Native IPV6
-
I have succesfully setup a ipv6/ipv4 dual stack connection with a HE.net tunnel.
But my provider (Businessconnect NL) can deliver native IPV6 on my fiber connection. Is this configuration already possible with the latest IPv6 build?Or is only the tunneling config possible?
-
Only static addressing is currently supported. I need to get my hands on a internet connection that uses something like dhcp6 for troubleshooting.
What is the suggested configuration of this ISP to get connectivity working?
Since you mention it is fiber they might be using static addressing for the WAN, perhaps dhcp6 would be more likely. If you can get pfSense connected setup and working over ipv4 I could remotely troubleshoot your connection to get ipv6 working.
-
Thanks for your reply, I am using static IPv4 addresses currently, so I suppose it will be static IPv6's also.
Will question my ISP for this tomorrow, and will test it a bit, if I need your help i will let you in via IPv4!!thanks
-
Hi everyone
Working without a flaw :)
Now waiting for a stable ipv6 build to implement it in my production evironement ;)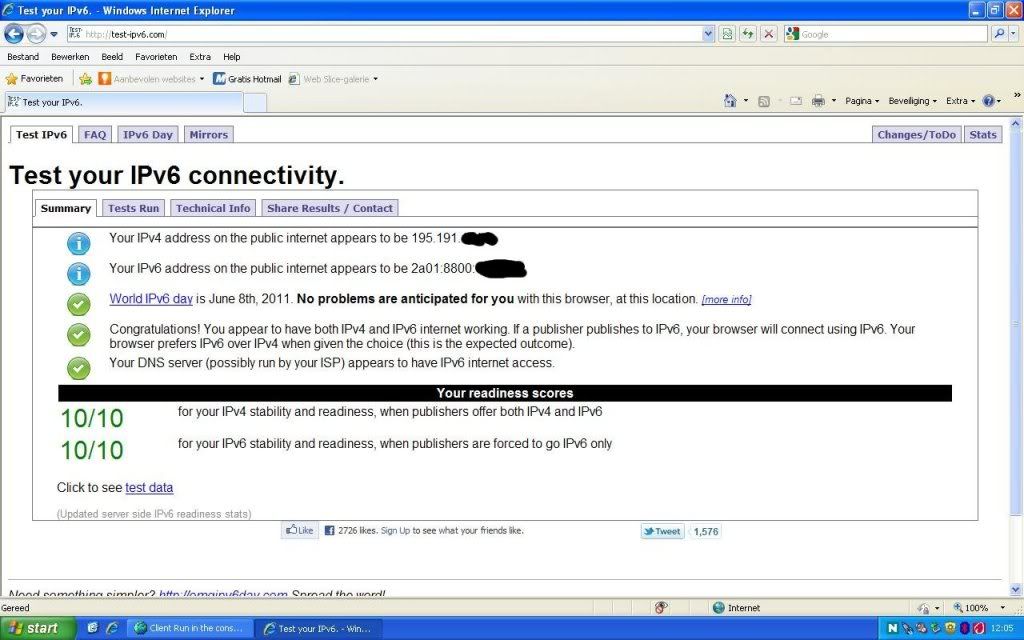
-
Hi,
I guess my needs are more or less the same talked here. I have several servers behind a pfsense, working well with ipv4, on a datacenter. Our carrier gives us native ipv6 connectivity, and a /64 (is, by far, enough, no need to use a /64 for each server) for all the servers.
So if I just configure LAN & WAN as ipv4+ipv6 interfaces, and I manually add the ipv6 gateway, I can ping to and from Internet with the ipv6 of the WAN interface. From the servers on the lan side, I can ping the ipv6 address of the LAN interface, and from pfsense I can ping the ipv6 ips of every server. But from the servers (on the lan side) I can't ping any internet (ipv6) host and I can't neither ping from Internet to any of those ipv6 on the lan side. I configure their default ipv6 gw with the ipv6 address of the lan interface. I also have enabled net.inet6.ip6.forwarding on pfsense, and rules both on WAN and LAN interfaces to allow any <-> any ipv6 traffic.
What's wrong?
Thanks,
Ruben
-
You are using a different /64 on the WAN from the LAN right?
It's routing.
Normally they point the routed /64 or bigger network to your firewall. That's how xs4all does it.
You get a /64 for the interconnect and a /48 (65k /64 networks) to assign to interfaces behind it.
-
Well, in fact, no. All belong to the same /64
The ::1 of the subnet is the default gw of pfsense; wan is ::2, lan is ::3, and so on in the lan side. Maybe it's not the better way of doing it, but the fact that the wan ipv6 is reachable from internet and the lan one isn't, means the packets are stopped at pfsense.
I have no problems in giving you access to the pfsense box if you want :) It's in production but I know you wouldn't break the ipv4 part ;)
Regards
-
You can not use the same subnet on the WAN and the LAN interface. That is not different from IPv4.
That won't work.You need to have the ISP/DC give you a subnet you can use behind pfSense. Ask the carrier for subnets you can use behind your router. They should comply easily with that.
If your carrier refutes your request (unlikely) they wouldn't understand internet routing 101.
Under normal circumstances they will allocate a /48 and point a route at the internetconnect ::2 which would be your WAN address on pfSense. Some ISPs will automatically downsize the interconnect to a /120 to prevent ND table overflows from port scans. This is best practice.
-
Thanks databeestje, I was afraid it was this. I'll let you know about this.
-
Yeah :) That way, works.