running pfsensei n a school
-
hi.
I would like to be able to run pfsensei n a school district.
hardware is not a big issue, nore is getting the software.
my big issue is web filtering.
what would be the viable way to do the web filtering?
some sources say PFBlockr NG, but i'm not sure.
others say squid guard, but again, I'm not sure.
I will use suricata for IDS/IPS.
thanks in advance -
I personally love Squid and Squidguard run it all day, again you would have to create a url blacklist and it is very complex to configure requires certificates, and special splice lists lots of settings, it is like a swiss army knife.
However for something that is running on a school I would recommend pfblocker it has more support base, and you can get that running faster.
Go with what the mainstream is using pfblocking, that way you get issues resolved faster.
-
@adisonverlice said in running pfsensei n a school:
others say squid guard, but again, I'm not sure.
I will use suricata for IDS/IPS.Ask yourself this question :
With your own device, like a phone, or PC, you connect to your won bank.
You and your bank, when connected, have a common interest : that your connection between your device and the bank's web server is secured.
You already know : you use https, and this means : traffic leaving your PC (or phone) and going to the bank, and traffic coming back from the bank is accessible by no one.Now, your question : the traffic leaves your device, and flows through other devices, like access points, switches, the quiepment of your ISP, other 'Internet' routres, up untill the bank, or any other site.
Your pfSense is somewhere in the middle of this chain.
With me so far ?You want to do IDS/IPS. Ok, nice, the packets flowing trough pfSense have packet headers, that contain destination and source IP, ports and some flags, counters and so on.
And a data payload, the actual data that is send to the server. This data is encrypted using TLS as you, and everybody else is using https.Your goal : decrypting the payload, and do some "IDS/IPS." on it, as you can't use the encrypted data : it's just a random stream of bits.
Afaik, even the 3 letter agencies can't do this. So neither can you, whatever device you use. This isn't pfSense's fault. It's us, you and me. We wanted inviolable securty, and we have it.
There are no exceptions.So, then how to do IDS/IPS ?
You remember the browser settings ? ALL the browser and network settings , Especially the ones you've never used before, and you always wandered : where are these for ?
It start with these :
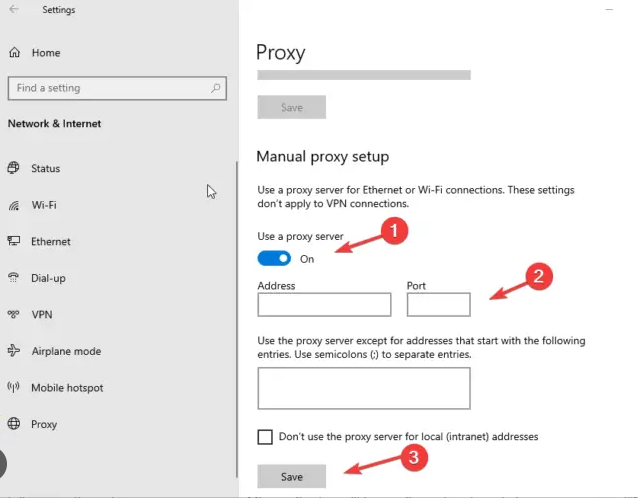
When you set up a proxy on your device, your PC, phone, etc, you give it the IP or host name of the proxy. This proxy will be pfSense.
From then on, your PC (phone) will contact the proxy = pfSense and ask it to do the actual request for it.
This means that you, from no on, have to trust the proxy, as it sees ALL your traffic = the payload.
This proxy setup has to be done for every device that uses the pfSense network - has to be done for every device that you want to 'filter'.I already see it coming : this is a school, nobody is going to modify their device's settings so the proxy can get used. And when they leave the school, settings have to be undo, and so on. They will refuse - or simply don't understand why they should do so, refuse even more when they understand why they should do so. Who likes to be spied upon ?
I'm pretty sure @JonathanLee can tell you way more about this subject, he is actually using it.
He started doing so a year or two before, he's on it 24/24h, he isn't still done with the setup, but he got pretty far ^^
( I don't, it's just not worth it )Be ware that their are many sites out there that will "know" that the traffic is proxied, so they will refuse the connection. This exception list is huge, and has to be handled manually.
So, final words : I don't say it can't be done.
It can.
What is often happens is : people get pfSense because : "Oh, pfSense can do IDS/IPS".
But its like getting a Boeing 737 MAX and think that you now can fly. You can't. Flying needs to be learned, the old fashioned way. No short cuts. It means : you have to go to school again ... -
@adisonverlice
The most common way of doing any web filtering is on the endpoint.
If you increased your budget and get a firewall that can do categorization filtering such as Fortigate or Palo then yes do it on the firewall but considering Squid is labeled a depreciated package and there are no paid lists to use with it to do filtering, you need to do this on the endpoint. With Squid you are wasting a lot of time and energy.Additionally, the documentation is clear
https://docs.netgate.com/pfsense/en/latest/recipes/block-websites.htmlThe best way to ensure these sites are not accessible is using an external proxy or content filtering capable of blocking by category.
-
@adisonverlice pfBlocker can use DNS block lists. You will need to prevent devices from using any other DNS, meaning, block DoH/DoT as well as port 53 outbound.
Suricata can work and we often use it for our clients, but I find that most outbound traffic is encrypted which Suricata can't see into. So if you're not hosting web servers or similar it may not help much.
-
@michmoor aw so pfsensei cannot do categorization filtering?
that is what it sounds like.
pfsensei is what i've been used to -
Sounds like you need an enterprise class content filtering service. Since you mentioned "school", I would be hesitant to recommend anything home grown as it would place liability on you personally.
In the past, I have used OpenDNS (owned by Cisco) Family Shield free tier. You can simply configure pfSense to forward all DNS queries to OpenDNS servers or create an account to give you finer grain control of content filtering categories.
You will have to configure pfSense to redirect and forward DNS queries to OpenDNS servers.
https://www.opendns.com/home-internet-security/
Or you can step up to Cisco Umbrella
https://umbrella.cisco.com
-
@elvisimprsntr said in running pfsensei n a school:
forward DNS queries to OpenDNS servers.
Or even : use pfBlockerng ....
I visited my family last month, and spoke with a cousin. He was aware that "certain domain names were blocked".
He's also aware that he can edit his local host file - even windows has one - and totally bypass any DNS blocking ....
And plan B is also there : he has spare prepaid SIM card ...
This cousin is just 8 ....
He isn't really smarter as any other kid out there.
He knows how to ask question - the verbal way, or the Google way ...So that's where we are going, back to square one :
Tell the kids not to put themself in front of a bear and kick it the face ...
Tell them not to 'drink' ...
Smoke ....
Etc etc.
This method worked fine for .... not sure, how long humanity exists ?
There will always be the one that drink, smoke, kick the bear, and so on.
Nature told us : get a spare kid ;)About the school solution : drastic but easy to admin solution : don't share your connection with 'kids', as your responsibility might called upon.
No need to get a lawyer if the kids couldn't connect to Toctic afaik. -
@Gertjan what?
-
@michmoor said in running pfsensei n a school:
what?
Simply said : kids can/tend to outsmart 'admins' ...
So no need to complicate things that already had simple solutions.
Better ? -
@Gertjan Yep i get it

I dont know what the laws and compliance/regulation is where the OP is from when it comes to filtering. In the united states there is CIPA which regulates this sort of things. pfBlocker absolutely would not be used and neither would Squid. A more well rounded solution would be implemented.
Can pfsense do web filtering? Ehhh..... Would I want it to do filtering? No. Especially when there are regulatory requirements. All comes down to what is permissible to the OPs region. -
@michmoor I guess what I was asking for is an open source solution for network filtering that could work with PFSense.
-
@adisonverlice said in running pfsensei n a school:
@michmoor I guess what I was asking for is an open source solution for network filtering that could work with PFSense.
Two commonly used applications are PiHole and AdGuard, which both work similar to pfblocker. The filtering will of course be based on lists, similar to the one's used in pfBlocker.
A nice feature in AdGuard is the Application filtering which uses a simple UI where you just check a box per App that you want to block. It also has a simple scheduler function so you can block only certain times of the day...And as @SteveITS already mentioned you need to prevent clients from circumventing your AdGuard server, setting DNS manually in the clients (as well as preventing DoH/DoT).
-
I Agree with @Gblenn
There doesn't seem to be any regulatory compliance here, so Adguard or Pihole it is. To be clear, these apps are not an inexpensive way of doing the same thing as commercial solutions.edit: I have heard of positive feedback from using nxfilter. Its a free solution but its proprietary.
https://nxfilter.org/p4/ -
@Gblenn that, and Adguard can do DOT and DOH.
I might enforce the DOH servers on the client side.