Snort fails to install.
-
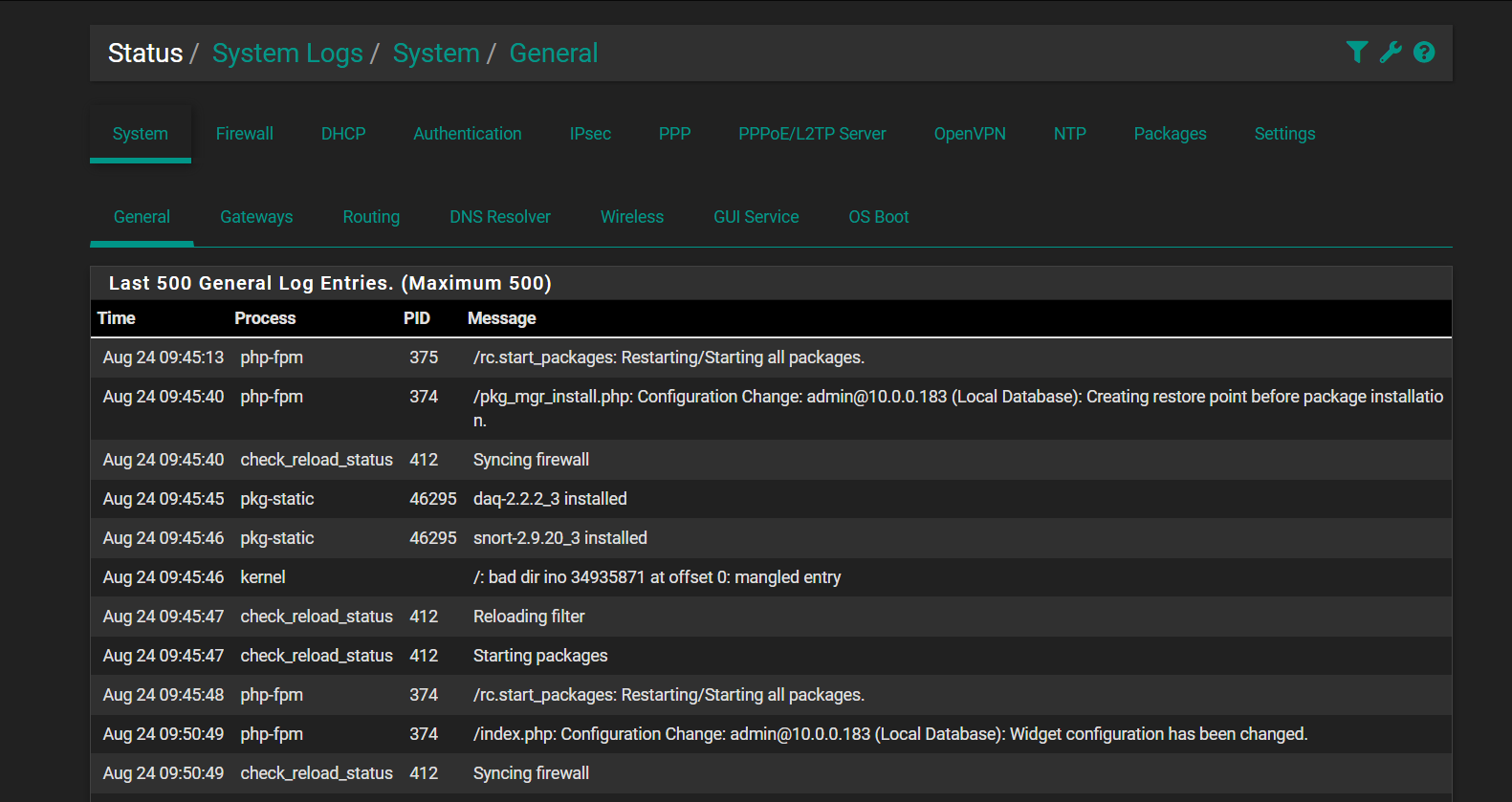
@bmeeks Its starts to log than fails to start
am I in the correct place because its not showing anything?
-
Those
fsckerrors look sort of ugly. If you just bought this box from Amazon, I would strongly recommend taking advantage of their easy exchange service. That disk looks defective. -
@bmeeks Wonderful... could it be a bad install? or is the disk buggered?
and my god this error on this forum is so annoying
As a new user, you can only post once every 120 second(s) until you have earned 3 reputation - please wait before posting again -
@BlueCoffee said in Snort fails to install.:
Its starts to log than fails to start
am I in the correct place because its not showing anything?
You are showing the log entries for the package's installation. That is not related to starting it up. Unless you had a pre-existing Snort configuration on the box, then the package will not be configured and thus it will not auto-start. Manual user configuration steps are required first.
-
After installation on a new machine, proceed to SERVICES > SNORT under the pfSense menu and configure the rules you want to download and use by visiting the GLOBAL SETTINGS tab.
-
Download the initial rules packages by visiting the UPDATES tab.
-
Finally, configure Snort on an interface. I strongly suggest LAN and not WAN. Save the changes you make, then return to the INTERFACES tab in Snort and click the "start" icon. You should see a spinning gear icon for a bit and then either Snort starts or it does not. At that point, immediately open up and view the system log in pfSense. You should see Snort log entries there.
Snort is not to protect your firewall. It's to protect hosts behind the firewall who all talk out using their LAN interface to the firewall. Putting Snort on the LAN has many advantages, and chief among them is that local hosts will have their local IP registered in alerts instead of the WAN's public IP which is what happens when you put Snort on the WAN.
@BlueCoffee said in Snort fails to install.:
could it be a bad install? or is the disk buggered?
Bad install I doubt. Bad disk much more likely. I would exchange it. Those errors do not bode well for longevity.
-
-
@bmeeks said in Snort fails to install.:
t is not to protect your firewall. It's to protect hosts behind the firewall who all talk out using their LAN interface to the firewall. Putting Snort on the LAN has many advantages, and chief among them is that local hosts will have their local IP registered in alerts instead of the WAN's public IP which is what happens when you p
I have done want you said other than the lan part. Ive changed it to lan and still the same will not start.
-
@BlueCoffee said in Snort fails to install.:
and my god this error on this forum is so annoying
As a new user, you can only post once every 120 second(s) until you have earned 3 reputation - please wait before posting again
I've given you 3 "up votes" to boost your reputation to 3. That should prevent the error in the future.
-
@bmeeks Thanks for that.
-
@BlueCoffee:
But immediately after it failing to start, show me what your pfSense system log says.There has to be something there if the process is actually attempting to start. The only time it will fail to log something is if there is a shared library issue. But we proved that is not the case because it starts up enough to show the Snort version at the command line.
Have you configured and used the Snort package on pfSense before?
-
@bmeeks said in Snort fails to install.:
@BlueCoffee:
But immediately after it failing to start, show me what your pfSense system log says.There has to be something there if the process is actually attempting to start. The only time it will fail to log something is if there is a shared library issue. But we proved that is not the case because it starts up enough to show the Snort version at the command line.
Have you used the Snort package on pfSense before?
I have on my last system. not on this new system. (tho I had it on wan for years.)
can fsck try and repair? should I start the whole install of Pfsense again?
-
@BlueCoffee said in Snort fails to install.:
can fsck try and repair? should I start the whole install of Pfsense again?
Yes, the utility can attempt a repair. That usually requires several runs while in single-user mode. Here is the official FreeBSD documentation for
fsck: https://man.freebsd.org/cgi/man.cgi?fsck.And here is the official Netgate documentation on disk repairs: https://docs.netgate.com/pfsense/en/latest/troubleshooting/filesystem-check.html#filesystem-check-manual.
You can try this, but I would be very hesitant to keep this hardware. Having these issues right out of the box is not normal unless at some point you simply removed power abruptly without letting the operating system perform a normal shutdown. pfSense is a computer operating system and needs to be shutdown gracefully. Simply pulling the plug or turning off a power switch will corrupt the file system.
-
And if you decide to perform a fresh install of pfSense, and you did not choose the ZFS option the first time, I recommend installing using the ZFS option when choosing the filesystem. That filesystem is much more resilient in case of sudden power loss. ZFS will be an option in the installer window.
-
@bmeeks ZFS asks me to do raid all the time.
-
@BlueCoffee said in Snort fails to install.:
@bmeeks ZFS asks me to do raid all the time.
No, you do not have to choose RAID. It will let you install to a single disk. Look through the options carefully. RAID is typically used with ZFS, but it is not a requirement that blocks installation otherwise.
Have a look here: https://docs.netgate.com/pfsense/en/latest/install/install-zfs.html.
-
ive installed again (before I had seen your ZFS post and I ran the command again
[2.7.0-RELEASE][admin@pfSense.home.arpa]/root: fsck ** /dev/ufsid/64e75ea55ebb8f0b (NO WRITE) ** SU+J Recovering /dev/ufsid/64e75ea55ebb8f0b USE JOURNAL? no ** Skipping journal, falling through to full fsck ** Last Mounted on / ** Root file system ** Phase 1 - Check Blocks and Sizes INCORRECT BLOCK COUNT I=25721102 (8 should be 0) CORRECT? no INCORRECT BLOCK COUNT I=40224271 (712 should be 704) CORRECT? no ** Phase 2 - Check Pathnames ** Phase 3 - Check Connectivity ** Phase 4 - Check Reference Counts UNREF FILE I=23317317 OWNER=root MODE=100644 SIZE=12462 MTIME=Aug 24 14:51 2023 RECONNECT? no CLEAR? no UNREF FILE I=23317318 OWNER=root MODE=100644 SIZE=12589 MTIME=Aug 24 14:51 2023 RECONNECT? no CLEAR? no UNREF FILE I=24999963 OWNER=root MODE=100600 SIZE=3389 MTIME=Aug 24 14:51 2023 RECONNECT? no CLEAR? no UNREF FILE I=24999964 OWNER=root MODE=100644 SIZE=748 MTIME=Aug 24 14:51 2023 RECONNECT? no CLEAR? no UNREF FILE I=24999965 OWNER=root MODE=100600 SIZE=419 MTIME=Aug 24 14:51 2023 RECONNECT? no CLEAR? no UNREF FILE I=24999966 OWNER=root MODE=100644 SIZE=104 MTIME=Aug 24 14:51 2023 RECONNECT? no CLEAR? no UNREF FILE I=27163420 OWNER=root MODE=100644 SIZE=2228 MTIME=Aug 24 14:51 2023 RECONNECT? no CLEAR? no UNREF FILE I=40224291 OWNER=root MODE=100644 SIZE=0 MTIME=Aug 24 14:51 2023 RECONNECT? no CLEAR? no UNREF FILE I=40624914 OWNER=root MODE=100644 SIZE=0 MTIME=Aug 24 14:51 2023 RECONNECT? no CLEAR? no UNREF FILE I=41666593 OWNER=root MODE=100644 SIZE=6 MTIME=Aug 24 14:51 2023 RECONNECT? no CLEAR? no UNREF FILE I=46554389 OWNER=root MODE=100644 SIZE=553 MTIME=Aug 24 14:51 2023 RECONNECT? no CLEAR? no UNREF FILE I=50480645 OWNER=root MODE=100666 SIZE=0 MTIME=Aug 24 14:45 2023 CLEAR? no UNREF FILE I=50480649 OWNER=root MODE=100644 SIZE=522 MTIME=Aug 24 14:51 2023 RECONNECT? no CLEAR? no ** Phase 5 - Check Cyl groups FREE BLK COUNT(S) WRONG IN SUPERBLK SALVAGE? no SUMMARY INFORMATION BAD SALVAGE? no BLK(S) MISSING IN BIT MAPS SALVAGE? no 26286 files, 459947 used, 119573829 free (3669 frags, 14946270 blocks, 0.0% fragmentation) ** /dev/nvd0p1 (NO WRITE) ** Phase 1 - Read FAT and checking connectivity ** Phase 2 - Checking Directories ** Phase 3 - Checking for Lost Files 6 files, 259 MiB free (16549 clusters) MARK FILE SYSTEM CLEAN? no ***** FILE SYSTEM IS LEFT MARKED AS DIRTY ***** [2.7.0-RELEASE][admin@pfSense.home.arpa]/root:Odd right
-
@BlueCoffee:
Follow the instructions very carefully in the documentation links I've provided from Netgate. Both of them for repairing the disk and installing using ZFS single-disk mode (also called Stripe 0). -
@bmeeks said in Snort fails to install.:
@BlueCoffee:
Follow the instructions very carefully in the documentation links I've provided from Netgate. Both of them for repairing the disk and installing using ZFS single-disk mode (also called Stripe 0).im sending it back mega crash than a flashing screen thanks for the help bmeeks.
-
Yeah, that hardware seems to have some gremlins inside. Exchange is a good idea.
-
@bmeeks could you recommend me one for around 200 pounds? (if you know of any)
-
@BlueCoffee said in Snort fails to install.:
@bmeeks could you recommend me one for around 200 pounds? (if you know of any)
The hardware you provided a link to appears fine for the job. Looks like maybe you just got unlucky and received a unit that should have failed the factory testing before it was stocked and shipped to a customer.
I am partial to Netgate hardware as purchasing that directly funds the continued development of pfSense CE.
But pretty much any Intel 64-bit CPU should work. If you want to use Snort, then you want the fastest CPU clock speed you can get. Snort is single-threaded, so that means no matter how many cores a CPU may have, Snort will only use one of them. In that scenario, faster clocks speeds trump more cores (at least for Snort).
The IDS/IPS packages want either a SSD or an actual spinning disk for logging. They can log so much stuff that a smaller eMMC can wear out quickly. In terms of RAM, anything over 4 GB is suffiicient. 8 GB would be more than enough for home use.
If you want to consider changing, Suricata is multithreaded and can can efficiently use all the cores in the CPU.
-
@bmeeks said in Snort fails to install.:
@BlueCoffee said in Snort fails to install.:
@bmeeks could you recommend me one for around 200 pounds? (if you know of any)
The hardware you provided a link to appears fine for the job. Looks like maybe you just got unlucky and received a unit that should have failed the factory testing before it was stocked and shipped to a customer.
I am partial to Netgate hardware as purchasing that directly funds the continued development of pfSense CE.
But pretty much any Intel 64-bit CPU should work. If you want to use Snort, then you want the fastest CPU clock speed you can get. Snort is single-threaded, so that means no matter how many cores a CPU may have, Snort will only use one of them. In that scenario, faster clocks speeds trump more cores (at least for Snort).
The IDS/IPS packages want either a SSD or an actual spinning disk for logging. They can log so much stuff that a smaller eMMC can wear out quickly. In terms of RAM, anything over 4 GB is suffiicient. 8 GB would be more than enough for home use.
If you want to consider changing, Suricata is multithreaded and can can efficiently use all the cores in the CPU.
Ive gone with the same one getting it tomorrow hopefully all's well with this one.
Are you the guy who made snort? I remember reading some stuff many years ago with that avatar you have.
Also can't believe I've been ruining it wrong all these years.