Site-to-site VPN broke after adding 2nd WAN *SOLVED*
-
Hey folks,
I've been tackling some dual WAN issues lately. I have gotten a lot of help from the forums and I am excited about what all I am learning in the process.
This is my last, but biggest issue that I have encountered since adding a 2nd WAN connection (opt1).
I have a site-to-site IPsec VPN between a 1.2 RC 3 and a 1.1 box. It has worked flawlessly for quite a while (I was on 1.1, then 1.2 RC) and will, on occasion work with my current setup. However, since adding my 2nd WAN connection its been flaky at best. The logs show the tunnel is enabled and established, but I cannot route traffic between the connections in either direction.I am doing policy based routing between the two WAN connections. WAN is for business and gets work VPN, VoIP and Email server traffic. The Opt1 connection is a personal connection and gets all other traffic (most machines on the LAN). Both connections allow incoming VPN that terminates at an L2TP server (not PFsense) inside the LAN.
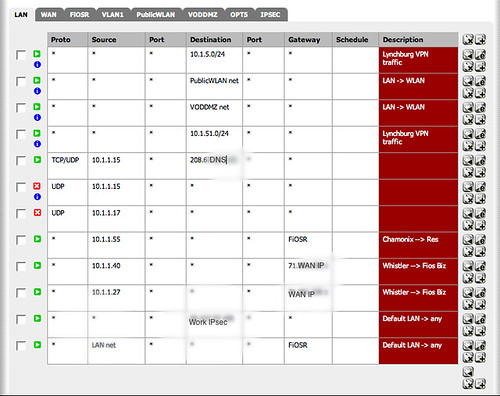
The VPN uses the 1st WAN (WAN) connection. I have tried adding a rule to my LAN that sends any traffic bound for the remote subnet over the default gateway (WAN). Rules shown below.
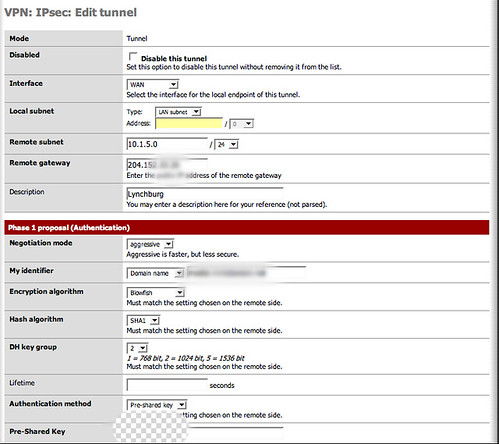
VPN setup
Here is a segment from the log (IPs masqueraded)
Lynchburg is the name of the other site, FYI (my site is Richmond)Dec 19 12:01:04 racoon: [Self]: INFO: 10.1.2.1[500] used as isakmp port (fd=25) Dec 19 12:01:04 racoon: INFO: fe80::280:c8ff:feb9:6d8e%dc1[500] used as isakmp port (fd=24) Dec 19 12:01:04 racoon: [Self]: INFO: 10.1.20.1[500] used as isakmp port (fd=23) Dec 19 12:01:04 racoon: INFO: fe80::280:c8ff:feb9:6d8f%dc2[500] used as isakmp port (fd=22) Dec 19 12:01:04 racoon: [Self]: INFO: 71.251.xxx.zzz[500] used as isakmp port (fd=21) Dec 19 12:01:04 racoon: INFO: fe80::230:48ff:fe41:134%fxp0[500] used as isakmp port (fd=20) Dec 19 12:01:04 racoon: [Self]: INFO: 10.1.1.1[500] used as isakmp port (fd=19) Dec 19 12:01:04 racoon: INFO: fe80::230:48ff:fe41:135%fxp1[500] used as isakmp port (fd=18) Dec 19 12:01:04 racoon: [Self]: INFO: 127.0.0.1[500] used as isakmp port (fd=17) Dec 19 12:01:04 racoon: INFO: ::1[500] used as isakmp port (fd=16) Dec 19 12:01:04 racoon: INFO: fe80::1%lo0[500] used as isakmp port (fd=15) Dec 19 12:00:47 racoon: [Lynchburg ]: INFO: IPsec-SA established: ESP/Tunnel 71.251.xxx.zzz[0]->204.152.aaa.bbb[0] spi=90568807(0x565f867) Dec 19 12:00:47 racoon: [Lynchburg ]: INFO: IPsec-SA established: ESP/Tunnel 204.152.aaa.bbb[0]->71.251.xxx.zzz[0] spi=253614950(0xf1ddb66) Dec 19 12:00:47 racoon: [Lynchburg ]: INFO: initiate new phase 2 negotiation: 71.251.xxx.zzz[0]<=>204.152.aaa.bbb[0] Dec 19 12:00:45 racoon: [Lynchburg ]: INFO: ISAKMP-SA established 71.251.xxx.zzz[500]-204.152.aaa.bbb[500] spi:0f242faafad5b01c:0b43ac155a9cb5a0 Dec 19 12:00:45 racoon: NOTIFY: couldn't find the proper pskey, try to get one by the peer's address. Dec 19 12:00:45 racoon: WARNING: No ID match. Dec 19 12:00:45 racoon: INFO: received Vendor ID: DPD Dec 19 12:00:45 racoon: INFO: begin Aggressive mode. Dec 19 12:00:45 racoon: [Lynchburg ]: INFO: initiate new phase 1 negotiation: 71.251.xxx.zzz[500]<=>204.152.aaa.bbb[500] Dec 19 12:00:45 racoon: [Lynchburg ]: INFO: IPsec-SA request for 204.152.aaa.bbb queued due to no phase1 found. Dec 19 12:00:45 racoon: INFO: unsupported PF_KEY message REGISTERLan Rules
-
Setup your VPNs as normal. Now add a rule to each firewalls LAN interface and permit traffic from the LAN subnet to destination private network and set the gateway as DEFAULT (*).
EDIT: the rule needs to be moved to the top as well.
-
Setup your VPNs as normal. Now add a rule to each firewalls LAN interface and permit traffic from the LAN subnet to destination private network and set the gateway as DEFAULT (*).
EDIT: the rule needs to be moved to the top as well.
Scott,
Thank you very much for the reply.
Would that rule be the same ad the first rule in my screenshot above?
I will add that to the remote PFsense box as well and see if it helps.For what its worth, I seem to get about 24 hours of working VPN between reboots (of my local PFsense box). Something is happening over night that seems to break things.
-
The VPN has been up for over 48 hours.
Thanks Scott- I think adding the rules solved the problem! -
Well…back to this old topic again.
After a few months of smooth sailing, we've started running into problems again.
The other site had a 24 hour outage on their T1 which has been resolved, but since then the VPN is broken again.The Web Console reports that the link is up, but neither LAN can reach each other.
Any thoughts on what might have changed or what I can do to troubleshoot?
-
is this still rc3?
-
-
yes, yes of course….
please try the inofficial rc5http://forum.pfsense.org/index.php/topic,7822.0.html
-
Well, it appears that an attempt to troubleshoot my xbox live connection fixed my VPN!!!
http://forum.pfsense.org/index.php/topic,7740.0.htmlI enabled manual outbound NAT (something I had to disable before to make it work) and presto, everything started flowing correctly. It will be a bit of a challenge because it appears I will have to be pretty diligent in setting the outbound rules in two places now, but thats not the end of the world if it works.
Thanks to everyone who helped troubleshot this!
…now if I could figure out how to mark this as "solved"....
-
"solved" done :)