NAT reflection behaviour changes after upgrade from 2.03 to 2.1
-
Hello,
we are using a pfSense (CARP HA) setup for one of our customers.
Network schema (three ethernet interfaces):
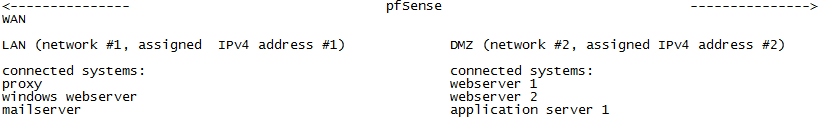
–-Direct traffic between LAN <-> DMZ is not permitted.
All incoming URI based http/https connections, which are assigned via DNS to IPv4 address #1, are redirected via NAT to the proxy server (LAN).
Depending on the URI the proxy redirects the request to the internal ip of the windows webserver (LAN) or to external IPv4 addresses #2 or #3 (dedicated for DMZ subnet) of WAN webserver 1 (DMZ) or webserver 2 (DMZ).If webserver 1 or webserver 2 tries to load some content via the external URI using f. exp. PHP fsockopen it made a external outbound connection and connects to the proxy in LAN over WAN with option "NAT reflection" activated (behaviour in 2.03).
The issue can also be verified with mails, sent out from the application server (DMZ) to mailserver (LAN).
Since the upgrade to 2.1 both connections does not work any more.tcpdump and the "Packet Capture" tool inside pfSense Webinterface shows up, that the request was sent correctly from the sender host and received at the pfSense.
The systems (webserver 1, webserver 2, application server 1) tries directly to access from DMZ subnet to the internal ip addresses of LAN subnet, which is not permitted because of the concept of a DMZ.
pfSense does not reassigned this connections to external or reflect this connection as in 2.03, which lead to that, that the connection is made to the internal ip addresses of LAN subnet.
At all incoming NAT rules (WAN interface) NAT reflection is set to "NAT+Proxy", but it seems, that the connection is not handled correctly at the pfSense.
Outbound NAT is set to "Manual Outbound NAT rule generation (AON - Advanced Outbound NAT)"A shortened extract of the outbound nat mapping for network #2 (network #1 is same except the other IPv4 address):
Interface Source SPort Dest DPort NAT adress NPort StPort Description
WAN network #2/24 * * 500 WAN address * YES Auto created rule for ISAKMP - DMZ to WAN
DMZ network #2/24 * * * IPv4 address #2 * NO Outgoing SNAT Public 2
WAN network #2/24 * * * IPv4 address #2 * NO Auto created rule for DMZ to WAN
As read in one other thread the automatic created outbound NAT rules are not visible inside the webinterfaceAt "System: Advanced: Firewall and NAT" the checkbox "Enable automatic outbound NAT for Reflection" was activated.
Setting "NAT Reflection mode for port forwards" is configured to "NAT+Proxy".A telnet session from a member of the DMZ subnet to the external IPv4 address #1, which is forwarded via NAT to member of LAN subnet, initialized f. exp. from the application server 1 (DMZ) shows up, that the connected port is open by netcat, but the request is not redirected to the desired target service (f. exp. postfix on the Mailserver (LAN)) and does not give the expected answer (f. exp. "220 mail.host.tld ESMTP Postfix").
I already read workarounds to not use NAT reflection, instead using local ip addresses (not suitable because it would break the concept of DMZ) or use split brain dns via customized dns forwarder (dns zone management is done by our customer self, so it would be difficult to keep all changes in sync). Both workarounds are not applicable, we only want to reobtain the earlier behaviour of nat reflection.
Could you please give me a hint for further troubleshooting or how to fix the issue?
Best regards