Internal DNS Not Working
-
@steveits I am not using any IPv6. I have also reset this setting back to only responding to queries from "LAN" and "LocalHost".
-
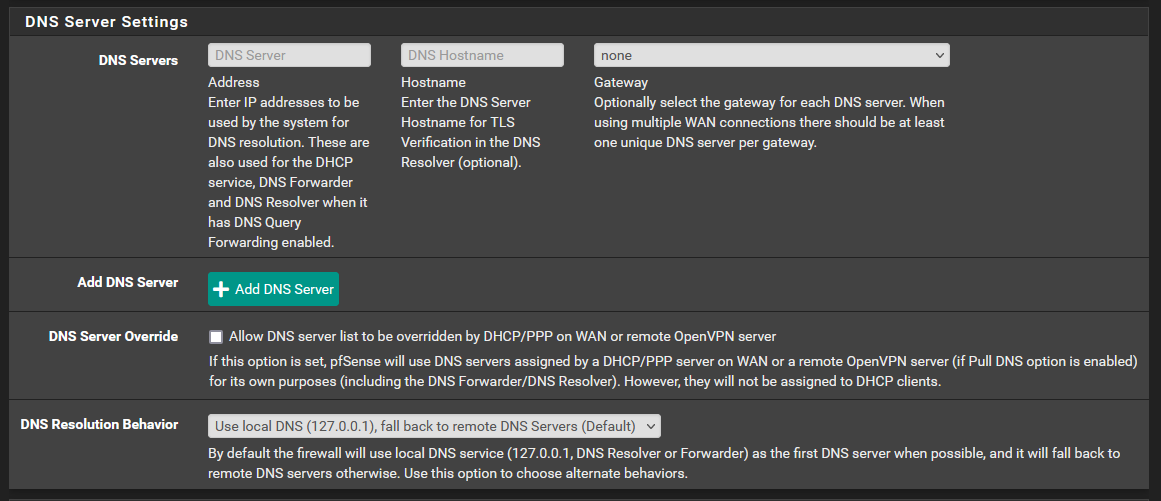
@aiden21c Let's take it in steps:
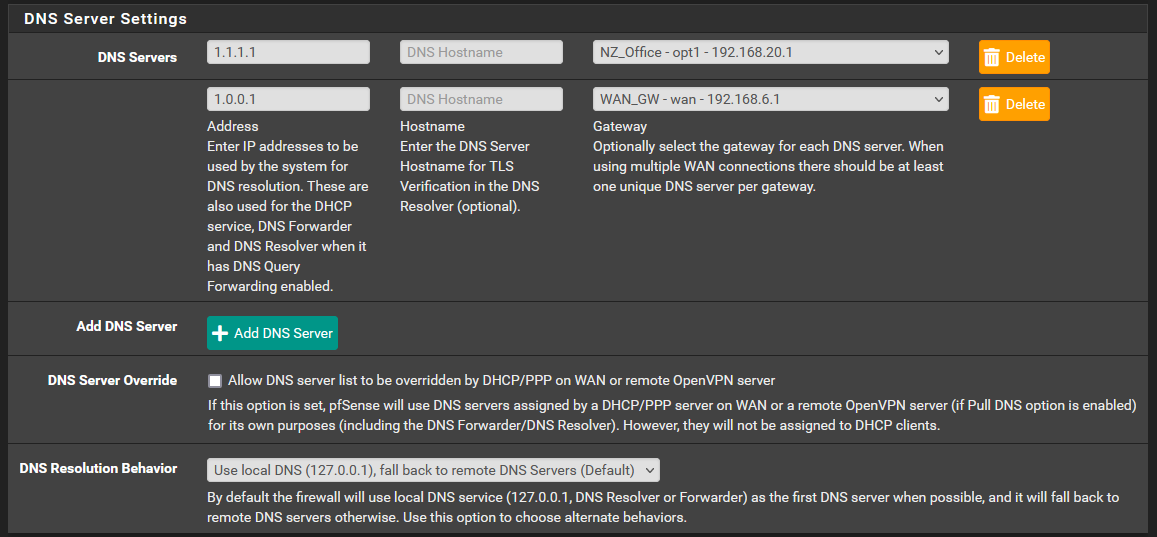
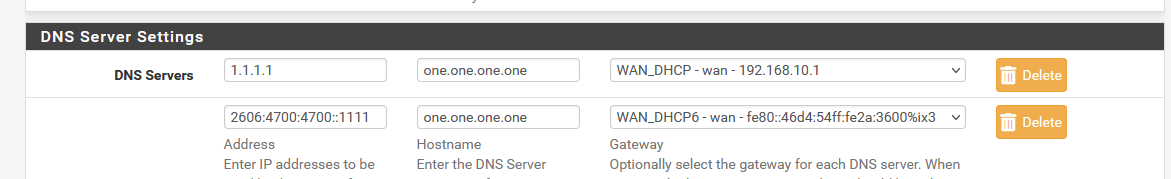
- (If it were me) Remove the extra servers in General Setup (for now)
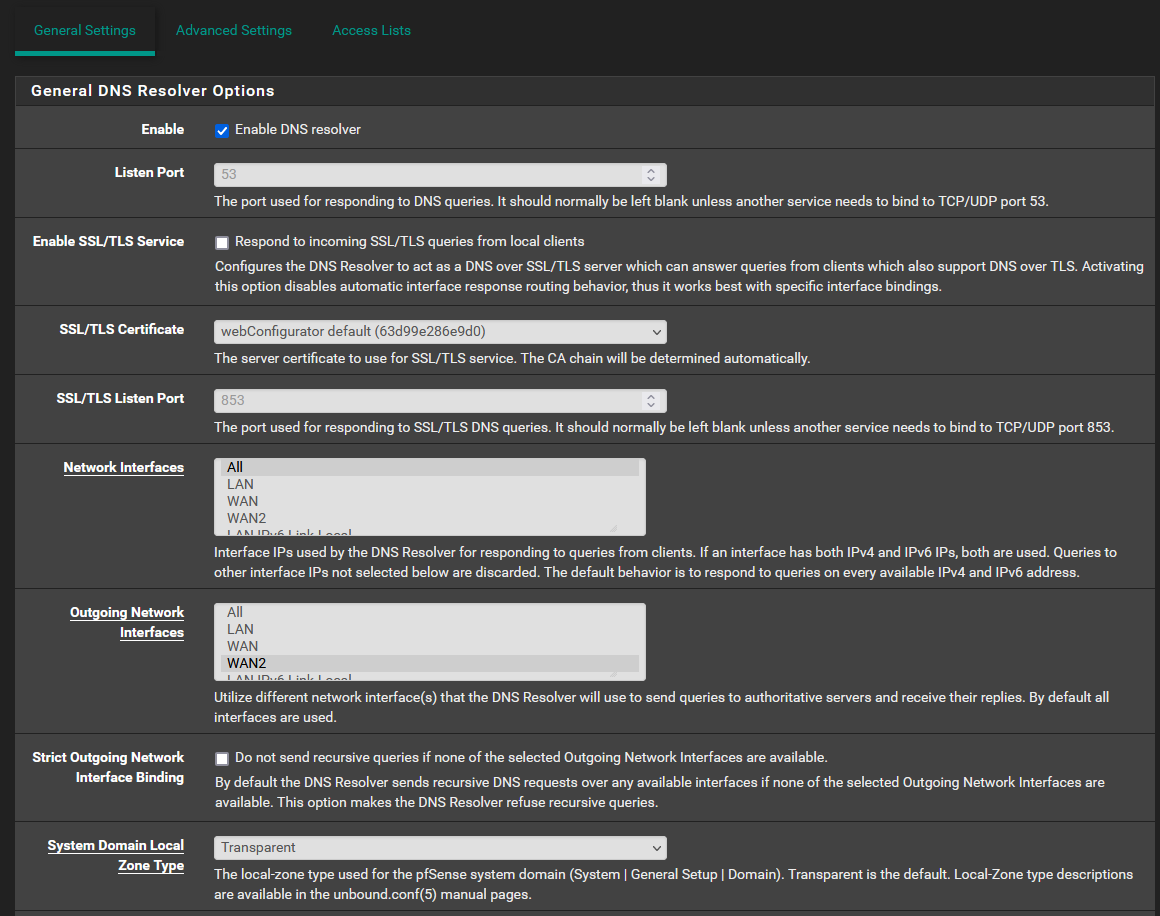
- Set DNS Resolver as:
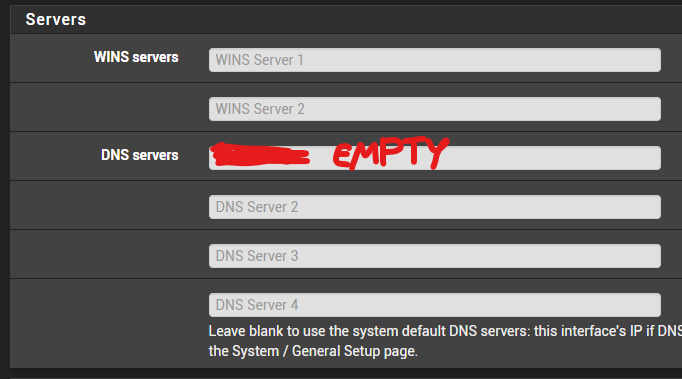
- Set all interfaces with DHCP in DHCP server as:
- Allow LAN to DNS (both TCP and UDP), LAN to DoT (TCP)
- Setup NTP correctly (DoT may have problems if clock is wrong)
- Provide a diagram of your network (along with exactly how you connect to WAN), so I (or others) can direct you what to do (and explain each step so you will be able to change config later by yourself)
-
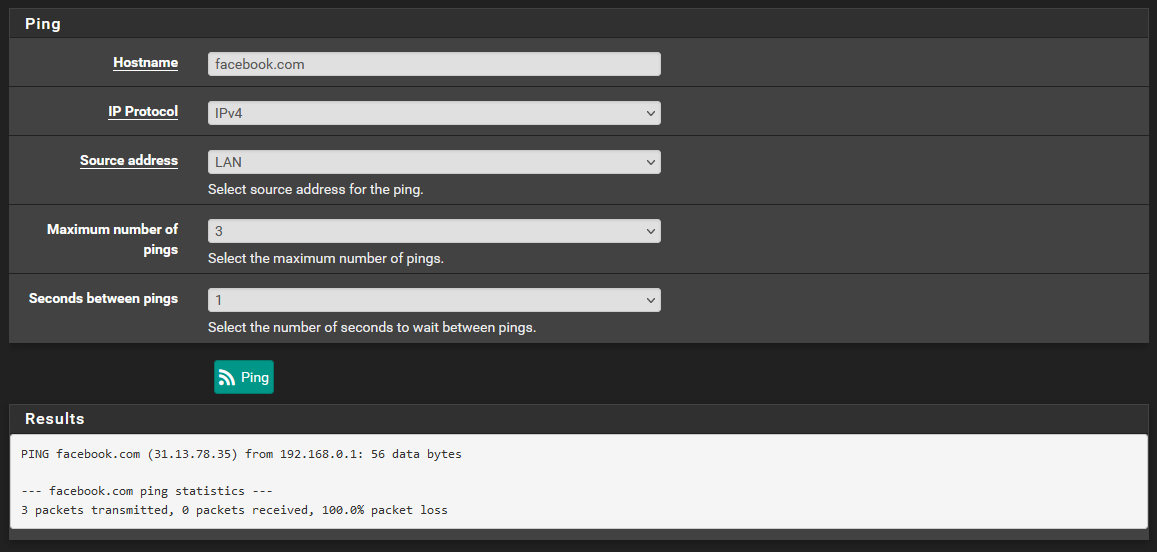
@aiden21c Also, as per dig, all is OK. You just tried pinging from the LAN ip of PfSense, which isn't NATed (meaning, it can't reach the internet, only WAN can).
-
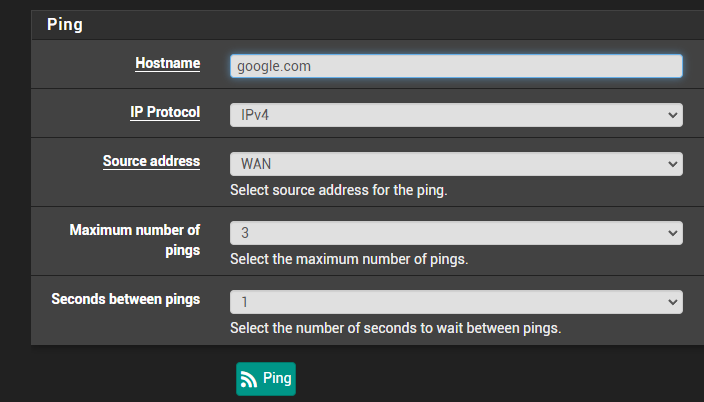
@aiden21c Next try
-
@nightlyshark No good unfortunately. I have done the following:
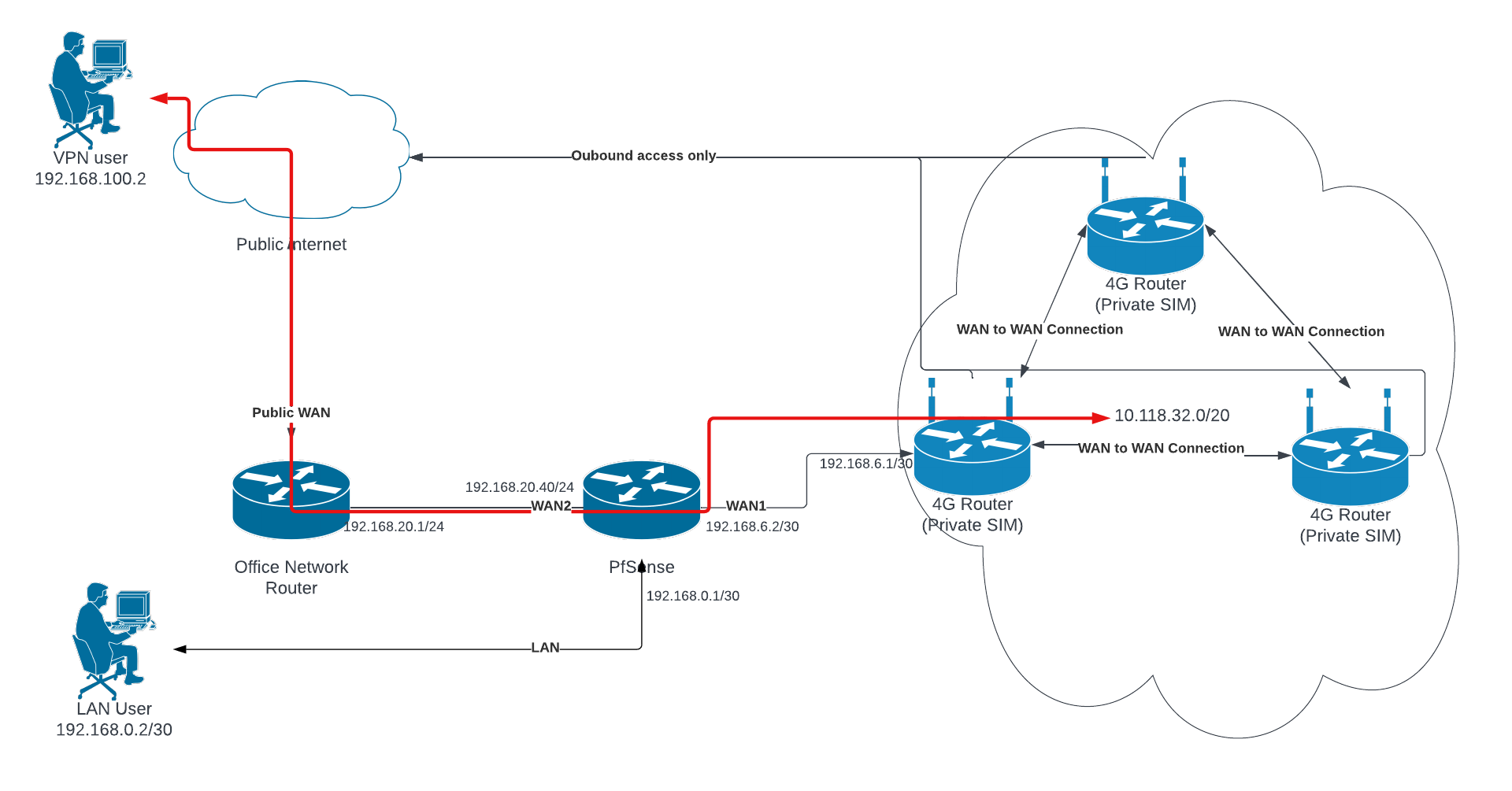
My network setup is a concurrent dual wan setup. This is where I route all traffic out of WAN2 (my main WAN connection) and only traffic directed to the networks specified in the routing rules will be routed through WAN1. I eventually want to have VPN traffic come down through WAN2 and be able to reach the network on WAN1.
-
@aiden21c I have now found another very weird issue. I have reset my settings to give the client device access to the internet, and it seems as though when I reset these settings, the DNS forwarder is working exactly as expected. Btw there is no DHCP on the LAN.
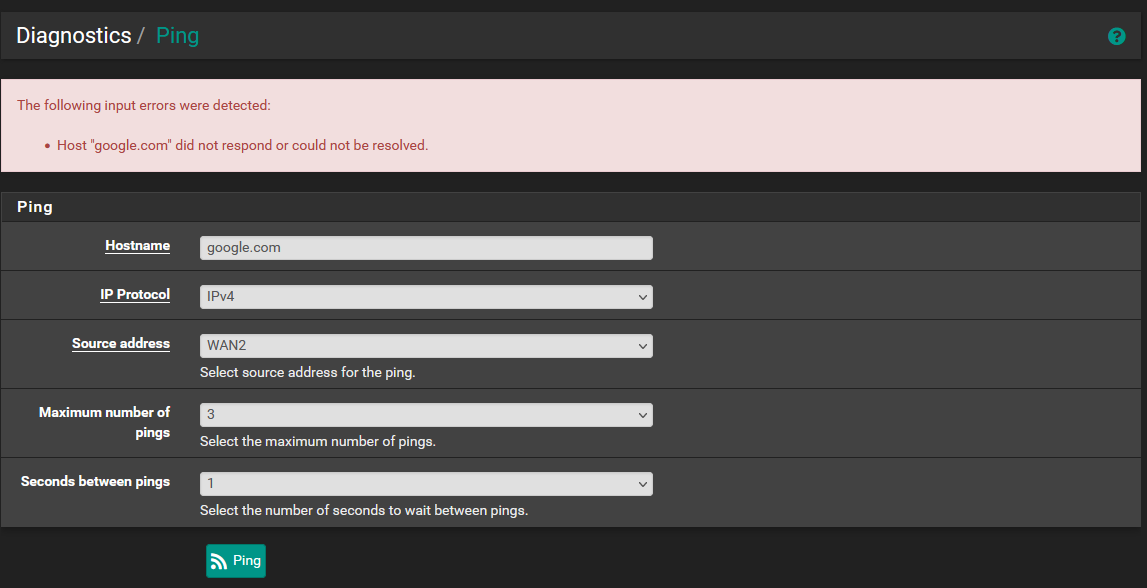
It seems that with my testing, I am actually only able to use the diagnostics to ping only the IP addresses specified within the General setup page. It doesn't matter what IPs I set in here, but so long as they are assigned to a gateway I can ping these from any of the 3 interfaces (2 WAN and 1 LAN). Examples:
General Setup
8.8.8.8 - wan2 gw
8.8.4.4 - wan1 gw
ping success to 8.8.4.4 and 8.8.8.8 from all 3 interfaces
ping failure to 1.1.1.1 and 1.0.0.1 from all 3 interfacesGeneral Setup 2
1.1.1.1 - wan2
1.0.0.1 - wan1
ping success to 1.1.1.1 and 1.0.0.1 from all 3 interfaces
ping failure to 8.8.8.8 and 8.8.4.4 from all 3 interface -
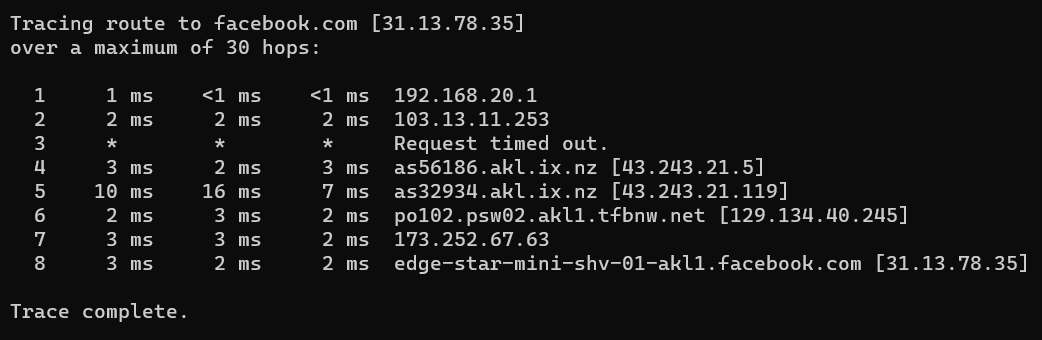
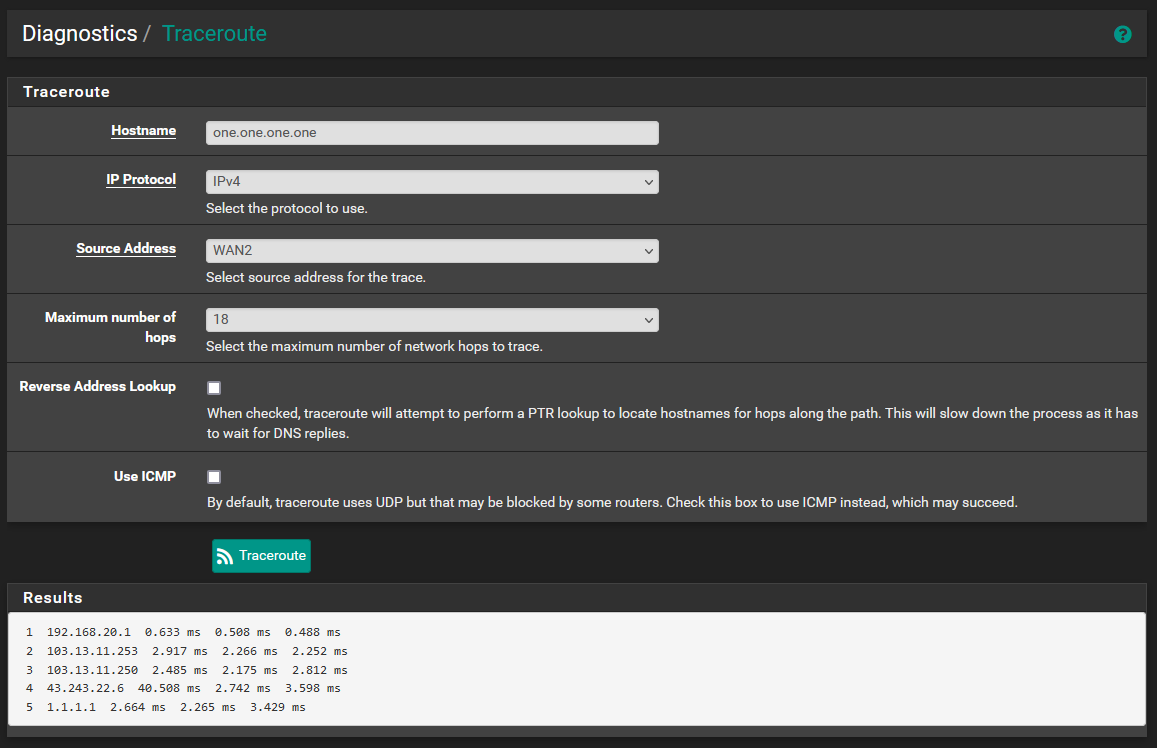
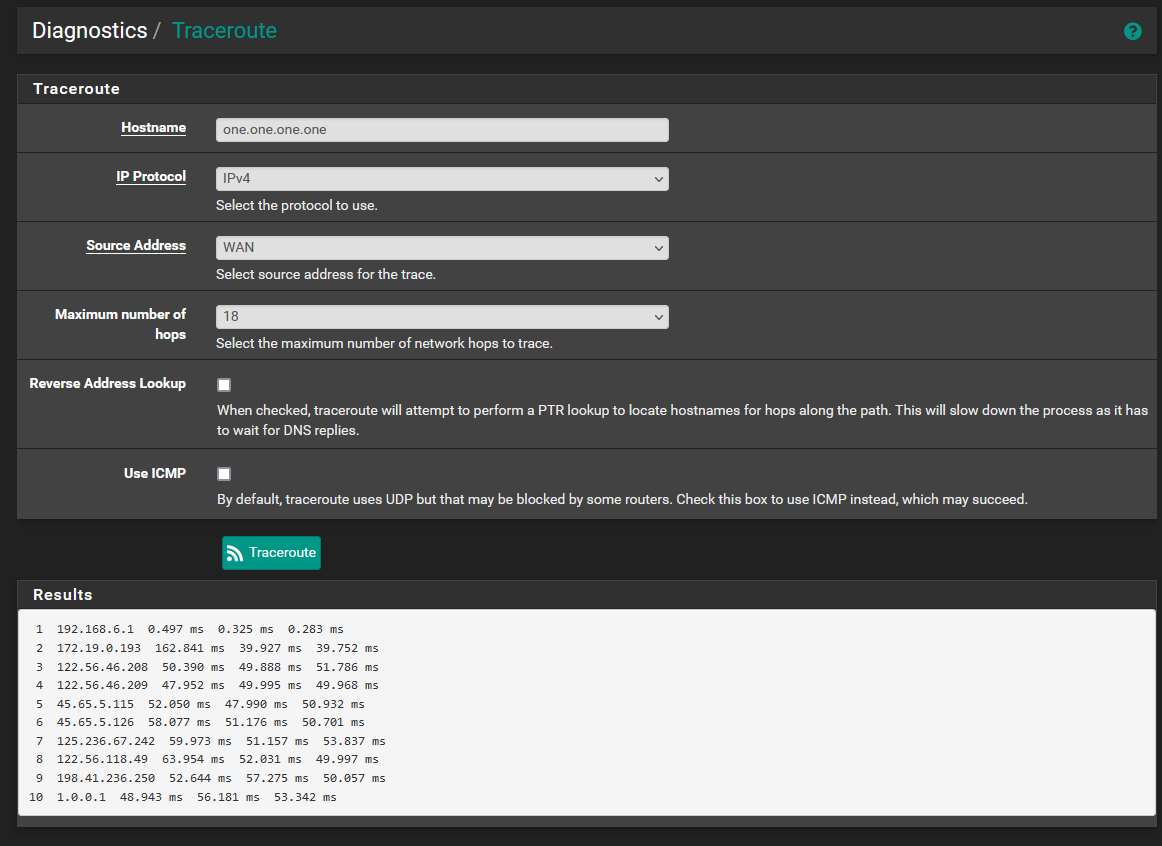
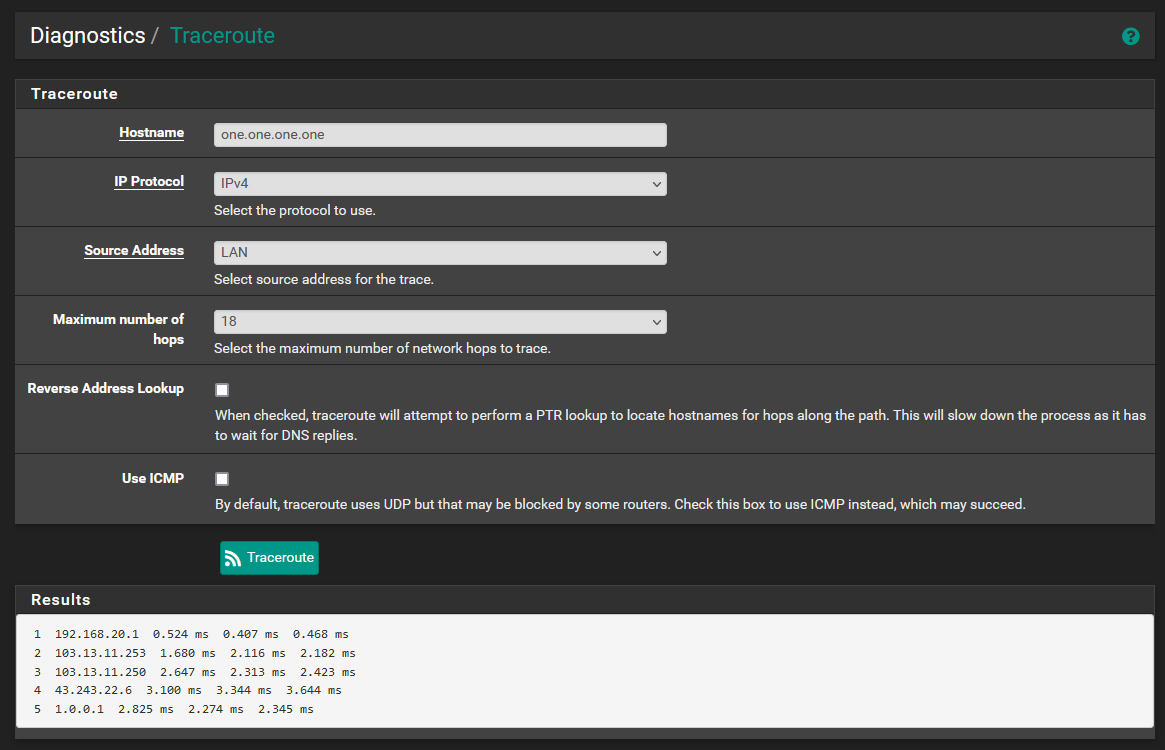
Here are the traceroutes to the hostnames of the DNS servers which are specified in the general setup page. Traceroutes fail if I attempt any other hostnames. In general setup, for this to work I need to set both gateways to use the DNS pair from the same provider, otherwise the opposing WAN and LAN wont be able to reach. Below I used 1.0.0.1 on WAN2 an 1.1.1.1 on WAN1.
When DNS servers from different providers are in General Setup, I can ping both IPs from any interface, but I can not traceroute to both hostnames, only the IPs.
-
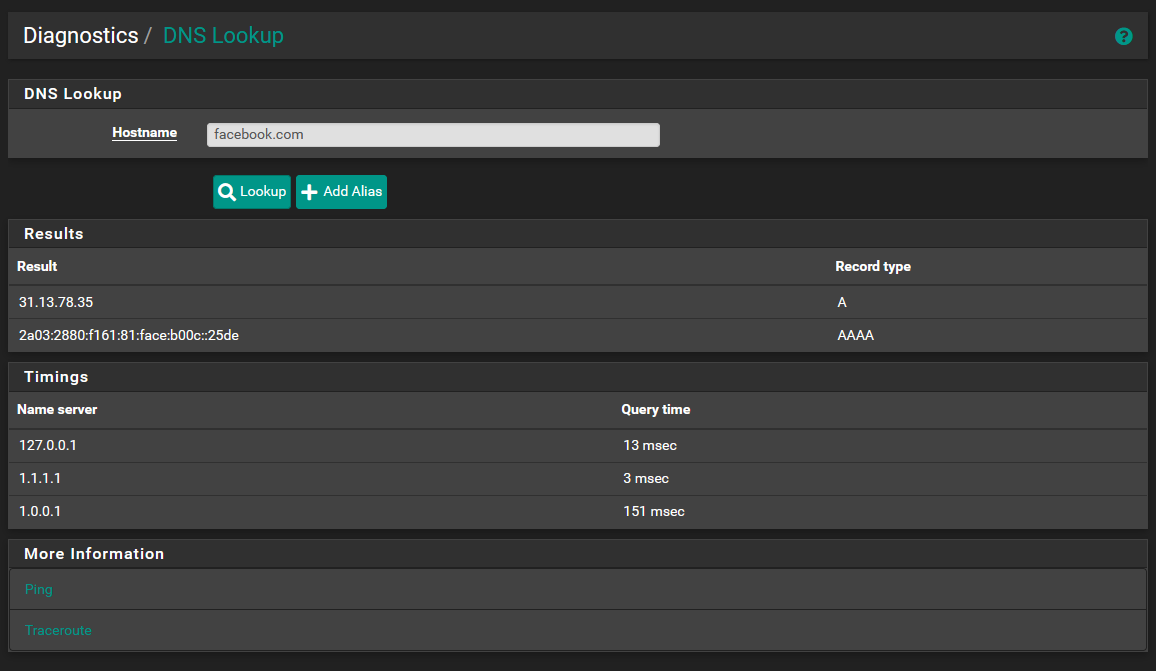
@aiden21c I suggest using the DNS lookup diag page to test DNS problems. While Google DNS should answer pings, testing by ping introduces another layer. One problem at a time . :)
Re pinging DNS servers, I believe pfSense sets up routing entries for them specifically. Ensure you have a default route and/or routing is correct.
-
@steveits as is visible above, DNS lookup was actually working. I was able to lookup facebook.com and have repeatedly been able to lookup google.com and others. I think this is likely a firewall or NAT issue, or something else entirely.
I still can't get my head around why my LAN client is able to use pfSense as it's dns and everything works fine, but the pfsense itself is having DNS (and outgoing Ping) issues, as I'm not actually able to use the ping diag tool to ping any IPs other than those specified. -
My turn.
I left "Resolving mode" for 48 hours.
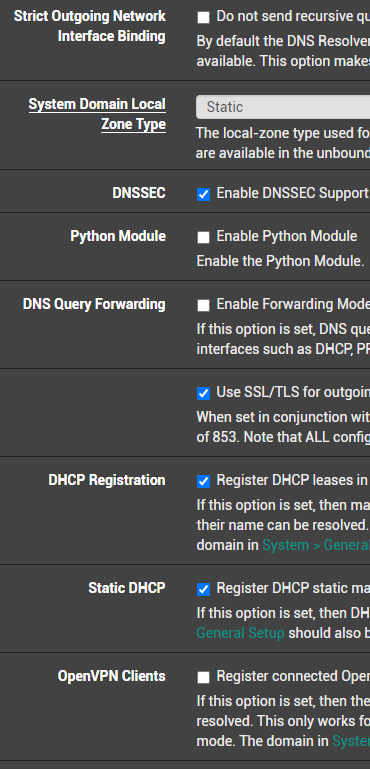
I've tested Forwarding for a while.I chose "1.1.1.1" - so I went to to 1.1.1.1 set up instructions. I even added TLS support.
So : first :
Take note : strictly speaking, I have just one WAN, but IPv4 and IPv6 are separate. Half of all my outgoing traffic is IPv6 these days.
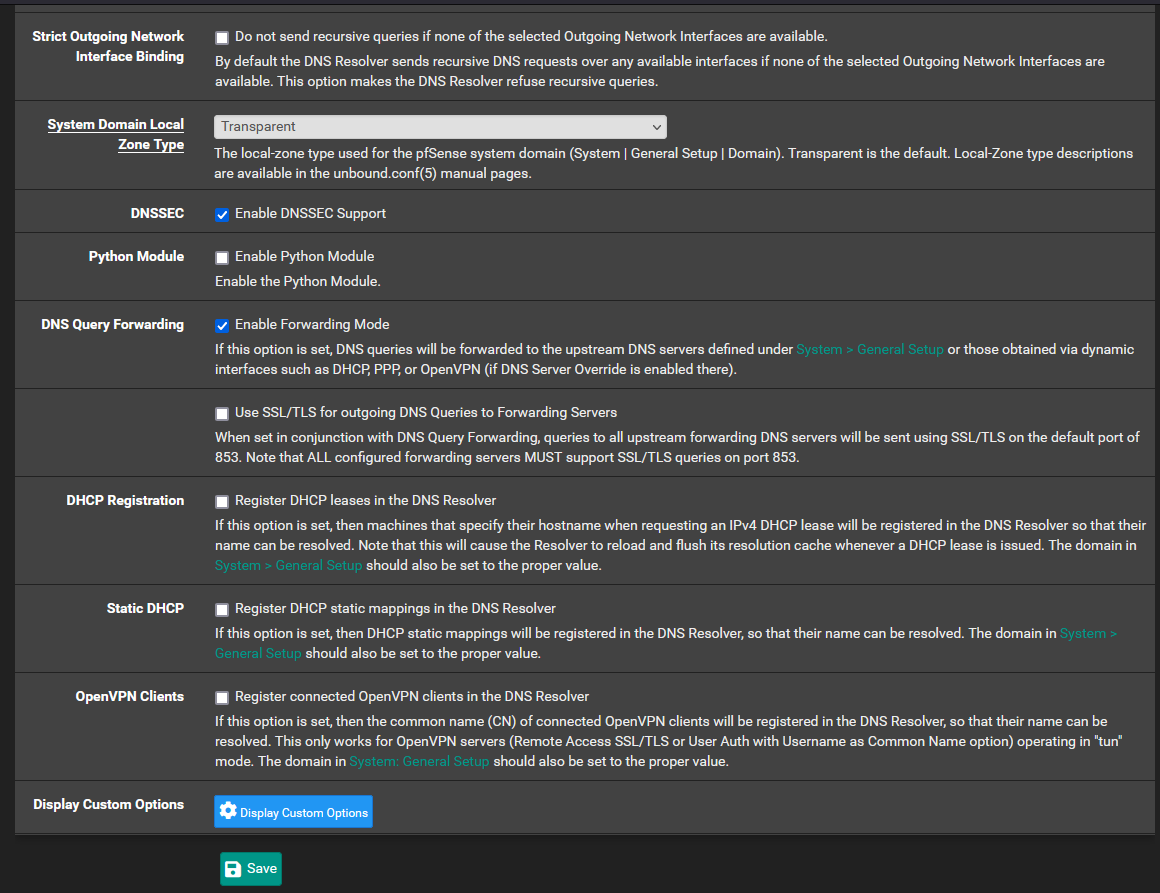
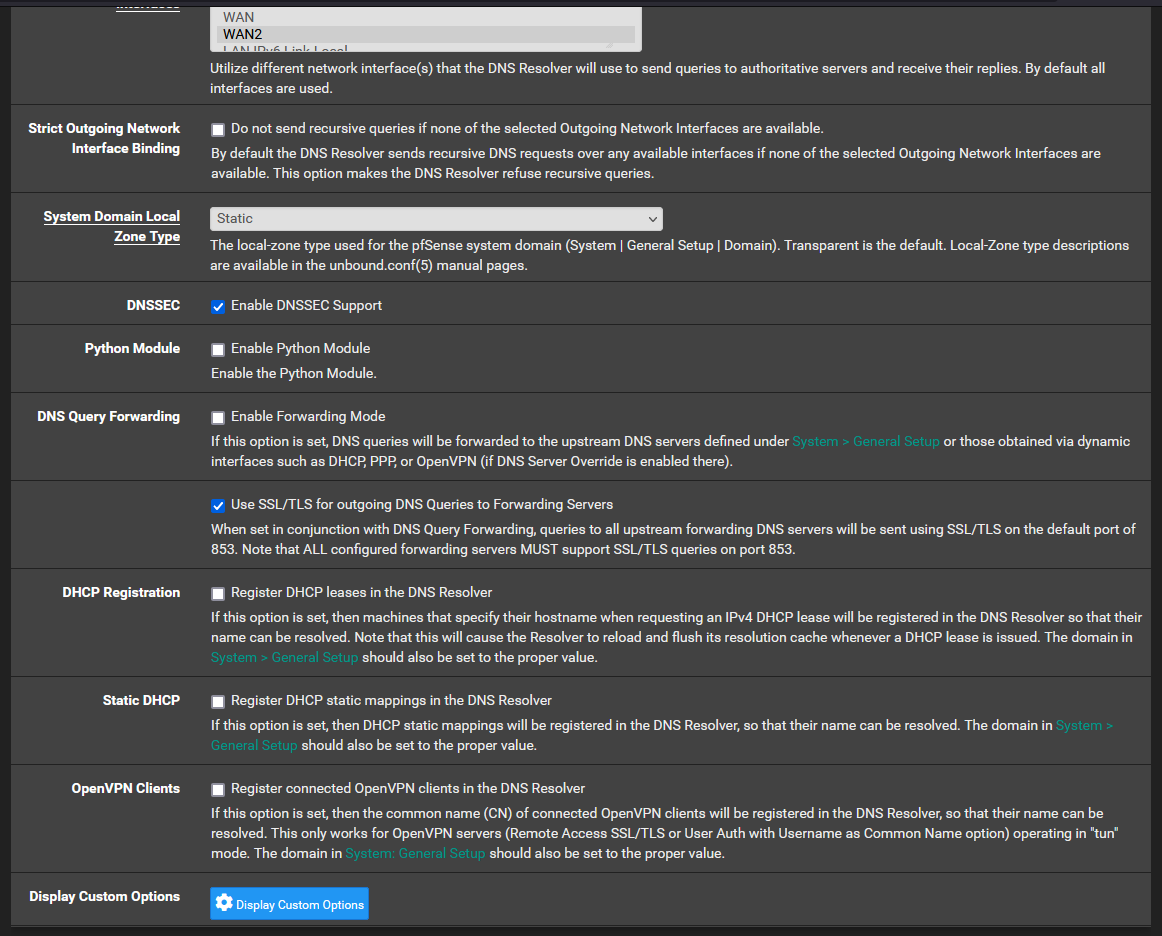
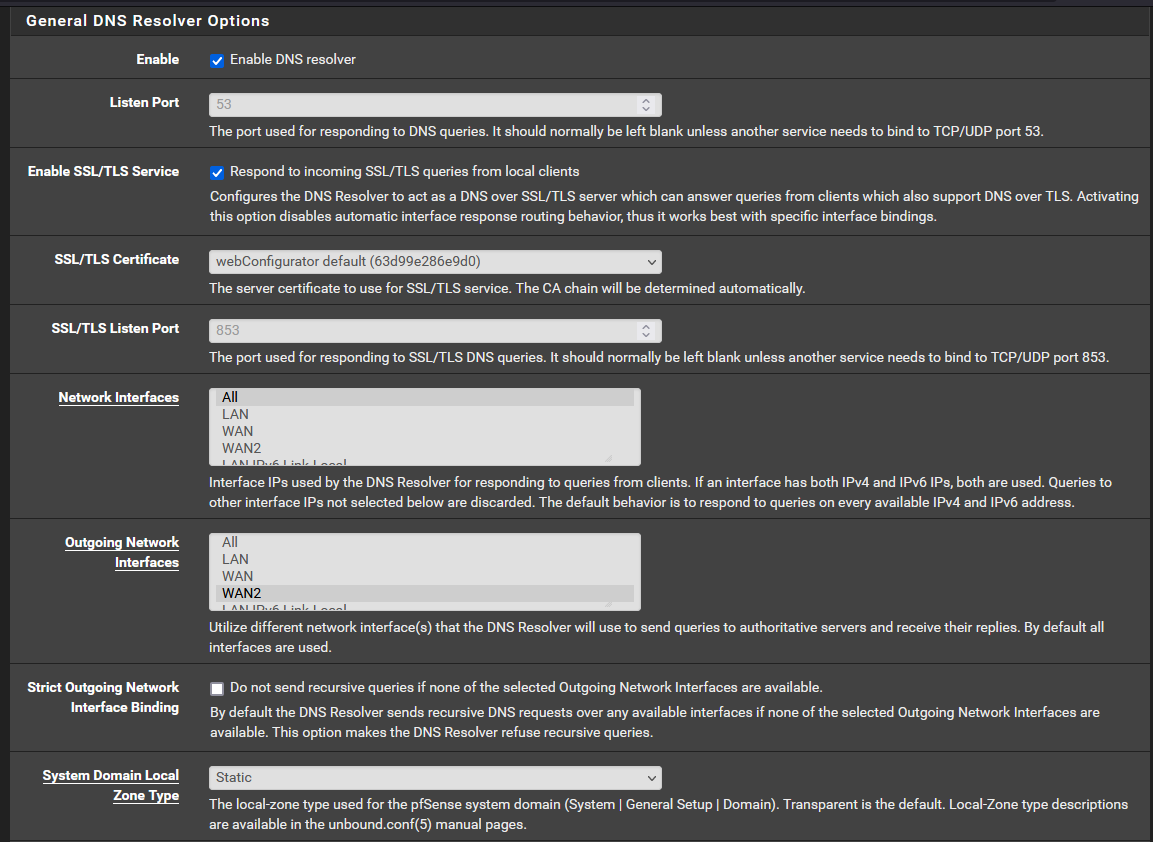
Then : Unbound :
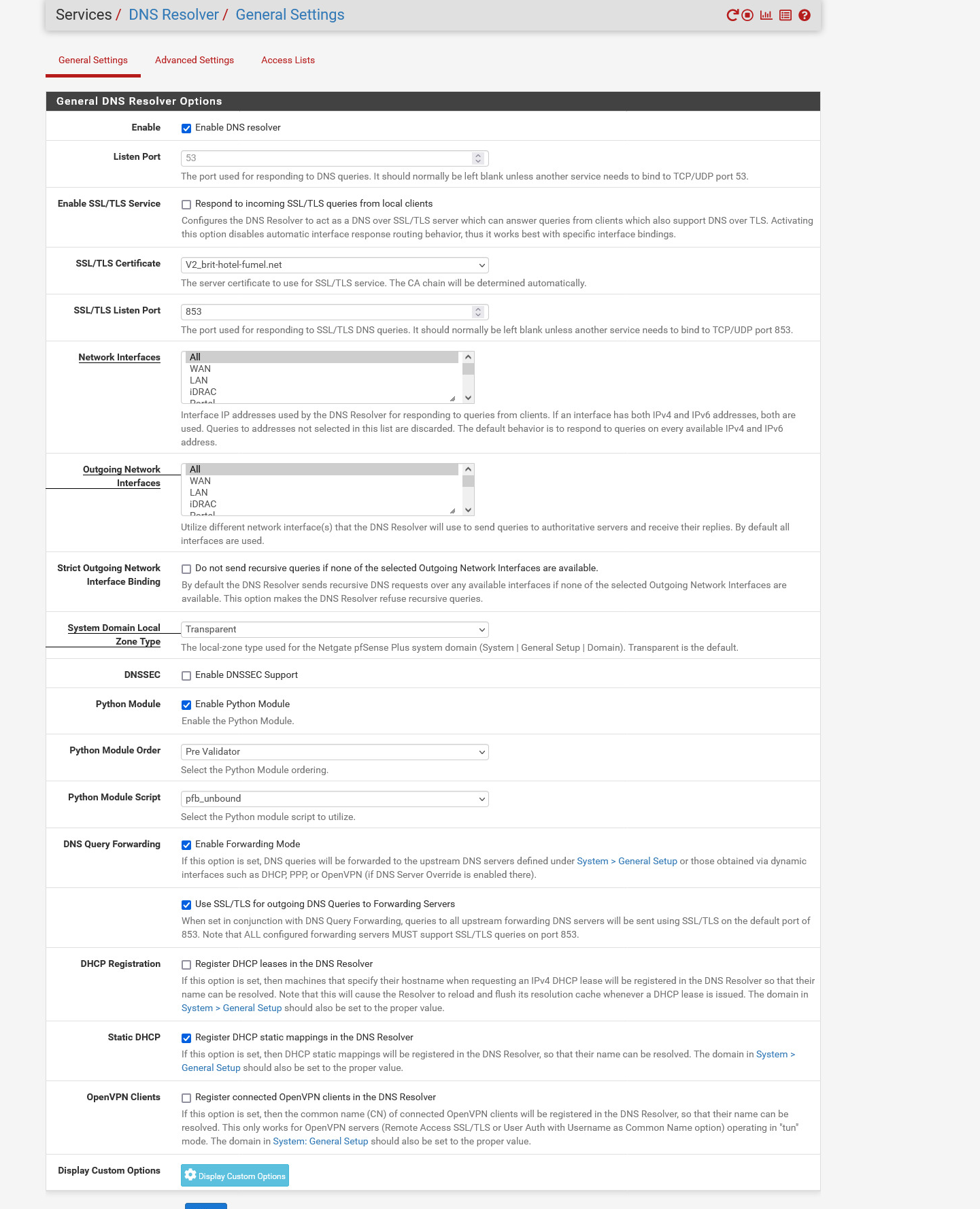
I made no changes to the Unbound Advanced page, neither the ACL page.
I have no floating rules.
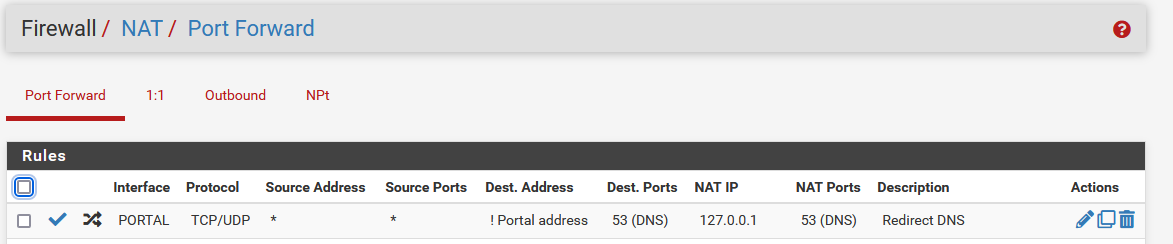
A DNS NAT rule for a specific interface : I force the (captive) PORTAL network to use 127.0.0.1 : that's unbound. I might as will delete this rule, I'm not using it myself.
And that's it.
This morning, I even forgot about the fact I was not resolving anymore.Since the day before, unbound didn't restart.
No DNS interruptions as far as I know.
During breakfast this morning, no captive portal clients were complaining.Btw : I'm using 23.01.
I've done an identical test during one week with 22.05
Same thing with 2.6.0, the CE version.
Using a SG-4100.
I was using VDSL before January, 15, 2023. Since then, fiber. -
@gertjan @aiden21c Please remove all port forwards or firewall rules that redirect or block DNS. If you have such rules activated with recursive mode, you are essentially redirecting Unbound packets back to itself.
@Gertjan Happy it works, anyway. Sorry for the edits, rushed to answer without drinking my coffee, first
 .
. -
@gertjan I must confess I don't have your full network diagram, though. If you get a chance, just to help anyone researching this in the future, make us a mock-up.
-
@aiden21c Show screenshots of your firewall rules (all of them, and remove any public IPv4's), all Port Forwards and your Gateways (System->Routing).
-
@gertjan Perhaps you were missing the accompanying FW rule?
-
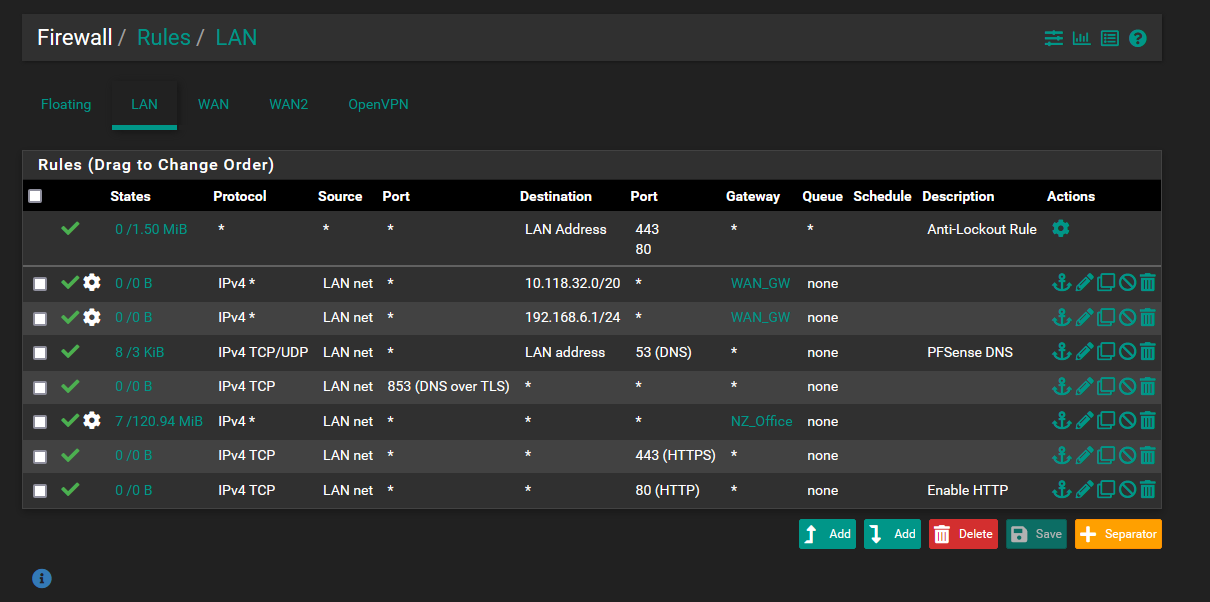
@nightlyshark These are my current firewall rules. I am not nearby the device atm, however I dont understand how removing the IPv4 route rules will help with this. I have no firewall rules on WAN1 and on WAN2 i only have the default rule which is added by the OVPN server. I have tried moving the DNS rule from the bottom to the top of the list to no avail.
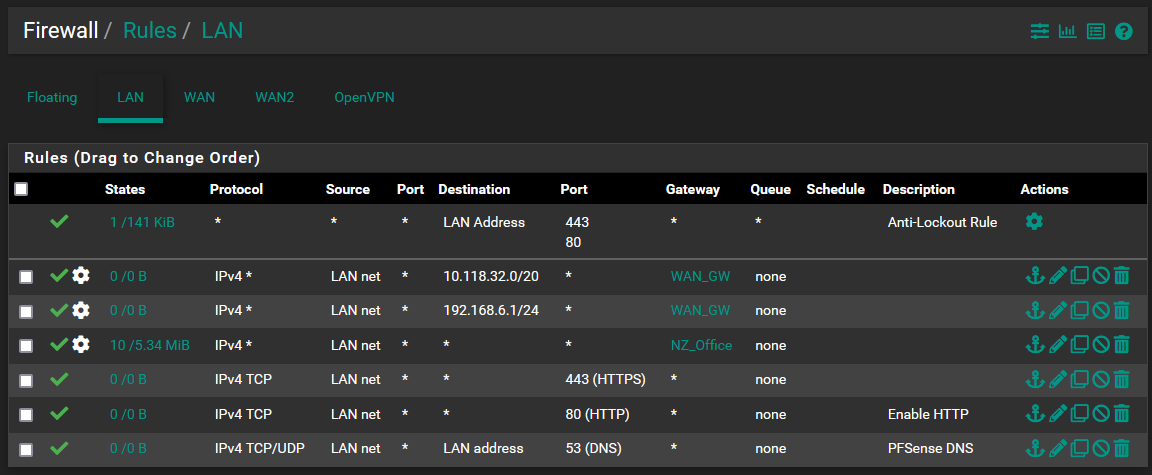
I have no port forwards at this stage. I have a static route to 10.118.32.0/20 via the 192.168.6.0/30 network.
I have tried this configuration with and without any DNS listed in General Setup.
I have 2 gateways with no "Default IPv4" or "Default IPv6" gateway set.
WAN1 - 192.168.6.1/30
WAN2 - 192.168.20.1/24
Let me know if you require any more info. -
@aiden21c The counters for your first 2 rules show no traffic, just pointing it out.
When I asked about the FW rules, I meant (mostly) Floating, WAN and WAN2. -
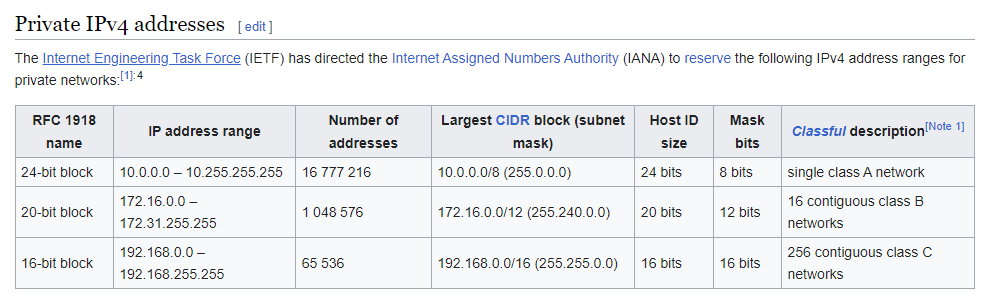
@aiden21c If you have private IPs on WAN and WAN2, that means that PfSense is behind a NAT. Routers should not (generally) connect to each other via the private space or behind NAT.
-
@nightlyshark I don't have any fw rules on either Wan interface, nor any floating rules. I believe this is the issue I'm having where I have a double NAT on each interface. As per my network diagram above I do have routers on both WANs which are acting as a gateway for the pfsense. How would I go about avoiding this issue as I don't really have any other option for my setup.
-
@aiden21c said in Internal DNS Not Working:
I dont understand how removing the IPv4 route rules
Your NZ_Office rule is before the others (including DNS) and covers everything, making those rules unusable. The more general rules (any->any) go after any rules with restrictions (443, 80, 53).
Also, your second rule has a destination of 192.168.6.1/30. Is this correct? Maybe you meant 192.168.6.0/30?
Also, also, you have two routing rules for WAN, but a single gateway. Each WAN that routes somewhere should get a gateway.
Also, also, also you have a routing rule for a private IPv4, 10.118.32.0/20:
Is that the office subnet? I didn't see an interface on PfSense with an address in that subnet. -
@aiden21c Do you mean CPE routers when you say "routers"? If so, you must contact your ISP(s) and get them to activate PPPoE passthrough on their CPEs, in order for you to be able to connect with a public IPv4.