Safari in Iphone is bypassing FIrewall rule
-
This post is deleted! -
@johnpoz I’ve set up firewall rules in pfSense to allow only WhatsApp traffic. The iPhones on my network get their DNS settings from our distribution switch, which uses Google’s public DNS (8.8.8.8).
Here’s the behavior I’m observing:
If I block 8.8.8.8, Safari on iPhones is unable to access the internet, and only WhatsApp works, which is the desired outcome.
However, blocking 8.8.8.8 also prevents Android phones from accessing WhatsApp.
If I allow 8.8.8.8 in the firewall rules, Android phones can use WhatsApp as expected, but this also allows Safari on iPhones to bypass the firewall rules and access the internet.anyone encountered something similar or have suggestions on how to resolve this? My goal is to allow only WhatsApp traffic while blocking all other internet access consistently across devices. Any help would be appreciated!
-
@mozmail doing something with dns has really little to do with firewall rules.. Post up your firewall rules, do you have any in floating?
If you think dns should only allow xyz, your going to find out that devices like to use their own dns, doh - that could bypass whatever it your wanting block or allow with dns.
Doing dns filtering is a tool in the toolbox - but blocking traffic or allowing traffic still comes down to the IPs and and the ports.
If your firewalls allow port 443 for example - you can block all you want with dns, doesn't matter if the application or device is using doh (port 443 over tcp) to look up want it wants.. Now you have no control over this device talking to whatever it wants via 443, because your firewall rule allow traffic to the internet on 443..
Doh pretty much makes dns filtering impossible if the device is not using your dns you filter at.
edit: and no not going to watch some video that is 7 minutes long with some guy that can't even be bother to put together some screenshots and info on what he is doing that would take like 30 seconds to read vs listening to him go over something.
He can put up a hour video if he wants - but where are the rules, what are the settings.. This info should be in the comments of the video. He really must be someone special - he has 80 subscribers ;)
edit: per this I found in a 2 second google it needs port 5222 and 443
https://developers.facebook.com/docs/whatsapp/guides/network-requirements/
If 443 is open, so is doh.. ie dns if the client/app is using that. If your just trying to whitelist some domains. And block everything else.
It lists a bunch there that are wild cards and hosted by what I would expect are CDNs..
.*.cdn.whatsapp.net g.whatsapp.net graph.facebook.com graph.whatsapp.com media-.*.cdn.whatsapp.net media..*.fna.whatsapp.net mmg.whatsapp.net pps.whatsapp.net static.whatsapp.net v.whatsapp.netDns filtering of those can be quite challenging, either allowing stuff you don't want or not allowing what you need too, etc.
The only to honestly work with domain or fqdn based filtering be it allow or deny is what a proxy.. How exactly are you suppose to get IPs from something like media-.*.cdn.whatsapp.net, so your firewall can allow or deny whatever that is, etc..
One of the things it ends up pointing to via a cname is
mmx-ds.cdn.whatsapp.net. 60 IN A 57.144.175.32
This has a ttl of 60 seconds.. It is quite possible that IP could change 60 seconds later, etc.. So how do you create IP rules to allow that, when the IP can change so quickly.
Also CDN hosted stuff can return different IPs depending on what region of the world your in..
Your best bet to locking to only something like that would be to monitor traffic from a client when using something like such an app is to monitor its traffic when using it, and allow only what the application uses for IPs and ports, most likely you will have to allow for netblocks or whole ASNs - which in turn could host other stuff.. And you will prob miss something, so something might not work. Or might work today but not work tomorrow.
-
@mozmail said in Safari in Iphone is bypassing FIrewall rule:
Here’s the behavior I’m observing:
If I block 8.8.8.8, Safari on iPhones is unable to access the internet, and only WhatsApp works, which is the desired outcome.
However, blocking 8.8.8.8 also prevents Android phones from accessing WhatsApp.
If I allow 8.8.8.8 in the firewall rules, Android phones can use WhatsApp as expected, but this also allows Safari on iPhones to bypass the firewall rules and access the internet.anyone encountered something similar or have suggestions on how to resolve this? My goal is to allow only WhatsApp traffic while blocking all other internet access consistently across devices. Any help would be appreciated!
If the behavior you described above is correct, here is what I would guess could be happening: https://support.apple.com/en-euro/102602. The link describes Apple's iCloud Private Relay service. This essentially is a sort of VPN over port 443. My guess is that Private Relay needs to be able to look up the IP for the Private Relay host, and so when you block 8.8.8.8 it can't find the Private Relay host. That would mean web browsing can't work because it can't do a DNS lookup. Unblocking 8.8.8.8 lets the iPhones perform their DNS lookup (probably via encrypted DoH) to 8.8.8.8 so they can query for the Private Relay Host. They find the host's IP address and connect to it over port 443, and then the iPhone user has a VPN connection bypassing your firewall rules (because you must allow port 443). Private Relay also uses the new QUIC protocol, which is UDP. Have you blocked UDP on port 443?
Of course it's also perfectly obvious that the clients can use 8.8.8.8, when not blocked, to look up any website IP and then connect straight to it via the open 443 port using TCP. Have you tested when 8.8.8.8 is unblocked that your Andoid devices are still restricted to only WhatsApp? I'm thinking they will have free reign on the web as well if 8.8.8.8 is available for DNS lookups and TCP port 443 is open. Those two requirements are all you need to browse today's Internet: the ability to contact a DNS server and an open port 443 over TCP (and UDP for QUIC).
Some follow-up searches on Google reveals that Android can only do DoH with Google and Cloudflare DNS servers. That's why when you block 8.8.8.8 the Android devices can't use DoH. Apple devices can apparently query an Apple DoH server, though. That's probably why the iPhones can find WhatsApp with 8.8.8.8 blocked. The iPhones can use DoH (over port 443) to perform the required DNS lookup on the Apple DNS server and then connect to WhatsApp over the open ports. Android devices can't find the IP address of WhatsApp over DoH when the Google DNS server (8.8.8.8) is blocked, because 8.8.8.8 is their "go-to DNS server" for DoH.
-
I learned something about my own phone

Thanks for the warning about iPhone sending all traffic over some sort of VPN. I never turned this on because "if I don't know what it does, I'm not going to activate it".@bmeeks said in Safari in Iphone is bypassing FIrewall rule:
Apple devices can apparently query an Apple DoH server, though.
Never saw it doing this ... but never looked for it doing that neither.
It gets a DNS when doing DHCPv4 and v6, the 'local' DNS (pfSense) and is happy to use that. -
@Gertjan said in Safari in Iphone is bypassing FIrewall rule:
Never saw it doing this
Turn on private relay, and see what happens ;)
-
-
@bmeeks Thank you very much for taking time to explain it.
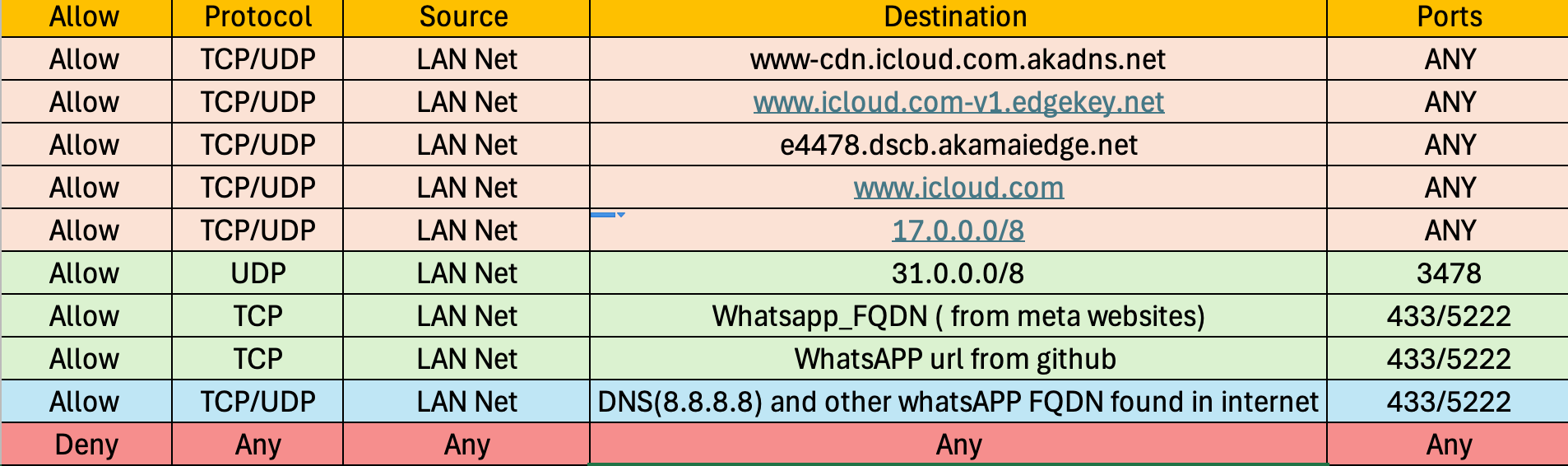
my FW rules.
Allow - rule1
protocol: TCP
source : LAN net
Destination: IP URL Table (https://adamnetworks.dev/pub/fwaliases/raw/master/ips/whatsapp.txt) this list have all the list of IPs from the Meta website for accessing whatsAPP (https://developers.facebook.com/docs/whatsapp/guides/network-requirements/)
From (Port): 443/5222
To (Port): 443/5222Allow- rule2
protocol: UDP
source : LAN net
Destination: Network or FQDN: 31.0.0.0 / 8(Facebook_IPv4_STUN)
From (Port): STUN (3478)
To (Port): STUN (3478)Allow-rule3
protocol: TCP/UDP
Source: LAN Net
Destination: DNS IP(8.8.8.8)
From (Port): 443/5222
To (Port): 443/5222Deny rule1
Any any any any@bmeeks said in Safari in Iphone is bypassing FIrewall rule:
Have you tested when 8.8.8.8 is unblocked that your Andoid devices are still restricted to only WhatsApp? I'm thinking they will have free reign on the web as well if 8.8.8.8 is available for DNS lookups and TCP port 443 is open
yes we tested it couple of times - when the DNS IP is allowed in android phone only whatsApp works other browsers is not working no other application is working - I think because in the allow rule the Destination IPs I am allowing is only whatsapp related IPs + DNS IP so even though some aplication get it resolved they cant passtraffic because that IP is not in allow list ? thats my understanding
-
@johnpoz plz see my new post reply I added my FW rule, which I am allowing only the destination IP address only related IP address which is provided by Facebook https://developers.facebook.com/docs/whatsapp/guides/network-requirements/.
I am denying all other IP address destinations.
-
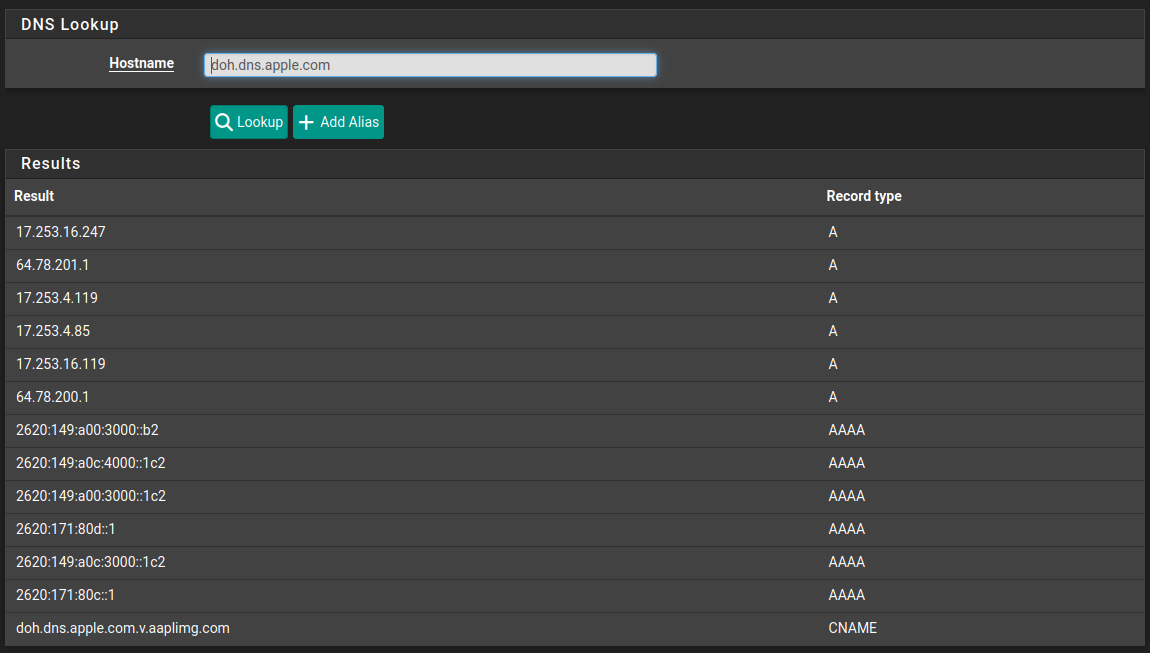
@Uglybrian so if I add new deny rule of adding all the doh address mentioned in the pic, will the safari accessing the internet will be blocked ?
-
@mozmail said in Safari in Iphone is bypassing FIrewall rule:
IP address which is provided by Facebook https://developers.facebook.com/docs/whatsapp/guides/network-requirements/.
Totally not up to date.
And facebook switched to IPv6... also missing. -
@mozmail said in Safari in Iphone is bypassing FIrewall rule:
@Uglybrian so if I add new deny rule of adding all the doh address mentioned in the pic, will the safari accessing the internet will be blocked ?
Well, maybe, but possibly not. As others mentioned, the IP addresses of the DoH servers can change. And some of the services are tied to CDNs that you have to enable to let other stuff work. Apple would be one for instance. If you block everything Apple, then iPhones can't get updates and certain Apple iOS stuff will not work. But allowing the Apple IP subnet blocks then lets the DoH traffic to Apple's servers get through.
I guess my ultimate question here would be "why do you want to restrict them to only WhatsApp?" As you are discovering, such specific filtering in today's Internet environment with so many CDNs and Anycast DNS services is becoming very difficult and heading towards impossible as DoH and QUIC become widespread
 .
. -
@Gertjan said in Safari in Iphone is bypassing FIrewall rule:
And facebook switched to IPv6... also missing.
Missing how.. Just because they enabled IPv6 doesn't mean any of those fqdn changed. And changed implies IPv4 is no longer available - which is just not true. You mean they enabled IPv6
If OP is running IPv6 then sure that would have to be taken into account when blocking IPs/Ports as well.. But if he isn't then means nothing if they have it enabled or not.
-
Private relay on Apple is a setting per each individual Wi-Fi network you connect to. For instance, for my home network wi-Fi settings I have private Wi-Fi addresses off and limit IP address tracking off. With these settings, my iPhone uses my local DNS,able to still get mail, messages, and filtering through PF blocker. On other Wi-Fi networks I joined private relay is turn on.
You can tell the people on campus with iPhone that if they want to use The campus Wi-Fi network these are the settings you need to employ with our network. Turn off private Wi-Fi addresses and limit IP tracking. This will not affect other Wi-Fi networks they use.
PF blocker has a DNBL safe search that you can utilize to block Apple iCloud private relay. There are also of course IP block list for Doh.
I use one from github/crypt0rr/public-doh-servers. -
After moving the DHCP server from the distribution switch to the pfSense box for my LAN network, we noticed that Safari traffic is completely blocked on all devices., WhatsApp voice and video calls work perfectly on both iPhone and Android.
The problem arises when users try to send or receive images via WhatsApp on iPhones. It takes more than an hour to send or download a picture, even though they can see the picture notification immediately. Strangely, other features like screen sharing during video calls work just fine.
I have attached the current pfSense LAN firewall rule for reference. Any ideas on what could be causing this or how to fix it?
Note: When I checked the WhatsApp URL IP list initially, it had 5 IP ranges dedicated to Apple, so I created a separate allow list named Icloude to see which one gets hit.
-
@Uglybrian said in Safari in Iphone is bypassing FIrewall rule:
You can tell the people on campus with iPhone that if they want to use The campus Wi-Fi network these are the settings you need to employ with our network. Turn off private Wi-Fi addresses and limit IP tracking. This will not affect other Wi-Fi networks they use
how to confirm that they turned off private wifi addresses and limit IP tracking ?
I can able to block the safari traffic after moving the DHCP server from the switch to the Netgate PFsense box. now only whatsapp works in iPhone and Android phones - but new issue is that Iphone uses when ever they try to send/receive pics it takes couple of hours - tested voice video call it works without any delay
-
@bmeeks said in Safari in Iphone is bypassing FIrewall rule:
I guess my ultimate question here would be "why do you want to restrict them to only WhatsApp?" As you are discovering, such specific filtering in today's Internet environment with so many CDNs and Anycast DNS services is becoming very difficult and heading towards impossible as DoH and QUIC become widespread
n Palo Alto and Cisco devices, it's easy to block traffic on an application-specific basis. I’m trying to achieve the same with a pfSense box. For example, on flights, only messaging apps are allowed, and all other internet traffic is blocked—so this use case and implementation already exist in the market. I’m now looking for a way to implement similar application-based blocking using pfSense. Any suggestions on how to do this?
I’ve almost managed to get application-based blocking working on the pfSense box
-
@mozmail said in Safari in Iphone is bypassing FIrewall rule:
@bmeeks said in Safari in Iphone is bypassing FIrewall rule:
I guess my ultimate question here would be "why do you want to restrict them to only WhatsApp?" As you are discovering, such specific filtering in today's Internet environment with so many CDNs and Anycast DNS services is becoming very difficult and heading towards impossible as DoH and QUIC become widespread
n Palo Alto and Cisco devices, it's easy to block traffic on an application-specific basis. I’m trying to achieve the same with a pfSense box. For example, on flights, only messaging apps are allowed, and all other internet traffic is blocked—so this use case and implementation already exist in the market. I’m now looking for a way to implement similar application-based blocking using pfSense. Any suggestions on how to do this?
I’ve almost managed to get application-based blocking working on the pfSense box
Those Palo Alto and Cisco devices have specific application detection technology built into them. That's also why they cost a ton of money to own and license
 . You pay for the priviledge of using that technology and for the labor and time of Palo Alto and Cisco security analysts to keep up with all the application technology changes and issue regular updates to keep the app detection/filtering working. pfSense does not natively offer application layer filtering, but it's also open source and free -- so there is that advantage.
. You pay for the priviledge of using that technology and for the labor and time of Palo Alto and Cisco security analysts to keep up with all the application technology changes and issue regular updates to keep the app detection/filtering working. pfSense does not natively offer application layer filtering, but it's also open source and free -- so there is that advantage.You can do this application detection and filtering on a limited basis, providing your are able and willing to write some of your own rules, with the Snort package on pfSense using its AppID feature.
-
@bmeeks I agree, due to budget we are going with PFsense and that's why checking the best to do with it, I got it working for now. with my above rule list and extra, I added to block the traffic to DNS IP 1.1.1.1 for port 853, from what I see Safari is using DNS over TLS port 853, with that blocked safari is blocked