Why do I need TS installed on pfsense router?
-
@chudak those are all about clients behind pfsense making their own TS connections, I have none of those.. I allowed the 41641 port to my wan that is it..
-
@johnpoz said in Why do I need TS installed on pfsense router?:
@chudak those are all about clients behind pfsense making their own TS connections, I have none of those.. I allowed the 41641 port to my wan that is it..
TCP/UDP on 41641 on WAN?
-
-
@chudak mine is set for UDP only - I set it up long time ago.. I must of looked to see what they require.. But Its working.. If I connect my phone from sell it shows direct connection and my rule shows a state.
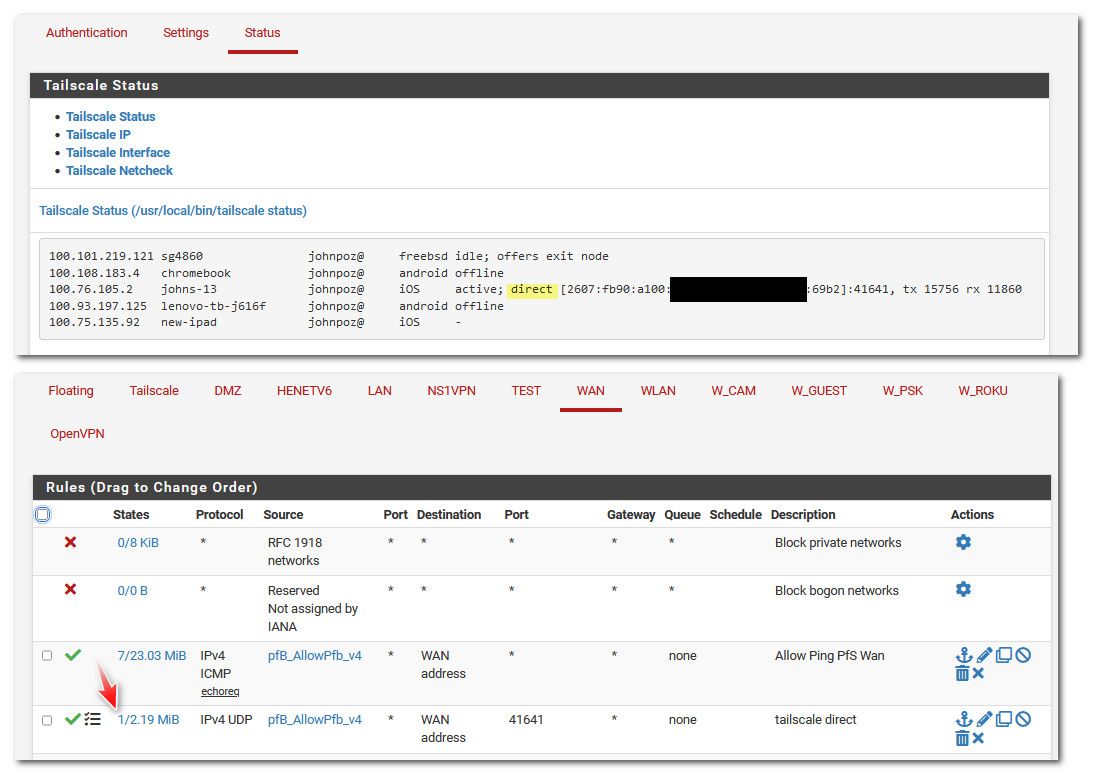
My phone on cell only gets IPv6, but t-mobile converts it to IPv4 when connecting to IPv4 stuff.
-
@johnpoz said in Why do I need TS installed on pfsense router?:
@chudak mine is set for UDP only
Changed my to UDP only and confirmed it still works fine
-
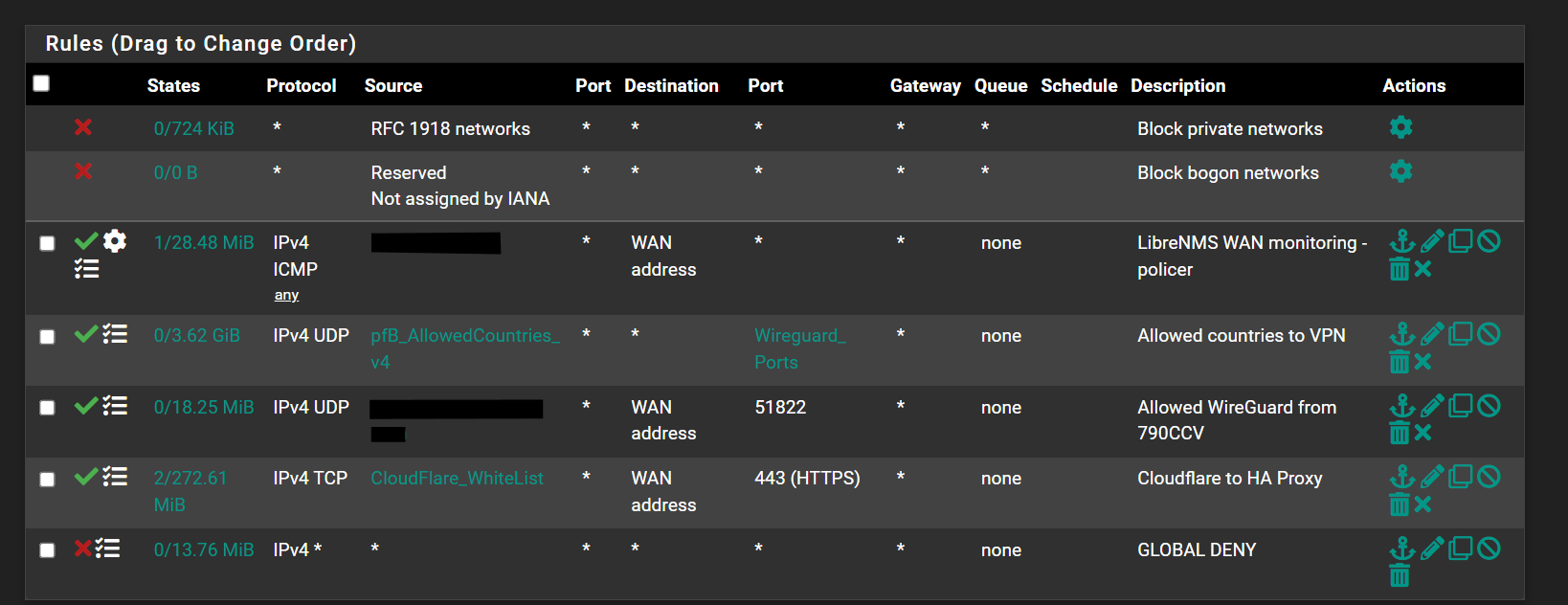
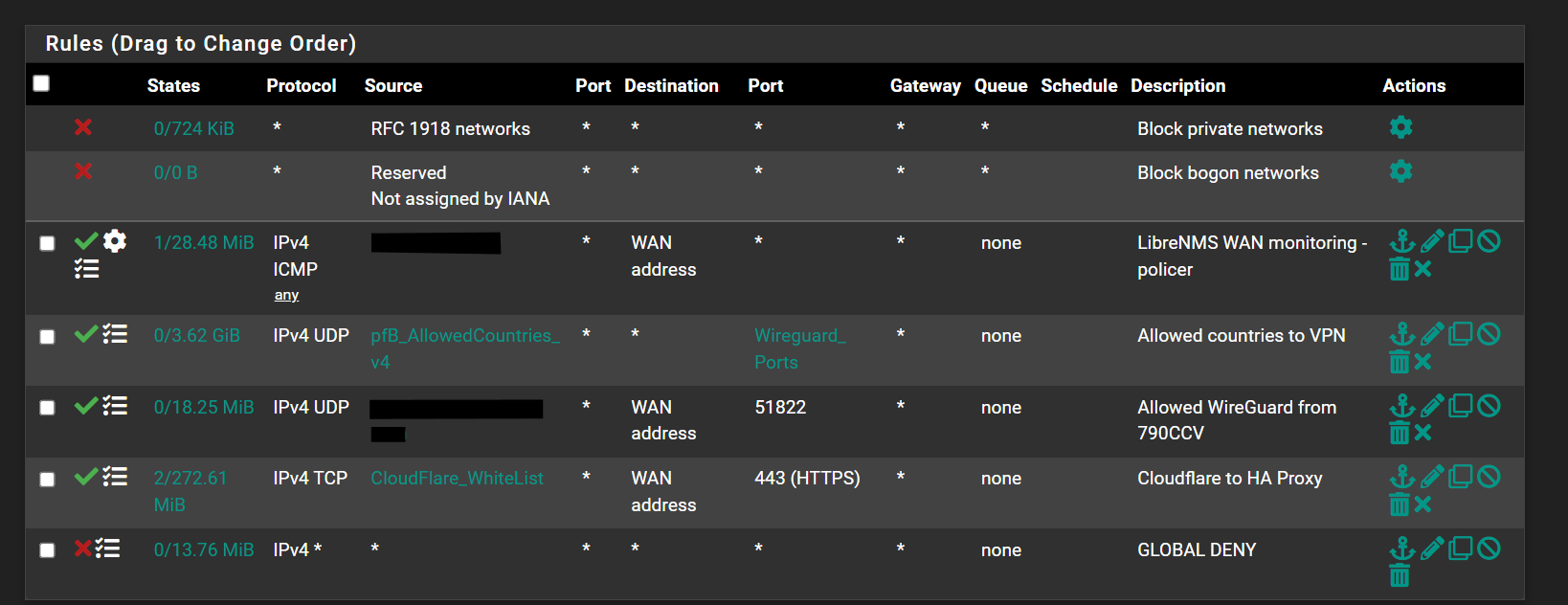
For what its worth i do not have the TS port open on my WAN side and im able to make direction connection and access all LAN resources.
The snippet is from my phone on LTE.

WAN rules
-
@michmoor said in Why do I need TS installed on pfsense router?:
For what its worth i do not have the TS port open on my WAN side and im able to make direction connection and access all LAN resources.
The snippet is from my phone on LTE.

WAN rules
Also confirmed
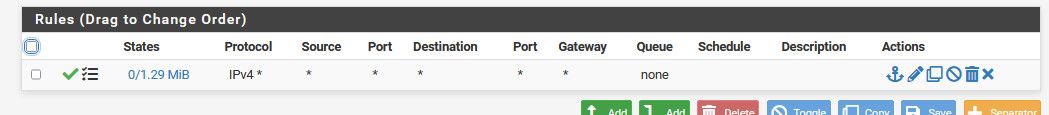
I disabled the open port 41461 rule and still see everything working fine.But you do have a rule on the TS interface, don't you? As here:
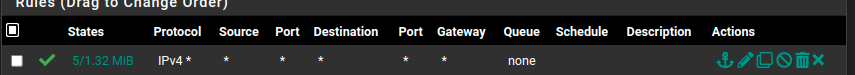
that seem like a must to have
-
@chudak I am pretty sure it uses stun to get through the nat. But its better to on purpose open it so you can view it, etc.
-
@chudak
TS rules are not required if accessing resources on your LAN. The reason is all in how TS and FreeBSD work out the routing. Essentially the most direct interface out to your LAN will be your source IP.
For example, if your LAN gateway IP is 192.168.1.1 then when you access a server on that LAN from TS, the server will see incoming requests from 192.168.1.1.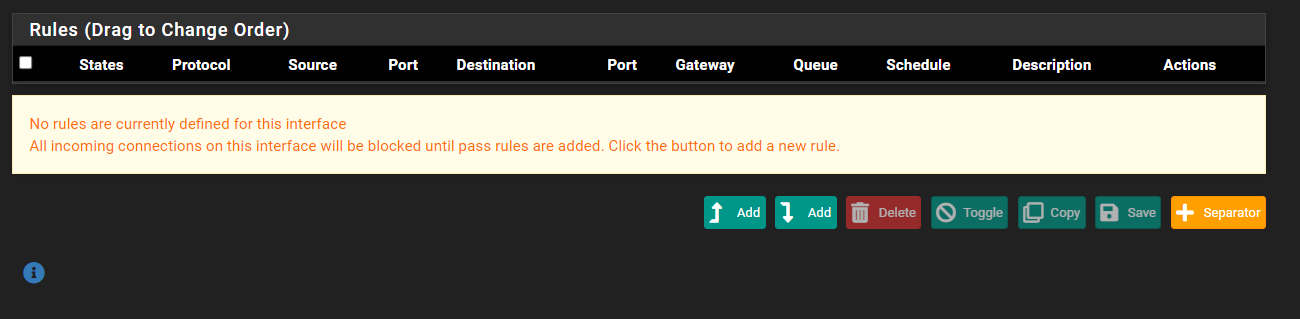
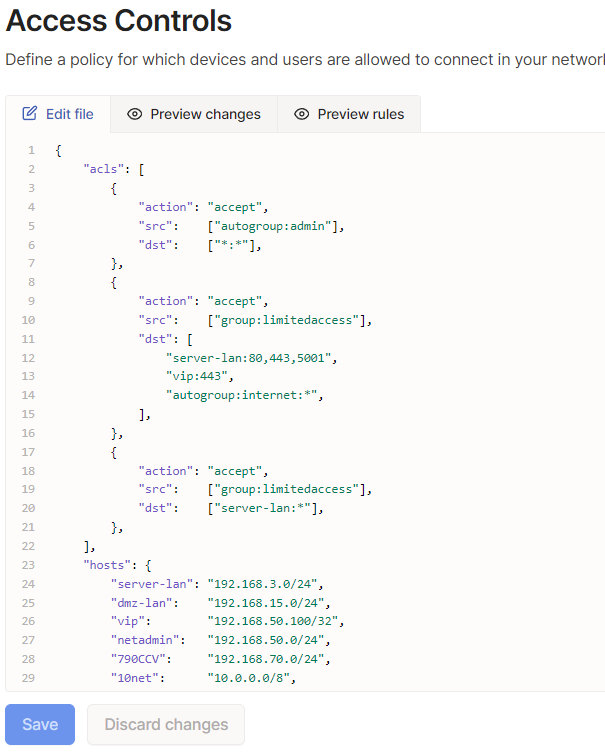
IMO, i do not like the implementation of TS on the firewall for this very reason. ACLs must be done on the TS controller but require you to write it in JSON. Its not difficult to write but its cumbersome. The default ACL on Tailsale is 'any-any' which is why communication works out of the box so to speak.
If this is for remote access to your home then no biggie but i would highly advise not to use this for any business deployment.Here are my ACL rules which work in my limited environment i am using this.
-
@michmoor I by any means not a tailscale expert or even user.. I have it up and running, it works - but I don't normally use it. if I need to remote in I use openvpn as my go too.
But if rules are not needed on the interface - why is showing traffic when was testing if could access pfsense web gui, doing some pings, etc..
-
@johnpoz
Traffic from your Tailnet is trying to hit your Tailnet IP assigned to the interface on your pfsense.
If i try to access my pfsense tailscale IP or try to ping it from my tailscale device like a laptop it fails because i dont have firewall rules on the interface. But you dont need it to access your LAN anyway so rules arent required. What im saying is that its not required to access your pfSense over your tailnet.I believe its all outlined in these two videos.
https://www.youtube.com/watch?v=Fg_jIPVcioY&t=1315s
https://www.youtube.com/watch?v=P-q-8R67OPY&t=923s -
@michmoor said in Why do I need TS installed on pfsense router?:
If i try to access my pfsense tailscale IP
Exactly - which is what he was trying to do, use his tailscale IP.