Packets go through, logging is set, but no logs of the traffic
-
@stephenw10 Yes, it does fail when an actual OpenVPN client sends traffic since that's how this issue was discovered initially. Clients were connecting to this - or trying to connect, we would see the traffic in the VM but not in PFSense logs.
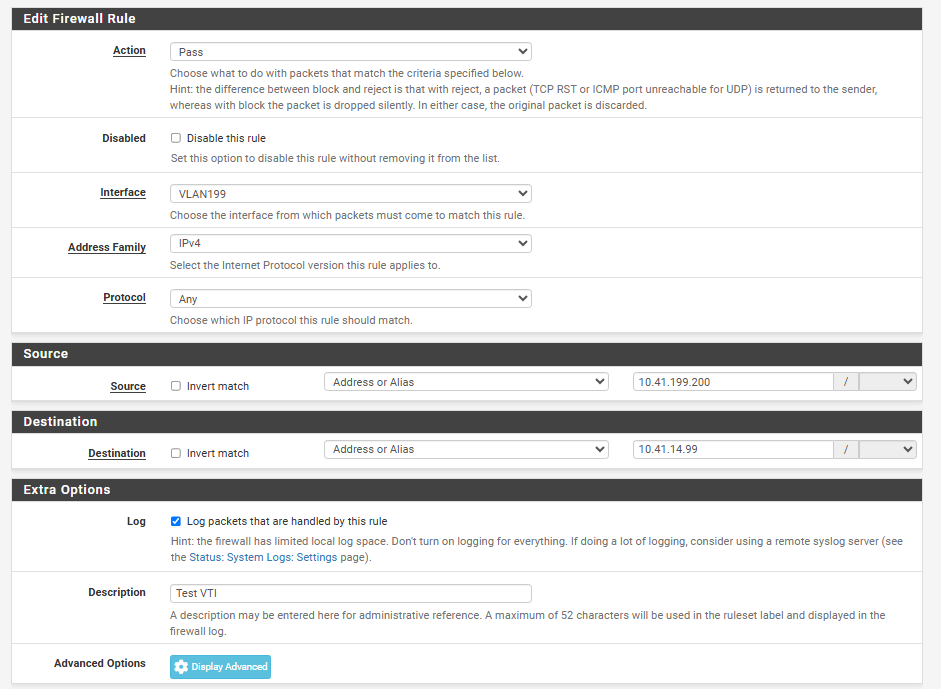
This rule was auto-created but since the description of the rule was empty, it was edited out so when it's logged, we have an idea of what's logged. The rule itself was auto-created, it was just edited afterwards.
The forwarding policy:
Disabled: unticket No RDR: unticket Interface: WAN Address Family: IPv4 Protocol: UDP Destination: Public IP address (alias) on WAN interface Destination port range: OpenVPN Redirect Target IP: 10.151.0.5 Redirect Target Port: OpenVPN Description: OpenVPN No XMLRPC Sync: not ticket NAT Reflection: Pure NAT Filter rule asociation: <name of rule associated to this NAT rule>. If I click on "View the filter rule" I get redirected to the rule that doesn't log.As I said, if you want to take a look, we can have a Zoom / Teams session as it might be easier for you to check it out (not really comfortable to share public IPs and stuff here :D )
-
@stephenw10
coming back with new info: it seems this is NOT the only rule that's affected. Below, I've specifically set a rule on the correct interface (since I'm seeing states next to that rule) to log ANY traffic from 10.41.199.200 (test host) to 10.41.14.99 (another test host). They're connected via an IPSec VTI tunnel, but I don't expect that to change anything. Below, logs from the PFSense and the device on the other end:
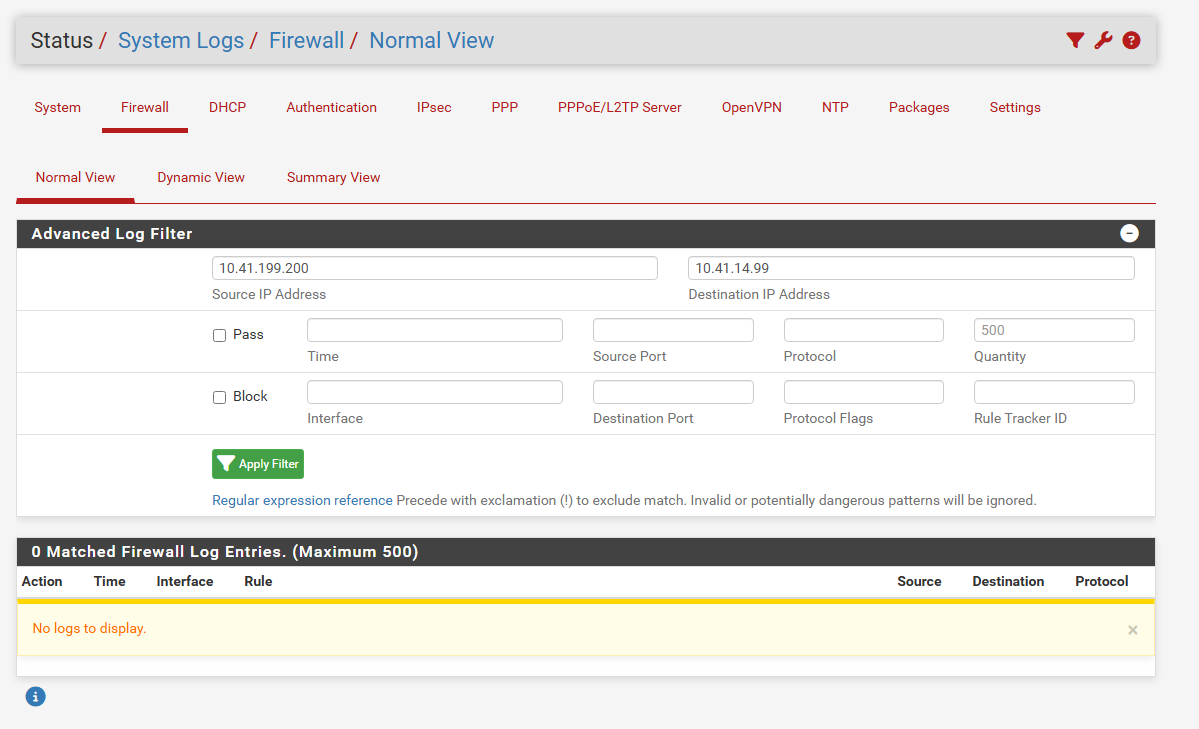
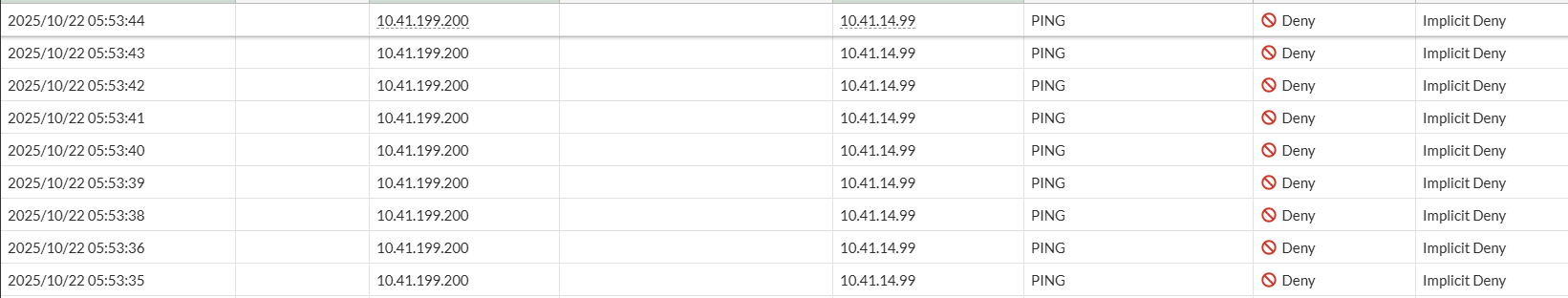
The fact that the traffic is stopped by the 2nd firewall is normal, as I haven't added the rule there yet, but the traffic reaches the 2nd firewall, while it's not logged in the PFSense.
The PFSense rule: