VLAN won't communicate with LAN
-
@johnpoz
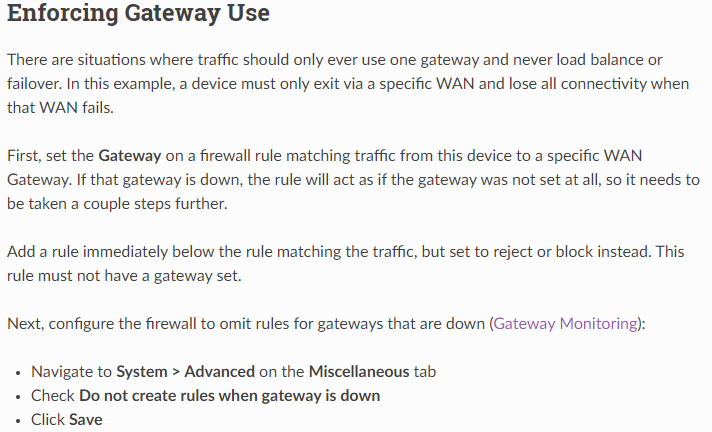
AFAIK he has set "disable rule when gateway is down" , and the next is to blackhole if the above rule is disabled. -
@johnpoz But haven't i done like it says in here, or am i missunderstanding something?
-
If he set gateway down disable rule - still no traffic allowed because there is no allow rule. What is the point of that block rule? Unless specific do not want to log traffic?
Only when that gateway is down?
-
@johnpoz I honestly have no idea - i just followed what's said on the Netgate site.
@bingo600
Sorry for waking this thread up again, but i can't understand what's wrong here.. I have 8 devices under "EJFAST" that works just fine, but one device can't access internet.. Only when i disable my block rule from talking to other networks "LOKALA", internet works for that device (?) So, now when i check the logs i can see it's trying to connect on my LAN with port :53, so just like "WIFI" interface, i added the DNS rule on "EJFAST" interface aswell, but - i still get the same deny in logs, and the device can't access internet.. Any ideas?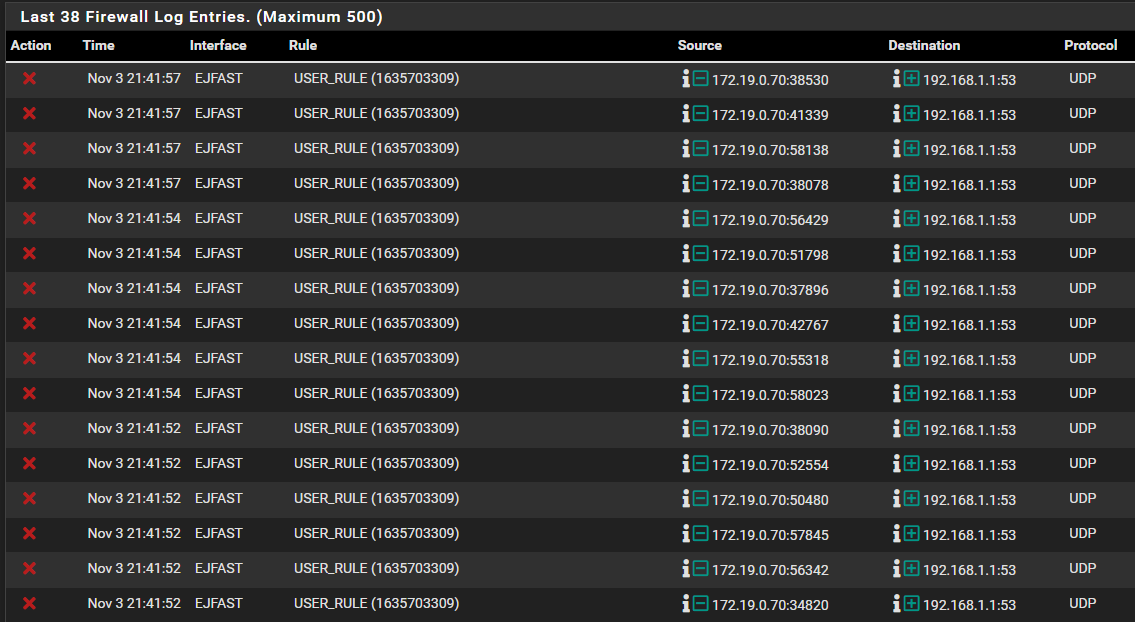
Thanks!
-
@djjoakim well where is your rule that would allow that traffic before you block it.
if something is trying to use 192.168.1.1 for dns - and your not allowing it - then no internet not going to work without dns..
i just followed what's said on the Netgate site.
Where - there is no where on site that says to make pointless rules..
Trying to apply a guide without understanding what is actually going on and what the rules actually do is going to lead to nonsense rules that make no sense in whatever setup your trying to do..
-
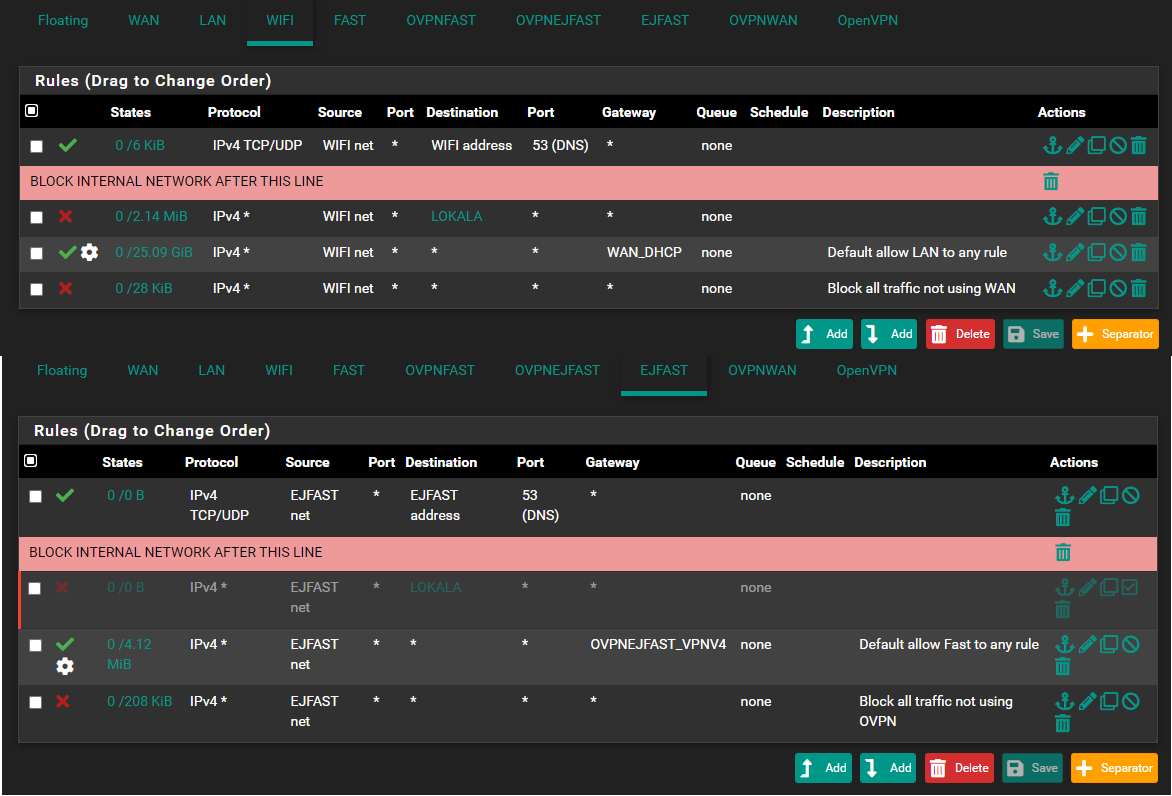
@johnpoz Yes i understand that... but the part i don't understand is that on the interface "WIFI" i added DNS rule, as shown below - and then it worked. But even with this rule added to "EJFAST" it won't work..
Well like i said, i am new to this and trying to learn, so i follow the guides that are available, please correct me if there is something i have misunderstand with this guide.
It's impossible to know everything with 1 week of knowledge.
-
-
That would be a kill switch for a vpn connection. Which your using wan dhcp gateway. So makes no sense in this context.
Blindly following some guide that makes no sense for what your doing - leads to nonsense rules..
You would only need such a rule if you have an allow rule below your policy route rule, if you didn't want that allow rule to be used - then you would need a block rule above the allow rule.
You have no ALLOW rule.. So like I said your traffic would be denied by default...
-
@johnpoz
yeah, you are right, I was shooing in the blind. Long time since I used OpenVPN. I use WG, and have no problem too accessing different networks locally. -
Your "deny" log showed that pfSense blocked EJFAST clients , sending DNS packets to 192.168.1.1 (Lan interface)
My guess is that you have set that DNS (LAN) IP in the EJFAST DHCP definitions.So you either have to remove the entry from the DHCP (then it will default to the connected interface , here EJFAST). .... Preferred.
Or allow DNS from EJFAST net to LAN address
/Bingo
-
@bingo600 Yep... got it working. Thank you so much again.. :)