OpenVPN External Connection
-
@viragomann Done!
I went back to start capturing packets and the VPN actually connected. It says no internet access and isn't allowing me to access anything, but it's finally connected!
I disconnected an reconnected multiple times to ensure it's connecting.
Thanks again for your help!
Any suggestions on how to continue configuring so I can access my network and workstation and utilize rdp?
-
@LMorefield
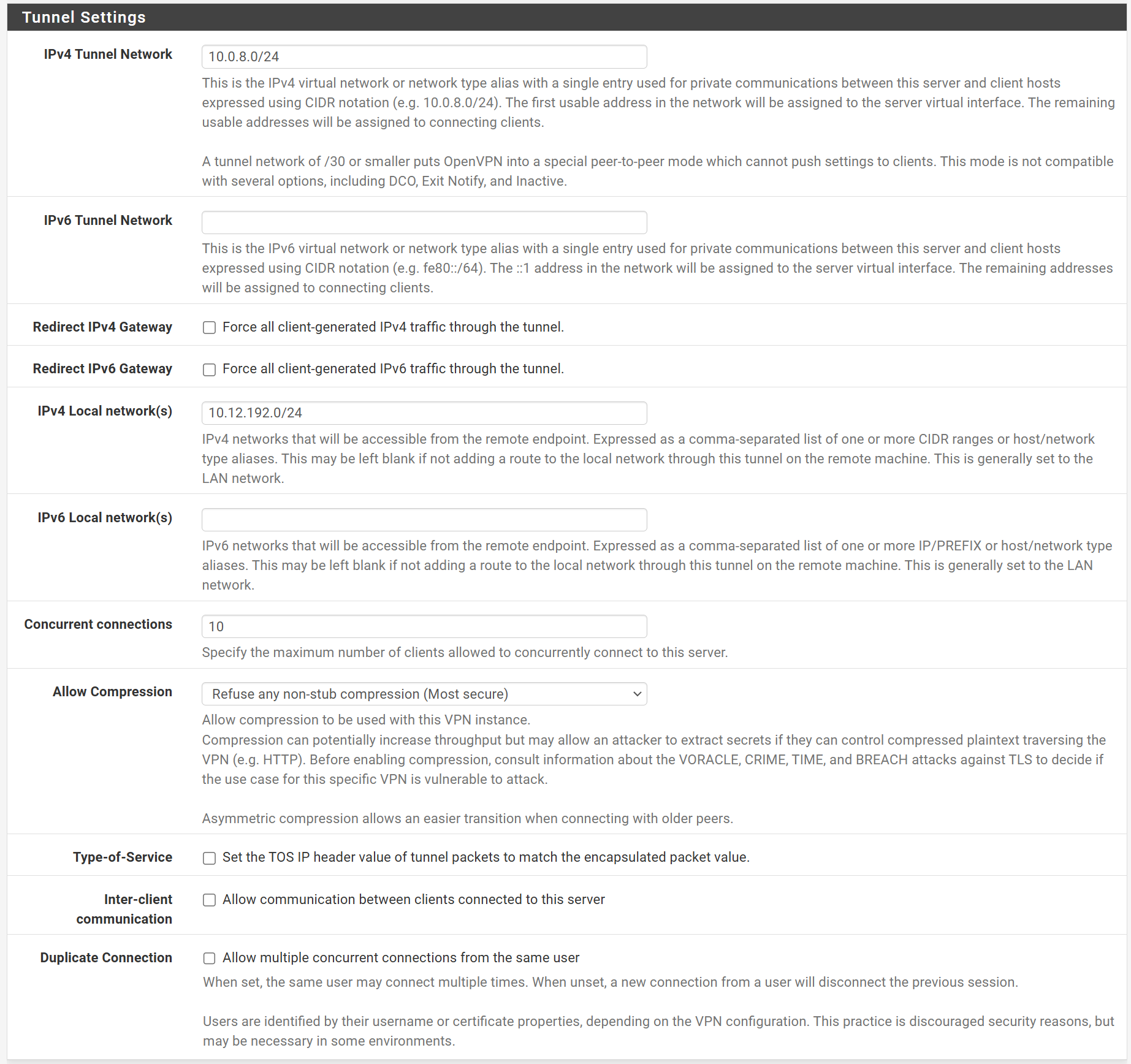
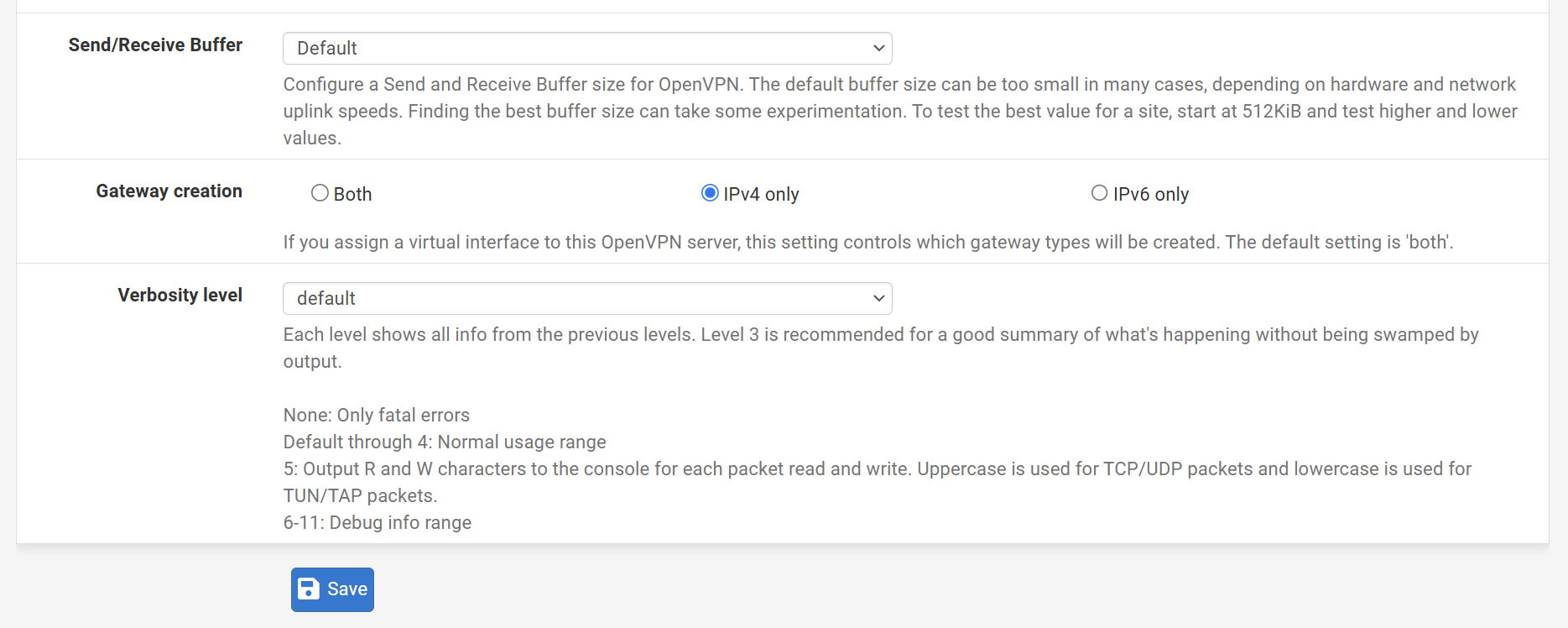
You OpenVPN rules allow access to the WAN subnet only. So I assume, this is what you want. And you don't want to redirect the whole upstream traffic from the client over the VPN.So did you have checked "redirect gateway" in the server settings?
If so remove this check and state you LAN subnet at "local networks".Also if you provide a DNS server in the VPN settings, ensure that you allow access to it.
-
@viragomann I'm looking to utilize the network once I remote into it, and mainly to access my workstation remotely using RDP. If the traffic going through the VPN is adverse, I can do without routing the traffic through the VPN.
I could not find the "redirect gateway" setting in the server settings.
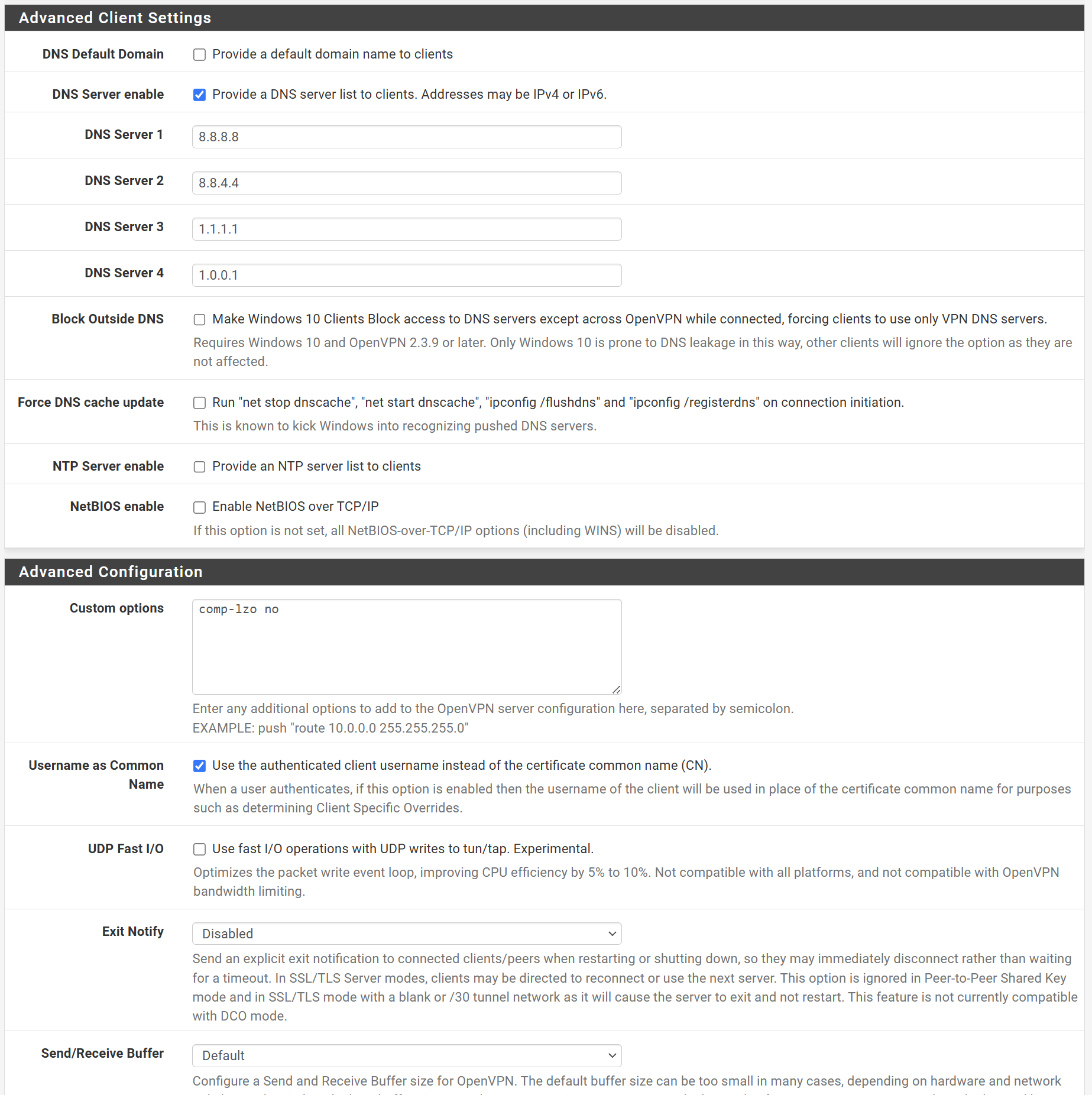
I added DNS servers in the VPN settings and opened it up I believe.
-
@LMorefield said in OpenVPN External Connection:
If the traffic going through the VPN is adverse, I can do without routing the traffic through the VPN.
This depends on your needs. Some want to redirect all traffic over the VPN to use the servers WAN IP to go out to the internet.
If you only intend to access the local networks stay with split tunneling.I could not find the "redirect gateway" setting in the server settings.
It "Redirect IPv4 gateway" and "Reirect IPv6 gateway". It's not checked.
I added DNS servers in the VPN settings and opened it up I believe.
Stating public DNS server requires, that the client has access to them. But I guess, this might be given.
So I'd expect, that the client has no issues with internet access with these settings.
BTW: there is no need to state "comp-lzo" in the custom options. This can be set at "allow compression".
-
Do you see states and/or bytes on the pass rule on WAN?
Anything logged now?
Edit: Ooops missed some posts.
-
I pinged internal IP's from the external connection and received, " Packets: Sent = 4, Received = 0, Lost = 4 (100% loss)"
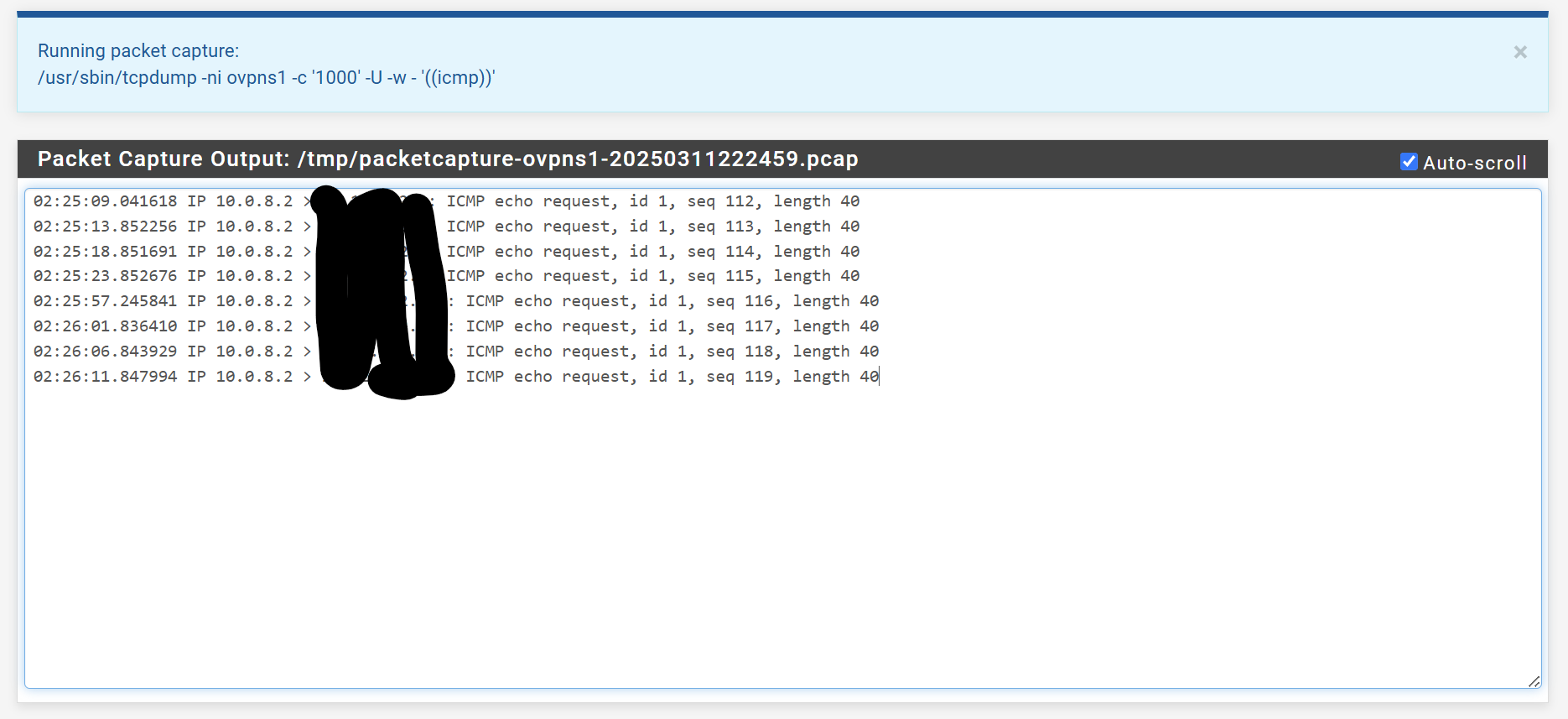
When I did the packet capture from pfSense using icmp as the protocol, the packet capture captured all of the pings, eight total, four for each IP address.
-
The destination there is some internal host on your LAN subnet? 10.12.192.0/24?
There's no need to obscure that, it's a private subnet. No one can route to it externally.
The destination host may not reply to pings from outside it's own subnet. pfSense will though, you should be able to ping the LAN IP.
-
@stephenw10 Haha, I wasn't too sure. And yes, here it is unobscured. Are you able to walk me through how to access the network now that I'm connected?
-
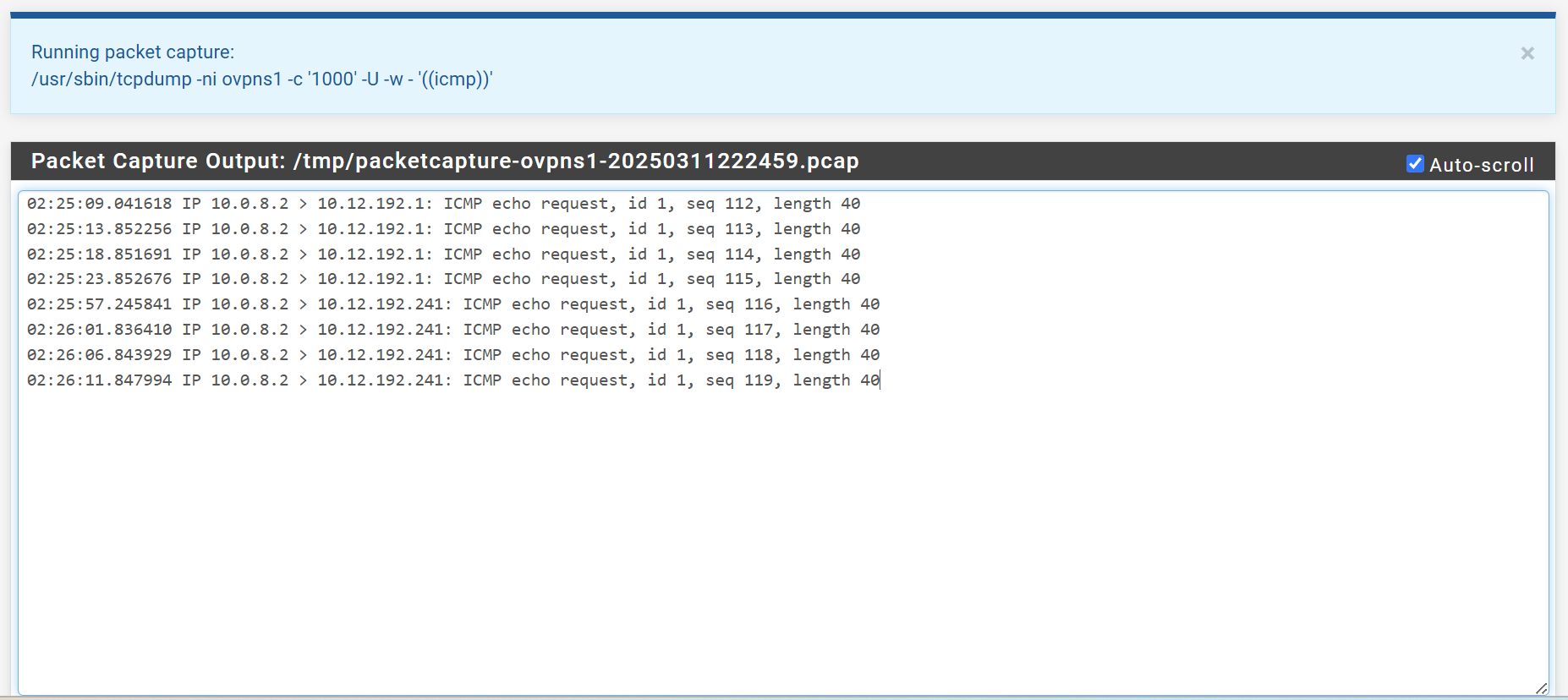
OK try running that pcap on the LAN interface. Make sure those pings are leaving there.
What are those hosts on LAN, .1 and .241?
If .1 is the LAN IP that should reply given the rules on OpenVPN. -
@stephenw10 The .1 is the pfSense gateway, the .241 is one of my desktops. I tried on LAN and got nothing for the pcap. Neither went through.
-
@LMorefield said in OpenVPN External Connection:
.1 is the pfSense gateway
You mean the LAN interface address? There shouldn't be a gateway on LAN.
You should see at least the pings to .241 on the LAN pcap though.

Your pass rule on openvpn is still the same? No gateway set?
Do you see any states open for that ping?
-
@stephenw10
.1 is where I go to login to PF sense, so I guess the LAN interface address. I ran the pcap on the LAN interface address and received the following. I tried pinging it four times.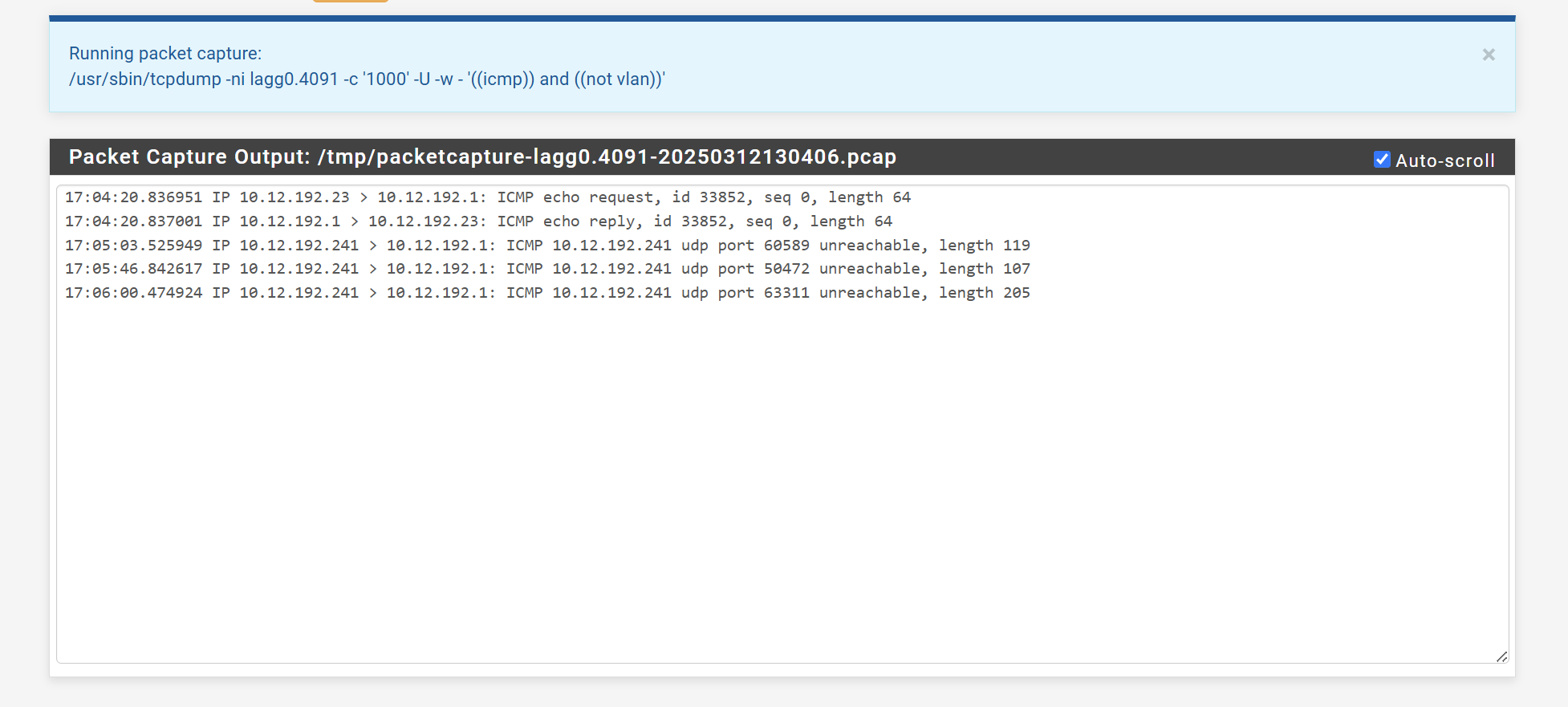
-
You ran pings to 10.12.192.241 from an openvpn client?
It's interesting that that host is sending icmp notifications back to the firewall that something is trying to access udp ports on it.
Are you seeing states created? Do you see states/bytes on the firewall rule on openvpn?
If not then it's being blocked by something. Floating rules maybe?
-
@stephenw10
Yes, was sending pings externally from an OpenVPN client to .241.There's 0/234 bytes
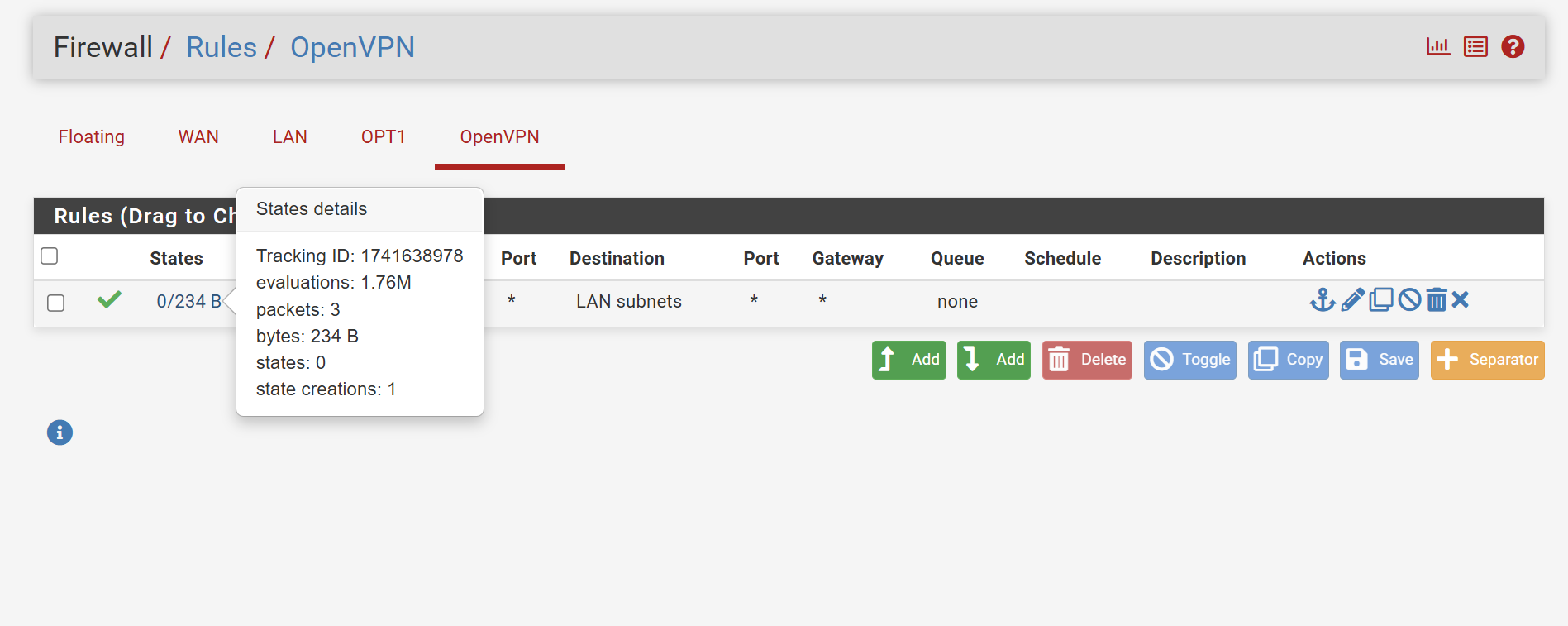
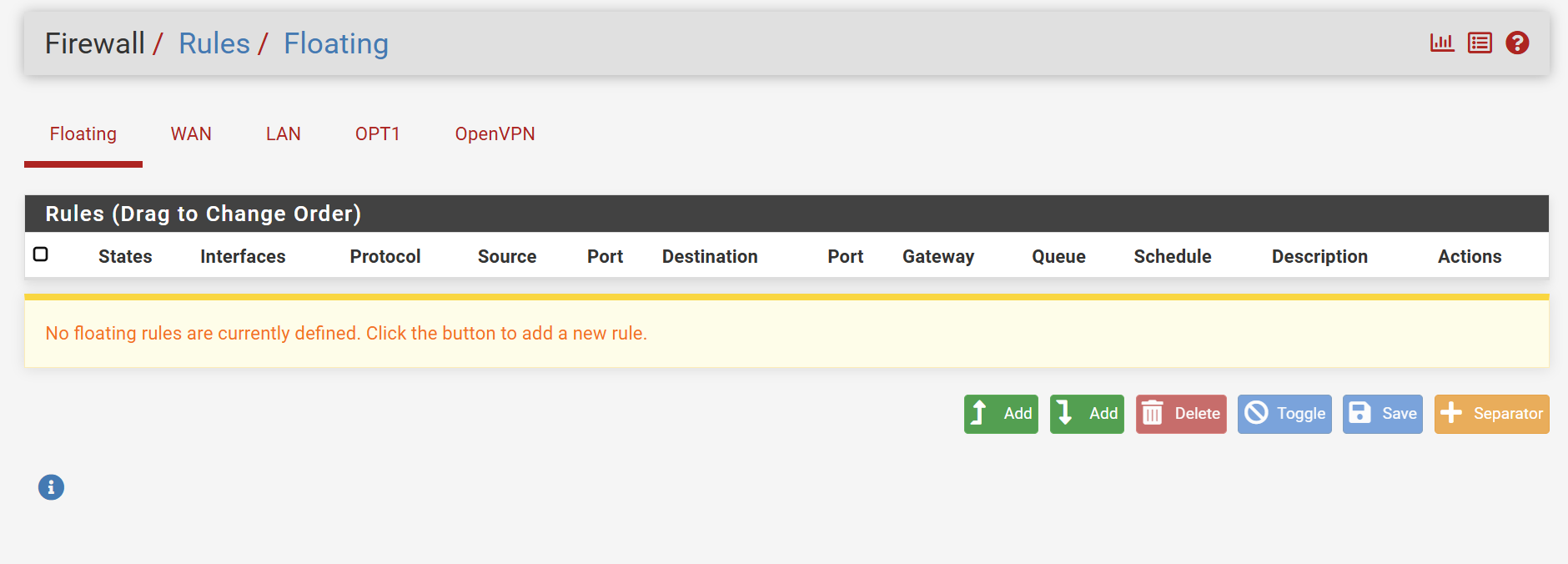
No floating rules.
-
@stephenw10 @viragomann
I just created a rule allowing port 53(DNS) which may not have had an effect, but I also created an ICMP rule in OpenVPN and I can now successfully ping the .241.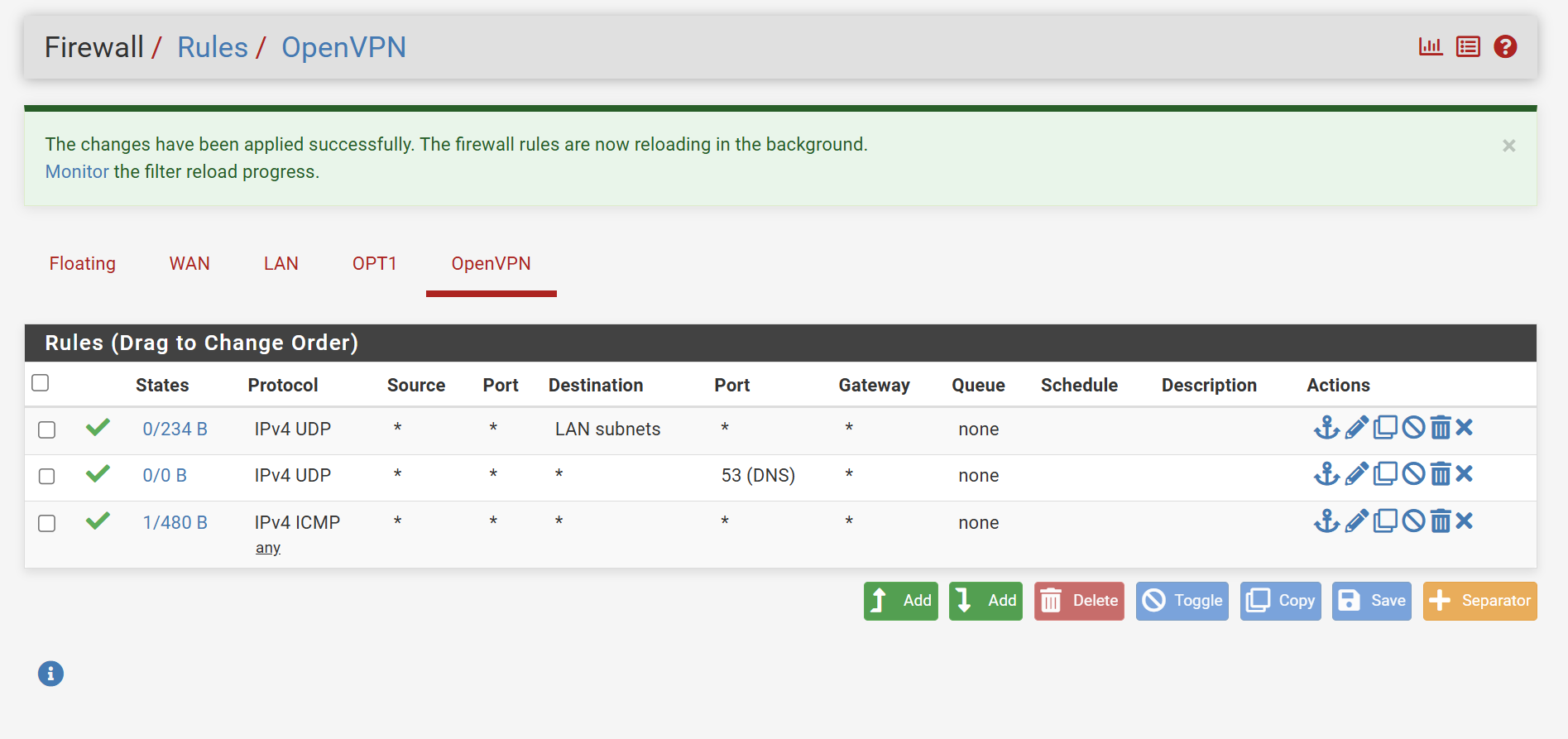
-
Your first Rule only allows UDP...
-Rico
-
@Rico
Awesome! That now allows me to access the LAN interface. Thanks! Any settings I need to change to allow me to RDP into my workstation? -
You have to pass TCP traffic for that. But I would just change that first rule to pass 'any' protocol to 'LAN subnets' and remove the other two rules.
-
@stephenw10 Done and it's working!
From the recent posts, is there anything I need to clear up to keep from getting hacked?
Thank you all again for your help, I appreciate you! I can't upvote yet or I'd be giving them!
-
I would consider putting OpenVPN on a different port. It's extremely unlikely you would be hacked that way but you will see connection attempts and possibly blocked traffic on the default port.