1 WAN interface, 3 LAN interfaces, OpenVPN allow communication to all networks
-
@jg8000
As I wrote above, I don't really believe, that it's pfSense, which is prohibiting you from accessing the devices. -
@jg8000 said in 1 WAN interface, 3 LAN interfaces, OpenVPN allow communication to all networks:
I am using the built in OpenVPN server, I’m just using a different subnet for VPN connections.
That's fine and would be required. But in your first post you showed the VPN subnet conflicting with one of the LANs. Re-reading that though I think it's a typo?
192.168.1.50.0/24Is that in fact 192.168.50.0/24? Which would be fine.
-
Yes it could well just be the hosts rejecting traffic from outside their subnet.
Can you ping the interface address (.1) from each subnet from the VPN clients?
-
Yes, I can ping .1 on each subnet
-
Ok so try to ping something on of the other subnets you think should respond; leave the ping running.
Check the state table in Diag > States. Filter it by that ping target and make sure you see the expected two states. One on the VPN and one on the internal interface.
Steve
-
thanks, I tried that for 2 subnets. State is 0:0 and packet number grows on the VPN client side but not on the other, for both. I allow any so icmp should get through.
Maybe the issue is elsewhere, I'll try and get a console up on the machine that I expect to be up.
-
Can you grab a screenshot of that?
-
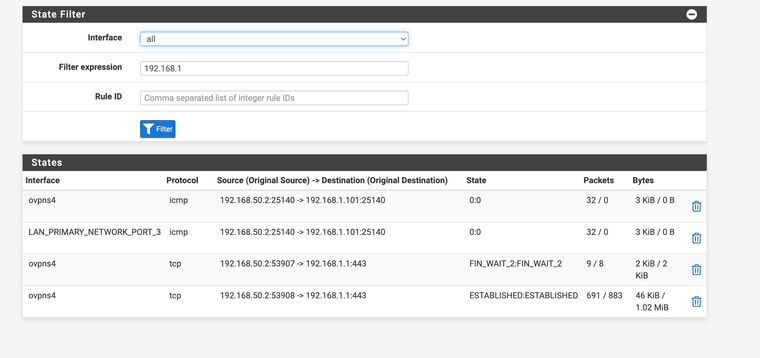
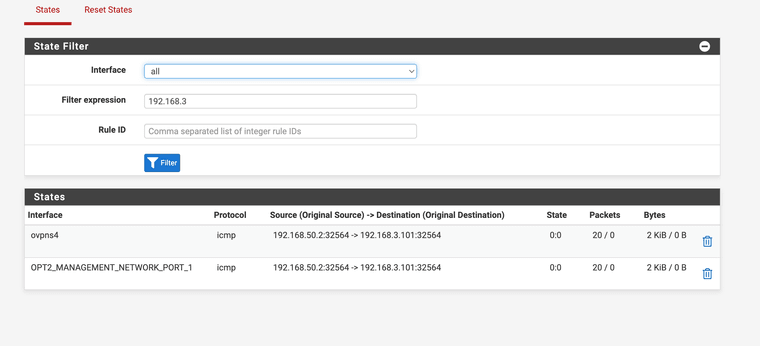
-
Ok, so in both cases that ping is coming in the VPN and leaving the internal interface correctly but no replies come back.
So either the target devices are not replying or the replies are not coming back to pfSense. More likely they just don't reply to pings from outside their own subnet because of local firewall restrictions.
What are those target devices?
-
Thank you for your help.
I have duplicated the issue on a separate setup.
I have 3 interfaces setup:
WAN
LAN: set to static 192.168.1.1/24
OPT1 - set to static 192.168.2.1/24
I enabled DHCP for both, and setup a windows client on each LAN. I don't have OpenVPN on this setup but I think the problem is similar.
The machines can't ping each other. They both get DHCP addresses, I can ping the statically assigned interface IP, access the pfsense admin .1 address from each client. I can even get to the other interface .1 pfsense login from each client.
But I can't get them to ping each other.
I don't understand what I'm doing wrong.
-
Ok, you are correct. It was the local firewall restricting the response. I turned off the local firewall and I can now ping. I did not try other services yet.
The real world scenario is access the LAN via ssh from the VPN Net, and to access the IMPI/iLO also.
Right now it's not working, can't access ssh or ping, it's Rocky 8/9 so a firewall could be the issue. Not sure about iLO, it should be accessible via https but that isn't working either.
-
You can work around it with an outbound NAT rule so traffic appears to be sourced from the pfSense interface address.
But a cleaner solution is to add rules on the targets to allow the access.
-
Thank you, so if I wanted to add an Outbound NAT rule to make it seem like the traffic is originating on the same subnet, how can I set this up?
If I come in via VPN on 192.168.50.0/24 and want to connect to 192.168.3.1/24 how is the rule configured?
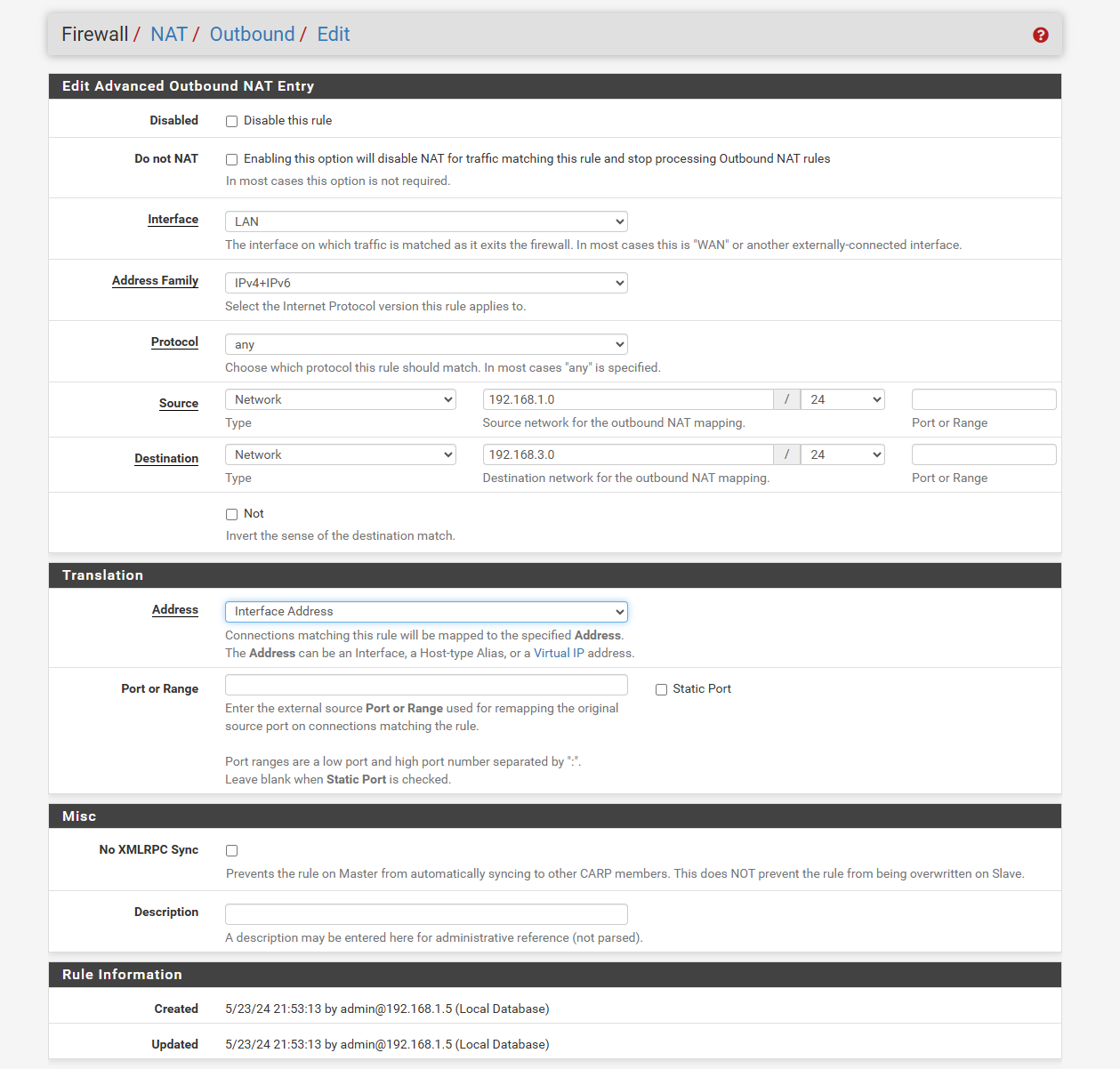
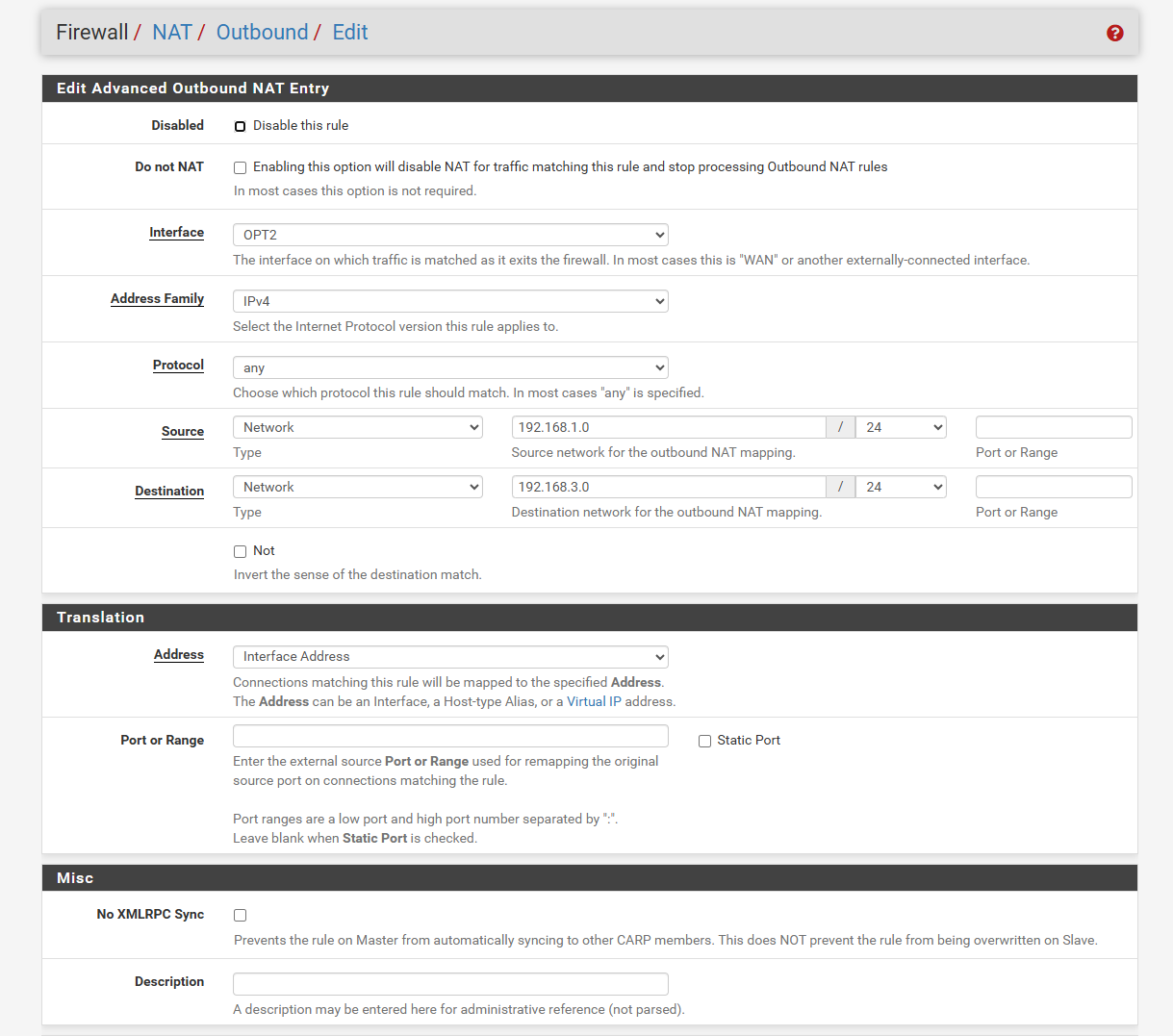
This is my attempt on my test bench trying to get to an IPMI device on 192.168.3.101 (OPT2) from 192.168.1.5 (LAN). I can get to IPMI only if I configure the network port to be on the 192.168.3.1/24 (OPT2) interface
-
That rule will work if you put it on the OPT2 interface. It gets applied outbound on the interface so must be on OPT2.
-
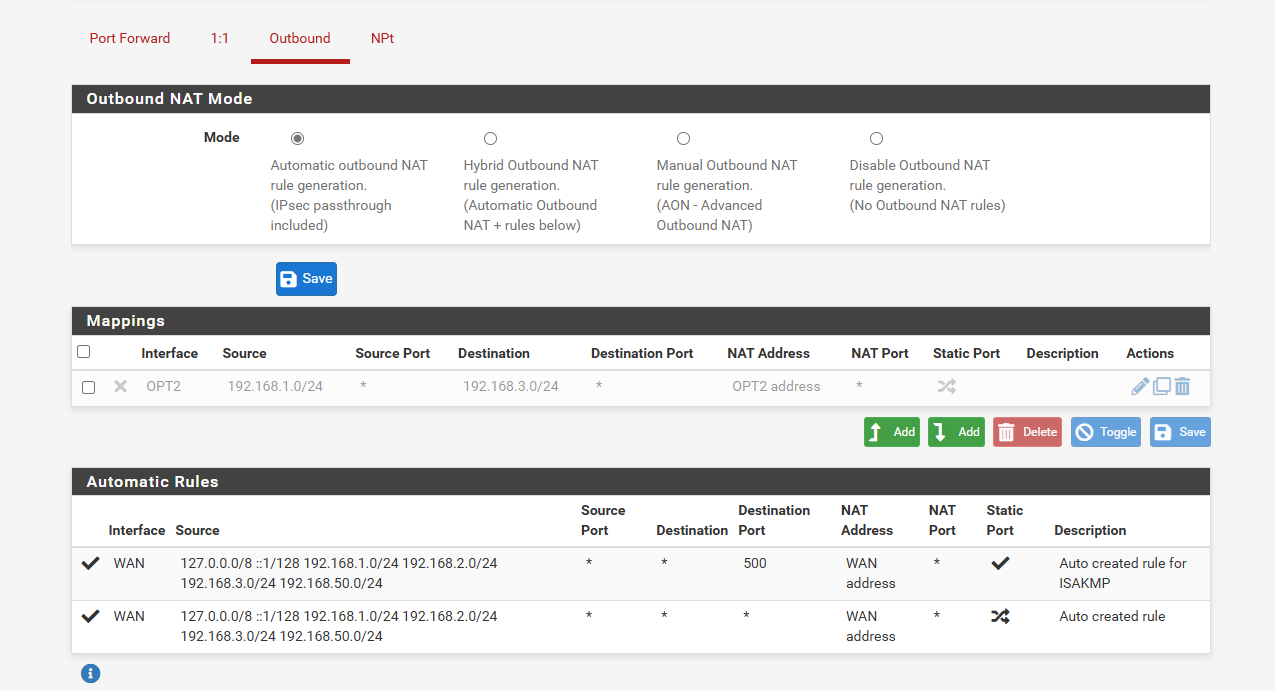
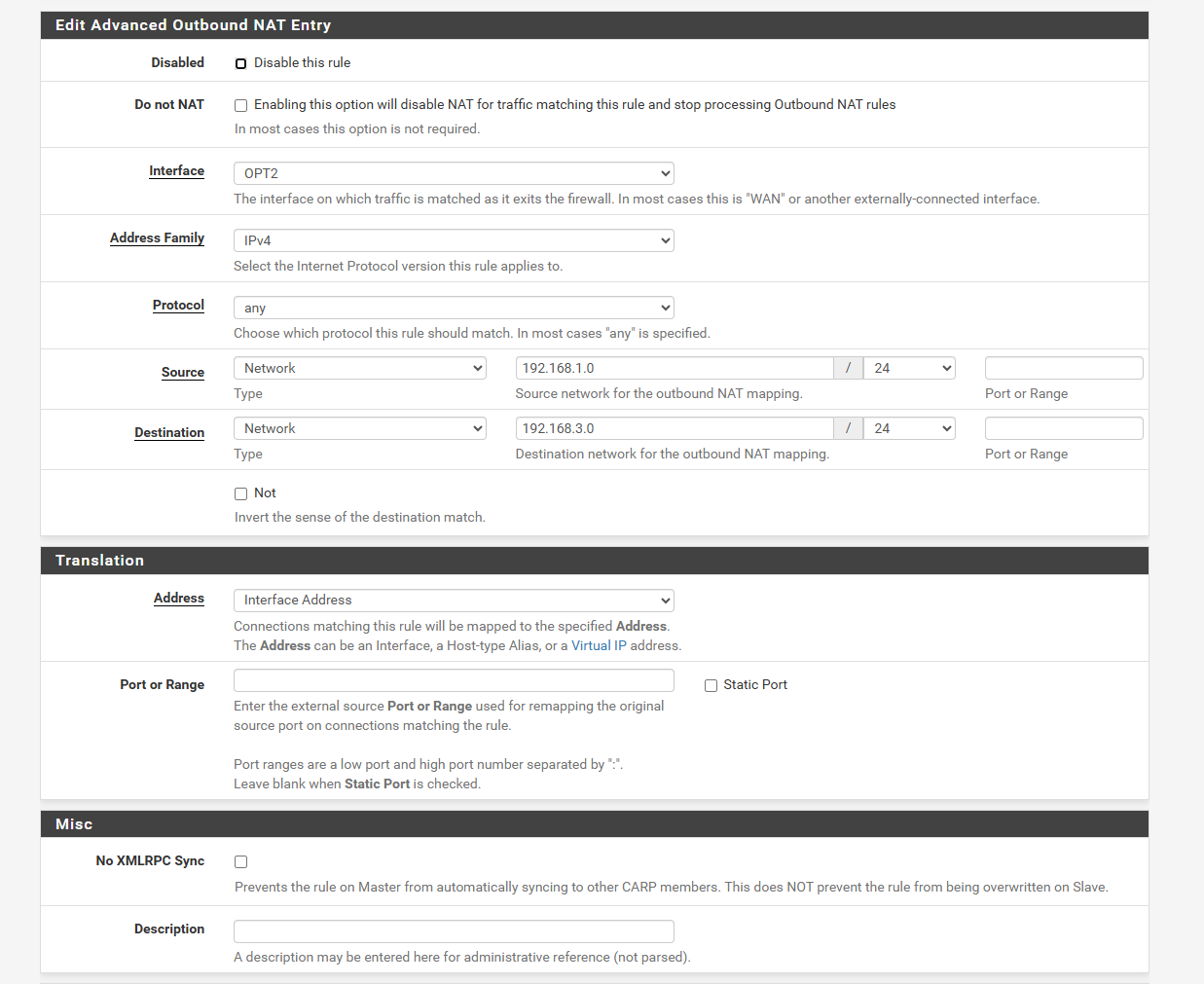
Should the rule be greyed out like this? I still can't get it to go, I changed the interface to OPT2. My test client is on the LAN interface (192.168.1.5)
-
Oh sorry you need to set outbound NAT to hybrid or manual to apply user rules. I suggest hybrid so auto rules are still updated.
-
@stephenw10
Thank you, it's no longer greyed out but still not working.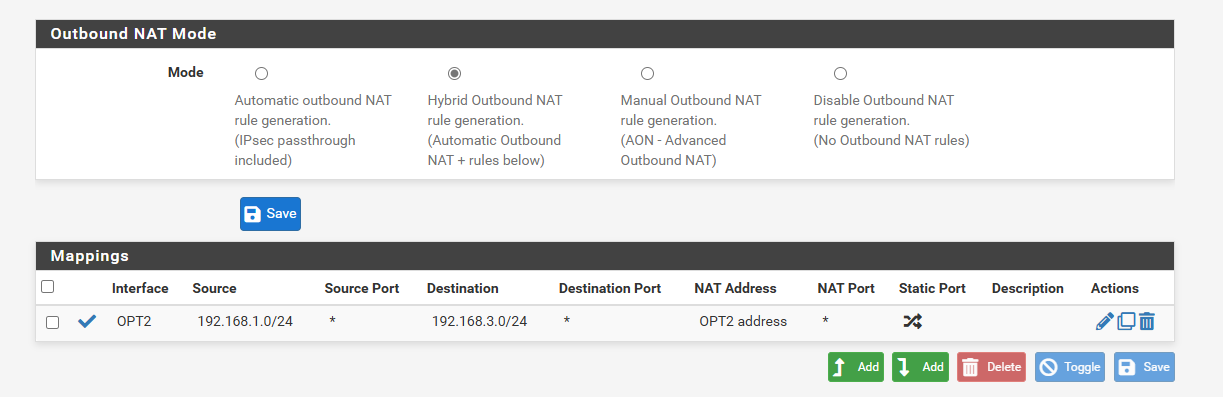
The idea is for (LAN) 192.168.1.5 to access (OPT2) 192.168.3.101 as if it were on the 192.168.3.0/24 subnet. Do I need to specify port ranges or anything? I hope not.
I can verify access by switching from (LAN)192.168.1.5 to (OPT2) 192.168.3.5 on the windows test client and accessing the web IPMI interface.
-
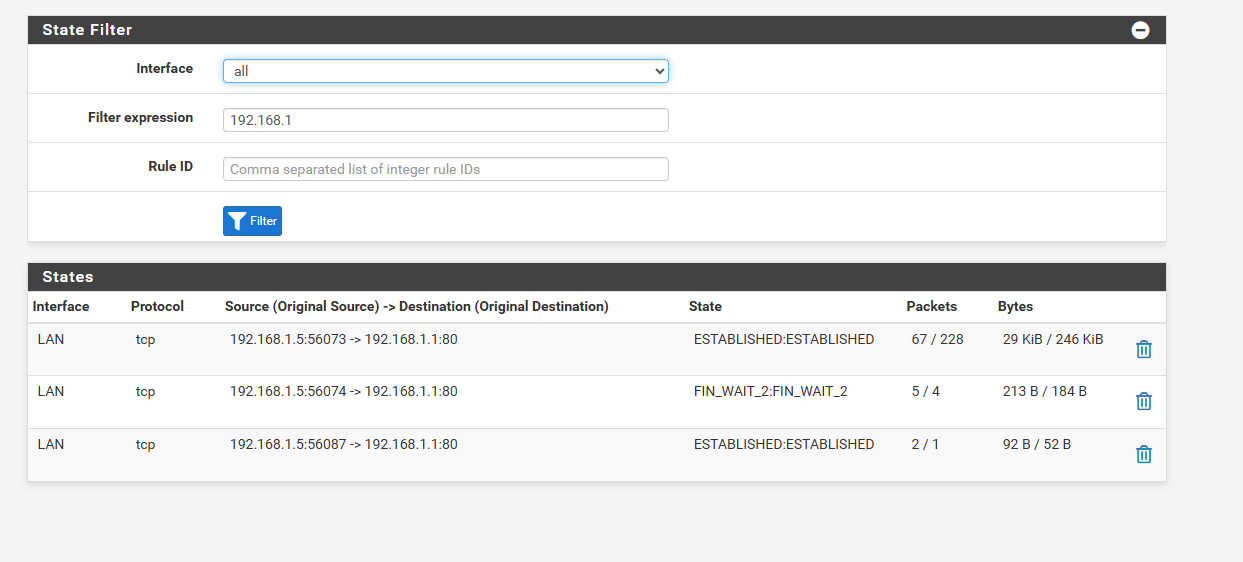
Check the state table again. You should see the translation on the OPT2 state.
-
I only see activity from 192.168.15 to the pfsense admin web admin. Nothing for 192.168.3
-
@jg8000 said in 1 WAN interface, 3 LAN interfaces, OpenVPN allow communication to all networks:
I can verify access by switching from (LAN)192.168.1.5 to (OPT2) 192.168.3.5 on the windows test client
How exactly are you making that switch? Does that client have NICs in both subnets? If so it's probably not sending traffic through pfSense at all.