SSL certs handling and HAproxy
-
Yes, some of the articles configure for http, some for https and some for both. I've tried them all.
I'll double check that the host can respond to http because I've make so many changes.
I'll update shortly. -
The host responds to http requests when using curl but not browsers. Not one browser wants to allow the http connection, even internally.
Second problem I see is that the web site was built using all https links so even when something would connect using http, all links in the sites db are https. So that doesn't work either. This means I need to configure pfsense to use https otherwise this cannot work.
Does it mean I mean one single self signed SSL cert on the server or one for every virtualhost on it?
Of course, re-enabling the certs on the web server gives full access again, directly at least but not via the firewall.
-
Actually, I did another test.
With the certs re-enabled on the web server;
I can connect directly to the web server just fine from any browser on the LAN.
I can connect from public over the Internet, going through pfsense.
That said, as shown above, haproxy knows only about port 80.So, what's happening now?
Is it working because I re-enabled the SSL certs on the server itself?
Is the pfsense cert being used or the one on the web server itself?Update:
When I check the SSL cert using decoder.link/sslchecker/, it shows the date for the cert on the web server, not the newer one on pfsense.
I guess that means that haproxy is not in the middle even though it's configured to be?Confusing.
-
Do you have port forwards on pfSense that are bypassing HAProxy?
-
Yes, I did and I've disabled that now.
From public, nmap shows port 443 filtered so no response what so ever. -
The thing is, if I don't enable the certs on the server, then it won't respond to port 443.
It cannot respond to port 80 because that's forwarded to port 443. -
If 443 shows as filtered that implies HAProxy is not listening on it. Or there are no firewall rules to pass it?
Where are you forwarding port 80 to port 443? That should never happen. You can redirect it to enforce https use but that's not a forward.
-
Wait, you just told me to remove the pfsense port forwards :).
The NAT rules were to forward incoming connections to that virtual IP to the web server LAN IP.As mentioned, I do see HAproxy in the dashboard showing port 80 and it's live.

The 80 to 443 is a redirect in the httpd.conf, forwarding port 80 connections to https.
-
You should not have any port forwards. HAProxy listens on the interfaces directly. You especially shouldn't forward port 80 to port 443 because it always fail. http redircets are OK but you should not have them here because HAProxy is connecting with http.
-
I've tested with all combinations as mentioned in this post.
I've had the server set to http only without redirects and both http and https but nothing gets to it.I'm a little confused about the port forwards now however.
I've had haproxy load balancing web servers for years and those have NAT rules to allow incoming traffic to get to the servers.
It must be working, I've seen countless times where we'd had a server or two down and the others were taking connections. -
Forwarding to a pool perhaps? If you have NAT rules on WAN forwarding traffic to the servers then HAProxy never sees that traffic. Maybe those rules are not actually matching the traffic. Or they are forwarding traffic to some address on the firewall where HAProxy is listening, which would be unnecessary.
What are those NAT rules?
-
I'll try to explain how things are set up then.
I have frontend and backend set up for three web servers for example.
I see haproxy showing all three servers in the dashboard.
If one server goes down, it shows in the dashboard.
If I reboot one of those servers, the others get the traffic.The NAT rules are for taking incoming public 80/443 connections to a virtual IP and sending that traffic to the web servers.
The web servers are also defined in an alias which has the three LAN IP addresses for them.Does that explain it?
-
If those NAT rule are catching incoming web traffic on both ports 80 and 443 and forwarding it to the internal server IPs directly then HAProxy never sees it.
You should not have any port forward rules. HAProxy should be able to listen on port 80 and 443 on that virtual IP directly.
-
How does the firewall know to send the incoming connections to the three web servers then? I've always had that rule.
The NAT IP is set to the alias I mentioned and it works.Of course, I learned that setup from reading many articles so now I'm even more confused that that has been working.
-
@lewis said in SSL certs handling and HAproxy:
How does the firewall know to send the incoming connections to the three web servers then? I've always had that rule.
The NAT IP is set to the alias I mentioned and it works.What I mean is that the IP for the destination web server is the alias that has three IPs in it. I see traffic to all three web servers.
-
that's what a frontend is need for
443/80 -> wan -> Haproxy frontend -> haproxy backend
no nat is needed
if the ip you mentioned are virtual ip of pfsense you just need to cconfigure haproxy to listen to that ip
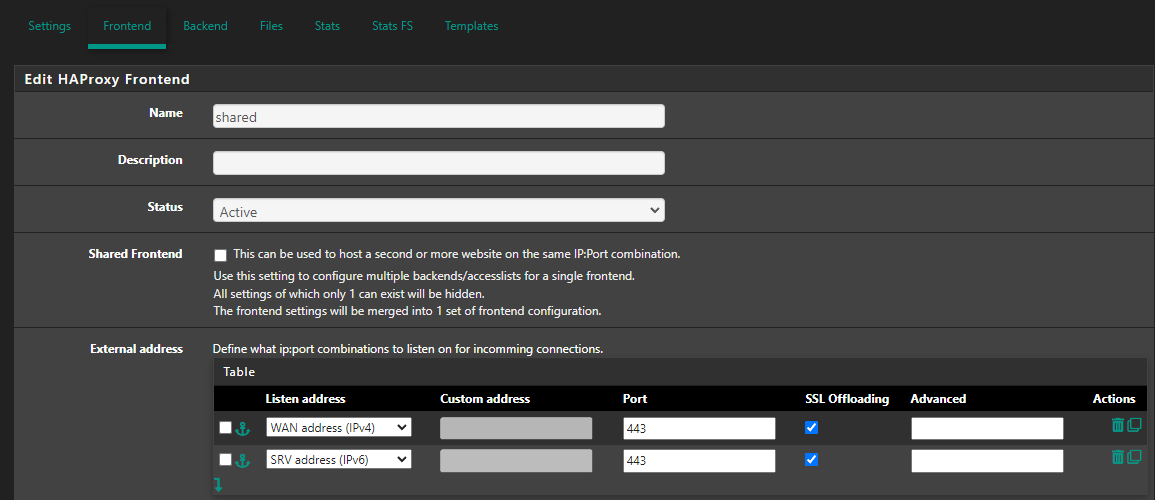
Listen adress
-
Yes, I've understood all that's being said but why does it seem that it's been working as I've explained above?
Yes, HAproxy is definitely listening on the correct interface so I'm there in terms of that part.Also, I cannot change that until I can solve the SSL issue since the web servers are using their SSL cert over a SAN share.
I need to solve the issue with being able to use pfsense, ACME and HAproxy then I can fix this new thing that's come up.So, if we can focus on getting just one web server working with ACME/HAproxy, that will show me how to do the rest.
-
Do you actually see any traffic in HAProxy in other installs though?
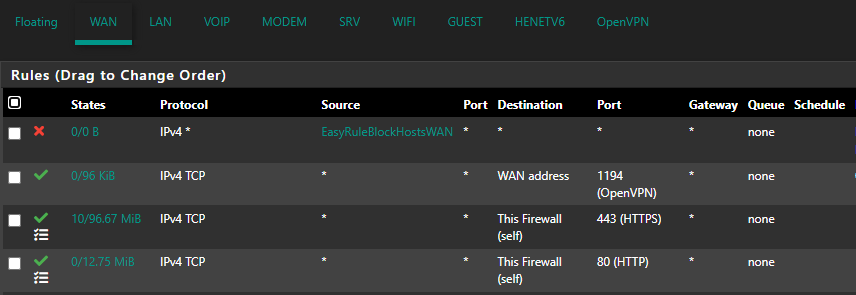
You need firewall rules on WAN to allow traffic to HAProxy of course.
I imagine it's working by just bypassing HAProxy on other systems. But then you don't get any of the HAProxy features like SSL off loading.
I would approach this the other way. Remove the forwards and get HAProxy functioning in a basic form before adding back the SSL features. Whatever testing you have done until now appears to be invalid since nothing was actually hitting HAProxy.
Unless we have misunderstood your description of those NAT rules. You have a screenshot?
-
Do you actually see any traffic in HAProxy in other installs though?
I don't have haproxy on any other install, just this one firewall.
You need firewall rules on WAN to allow traffic to HAProxy of course.
I had NAT rules but now I'm told those aren't needed, HAproxy knows about the incoming traffic over the selected interface.
I imagine it's working by just bypassing HAProxy on other systems. But then you don't get any of the HAProxy features like SSL off loading.
This is the first time I'm trying to use ACME on the firewall. HAproxy is in use to load balance web servers. That's always worked.
I would approach this the other way. Remove the forwards and get HAProxy functioning in a basic form before adding back the SSL features.
I'll have to set it up as a test on another pfsense as I cannot disrupt services on this one I've been trying to get working.
Whatever testing you have done until now appears to be invalid since nothing was actually hitting HAProxy.
But the weird thing is, I do get fail over. And more than that, the IP for the rule was set with the alias that has three web servers and all three get traffic so, something else is goofy here.
Unless we have misunderstood your description of those NAT rules. You have a screenshot?
Where do I start? I'll get back on this tomorrow and nab a bunch of screen shots.
-
Ah, sorry I thought you meant you had other installs running with HAProxy.
Ok so disable or remove those NAT rules. Make sure there are firewall pass rules to allow the incoming traffic to access HAProxy. Check the HAProxy status to see what's happening.
Grab screenshots.