pfBlockerNG not logging anything by default?
-
@rasputinthegreatest said in pfBlockerNG not logging anything by default?:
I know you say it's nothing but why am I even seeing this in the first place?
Test this :
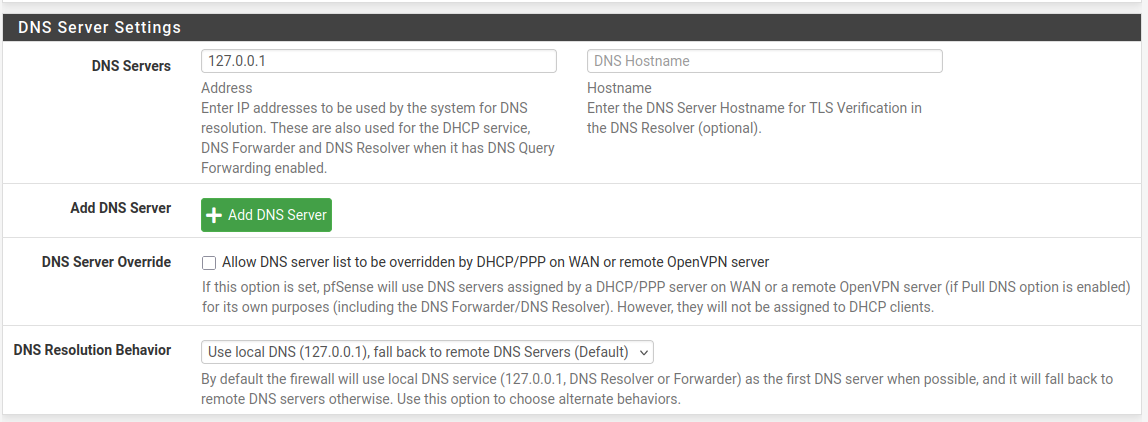
Install a pfSense with its WAN into an existing network. Default, the pfSense WAN uses DHCP, so it's "plug and play".
Hook up a switch to LAN - don'(t sue any other of the switch port. Leave them empty.
Use the pfSense console access to analyze logs.
Make sure that .... there are very few or no DNS look ups.
May one ne in a while, asking for abcd.netgate.com or some other pfsense.org domain as pfSense tests ones in a while if upgrades are avaible.
If you have set up a time service, you'll see that a time server is contacted.
And that's it.Now, populate your LAN.
All kind of traffics starts to show up. These come from your LAN devices.@rasputinthegreatest said in pfBlockerNG not logging anything by default?:
if you own your own website on Cloudflare. They try out all sorts of names to see if anything is there.
"Cloudflare" lives on the WAN side, also known as the Internet.
Nothing that lives out there can come into the WAN - not one bit. Ever.
( well, admins can do strange things, true, so lets presume a default pfSense install )
So, what can these bots do ? They can't use your resolver (unbound) to resolve stuff. They can't access your pfSense unbound from the outside.Bots that live on devices on your LAN : that's another story. All your other LAN devices are exposed now and pfSense can't do anything about it. That's why most devices have their own firewall.
-
@Gertjan said in pfBlockerNG not logging anything by default?:
Install a pfSense with its WAN into an existing network. Default, the pfSense WAN uses DHCP, so it's "plug and play".
So you mean build a new computer with pfsense again? My pfsense is already part of an existing network since I run double-nat. I have only my ISP network to test from. Could a managed switch be the culprit somehow?
@Gertjan said in pfBlockerNG not logging anything by default?:
Use the pfSense console access to analyze logs.
Don't I have to connect a device to access pfsense or how would I do that?
-
@rasputinthegreatest said in pfBlockerNG not logging anything by default?:
So you mean build a new computer ...
I prefer you see things with your own eyes.
Or just believe my words : hook up a clean non tampered pfSense (you are allowed to change the password, nothing more - no packages) it will work.
With very few to no DNS requests to handle.@rasputinthegreatest said in pfBlockerNG not logging anything by default?:
Could a managed switch be the culprit somehow?
Why ? Smart switches don't generate DNS requests.
@rasputinthegreatest said in pfBlockerNG not logging anything by default?:
Don't I have to connect a device to access pfsense or how would I do that?
?
The most important interface on pfSense is the "console" connection
It always work.
NICs can be down. -
@Gertjan said in pfBlockerNG not logging anything by default?:
prefer you see things with your own eyes.
Or just believe my words : hook up a clean non tampered pfSense (you are allowed to change the password, nothing more - no packages) it will work.
With very few to no DNS requests to handle.I am on it. But verifying it has not been tampered with is impossible even on a clean installation if it's embedded in firmware for example.
Also don't I need to increase log levels or at least install pfblockerNG to even see any of these DNS queries? I only found them through pfblockerNG in the first place. In default logs it would not show up.@Gertjan said in pfBlockerNG not logging anything by default?:
Why ? Smart switches don't generate DNS requests.
My QNAP switch has a section for IGMP snooping and LLDP. Maybe it has some stuff in it's "memory" that it is broadcasting? Sorry I have no idea.
@Gertjan said in pfBlockerNG not logging anything by default?:
The most important interface on pfSense is the "console" connection

It always work.
NICs can be down.What does that look like? Do I need a special hardware for that or does it work another way? I can only have a screen and keyboard plugged into the firewall. Does it offer a GUI/shell or direct input through that? Otherwise I am out of luck here. I only have IPMI on the board but that would need a connection to a different device as well so it's not ideal.
-
@rasputinthegreatest said in pfBlockerNG not logging anything by default?:
is impossible even on a clean installation if it's embedded in firmware for example.
Because "you don't want to". (no time, other interest, etc) Remember : pfSense is 'open source' **. So, here it is - to be seen by everybody who takes the effort to understand what it all means.
** granted : the FreeBSD kernel has its own github source tree, and can be found else where.
Maybe there are a process or two (binaries) that are owned by Netgate without freely accessible source but these can be reverse engineered (tools exist) if you really want to know what happens in there.@rasputinthegreatest said in pfBlockerNG not logging anything by default?:
In default logs it would not show up.
And that's a good thing.
Just know that you can see them if you need to.
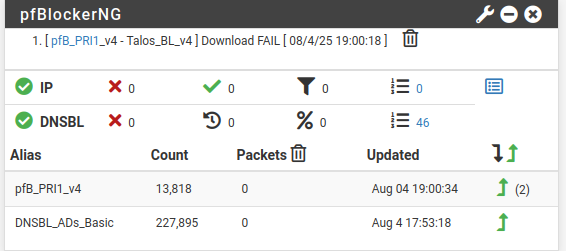
pfBlockerng makes already nice stats for you.@rasputinthegreatest said in pfBlockerNG not logging anything by default?:
What does that look like?
On this kind of devices : My 4100 : there is no VGA or HDMI connector. So, when the system boots, you can't see the BIOS, you 'see' nothing untill the web GUI engine starts. For that to work, a LAN interface needs to be up. For an interface to be up, the system had to boot to the end without errors.
So, these devices have a "serial port". That port is sued to spit out the BIOS and boot process. Hook up a serial 'USB' connector, and use a terminal emulator.If you use a "PC" as a pfSense device then you have a video card, and USB mouse, keyboard etc so that will be your 'console' access. Hook up a screen and you see the boot process etc.
Another example : your smart switch , How do you access the GUI ? => with a web browser. You can't attach a VGA screen to it neither. What happens when the firmware update fails ? You have to use the console access - if one exist. If it doesn't : you waste bin the device as no access anymore.
Neither your APs, Printers, coffee machine, airco; whatever. Most have a 'hidden' serial connection for low 'console' level access. Always 'command line based' of course. -
@Gertjan said in pfBlockerNG not logging anything by default?:
Because "you don't want to". (no time, other interest, etc
What do you mean? I am unfortunately not a software engineer nor a hardware specialist. It would probably take me years to figure any of this stuff out. Definitely no time for that. My switch has a console port but I never used it thus far.
@Gertjan said in pfBlockerNG not logging anything by default?:
And that's a good thing.
Just know that you can see them if you need to.
pfBlockerng makes already nice stats for you.So on that clean machine with a fresh install you recommend installing pfblockerNG? But how is it a good thing if I don't see what is going on? I need some sort of log that would show these weird domains to me in case they happen there as well on a separat network. If I hadn't installed pfblockerNG I would not even have seen whats going on. I consider that a bad thing. Or one could say ignorance is bliss?

BTW: I haven't seen any new entries since my work computer is off. Yesterday it happend after it was off but I think only because I tried to ping it from my laptop and through pfsense. So I feel like my work computer is the culprit which is not great either...
-
This post is deleted! -
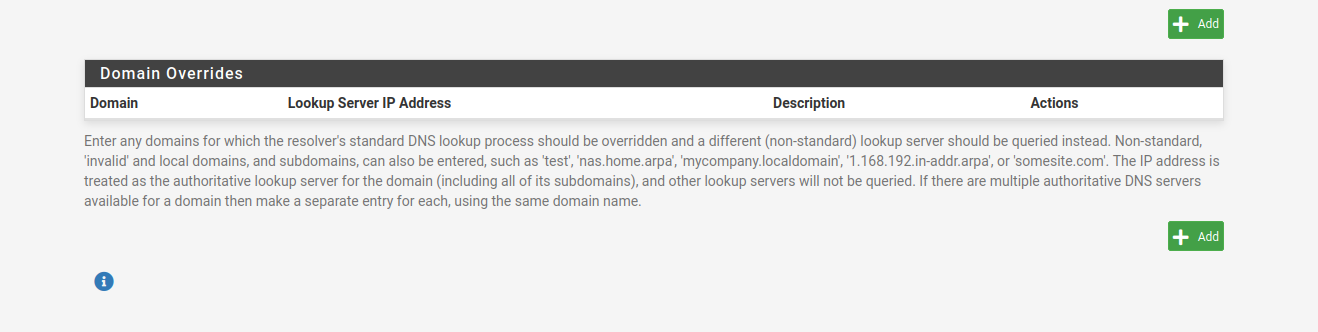
Is it possible to set a *.local and *.arpa domain override here to get rid of all these entries?
-
Wild cards like *.something are not allowed.
Domain Overrides is meant to be used for something completely different.
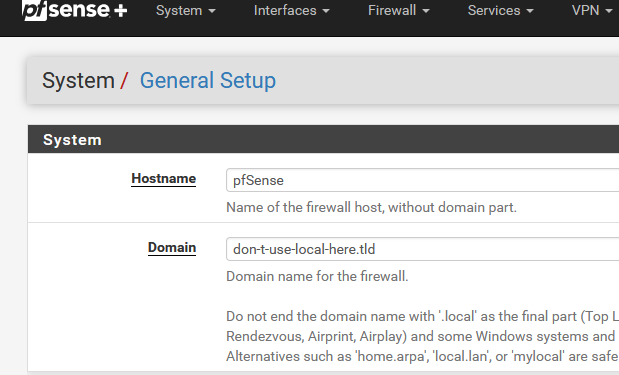
Be sure to rename your :
then, if you have to, locate the device that sends these DNS requests. Shut it down or find the process sends these requests, and kill it.
-
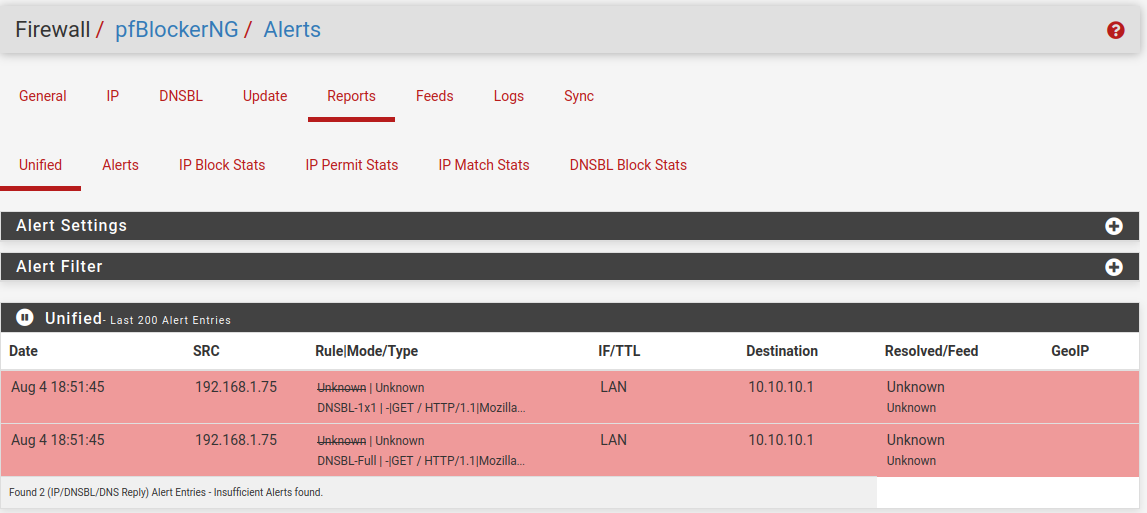
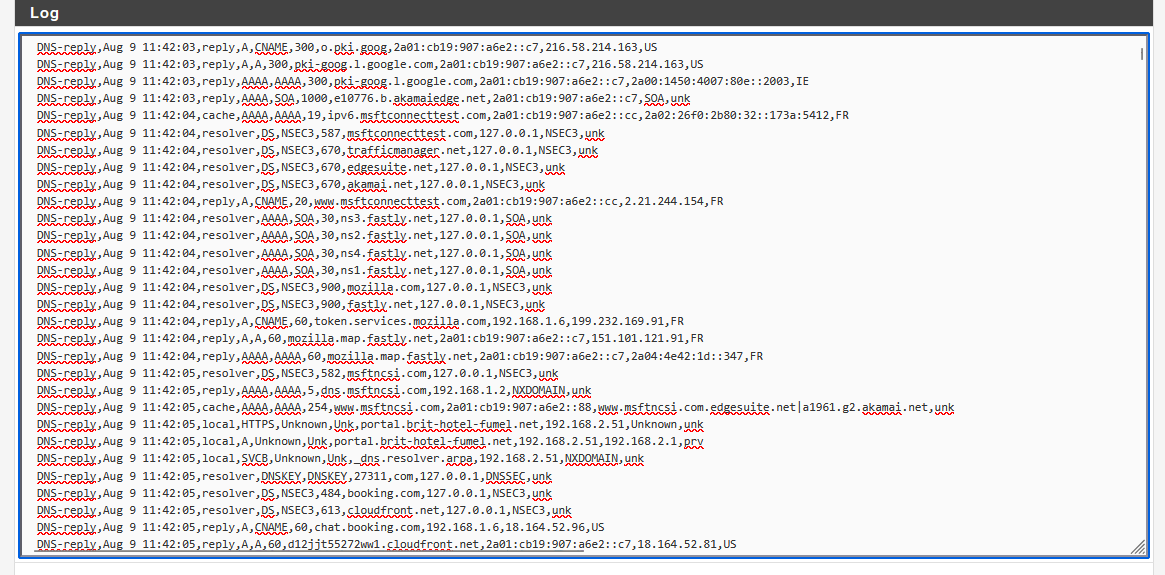
@Gertjan Whenever it is a full hour I see stuff like this in my logs:
https://otx.alienvault.com/indicator/ip/94.16.122.152
It seems to be time servers but it's a TOR node and some private person hosting traefik? I feel like this should not show up? It originates from my ASUS access point. But it is also related to when the emerging threats get updated. All happens at the full hour mark. I don't know why some random private persons ntp server gets queried. -
This post is deleted! -
So today I had just my work computer running behind pfsense as an experiment and I am still seeing these weird DNS queries. Now for the weekend I will only use my laptop and see what happens. If I am still seeing these queries there must be something up with pfsense.
-
Why would pfSense generate random host names / URLs ?
If it (unbound) has to resolve "otx.alienvault.com" then that was because it was asked to do so. The request came in by LAN, and was handled. And logged.
Shut down all LAN devices, and "DNS requests" will stop.
The ones still there will be 'Netgate' or 'time server' based.@rasputinthegreatest said in pfBlockerNG not logging anything by default?:
https://otx.alienvault.com/indicator/ip/94.16.122.152
Where - what log - did you find that URL (DNS only deals with host names) ?
-
@Gertjan s7.vonderste.in resolves to 94.16.122.152. I just saw a dns request for that. In the whitelist on OTX Alienvault there is a timeserver: 3.de.pool.ntp.org
I just don't know why a timeserver runs on a TOR node and seems to be hosted by a private person.
Maybe pfblocker resolves it incorrectly becaues the time server is hosted on the same IP?
Anyway I see this coming from my ASUS router which is in Access Point mode. These weird domains always come up every hour and I think they are related to ntp on that ASUS router. Since I disconnected it it has stopped. Here is an example of what I see. Scanning these IPs shows nothing malicious but who knows.93.122.215.85.in-addr.arpa,192.168.1.8,sonne.floppy.org,unk 94.244.38.46.in-addr.arpa,192.168.1.8,basilisk.mybb.deWhat didn't stop was on my work computer these weird replies as mentioned above.
reply,A,NSEC,1081,domaincontroller-gPHvwjYS.local,192.168.1.86,NXDOMAIN,unkBut it only happend once today instead of multiple times like the days before.
@Gertjan said in pfBlockerNG not logging anything by default?:
Where - what log - did you find that URL (DNS only deals with host names) ?
I find them in pfblockerNG dns_reply log under Logs
EDIT: I just realized that it is kind of in the name pool.ntp.org
its made up of multiple sources so it does make sense that it resolves some of these weird private hosts? -
@rasputinthegreatest said in pfBlockerNG not logging anything by default?:
its made up of multiple sources so it does make sense that it resolves some of these weird private hosts
An public NTP pool like pool.ntp.org would not list host names with weird random paddings that reference local devices.
"domaincontroller-gPHvwjYS.local,192.168.1.86" is a reverse PTR, and is requested by one of your local
devices.
Why , I don't know.@rasputinthegreatest said in pfBlockerNG not logging anything by default?:
I find them in pfblockerNG dns_reply log under Logs
No URLs there, only host names.
-
@Gertjan said in pfBlockerNG not logging anything by default?:
"domaincontroller-gPHvwjYS.local,192.168.1.86" is a reverse PTR, and is requested by one of your local
Yes these local domains are requested by my work computer. They are unrelated to NTP. I was talking about these entries every hour:
93.122.215.85.in-addr.arpa,192.168.1.8,sonne.floppy.org,unk 94.244.38.46.in-addr.arpa,192.168.1.8,basilisk.mybb.deAre you using pool.ntp.org? If so what does it show at the full hour for you? Like 12am, 1pm etc?
I read that it's made up of a pool of timeservers that are closest to you to get the most accurate time. That's why they get queried. -
I finally got around installing a new pfsense firewall and the first connections I am seeing right of the bat are lets say strange. I don't know what they are:
https://otx.alienvault.com/indicator/ip/178.250.1.11
https://www.abuseipdb.com/check/178.250.1.11
https://www.virustotal.com/gui/ip-address/178.250.1.11/community
https://viz.greynoise.io/ip/178.250.1.11Aug 10 11:07:09 WAN Default deny rule IPv4 (1000000103) 178.250.1.11:443 192.168.178.21:18414 TCP:PAIts incoming from WAN trying to get to the firewall. Very mixed results here.
Never heard of criteo and it is flagged by some people despite being whitelisted on otx alienvault. I remember seeing the same the first time I installed pfsense on my other machine I think. Any idea what it could be?
I also did a packetcapture and there are losts of ACKed Unseen segments. Does this indicate anything?
On my other firewall I don't see anything coming from WAN to LAN but on the new one there is so much IPs. What can it be?