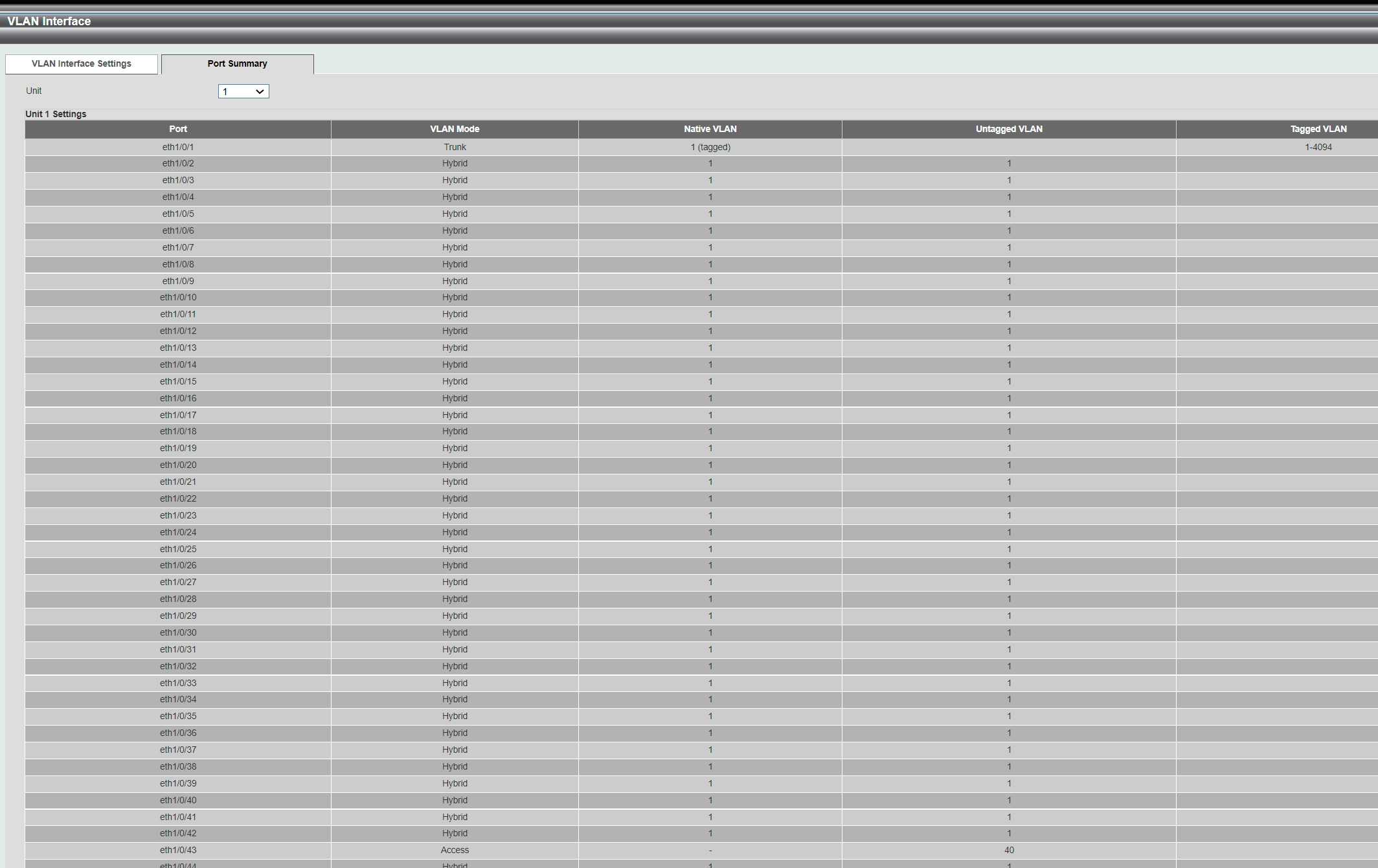
So you are also saying this looks correct?

My goal is to just get one server over to a VLAN and I think all the other GUIs I have seen from other vendors handles this very easy: You just choose edit VLAN 40 for instance, then choose all ports you want to join (tagged port 1 (pfsense) and untag the access port (the PC) in their visual list of ports. It should be that simple. Since a tagged port 1 inside a vlan can be a member on vlan 10 or other vlans (not sure if it technical is a member, but all other GUIs let you choose port 1 and port 43 for example - and you can repeat that for port 1 and port 3.. and port 1 and 5.. As long as port 1 is tagged inside each VLAN and all the other ports in the VLAN is untagged (PC/servers), it can help provide internet/pfsense to all vlans).
I have a pfSense box at home and a PC.. by changing the PC's adapter to VLAN40 (using the broadcom diagnose network utility) and connecting to the pfSenses LAN-port, I was able to get the DHCP-leases on that private VLAN
 So much fun! I see the fw rules under that VLAN is respected also and blocked everything until I opened up. So everything work as expected in LAB. Next is to introduce a switch to see if I can do the VLAN on the switch without changing the network cards vlan id... Unfortunately, I don't have Dlink, but can at least test my skills on a different brand..
So much fun! I see the fw rules under that VLAN is respected also and blocked everything until I opened up. So everything work as expected in LAB. Next is to introduce a switch to see if I can do the VLAN on the switch without changing the network cards vlan id... Unfortunately, I don't have Dlink, but can at least test my skills on a different brand..Could I in theory do the same with the server, just change the card there also and avoid the D-link issues? As long as the switch isn't removing the VLAN-tags between the server and the pfSense, the server has a bit less noise from the network at least I would assume.
-
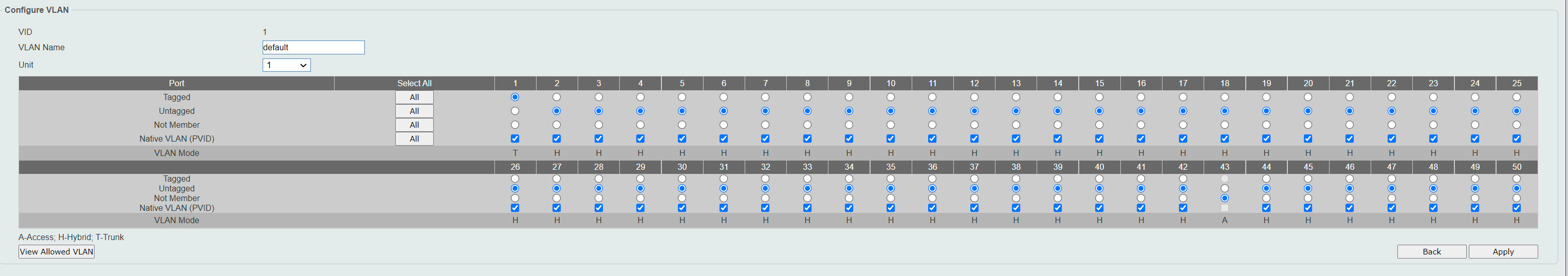
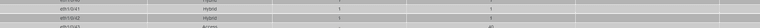
That picture shows that the switch Eth1/0/1 is setup to do "untagged traffic" in Vlan1 , and at the same time pass tagged traffic for Vlan40.
This would mean that if you connect that port to pfSense:
Untagged traffic (between pfSense & Switch) would end up the Switch's Vlan1 ,
And that link would also pass traffic tagged with Vlan40.So far so good .....
But your PC (Server) that i think should transport Data in Vlan40.
Needs to be connected to a port that is Untagged Member of Vlan40.If you ie. connect the server to Eth1/0/2 , you have to do 2 things.
1:
Make Eth1/0/2 "Not a Member" of "untagged" Vlan1 , else you can't switch to "untagged" Vlan402:
Make Eth1/0/2 Untagged member of Vlan40 - I would set it to Access Port , not Hybrid.Now the traffic generated from the server in Eth1/0/2 would belong to Vlan40 , and also be forwarded (tagged) on Eth1/0/1 , as you specified that (tagged Vlan 40).
Traffic "Tagged Vlan40" traffic received from pfSense on Eth1/0/1 , would also be copied to Eth1/0/2 , as that port is member of Vlan40. Since the port is an Untagged member , the Vlan40 tagging (not data) is removed before copied to Eth1/0/2 .. As "Normal ethernet data".
Edit:
Why do you have all ports a Untagged member of Vlan1 ??
The default i think ....
That's going to "Bite you" when you want to make any of those ports Untagged member of ANY other vlan. As you have to remove it from Untagged Vlan1 first./Bingo
-
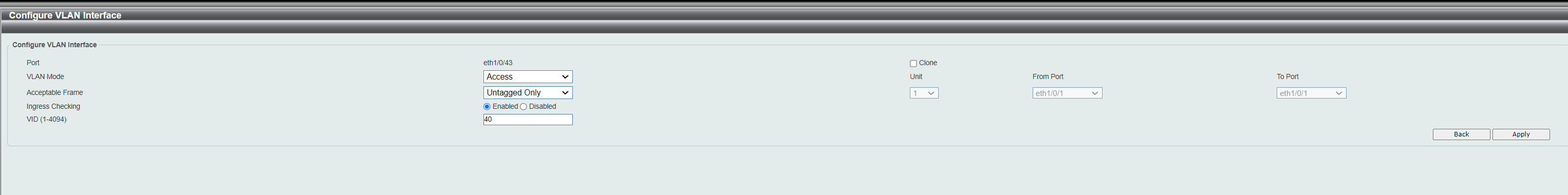
@bingo600 Port 43 is the access port=VLAN40. As indicated here. Once a port is defined as access-port, it locks the port from beeing anything else than Untagged as far as I can tell (I can't even override it and make it anything else). I have my PC connected on port 43.
The caption where it says "40" is Untagged VLAN.
-
@bingo600 said in VLAN on D-link:
Why do you have all ports a Untagged member of Vlan1 ??
The default i think ....
That's going to "Bite you" when you want to make any of those ports Untagged member of ANY other vlan. As you have to remove it from Untagged Vlan1 first.All ports except port 43 is in VLAN1 I would assume. I have some customers on this switch and always been running it without VLAN, so I don't want to take them offline during my trial and error. So it just felt safer to have them there until I know what I'm doing. If I manage to get port 43 locked on VLAN40, I'm pretty confident i can release other ports out of VLAN1 and into a different VLAN one by one :) Just seems like a big way to go just now before I find the smoking gun...
But.. if it is correct above.. then why isn't it working :( I have DHCP active on pfSense VLAN40 and it doesn't give out anything to the PC in port 43. I have the same setup of pfSense as in my lab (where it is working), so I know it is correct setup on pfSense.
-
On the "Snip where you" show Port43 belonging to "Untagged" Vlan40 , what does it aay about Native Vlan , it should show nothing or 40
I would do 2 things ...
1:
Give the PC in P43 a static ip in the pfSense Vlan40 range.
Can you ping from the PC in P43 to the pfSense Vlan40 interface ip addr.
I doubt , but worth a try.2:
Make another port (44 ?) untagged member of Vlan40.
Connect a PC to both port 43 , and port 44 , give them a temporary static ip in the same net ... 192.168.x.10/24 and 192.168.x.11/24.
See if you can ping from one pc to another , if success then both must be in same vlan.Once a port is defined as access-port, it locks the port from beeing anything else than Untagged as far as I can tell (I can't even override it and make it anything else). I have my PC connected on port 43.
That is correct , an access port would be an Untagged member of just one Vlan.
To override make it a member of another Vlan , or make it NON Access first i suppose ... I have never used or seen a D-Link 15xx series.
/Bingo
-
@bingo600 said in VLAN on D-link:
On the "Snip where you" show Port43 belonging to "Untagged" Vlan40 , what does it aay about Native Vlan , it should show nothing or 40
I would do 2 things ...
1:
Give the PC in P43 a static ip in the pfSense Vlan40 range.
Can you ping from the PC in P43 to the pfSense Vlan40 interface ip addr.
I doubt , but worth a try.Under Native, it just shows - instead of any value. Indicating nothing.
Correct, no reply. Tried the other way also, from pfSense to this IP. Will try method #2 now.
-
Once I brougth the two servers into the VLAN40 (both untagged), they could communicate/ping eachother from member ports. When I removed one of them as member from VLAN40, communication between them stopped at once. So we have VLAN isolation from port to port.
I also tried to put an IP in the pfSense-range that I had before (in no-vlan-mode or non-configured) and I couldn't ping pfSense when I was member of VLAN40. As soon as I escaped from VLAN40, I could communicate with internet and the pfSense - including the IP of the interface for VLAN40.
-
@bingo600 One strange observeration though:
Each time I enable "Untagged member" on the 2nd port I tried (port 43), it removed the VLAN "40" under Tagged VLAN on port 1. So now it looks like this:
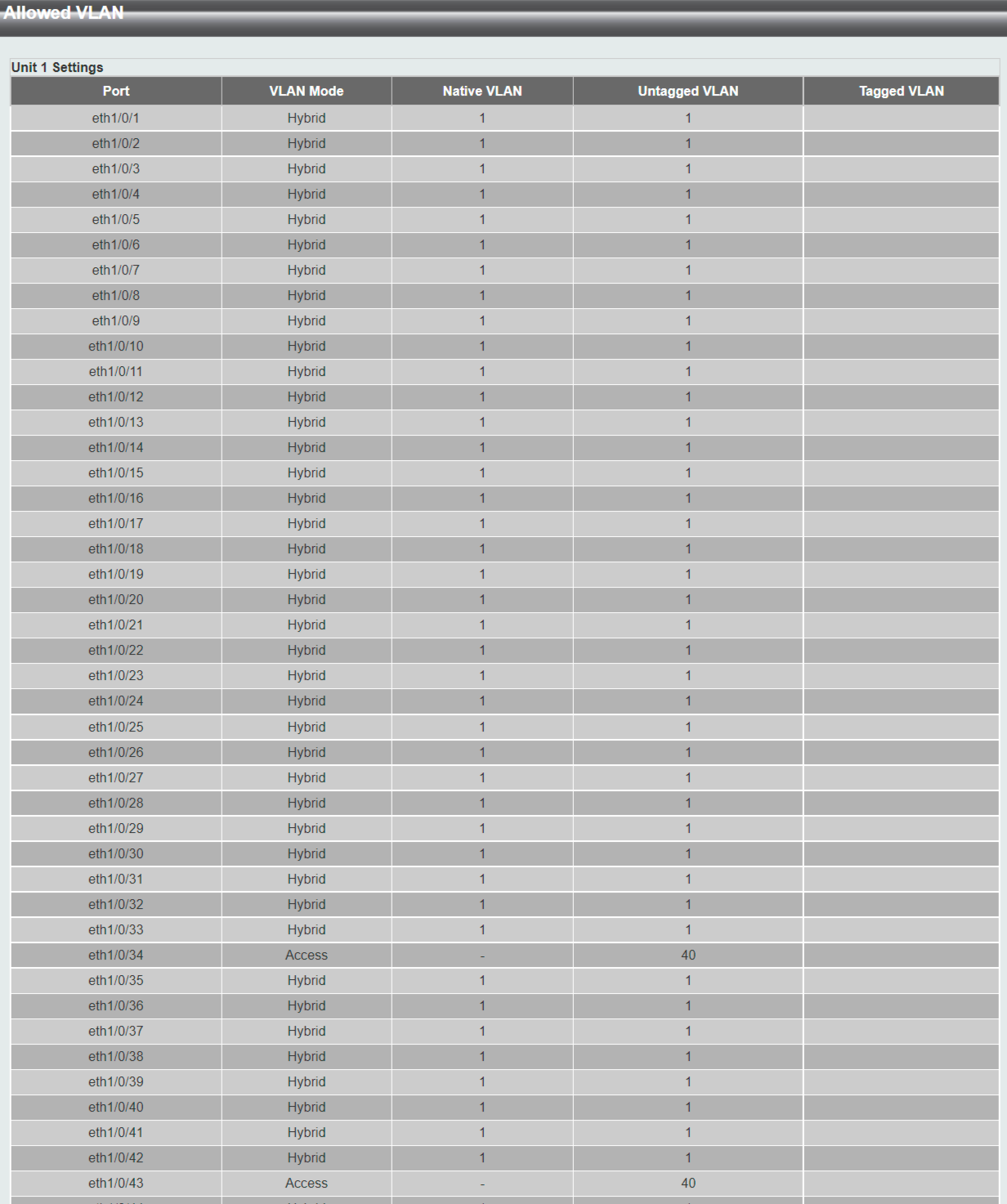
I have put "40" back there on port 1, but it seems like I'm figthing the system and it tries to tell me something!
Here you see the "member port definition" for VLAN40 (if I try to choose Tagged member on port 1, it will not stick, I tried):
And here you see how it just just now, after I corrected so that 40 appear under Tagged VLAN again:
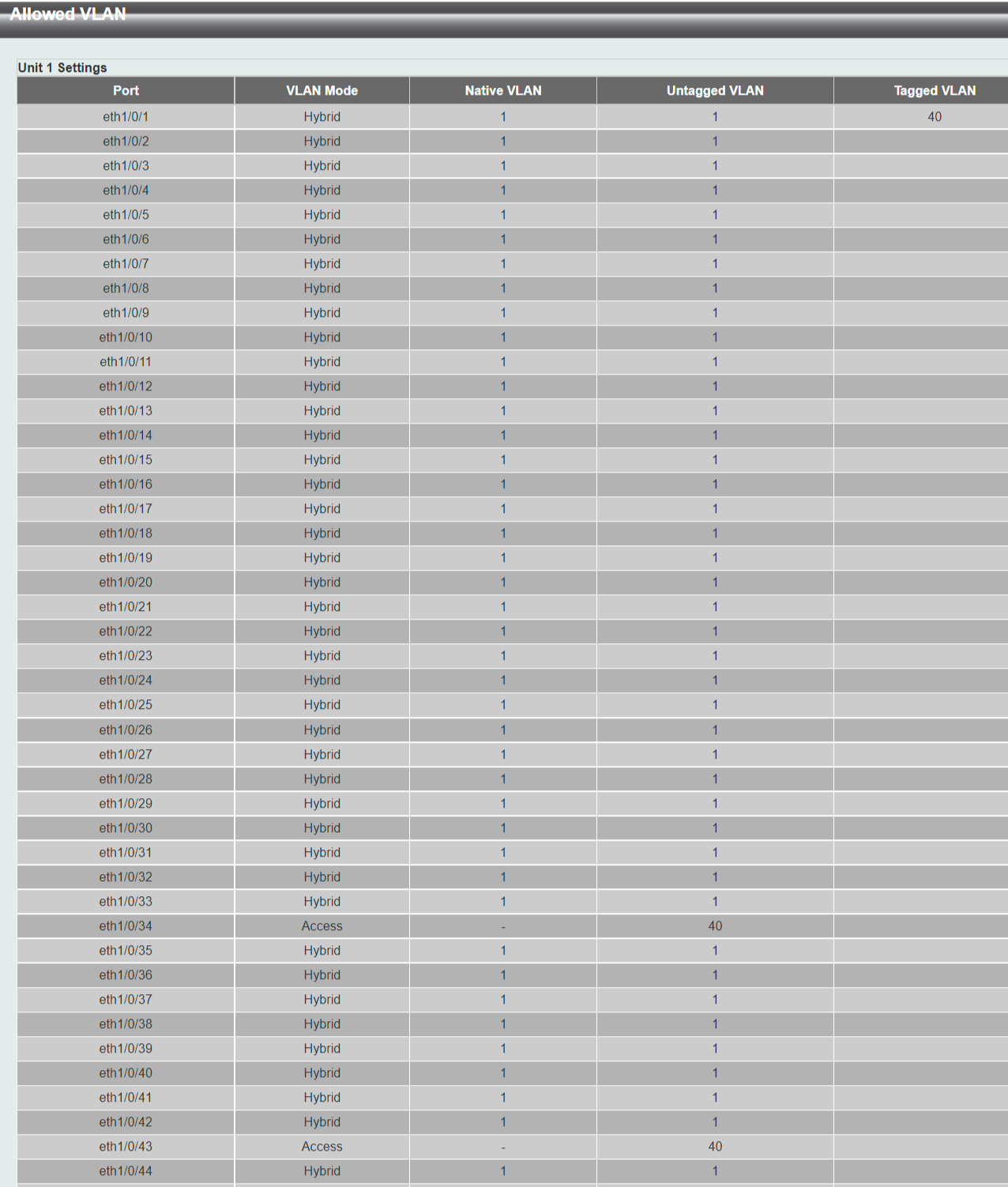
But only communication between ports on VLAN40, I can't communicate with Port 1. In my head, it should have been tagged port, but this interface almost looks the oposite of what I find logic... But you are two people saying it looks normal, so I will go with that for now ;)