IPSec VTI phase2 0.0.0.0/0 bypasses firewall rule
-
Hello everyone, everything good?
It is a pleasure to come back here to count on your support. Many thanks in advance!
I'm experiencing the following problem:
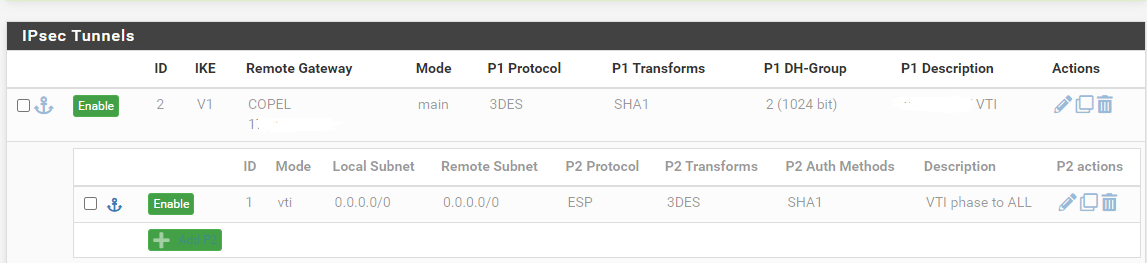
I have an IPSec "VTI" connection with a partner. This VPN already existed in the IPSec model "Tunnel IPV4" but due to an internal demand we were forced to change to VTI.
Before, we had configured several "phases 2" in the Tunnel IPV4 model where we defined, for each phase, a route informing each origin network for each destination network in the partner. We had almost 20 "phases 2" configured and working perfectly.
Now with the "VTI" model we need to configure a "phase 2" only with origin 0.0.0.0/0 and destination 0.0.0.0/0. So we create the interface, routes and access happens normally.
The problem is the side effect this VPN VTI has on my firewall rules. I have several rules on the lan, for example to force traffic from certain hosts to go out through link A or B and when I activate the VPN with this route from 0/0 to 0/0 the rules simply stop working. The traffic still goes through but the gateway that is assigned in the rule no longer works. Now all traffic goes through the default gateway.
A proof of this is that if I create more tunnels specifying the networks, for example, 0.0.0.0/0 to 192.168.1.0/24 and activate the VPN, the firewall rules work again. But this way I can't connect to the remote peer that is configured to receive a tunnel 0/0 to 0/0.
I really need to work with a "phase 2" VTI with the route 0.0.0.0/0 to 0.0.0.0/0, otherwise I can't connect to the other peer.
Could you help me with this?
My pfsense is:
2.6.0-RELEASE (amd64)
built on Mon Jan 31 19:57:53 UTC 2022
FreeBSD 12.3-STABLE -
That is not a valid configuration.
With VTI the P2 addresses are addresses configured on the underlying VTI interface in the OS. Trying to set 0.0.0.0 there is likely stomping all over your route table and doing who knows what else.
The addresses on the VTI interface have zero bearing on what traffic passes over VTI, that's all handled by routing. You would never specify 0.0.0.0/0 anywhere on VTI like you might have on a policy-based tunnel if you want to route everything across it.
-
@jimp Thank's for your time!
Unfortunately, I don't have the experience to discuss VTI in depth. I am grateful for the observation.
However I managed to get my gateway rule working when I set a destination. And to point to the world I use something like "!127.0.0.1". After that the rule started to obey and my LAN started to go out through the gateway described in the rule.
However I'm afraid of the way this is configured, I don't know the impact of this for future cases. My only limitation now is my partner's sonicwall firewall that when he selects Tunnel Interface (VTI) he cannot define "Local Subnet" and "Remote Subnet". It's like it only accepts 0/0 for 0/0.
I did another test that was to configure phase2 with a different "Remote Subnet" with any network that doesn't even exist for us, without changing the sonicwall side and phase2 connects. So it seems that sonicwall's behavior when as a tunnel interface is to accept whatever network I configure on my side. Of course, for it to work I must configure the right networks, but this explanation is just for information purposes. Ahh, and I realized that because before I tried to connect several phases2, one for each network and only one worked. So I did the test above and it worked.
What I'm going to do now is create, together with my partner on sonicwall, several phase2s, one for each network I need to connect, and then try to redo all the phase2s I need by correctly defining the destination networks I need.
I hope it works out like this.
Thanks a lot for your help once again.