Chrony, PTP, Network Time Security (NTS, NTPsec) to replace unsecure/old NTP (ntpd)
-
@johnpoz said in Network Time Security (NTS, NTPsec) to replace unsecure/old NTP (ntpd):
I think 3.5 is available since freebsd 12?
Ah, right it's already 4.1 currently...
https://www.freebsd.org/cgi/ports.cgi?query=Chrony&stype=all++++edit:
Then all we need is PHP, Netgate and you're done :-) -
@daddygo said in Network Time Security (NTS, NTPsec) to replace unsecure/old NTP (ntpd):
Then all we need is PHP, Netgate and you're done
Easy peasy ;) @Sergei_Shablovsky can you knock that out this afternoon ;) hehehe
-
@daddygo said in Network Time Security (NTS, NTPsec) to replace unsecure/old NTP (ntpd):
@johnpoz said in Network Time Security (NTS, NTPsec) to replace unsecure/old NTP (ntpd):
I think 3.5 is available since freebsd 12?
Ah, right it's already 4.1 currently...
https://www.freebsd.org/cgi/ports.cgi?query=Chrony&stype=all++++edit:
Then all we need is PHP, Netgate and you're done :-)As You may see both for ntpd (FreeBSD) and Chrony (FreeBSD, offsite) a lot of settings are common, so most users that need NTP service on pfSense would have short adoption time and not to be disappointed by a lot of new options in NTP GUI.
The main question is still “because of ntpd was outdated is replacement to Chrony in pfSense NTP service needed, or better to keep both ntpd and Chrony as additional pfSense package”.
Anyway time of ntpd gone away (like most of old protocols) and one day this question pop up again. Why need to be so sticky to old protocol? Chrony able to keep old-fashioned ntpd clients well without any issues, Chrony already exist in FreeBSD 12 and 13...
-
@sergei_shablovsky said in Chrony, Network Time Security (NTS, NTPsec) to replace unsecure/old NTP (ntpd):
The main question is still “because of ntpd was outdated is replacement to Chrony in pfSense NTP service needed, or better to keep both ntpd and Chrony as additional pfSense package”.
NTP should not be removed from pfSense , it is still the industry standard, for timekeeping.
Anyway time of ntpd gone away (like most of old protocols) and one day this question pop up again. Why need to be so sticky to old protocol? Chrony able to keep old-fashioned ntpd clients well without any issues, Chrony already exist in FreeBSD 12 and 13...
How do you come to that conclusion : That "time of ntpd gone away" ?
It is my impression that: Before this thread you didn't even know Chrony existed .....If you can convince Netgate to or implement your self: A Chrony integration then by all means go do it. An additional pfSense Chrony package wouldn't hurt.
But don't "slaugther" the NTP package (implementation), just because you got an idea.
/Bingo
-
@bingo600 said in Chrony, Network Time Security (NTS, NTPsec) to replace unsecure/old NTP (ntpd):
@sergei_shablovsky said in Chrony, Network Time Security (NTS, NTPsec) to replace unsecure/old NTP (ntpd):
The main question is still “because of ntpd was outdated is replacement to Chrony in pfSense NTP service needed, or better to keep both ntpd and Chrony as additional pfSense package”.
NTP should not be removed from pfSense , it is still the industry standard, for timekeeping.
Anyway time of ntpd gone away (like most of old protocols) and one day this question pop up again. Why need to be so sticky to old protocol? Chrony able to keep old-fashioned ntpd clients well without any issues, Chrony already exist in FreeBSD 12 and 13...
How do you come to that conclusion : That "time of ntpd gone away" ?
It is my impression that: Before this thread you didn't even know Chrony existed .....I just try to make things better. (“better” means in technical term;)
I hands up on Your solution, because it’s better than only implementing NTS/NTPsec.
If you can convince Netgate to or implement your self: A Chrony integration then by all means go do it. An additional pfSense Chrony package wouldn't hurt.
But don't "slaugther" the NTP package (implementation), just because you got an idea.
;) Ok, let’s start with Chrony in addition to pfSense's ;)
-
@sergei_shablovsky said in Chrony, Network Time Security (NTS, NTPsec) to replace unsecure/old NTP (ntpd):
“because of ntpd was outdated
hmmmm,

This is a very tough and I think premature statement, the whole world cannot be so foolish as to trust its life to an outdated protocol, yes its life, because we depend on it at the moment
-not to mention the fact that this money-modulated world of ours is also run by this protocol in terms of money
we think it is not so important, but it is and it still works well in the background
Ok, I see that you registered at the end of 2019, ergo you can see that introducing a new thing to pfSense is not a "torch marching"
at the moment there are other more important things to be improved, which I think is a priority
https://redmine.pfsense.org/projects/pfsense/roadmapDon't get me wrong, we would love to see your work, if you take on this challenge, have here a couple of "well versed in the ways of time" colleague, you know :) and we could certainly help...
BTW:
There were some attempts that I was interested in at one time (ntpv3 vs. ntpv4), but I stayed with the multi-source (3-5) NTP
https://blog.cloudflare.com/roughtime/And for important workloads, as I mentioned above, PTP IEEE 1588-2002 / IEEE 1588-2008 for audio remains the target hardware Meinberg
-
@daddygo
What switches are you using to distribute your PTP, around on the site(s) ?
That's imho the biggest PTP Killer, that you's need all your switches to be PTP enabled.Especially if you already have an existing (working) switch infrastructure.
I for one doesn't have a single PTP enabled switch at home.
And would prob. not be paying extras for one.Then again if i needed any of my home devices to "Really" be in "sync" i would prob. just distribute my GPSDO (or PRS-10 Rubidium) 1-PPS around using balanced mode and RJ-45 cables. Not an optimal method in a large corp building.
/Bingo
-
@bingo600 said in Chrony, Network Time Security (NTS, NTPsec) to replace unsecure/old NTP (ntpd):
What switches are you using to distribute your PTP, around on the site(s) ?
Let's see.....
Enterprise level:
One that has worked for us for a long time (and since we also do video processing) is the Arista 7500 series family:
https://www.arista.com/assets/data/pdf/Whitepapers/ME-PTP-White-Paper.pdf
https://www.arista.com/assets/data/pdf/Datasheets/7500RDataSheet.pdf
My experience so far is that this cannot be done well and cost-effectively in a SOHO environment.
In our smaller studios we use the following devices, synchronized from an external clock source:
https://studio-tech.com/products/m5401a/
(with GPS module opc.)
+++ Cisco Catalyst 3800 series + 10G optic network (in-house facilities)
https://www.cisco.com/c/en/us/products/collateral/switches/catalyst-9300-series-switches/q-and-a-c67-744007.pdf@bingo600 "Especially if you already have an existing (working) switch infrastructure."
When we changed to DANTE AoIP and AES67 we changed the complete L1 - L2 infrastructure...
This is the only reasonable way to do it, as good PTP is the rule of thumb for real-time audio deliveryWe implemented this DANTE stuff almost 7 years ago, as the first radio network in Central Europe,
It has a lot of pitfalls, but once I get it right it's very convenient, I can route the sound exactly like TCP, hahahaha...Our mixing tables are also software based, no more FADER replacement because the mechanics components are tired
We represent America in Europe
https://www.arrakis-systems.com/arrakis---darc-virtual-console.html
(My company is the representative of Arrakis)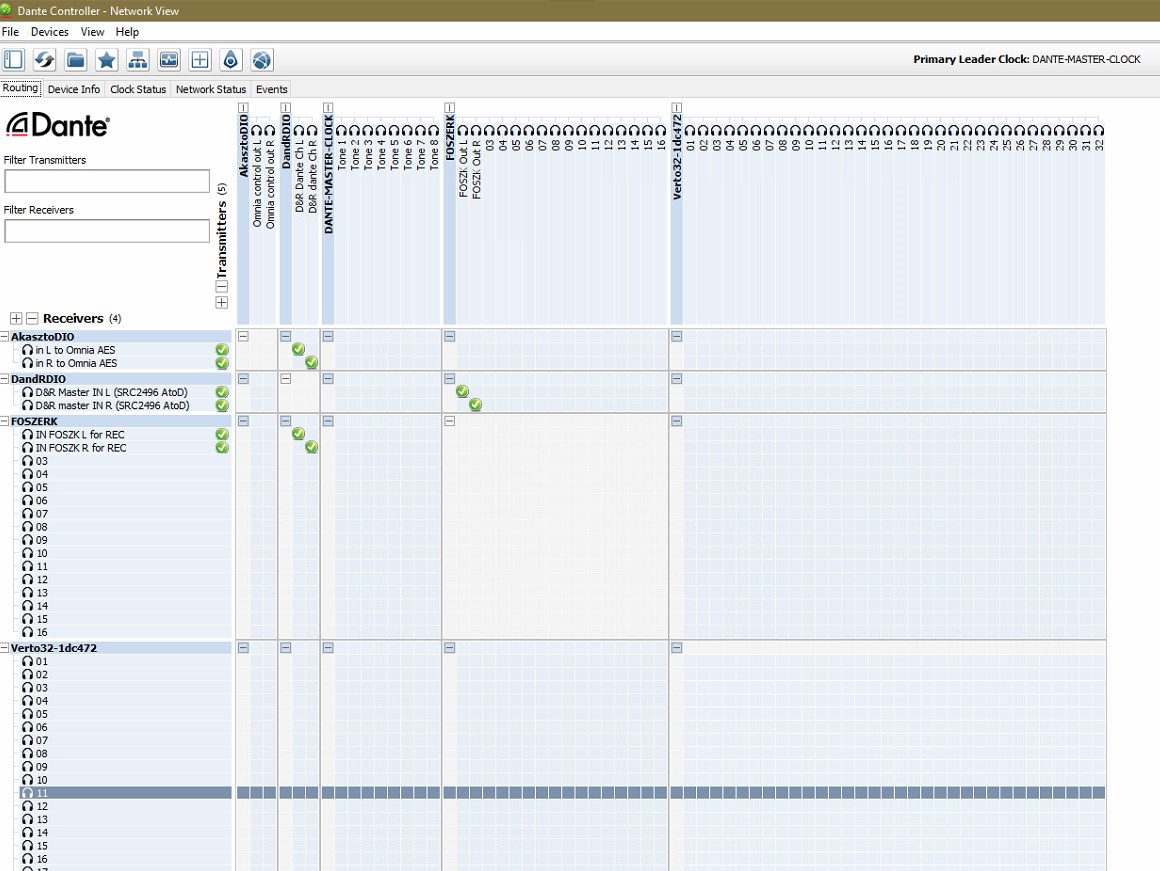
So here I encountered the concept of time in more depth, and here as well Hawking - The Time :)
-
@daddygo said in [Chrony, Network Time Security (NTS, NTPsec) to
+++ Cisco Catalyst 3800 series + 10G optic network (in-house facilities)
https://www.cisco.com/c/en/us/products/collateral/switches/catalyst-9300-series-switches/q-and-a-c67-744007.pdfI could have gotten two c3800,for less than $500, but they're power hungry and noisy. So i skipped on those.
You linked the C9300, those are nice DC Switches, but quite above a "home budget" ... Even the SFP+ are above , i'we set up a few in a DC.
, i'we set up a few in a DC.Well i'm not routing Pro audio or Video , so i'll stick to my home time-nuttery
/Bingo
-
@bingo600 said in Chrony, Network Time Security (NTS, NTPsec) to replace unsecure/old NTP (ntpd):
Well i'm not routing Pro audio or Video , so i'll stick to my home time-nuttery
Yeah, these are big boy toys....

I can't remember exactly, but the cost of acquisition was close to 350K USDIn a normal family house they are not applicable, as you write a nuclear power plant should be bringing for them...
I just took it out of the storeroom 2 pcs. Cisco UCS FI6248UP Fabric Interconnect to upgrade the UCS Manager on them before they go to the market, my wife chased me around the house with a big knife, because of the noise. (they only operated for half a day) hihihihihi
I keep animals like these at home:
1 pcs. MikroTik CRS305-1G-4S+IN for GPON distribution
2 pcs. Cisco SG500XG-8F8T (in stack)
2 pcs. Cisco SG350X-24P
1 pcs. SuperMicro M11SDV-4C-LN4F + Intel X710-DA4 for pfSense
1 pcs. SuperMicro SYS-E300-12C + Intel Xeon W1290 for VMs
1 pcs. Synology RS1221RP+ for storage
3 pcs. Cisco AIR-AP1852I-E-K9 for wirelessIt's plenty for home use :)
-
@daddygo said in Chrony, Network Time Security (NTS, NTPsec) to replace unsecure/old NTP (ntpd):
2 pcs. Cisco SG500XG-8F8T (in stack)
2 pcs. Cisco SG350X-24PThose for sure would be sweet for home use - nice! I am jealous for sure..
-
@johnpoz said in Chrony, Network Time Security (NTS, NTPsec) to replace unsecure/old NTP (ntpd):
Those for sure would be sweet for home use - nice! I am jealous for sure..
I got lucky with the 500s, I bought from an Australian guy on eBay about a year ago, he either didn't know what he was selling or was too nice to sell me a pair 500 + 6pcs. twinax cables for AUD 850.
(Oh yes, I arranged the shipping from AU, including with customs, was 180 USD)The SG350Xs are from the radio company, they just fell off the truck and I snapped them up, :)
-
@daddygo said in Chrony, Network Time Security (NTS, NTPsec) to replace unsecure/old NTP (ntpd):
3 pcs. Cisco AIR-AP1852I-E-K9 for wireless
I'm still at 1Gbit at home.
All using lowpower fanless switches.My "Server" (File,Mail, DNS & DHCP) is a Deb-10 Linux , running on an 2GHz Atom.
I just have a "Little" Acer-Revo (Core i3 - 16GB Ram + SSD) for VMware
Runs my Zabbix monitoring and PI-Hole , and a few other Debian'sI have C2702E AP's here & in the summerhouse ($42/pcs).
Those SG500's looks nice , but atm. i really have no need for 10G.
Maybe with the "Next Server" ...
But my wife has a BIGGER KNIFE than yours , and has "Fan allergy" , besides she can hear the "grass grow"I just said no to a DLP360 G9 server for free

Was NEVER going to get away with that one .... (Office next to the bedroom)/Bingo
-
@bingo600 said in Chrony, Network Time Security (NTS, NTPsec) to replace unsecure/old NTP (ntpd):
But my wife has a BIGGER KNIFE than yours
 I don't think so, we've been entertaining each other for 29 years) - has a big, big fucking big knife :)
I don't think so, we've been entertaining each other for 29 years) - has a big, big fucking big knife :)You haven't seen my lady (my darling), she's a real hunter and a real killer... :)
she ...... :) especially attacks DC grade Cisco stuff, hihihihi
1G at home is more than enough, but I'm moving on with this
(basic idea, 10G is coming (in SOHO) and I am already compatible with it, otherwise there is no significant difference at the moment)I'm building my own house soon, I'm going to have a lot of trouble deciding what to build from the ground up.... L1
-
@daddygo said in Chrony, Network Time Security (NTS, NTPsec) to replace unsecure/old NTP (ntpd):
10G is coming (in SOHO) and I am already compatible with it,
Its already here to be honest.. Just need a few more years for the price to come down before more adoption if you ask me..
I have a few more years left on my main switch for support.. But as that nears and look for replacement, I would love a reasonable priced.. Say $200ish replacement for my sg300-28 that had atleast a few multigig ports 10ge, but also support 2.5/5ge. And hey poe would also be nice.. Or something that had sfp+ support where the modules are not all that expensive where I could add multigig..
I have 2.5ge running between my nas and pc, and yeah no way in hell I would ever go back to just gig for that connection.. But it was a bolt on sort of way of getting it with usb dongles.. It works, but much rather have that connection running through the switch vs just san type of connection between pc and nas on different network.
And my internet is only 500/50 - it works and its fine and ok with the price. I don't really see need for gig to internet for my use.. But would really love to see that at 500/500. 1/1 gig would be fantastic.. But current isps in the area have no sort of symmetrical offerings and the bump to 1000 would still only be 50 up, so its pretty pointless for my use.
-
@johnpoz said in Chrony, Network Time Security (NTS, NTPsec) to replace unsecure/old NTP (ntpd):
if you ask me..
yes I think you are a special guy :)
don't worry your opinion really matters, I see the energy you add to the forum, respect (!!!)I love Cisco at home SMB (SG series). and everywhere else, serious and considered philosophy...
+++edit:
I won't forget your SMB3 writeup on the more serious file transfer to Syno
+++edit2:
if I remember correctly is it a Realtek 2.5G USB NIC? -
@daddygo yeah the nic is club3d model, and it realtek chip..
Using this driver
https://github.com/bb-qq/r8152Overall it has been fine - but it has cut out a few times.. Where I had to unplug it and plug it back in..
SMB3 multichannel, yeah that is another option to break the 1g barrier for sure - would go back to that if had to go back to gig that is for sure.. Ran that for a couple years, never any issues with it.. But going to 2.5 did get me overall boost in top end speed..
But yeah multigig or better yet full 10ge is yeah a viable option for the soho, and prices are doable.. Its not like thousands or anything - so it can be done in the home if you want too.. But the price of doing it, is quite a bit more than just gig.. I would of hoped that 2.5/5 would become more mainstream - there are some 2.5 gig switches in the 100$ range out that is making that way more viable and pc makers are starting to include nics that can do 2.5
-
AFAIK this is the cheapest 10Gb decent "Home switch"
MikroTik Cloud Router Switch CRS309-1G-8S+IN
One on offer here , else around $280
https://www.ebay.com/itm/363622236174I have heard several reports about "fs.com" switches being nice, haven't tried them my self.
"Home"
https://www.fs.com/de-en/products/122281.htmlA bit more DC like (40G uplinks)
https://www.fs.com/de-en/products/108710.htmlTheir optics should be quite cheap too.
But not a "score" like DG's Ciscos
/Bingo
-
@bingo600 said in Chrony, Network Time Security (NTS, NTPsec) to replace unsecure/old NTP (ntpd):
I have heard several reports about "fs.com" switches being nice, haven't tried them my self.
do not do this, pls.

I've had a good relationship with FS:COM for a long time, they have super SFP/SFP+ modules, check it out:

but don't buy switches from them(!!!), BROADCOM chips are in many units and they are fast, but for example, if you want to set the current time it's simple, but strange....
by giving them DNS, they are immediately connected to a Chinese server (?)
if you are interested I will show you this tomorrow, I have Wireshark files about this and a switch like this in the next room in my flat

-
@bingo600 said in Chrony, Network Time Security (NTS, NTPsec) to replace unsecure/old NTP (ntpd):
MikroTik Cloud Router Switch CRS309-1G-8S+IN
One on offer here , else around $280
https://www.ebay.com/itm/363622236174Hmmmm,

Don't think that MikroTik is stable, look at this conversation, you wonder who I am???? :-)
(in this conversation)https://forum.mikrotik.com/viewtopic.php?t=167891
CSS610-8G-2S yes that's right it's the same in terms of the fraudulent switch, hhihihi :) - MikroTik Cloud Router Switch CRS309-1G-8S+IN