freeradius / eap-tls / Android 13
-
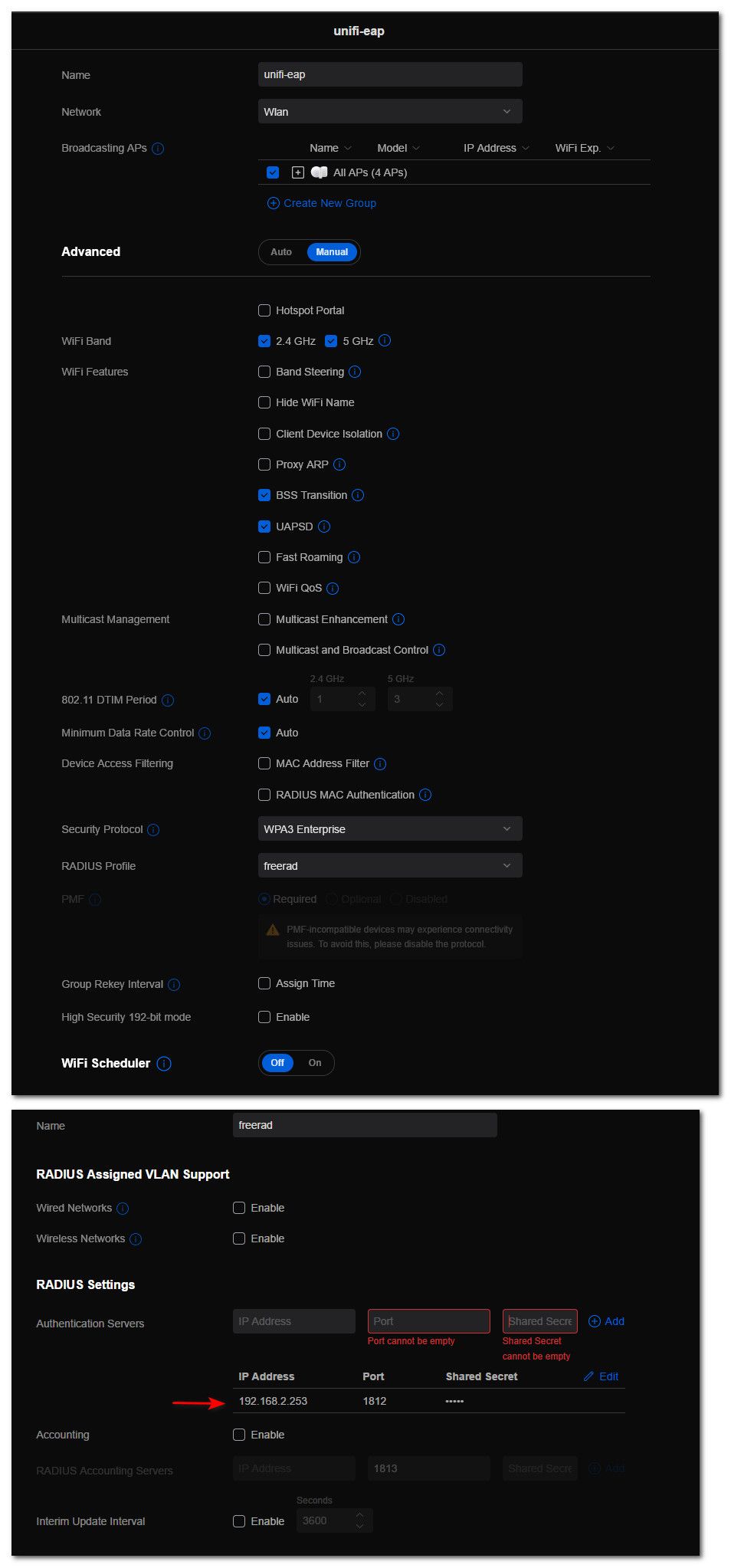
@furom how exactly do you have your unifi setup for wpa3-enterprise? You didn't click on the 192 did you, our APs do not support that.
Your saying it works with wpa2-enteprise? What about wpa3-personal?
you updated your firmware on your AP right? What controller version are you running?
-
@johnpoz said in freeradius / eap-tls / Android 13:
@furom how exactly do you have your unifi setup for wpa3-enterprise?
It is identical to what you have posted, I wanted to make sure no mistakes due to non-working options
You didn't click on the 192 did you, our APs do not support that.
I did at first, but as that didn't work, didn't include that in what I was trying with later on
Your saying it works with wpa2-enteprise?
No, the new tablet does not work with any WPAx-Enterprise.
What about wpa3-personal?
WPA3-Personal connects and works. Hadn't tried that until now, but supposedly better than any of the non-working alternatives... Strange EAP-TLS still refuse though
you updated your firmware on your AP right? What controller version are you running?
Yes, I have upgraded the AP, now running on 6.5.54.14746
-
@furom well if me, what I would do to try and glean some insight to what exactly is failing..
I would do a killall radiusd
then start it in debug mode with
radiusd -X
Then try your auth - you will be flooded with info.. just a small snip of my tablet authing
(4) TLS-Session-Information = "(TLS) recv TLS 1.2 Handshake, CertificateVerify" (4) TLS-Session-Information = "(TLS) recv TLS 1.2 Handshake, Finished" (4) TLS-Session-Information = "(TLS) send TLS 1.2 ChangeCipherSpec" (4) TLS-Session-Information = "(TLS) send TLS 1.2 Handshake, Finished" (4) TLS-Session-Cipher-Suite = "ECDHE-ECDSA-AES128-GCM-SHA256" (4) TLS-Session-Version = "TLS 1.2" (4) Sent Access-Challenge Id 24 from 192.168.2.253:1812 to 192.168.2.4:33751 length 119 (4) EAP-Message = 0x0187003d0d800000003314030300010116030300282a3c2d8e314713ca963244f76526de3b14e6c288b234f0f7c6bd662fda640482f8cbd79a8fc0bf63 (4) Message-Authenticator = 0x00000000000000000000000000000000 (4) State = 0x8f9121a78b162c3e188eee1434fd9653 (4) Finished request Waking up in 4.8 seconds. (5) Received Access-Request Id 25 from 192.168.2.4:33751 to 192.168.2.253:1812 length 251 (5) User-Name = "tablet.home.arpa" (5) NAS-IP-Address = 192.168.2.4 (5) NAS-Identifier = "1618d6c21f6b" (5) Called-Station-Id = "16-18-D6-C2-1F-6B:unifi-eap" (5) NAS-Port-Type = Wireless-802.11 (5) Service-Type = Framed-User (5) Calling-Station-Id = "04-34-F6-AA-02-D9" (5) Connect-Info = "CONNECT 0Mbps 802.11b" (5) Acct-Session-Id = "CF1EEF7980492BF6" (5) Acct-Multi-Session-Id = "80BA7EF3E58094C1" (5) WLAN-Pairwise-Cipher = 1027076 (5) WLAN-Group-Cipher = 1027076 (5) WLAN-AKM-Suite = 1027077 (5) WLAN-Group-Mgmt-Cipher = 1027078 (5) Framed-MTU = 1400 (5) EAP-Message = 0x028700060d00 (5) State = 0x8f9121a78b162c3e188eee1434fd9653 (5) Message-Authenticator = 0xe0ac3128b8fedaa1ac89444320ac40c9 (5) Restoring &session-state (5) &session-state:Framed-MTU = 994 (5) &session-state:TLS-Session-Information = "(TLS) recv TLS 1.3 Handshake, ClientHello" (5) &session-state:TLS-Session-Information = "(TLS) send TLS 1.2 Handshake, ServerHello" (5) &session-state:TLS-Session-Information = "(TLS) send TLS 1.2 Handshake, Certificate"You may need to reboot your AP if your not seeing any info - seems the AP caches some of the info or something..
-
@johnpoz said in freeradius / eap-tls / Android 13:
@furom well if me, what I would do to try and glean some insight to what exactly is failing..
I would do a killall radiusd
then start it in debug mode with
radiusd -X
Then try your auth - you will be flooded with info.. just a small snip of my tablet authing
You may need to reboot your AP if your not seeing any info - seems the AP caches some of the info or something..
This sounds like fun! :) I'll give it a go. I just tried EAP-PEAP and TTLS, neither worked so this will perhaps reveal something interesting... I have read that later Android handled CA's differently and won't trust anything easily, which probably is a good thing for the most part...
Edit: Omg... Well, you weren't kidding about barfing a lot of data... Saw several errors swoshing by, will look for them now
-
@furom It looks like this should contain the interesting error
(4) ERROR: Failed retrieving values required to evaluate condition (4) [expiration] = noop (4) [logintime] = noop (4) pap: WARNING: Auth-Type already set. Not setting to PAP (4) [pap] = noop (4) } # authorize = updated (4) Found Auth-Type = eap (4) # Executing group from file /usr/local/etc/raddb/sites-enabled/default (4) authenticate { (4) eap: Expiring EAP session with state 0x4c94f6214f91fbc3 (4) eap: Finished EAP session with state 0x4c94f6214f91fbc3 (4) eap: Previous EAP request found for state 0x4c94f6214f91fbc3, released from the list (4) eap: Peer sent packet with method EAP TLS (13) (4) eap: Calling submodule eap_tls to process data (4) eap_tls: (TLS) EAP Done initial handshake (4) eap_tls: (TLS) recv TLS 1.2 Alert, fatal internal_error (4) eap_tls: ERROR: (TLS) Alert read:fatal:internal error (4) eap_tls: (TLS) Server : Need to read more data: error (4) eap_tls: ERROR: (TLS) Failed reading from OpenSSL: error:14094438:SSL routines:ssl3_read_bytes:tlsv1 alert internal error (4) eap_tls: (TLS) In Handshake Phase (4) eap_tls: (TLS) Application data. (4) eap_tls: ERROR: (TLS) Cannot continue, as the peer is misbehaving. (4) eap_tls: ERROR: [eaptls process] = fail (4) eap: ERROR: Failed continuing EAP TLS (13) session. EAP sub-module failed (4) eap: Sending EAP Failure (code 4) ID 5 length 4 (4) eap: Failed in EAP select (4) [eap] = invalid (4) } # authenticate = invalid (4) Failed to authenticate the user (4) Using Post-Auth-Type Reject (4) # Executing group from file /usr/local/etc/raddb/sites-enabled/default (4) Post-Auth-Type REJECT { (4) attr_filter.access_reject: EXPAND %{User-Name}The top 4 rows repeat a few times without the other errors. Interestingly, it says that it needs to 'read more data', and the first error reads like this
(1) ERROR: Failed retrieving values required to evaluate condition (1) [expiration] = noop (1) [logintime] = noop (1) pap: WARNING: Auth-Type already set. Not setting to PAP (1) [pap] = noop (1) } # authorize = updated (1) Found Auth-Type = eap (1) # Executing group from file /usr/local/etc/raddb/sites-enabled/default (1) authenticate { (1) eap: Expiring EAP session with state 0x4c94f6214c96fbc3 (1) eap: Finished EAP session with state 0x4c94f6214c96fbc3 (1) eap: Previous EAP request found for state 0x4c94f6214c96fbc3, released from the list (1) eap: Peer sent packet with method EAP TLS (13) (1) eap: Calling submodule eap_tls to process data (1) eap_tls: (TLS) EAP Got final fragment (131 bytes) (1) eap_tls: WARNING: (TLS) EAP Total received record fragments (131 bytes), does not equal expected expected data length (0 bytes)So something is going on here...
-
@furom said in freeradius / eap-tls / Android 13:
(4) eap_tls: (TLS) EAP Done initial handshake
(4) eap_tls: (TLS) recv TLS 1.2 Alert, fatal internal_error
(4) eap_tls: ERROR: (TLS) Alert read:fatal:internal error
(4) eap_tls: (TLS) Server : Need to read more data: error
(4) eap_tls: ERROR: (TLS) Failed reading from OpenSSL: error:14094438:SSL routines:ssl3_read_bytes:tlsv1 alert internal error
(4) eap_tls: (TLS) In Handshake Phase
(4) eap_tls: (TLS) Application data.
(4) eap_tls: ERROR: (TLS) Cannot continue, as the peer is misbehaving.Well that for sure would explain why your eap-tls is not working... But your saying you got your old tablet working.. Are you not using the same certs that you used for server and same CA?
So something wrong with the client cert, or how the client is sending it? Or just how the client does the handshake?
edit: My son has a android phone - not sure when he will be over next... We might be doing some sort of bbq on monday, so if so I will try to get his phone connected, not sure what its running.. But I do know it is an android device.
-
@johnpoz said in freeradius / eap-tls / Android 13:
@furom said in freeradius / eap-tls / Android 13:
(4) eap_tls: (TLS) EAP Done initial handshake
(4) eap_tls: (TLS) recv TLS 1.2 Alert, fatal internal_error
(4) eap_tls: ERROR: (TLS) Alert read:fatal:internal error
(4) eap_tls: (TLS) Server : Need to read more data: error
(4) eap_tls: ERROR: (TLS) Failed reading from OpenSSL: error:14094438:SSL routines:ssl3_read_bytes:tlsv1 alert internal error
(4) eap_tls: (TLS) In Handshake Phase
(4) eap_tls: (TLS) Application data.
(4) eap_tls: ERROR: (TLS) Cannot continue, as the peer is misbehaving.Well that for sure would explain why your eap-tls is not working... But your saying you got your old tablet working.. Are you not using the same certs that you used for server and same CA?
So something wrong with the client cert, or how the client is sending it?
Glad to hear it makes some sense at least. Not looking great, so much I do understand... :)
No, I created a second cert for the new tablet as I may want them both still...
I now copied the cert I used on the old tablet (working with WPA2-Enterprise/eap-tls/Android 7) to the new one, and errors are identical
-
@furom Perhaps a fragmentation problem ?
Try to edit eap.conf and set fragment_size = 1344A nanoHD and a unifi6-lite only worked with wpa2-enterprise after doing this change.
-
@furom I looked up if they plan on updating my P11 plus to 13, and doesn't look like it - they list 12 as last, and actually eol security updates 11/23, so that not good.. But the little * says
Lenovo tablets get updates for security issues documented in Android Security bulletin.
Its only my train tablet so not too worried about it, but would be nice if could update to 13 and test..
So this tablet doesn't even work with wpa2 enterprise? I would prob just go with wpa3 personal and call it a day then.. wpa3 personal brings "Simultaneous Authentication of Equals (SAE)." so that is good for any sort of offline attack on the password.
-
@mcury said in freeradius / eap-tls / Android 13:
eap.conf and set fragment_size = 1344
Mine is set to
fragment_size = 1024Not having any issues.. I do not have a U6-lite, and furom has a uap-ac-lite, which I also have.. I am not seeing any issues with connecting on any of my ap, the lite, the pro or the lr - all just uap-ac, no U6...
I do have a flex HD I could test with, but its currently inactive..
-
@johnpoz said in freeradius / eap-tls / Android 13:
Not having any issues.. I do not have a U6-lite, and furom has a uap-ac-lite, which I also have.. I am not seeing any issues with connecting on any of my ap, the lite, the pro or the lr - all just uap-ac, no U6...
I do have a flex HD I could test with, but its currently inactive..I did have issues with the default values..
At that time, I decided to perform a packet capture and noticed a lot of EAP packets, when it shouldn't have that amount.
After some research, found that changing that value to 1344 fixed all the issues.
https://lists.freeradius.org/pipermail/freeradius-users/2012-January/058297.html
-
@mcury said in freeradius / eap-tls / Android 13:
@furom Perhaps a fragmentation problem ?
Try to edit eap.conf and set fragment_size = 1344A nanoHD and a unifi6-lite only worked with wpa2-enterprise after doing this change.
It would be interesting to test... Where do I find "eap" in freeRadius on pfSense?
-
-
@johnpoz said in freeradius / eap-tls / Android 13:
@furom the eap file would be here
/usr/local/etc/raddb/mods-enabled
@mcury the way I read what you linked seems too says to lower it ;) hehe
"The simplest thing to try is to see eap.conf, and change fragment_size
to something smaller."Well, I set it through the gui and restarted in debug mode. Now verified the value in the file file indeed reads "1344", but same error unfortunately.
It was a good try, thanks for that
-
@johnpoz said in freeradius / eap-tls / Android 13:
@mcury the way I read what you linked seems too says to lower it ;) hehe
"The simplest thing to try is to see eap.conf, and change fragment_size
to something smaller.Indeed, but that pointed me to the right direction, from there I decided to perform a packet capture.
Once I set it to 1344, it worked, no more fragmentation.I suppose it was here that I got the suggestion for this value from:
https://community.ui.com/questions/Issue-with-WPA2-Enterprise-Across-sites/7070e262-c2c6-403b-a61d-a98ad3b3db53 -
@mcury that seems to be talking about
"Framed-MTU and set it to 1344 and issue was resolved."
That is different than the fragment size.. Pretty sure that framed -mtu is calculated, I see different values when in debug mode
(3) Framed-MTU = 1400
Different one
(5) User-Name = "tablet.home.arpa"
(5) Framed-MTU += 994Could you post your full output when you run in debug mode @furom attach as a .txt file.
-
Could this be of relevance?
No EAP Start, assuming it's an on-going EAP conversationJust prior to that it tries to match an email (containing a "@") and fails. So perhaps a username must be an email? Worth a try I suppose
-
@furom said in freeradius / eap-tls / Android 13:
So perhaps a username must be an email? Worth a try I suppose
I see the same notices.. And not having any issue..
(4) # Executing section authorize from file /usr/local/etc/raddb/sites-enabled/default (4) authorize { (4) [preprocess] = ok (4) [chap] = noop (4) [mschap] = noop (4) [digest] = noop (4) suffix: Checking for suffix after "@" (4) suffix: No '@' in User-Name = "tablet.home.arpa", skipping NULL due to config. (4) [suffix] = noop (4) ntdomain: Checking for prefix before "\" (4) ntdomain: No '\' in User-Name = "tablet.home.arpa", skipping NULL due to config. (4) [ntdomain] = noop (4) eap: Peer sent EAP Response (code 2) ID 192 length 82 (4) eap: No EAP Start, assuming it's an on-going EAP conversation (4) [eap] = updated (4) files: users: Matched entry tablet.home.arpa at line 17 (4) [files] = ok -
@johnpoz said in freeradius / eap-tls / Android 13:
(3) Framed-MTU = 1400
This value is set in eap.conf, inside: tls-config tls-common {
# fragment_size = 1024
fragment_size = 1344 -
@mcury Your 2nd link talked about editing the framed-mtu, not the fragment size.. But I believe the framed mtu is normally calculated I thought, I sure don't have a framed-mtu in my eap file, and its seems to be calculating the different framed mtu size based on what size its seeing.
I don't really think its related to that - but something with his android version, seems their are a lot of discussion about android 11 or above and wpa enterprise.. What I have seen seems to be should have a problem in 12 as well. But I think some of these things are handled by the maker changes to their release for their devices.
I am using a lenovo with 12, and @furom is using a samsung with 13.. etc..
What versions of android are you using @mcury and your using eap-tls?
