3 WAN, 2 isolated LAN's - help with configuration!
-
I've inherited a bit of a wacky network setup in my workplace. My basic configuration is as follows:
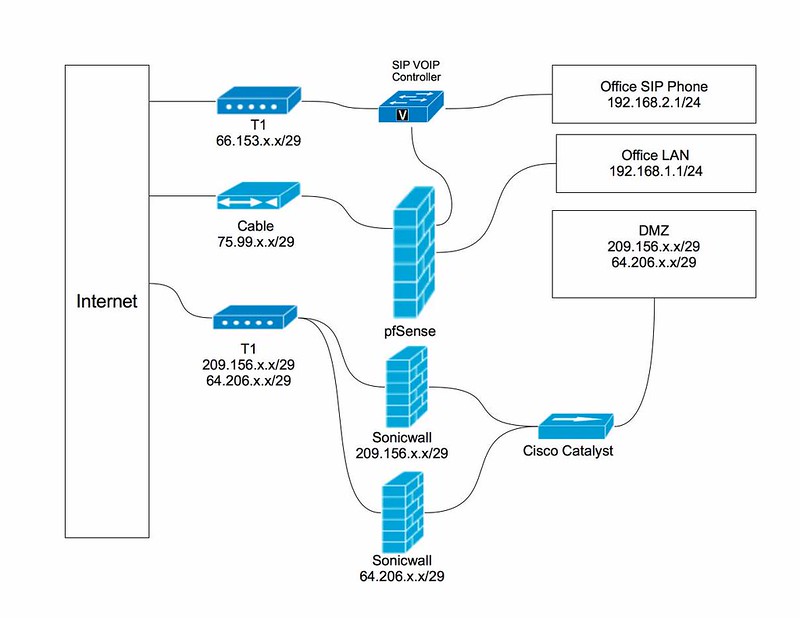 White Plains Network Diagram - 2014-04-17 by gojoshgo42, on Flickr
White Plains Network Diagram - 2014-04-17 by gojoshgo42, on Flickr
(click through for full resolution)The two Sonicwalls are essentially bridging two netblocks together (apparently the company that provided us with the T1 couldn't give 2 contiguous netblocks), and each server behind the firewall has a public IP assigned on a 1-to-1 basis. The firewalls to only filter some ports, though. The Sonicwalls, switch and servers behind them are managed by an outside company. There are two Sonicwalls not for failover, but because the particular models they're using can't be configured for more than one netblock. :o
The pfSense firewall, servers and workstations behind it, and the SIP network are what I'm responsible for.
Unfortunately the Sonicwalls have been locking up and requiring a reboot 1-2 times a day for the past few days The box we're using for pfSense has 3 spare interfaces right now, so I was considering moving the connections that currently go through the Sonicwalls, into the pfSense box. The networks would remain logically separated, although employees on the LAN do need to route to the servers currently behind the Sonicwall.
Here's what I am hoping to achieve:
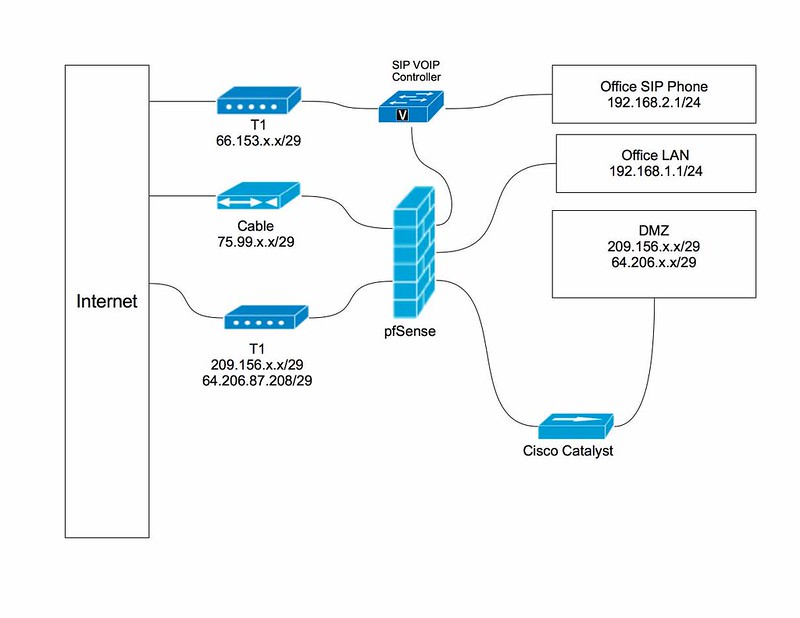 White Plains Network Diagram - proposed - 2014-04-17 by gojoshgo42, on Flickr
White Plains Network Diagram - proposed - 2014-04-17 by gojoshgo42, on Flickr
(again, click for full resolution).I'm a little confused on how to best implement this, though. I need to have the new WAN interface have both netblocks assigned to it, and it needs to route to the Cisco Switch. Additionally, employees on the LAN need to be able to get to the servers. I've seen references to bridging interfaces to create a DMZ, but I'm not sure that's quite what I need.
I don't have a non-production pfSense instance to try configurations out on, so I was hoping to get some guidance before I proceed. I'll be trying to apply the new configuration off-hours, but the more down time, the more complaints, as people access all servers at all hours.
Please forgive my ignorance, poor network diagrams, and wacky requirements. Because I don't have the ability to manage the servers with public IP's, I can't implement a sane set up (at least not for a while), so I'm stuck trying to get something working with what I have…