Shrew soft, IPSec Mobile issues, connects but cannot PING! Please Help!
-
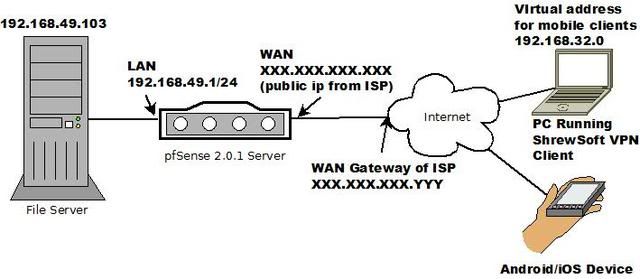
Hi, I am very new to pfSense and somewhat new to routing so I am thinking there is some setting that is incorrect. I have a fileserver that I want to connect to with an IPSec Tunnel over the internet with pfSense 2.0 IPSec router and a shrew soft windows 7 vpn client.
Once I get this configured correctly I want to connect with android/iPad.
I followed the tutorial for http://doc.pfsense.org/index.php/Mobile_IPsec_on_2.0 and I am able to connect with both shrewsoft and my droid bionic. I can see that I am getting an ip address for the connection but I can't ping anything on the network except for my own IP.
Here's my pfSense setup.
[WAN] Internet connection is connected to WAN port pfSense Server.
xxx.xxx.xxx.xxx/8 my public IP address [WAN Static]
xxx.xxx.xxx.yyy Wan Gateway of my network provider.
Block private networks
block bogon networks[LAN] Static,
FileServer I want to connect to (192.168.49.103) is plugged into the port on pfSense Server, along with a few other computers and a wifi router. All computers connected via wifi router can see fileserver
192.168.49.1 / 24
Gateway <none>[IPSec Phase 1 settings]Interface [WAN]
Description [phase1 entry]
Phase 1 proposal (Authentication)
Authentication method [Mutual PSK+Xauth]
Negotiation mode [aggressive]
My identifier [My IP Address]
Peer identifier [distinguished name] [property.lan]
Pre-Shared Key [test]
Policy Generation [default]
Proposal Checking [Obey]
Encryption algorithm [AES 128]
Hash algorithm [SHA 1]
DH key group [2]
Lifetime 28800 seconds
Advanced Options
NAT Traversal [enable]
Dead Peer Detection Enable DPD [checked]
[10]seconds Delay between requesting peer acknowledgement.
[5]retries Number of consecutive failures allowed before disconnect.[Phase 2]
Mode [tunnel]
Local Network
Type: [none]
Address: [blank] /
Description [Lan Phase 2]
Phase 2 proposal (SA/Key Exchange)
Protocol [ESP]
ESP is encryption, AH is authentication only
Encryption algorithms
AES [checked][128]
Blowfish
3DES
CAST128
DESHash algorithms SHA1 [checked]
MD5
PFS key group [off]
Lifetime [3600] secondsMobile Clients [enabled]
User Authentication Source: [system]
Group Authentication Source: [system]
Client Configuration (mode-cfg)
Virtual Address Pool
[checked] Provide a virtual IP address to clients
Network: 192.168.2.0/24
Network List [unchecked]
Save Xauth Password [unchecked]DNS Default Domain
Provide a default domain name to clients [checked] [property]
DNS Servers
Provide a DNS server list to clients [checked]
Server #1: [8.8.8.8]
Server #2: [208.67.222.222]
[everthing else unchecked]Pre-shared Keys
I have added my username and password here.Firewall Rules
[IPSec Rules]
ID Proto Source Port Destination Port Gateway Queue Schedule Description
[add new rule]
[click to toggle enabled/disabled status] * * * * * * none Allows anythingI have also added allow anything on the WAN and LAN and FLOATING tabs to make sure nothing is blocked.
From inside the LAN via wifi router I can access the internet, connect to pfsense server and connect to the fileserver.
When I go to a remote computer on the Internet I can connect via Shrewsoft but I cant see the server, pfSense server console, nor the fileserver. I cant ping anything except my own ip address.
The address it gives me is 192.168.2.2Here is my ipSec VPN log (reverse order)
Feb 12 00:45:29 racoon: INFO: Released port 0 Feb 12 00:45:29 racoon: [Self]: INFO: ISAKMP-SA deleted xxx.xxx.xxx.xxx181[4500]-192.168.49.2[4500] spi:ksdjdfslkdj8498ds8:203j9390j09d0d0d Feb 12 00:45:29 racoon: INFO: purged ISAKMP-SA spi=ksdjdfslkdj8498ds8:203j9390j09d0d0d:00007af7. Feb 12 00:45:29 racoon: INFO: purged IPsec-SA spi=155865592. Feb 12 00:45:29 racoon: INFO: purging ISAKMP-SA spi=ksdjdfslkdj8498ds8:203j9390j09d0d0d:00007af7. Feb 12 00:45:29 racoon: INFO: purged IPsec-SA proto_id=ESP spi=3055141787. Feb 12 00:45:29 racoon: INFO: deleting a generated policy. Feb 12 00:45:04 racoon: [Self]: INFO: IPsec-SA established: ESP xxx.xxx.xxx.xxx.181[500]->192.168.49.2[500] spi=3055141787(0xb619c39b) Feb 12 00:45:04 racoon: [Self]: INFO: IPsec-SA established: ESP xxx.xxx.xxx.xxx.181[500]->192.168.49.2[500] spi=155865592(0x94a51f8) Feb 12 00:45:04 racoon: INFO: Adjusting peer's encmode UDP-Tunnel(3)->Tunnel(1) Feb 12 00:45:04 racoon: INFO: Adjusting my encmode UDP-Tunnel->Tunnel Feb 12 00:45:04 racoon: INFO: no policy found, try to generate the policy : 192.168.2.1/32[0] 0.0.0.0/0[0] proto=any dir=in Feb 12 00:45:04 racoon: [Self]: INFO: respond new phase 2 negotiation: xxx.xxx.xxx.xxx.181[4500]<=>192.168.49.2[4500] Feb 12 00:45:04 racoon: WARNING: Ignored attribute INTERNAL_ADDRESS_EXPIRY Feb 12 00:45:04 racoon: INFO: login succeeded for user "username" Feb 12 00:45:04 racoon: INFO: Using port 0 Feb 12 00:45:04 racoon: [192.168.49.2] INFO: received INITIAL-CONTACT Feb 12 00:45:04 racoon: [Self]: INFO: ISAKMP-SA established xxx.xxx.xxx.xxx.181[4500]-192.168.49.2[4500] spi:ksdjdfslkdj8498ds8:203j9390j09d0d0d Feb 12 00:45:04 racoon: INFO: Sending Xauth request Feb 12 00:45:04 racoon: INFO: NAT detected: ME PEER Feb 12 00:45:04 racoon: INFO: NAT-D payload #1 doesn't match Feb 12 00:45:04 racoon: [192.168.49.2] INFO: Hashing 192.168.49.2[4500] with algo #2 Feb 12 00:45:04 racoon: INFO: NAT-D payload #0 doesn't match Feb 12 00:45:04 racoon: [Self]: [xxx.xxx.xxx.xxx.181] INFO: Hashing xxx.xxx.xxx.xxx.181[4500] with algo #2 Feb 12 00:45:04 racoon: [Self]: INFO: NAT-T: ports changed to: 192.168.49.2[4500]<->xxx.xxx.xxx.xxx.181[4500] Feb 12 00:45:04 racoon: INFO: Adding xauth VID payload. Feb 12 00:45:04 racoon: [Self]: [xxx.xxx.xxx.xxx.181] INFO: Hashing xxx.xxx.xxx.xxx.181[500] with algo #2 Feb 12 00:45:04 racoon: [192.168.49.2] INFO: Hashing 192.168.49.2[500] with algo #2 Feb 12 00:45:04 racoon: INFO: Adding remote and local NAT-D payloads. Feb 12 00:45:04 racoon: [192.168.49.2] INFO: Selected NAT-T version: RFC 3947 Feb 12 00:45:04 racoon: INFO: received Vendor ID: CISCO-UNITY Feb 12 00:45:04 racoon: INFO: received Vendor ID: DPD Feb 12 00:45:04 racoon: INFO: received broken Microsoft ID: FRAGMENTATION Feb 12 00:45:04 racoon: INFO: received Vendor ID: RFC 3947 Feb 12 00:45:04 racoon: INFO: received Vendor ID: draft-ietf-ipsec-nat-t-ike-03 Feb 12 00:45:04 racoon: INFO: received Vendor ID: draft-ietf-ipsec-nat-t-ike-02 Feb 12 00:45:04 racoon: INFO: received Vendor ID: draft-ietf-ipsec-nat-t-ike-01 Feb 12 00:45:04 racoon: INFO: received Vendor ID: draft-ietf-ipsec-nat-t-ike-00 Feb 12 00:45:04 racoon: INFO: received Vendor ID: draft-ietf-ipsra-isakmp-xauth-06.txt Feb 12 00:45:04 racoon: INFO: begin Aggressive mode. Feb 12 00:45:04 racoon: [Self]: INFO: respond new phase 1 negotiation: xxx.xxx.xxx.xxx.181[500]<=>192.168.49.2[500]If I need to include more information please let me know. I have seen several posts similar to mine but for some reason nobody ever posts their solution.
I need to get this working as soon as possible.
Thanks in advance,
cakewipe</none> -
No replies? Am I so far off that I can't be helped? ???
-
On pfSense, ensure you have the Phase 2 Local Network Type set to LAN subnet or whatever network your server resides on. Also, on the mobile settings list, check the Network List, I do not know why the guides on here say not to do that.
On the Shrewsoft client, make sure you have Policy Generation set to Unique, and Obtain Topology Automatically enabled.
Eventually, you may want to force NAT Traversal on, but wait until you have a stubborn network which you cannot VPN from before you try that.
-
Hi,
Thanks for the help and sorry for the long delay but I've been working on other projects.
Vorkbaard sent me this reply via IM.
@Vorkbaard:Hi, I read your post and I had more or less the same problem. I'm sending you a dm so as not to spam the forum as I have already posted a general topic advertising the article I wrote on how I solved this.
If you're interested, here is my solution: https://sites.google.com/a/vorkbaard.nl/dekapitein/tech-1/how-to-set-up-ipsec-tunneling-in-pfsense-2-0-release-for-road-warriors
Hope it helps!
I followed his instructions and now I am able to see my pfSense server admin console and ping it fine over the vpn but I still can't ping the file server access the URL of the server.
In the instructions he doesn't go into the firewall or the NAT settings very much and I'm wondering if this is my problem.
I went in and opened all ports for IPsec and WAN and LAN but I still cant see the fileserver.I've made a simple drawing of my setup and I'm hoping someone can help me figure out why I cant see my fileserver.
None of the other replies helped at all and if I can't figure pfsense out then I may need to go to another type of router. :'(
My setup is really very simple but I can't seam to figure out what I am missing I am sure it's something simple.Thanks in advance.
-
Can nobody help?
I can access the internet from the server through the pfsense router and can connect to the router through vpn I just can't access the server. -
After a TON of reading and trial and error I finally found a setting that allowed me to ping my fileserver. I've noticed a ton of people have similar issues and nobody seams to help them so I'm hoping this will help someone.
In the forum I stumbled across this post http://forum.pfsense.org/index.php/topic,49289.0.html his network seams much different from mine but I decided to follow the instructions laid out here: http://doc.pfsense.org/index.php/Why_can%27t_I_query_SNMP,_use_syslog,_NTP,_or_other_services_initiated_by_the_firewall_itself_over_IPsec_VPN%3F
I had to setup a Static Route
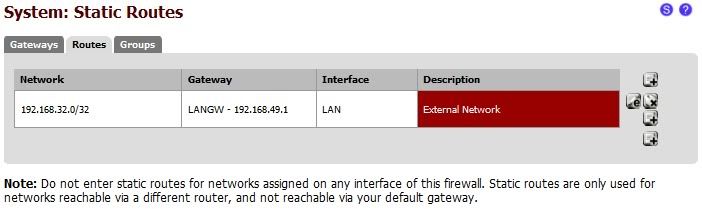
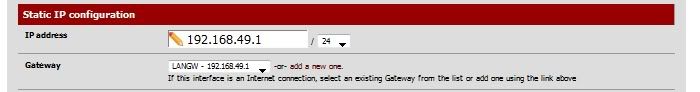
and I also had to add the LAN IP address as my LAN Gateway
I can now ping just fine but I don't understand why this static route was necessary. Mine is a simple client connecting to a server through IPSec VPN. This seams like one of the most basic VPN configurations and something like this wouldn't be necessary.
Since I've setup this static route my connection has become VERY unstable.
Is there a better solution someone can think of? -
Finally after much trial and error, I decided to pay the $600 for support to figure out why I couldn't access my server without a static route. It turns out my default gateway on my server got reset to 0.0.0.0. I know this is a stupid error but I did set it up before. It took many hours to figure out and I hope this can help someone else. I could see the server through a cisco vpn with the same settings so I didn't think it could be a setting on the Server itself.
With their help, I was able to configure my vpn to be accessible through Shrewsoft (windows), IOS and Android devices. I am trying to document the settings I used but in the meantime if anyone needs help with the same thing ping me and I can send you the settings I have.
Thanks to chris and jim for your help.
-
As an additional note, the reason it was working with the static route wasn't because of the static route, but because you had the LAN "gateway" set on the LAN interface page, which caused it to apply outbound NAT to the traffic leaving the LAN interface. Due to the outbound NAT, the traffic leaving that interface appeared to come from the firewall itself, so it returned OK since your server believed it originated from within its own subnet.
Kind of a tricky one, surely.
-
Finally after much trial and error, I decided to pay the $600 for support to figure out why I couldn't access my server without a static route. It turns out my default gateway on my server got reset to 0.0.0.0. I know this is a stupid error but I did set it up before. It took many hours to figure out and I hope this can help someone else. I could see the server through a cisco vpn with the same settings so I didn't think it could be a setting on the Server itself.
With their help, I was able to configure my vpn to be accessible through Shrewsoft (windows), IOS and Android devices. I am trying to document the settings I used but in the meantime if anyone needs help with the same thing ping me and I can send you the settings I have.
Thanks to chris and jim for your help.
Can you send me the configuration details…pls...ssl3004@yahoo.com
thanks
-
Can you send me the configuration details…pls...ssl3004@yahoo.com
thanks
Sent to ssl3004@yahoo.com
-
I have added my documentation to google docs so anyone can see it.
Here is the link for pfSense Router settings
https://docs.google.com/file/d/0B2zOOBoh3isOSmtYakVEc3ZNWDA/edit?usp=sharingHere is the link for Shrewsoft, Android, iOS Clients.
https://docs.google.com/document/d/1Pl21sk7ckU6dSqgxtXu6iNIv8-60bv7AFFVUQwdJ_WE/edit?usp=sharingPlease leave comments if this is helpful so I will know not to remove the documents from my share.
-
I have added my documentation to google docs so anyone can see it.
Here is the link for pfSense Router settings
https://docs.google.com/file/d/0B2zOOBoh3isOSmtYakVEc3ZNWDA/edit?usp=sharingHere is the link for Shrewsoft, Android, iOS Clients.
https://docs.google.com/document/d/1Pl21sk7ckU6dSqgxtXu6iNIv8-60bv7AFFVUQwdJ_WE/edit?usp=sharingPlease leave comments if this is helpful so I will know not to remove the documents from my share.
Hello Cakewipe,
Thanx for your work here. I am having a similar problem you had. When the client connects, there is no route handed to the client according to ipconfig on the windows box.I see not route to that network on the pfsense box.
So looking over your doc above it looks like you are still using the static route, is that true?
Did you have to use PSK-Xauth? It wouldn't work with just PSK?
I looked over your doc