VPN point to point
-
You can upload files for me here: https://nc.netgate.com/nextcloud/index.php/s/ai7Km5LsYWZRQMf
-
@stephenw10
I already uploaded the file -
Hmm, nothing instantly jumps out but something that can cause a connection to succeed once then fail is an encryption mismatch at phase2. If it matches phase1 it will initially use that for phase2 in an IKEv2 connection but then fail at rekey. Check that.
It could also be something con figured with more allowed at one end. So pfSense will allow connections that configured with one of the enabled algorithms but the other end might only have one.
If you can copy/paste the complete logs from when it's failing it's much easier to review than a video.
-
@stephenw10 said in VPN point to point:
If you can copy/paste the complete logs from when it's failing it's much easier to review than a video.
-
When does it fail, after how long? When it first rekeys?
-
@stephenw10 said in VPN point to point:
When does it fail, after how long? When it first rekeys?
I pick it up at 7 am and at 14 pm it falls off and I pick it up again manually. If you think I can give you access to see the team as a whole, my English is not very good
-
Mmm, it looks like the re-auth time is ~7h so that lines up; it fails at re-auth.
Really I would want to see the full log from both sides covering the time where it tries to re-auth and fails.
I would also compare the VPN config from both sides carefully. It looks like one side allows connections the other side would refuse.
The error shown is a key mismatch:
https://docs.netgate.com/pfsense/en/latest/troubleshooting/ipsec-logs.html#phase-1-pre-shared-key-mismatch
But since it can connect when pfSense establishes the tunnel that appears to be correct. Unless somehow Cisco has multiple keys.Steve
-
@stephenw10 said in VPN point to point:
But since it can connect when pfSense establishes the tunnel that appears to be correct. Unless somehow Cisco has multiple keys.
This started after the update of pfsense to 2.7 before the configurations were in des and md5, what generates noise is that the other point works correctly the problem is only this point
-
Ah OK. So you had to update the ciphers at both ends and then this started?
-
@stephenw10 said in VPN point to point:
Ah OK. So you had to update the ciphers at both ends and then this started?
That's right, modify both points, and only one has this behavior the other works perfect
-
How do you mean 'both points'?
Two tunnels?
The other tunnel that's configured in pfSense? What's at the other end of that?
-
This post is deleted! -
@rmainero
router cisco 881 both pointsWhat I see is that the problem point rises in port 4500 nat-t and the other in port 500 but both are in automatic
-
It's more that when one side moves from port 500 to port 4500 for the key exchange the other side rejects it. You can see in the logs that happens both ways.
-
Both Cisco end points are behind NAT?
-
@stephenw10 said in VPN point to point:
Both Cisco end points are behind NAT?
Yes, both computers configured the same, with different key and subnet
-
Something is different. Same firmware version on the Cisco endpoints?
-
@stephenw10 said in VPN point to point:
Something is different. Same firmware version on the Cisco endpoints?
No, the firmware is different, I'm going to try putting the same
-
@rmainero
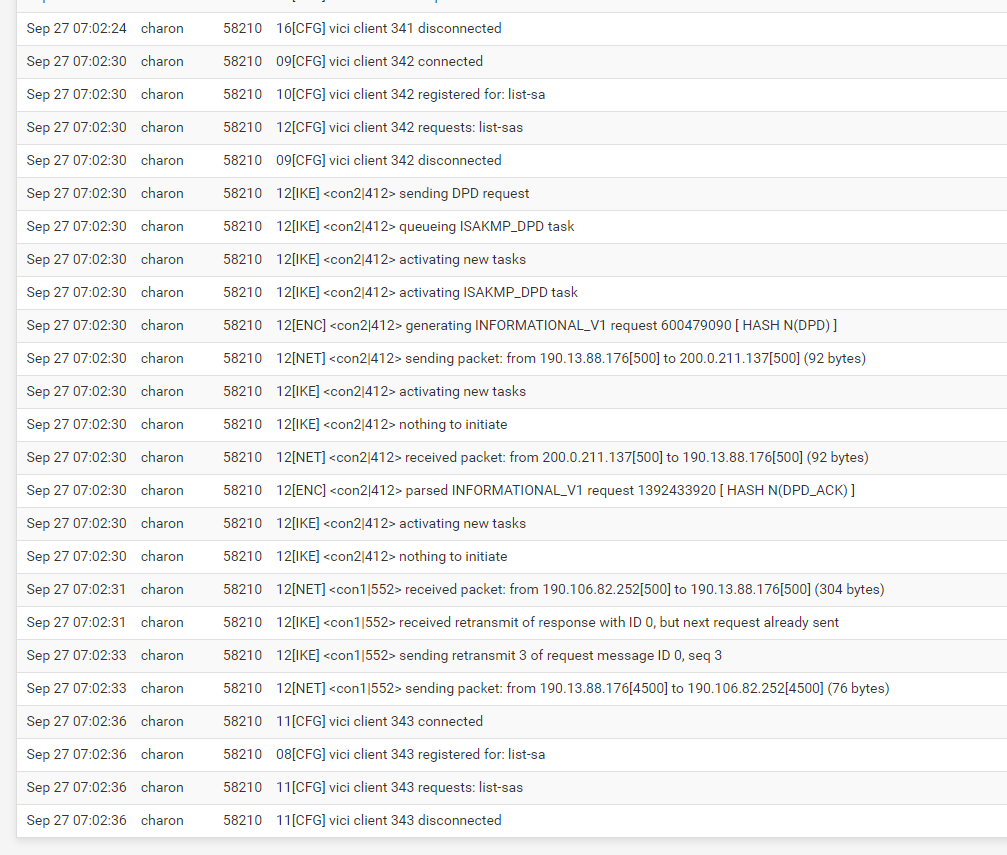
Last 500 IPsec Log Entries. (Maximum 500)
Sep 27 14:02:22 charon 18669 06[CFG] mobike = 0
Sep 27 14:02:22 charon 18669 06[CFG] aggressive = 0
Sep 27 14:02:22 charon 18669 06[CFG] dscp = 0x00
Sep 27 14:02:22 charon 18669 06[CFG] encap = 0
Sep 27 14:02:22 charon 18669 06[CFG] dpd_delay = 10
Sep 27 14:02:22 charon 18669 06[CFG] dpd_timeout = 60
Sep 27 14:02:22 charon 18669 06[CFG] fragmentation = 2
Sep 27 14:02:22 charon 18669 06[CFG] childless = 0
Sep 27 14:02:22 charon 18669 06[CFG] unique = UNIQUE_REPLACE
Sep 27 14:02:22 charon 18669 06[CFG] keyingtries = 1
Sep 27 14:02:22 charon 18669 06[CFG] reauth_time = 25920
Sep 27 14:02:22 charon 18669 06[CFG] rekey_time = 0
Sep 27 14:02:22 charon 18669 06[CFG] over_time = 2880
Sep 27 14:02:22 charon 18669 06[CFG] rand_time = 2880
Sep 27 14:02:22 charon 18669 06[CFG] proposals = IKE:AES_CBC_128/HMAC_SHA1_96/PRF_HMAC_SHA1/MODP_1024
Sep 27 14:02:22 charon 18669 06[CFG] if_id_in = 0
Sep 27 14:02:22 charon 18669 06[CFG] if_id_out = 0
Sep 27 14:02:22 charon 18669 06[CFG] local:
Sep 27 14:02:22 charon 18669 06[CFG] class = pre-shared key
Sep 27 14:02:22 charon 18669 06[CFG] id = %any
Sep 27 14:02:22 charon 18669 06[CFG] remote:
Sep 27 14:02:22 charon 18669 06[CFG] class = pre-shared key
Sep 27 14:02:22 charon 18669 06[CFG] id = %any
Sep 27 14:02:22 charon 18669 06[CFG] added vici connection: con1
Sep 27 14:02:22 charon 18669 06[CFG] installing 'con1_1'
Sep 27 14:02:22 charon 18669 06[CFG] configured proposals: ESP:AES_CBC_256/HMAC_SHA1_96/NO_EXT_SEQ, ESP:AES_CBC_192/HMAC_SHA1_96/NO_EXT_SEQ, ESP:AES_CBC_128/HMAC_SHA1_96/NO_EXT_SEQ
Sep 27 14:02:22 charon 18669 06[CHD] CHILD_SA con1_1{1} state change: CREATED => ROUTED
Sep 27 14:02:22 charon 18669 08[CFG] vici client 2 disconnected
Sep 27 14:02:23 charon 18669 13[CFG] vici client 3 connected
Sep 27 14:02:23 charon 18669 11[CFG] vici client 3 registered for: list-sa
Sep 27 14:02:23 charon 18669 11[CFG] vici client 3 requests: list-sas
Sep 27 14:02:23 charon 18669 10[CFG] vici client 3 disconnected
Sep 27 14:02:23 charon 18669 09[NET] <1> received packet: from 200.0.211.137[500] to 190.13.88.176[500] (168 bytes)
Sep 27 14:02:23 charon 18669 09[ENC] <1> parsed ID_PROT request 0 [ SA V V V V ]
Sep 27 14:02:23 charon 18669 09[CFG] <1> looking for an IKEv1 config for 190.13.88.176...200.0.211.137
Sep 27 14:02:23 charon 18669 09[IKE] <1> no IKE config found for 190.13.88.176...200.0.211.137, sending NO_PROPOSAL_CHOSEN
Sep 27 14:02:23 charon 18669 09[ENC] <1> generating INFORMATIONAL_V1 request 2094589081 [ N(NO_PROP) ]
Sep 27 14:02:23 charon 18669 09[NET] <1> sending packet: from 190.13.88.176[500] to 200.0.211.137[500] (40 bytes)
Sep 27 14:02:23 charon 18669 09[IKE] <1> IKE_SA (unnamed)[1] state change: CREATED => DESTROYING
Sep 27 14:02:27 charon 18669 05[CFG] vici client 4 connected
Sep 27 14:02:27 charon 18669 08[CFG] vici client 4 registered for: list-sa
Sep 27 14:02:27 charon 18669 08[CFG] vici client 4 requests: list-sas
Sep 27 14:02:27 charon 18669 06[CFG] vici client 4 disconnected
Sep 27 14:02:27 charon 18669 16[KNL] creating acquire job for policy 190.13.88.176/32|/0 === 190.106.82.252/32|/0 with reqid {1}
Sep 27 14:02:27 charon 18669 08[IKE] <con1|2> queueing ISAKMP_VENDOR task
Sep 27 14:02:27 charon 18669 08[IKE] <con1|2> queueing ISAKMP_CERT_PRE task
Sep 27 14:02:27 charon 18669 08[IKE] <con1|2> queueing MAIN_MODE task
Sep 27 14:02:27 charon 18669 08[IKE] <con1|2> queueing ISAKMP_CERT_POST task
Sep 27 14:02:27 charon 18669 08[IKE] <con1|2> queueing ISAKMP_NATD task
Sep 27 14:02:27 charon 18669 08[IKE] <con1|2> queueing QUICK_MODE task
Sep 27 14:02:27 charon 18669 08[IKE] <con1|2> activating new tasks
Sep 27 14:02:27 charon 18669 08[IKE] <con1|2> activating ISAKMP_VENDOR task
Sep 27 14:02:27 charon 18669 08[IKE] <con1|2> activating ISAKMP_CERT_PRE task
Sep 27 14:02:27 charon 18669 08[IKE] <con1|2> activating MAIN_MODE task
Sep 27 14:02:27 charon 18669 08[IKE] <con1|2> activating ISAKMP_CERT_POST task
Sep 27 14:02:27 charon 18669 08[IKE] <con1|2> activating ISAKMP_NATD task
Sep 27 14:02:27 charon 18669 08[IKE] <con1|2> sending XAuth vendor ID
Sep 27 14:02:27 charon 18669 08[IKE] <con1|2> sending DPD vendor ID
Sep 27 14:02:27 charon 18669 08[IKE] <con1|2> sending FRAGMENTATION vendor ID
Sep 27 14:02:27 charon 18669 08[IKE] <con1|2> sending NAT-T (RFC 3947) vendor ID
Sep 27 14:02:27 charon 18669 08[IKE] <con1|2> sending draft-ietf-ipsec-nat-t-ike-02\n vendor ID
Sep 27 14:02:27 charon 18669 08[IKE] <con1|2> initiating Main Mode IKE_SA con1[2] to 190.106.82.252
Sep 27 14:02:27 charon 18669 08[IKE] <con1|2> IKE_SA con1[2] state change: CREATED => CONNECTING
Sep 27 14:02:27 charon 18669 08[CFG] <con1|2> configured proposals: IKE:AES_CBC_128/HMAC_SHA1_96/PRF_HMAC_SHA1/MODP_1024
Sep 27 14:02:27 charon 18669 08[ENC] <con1|2> generating ID_PROT request 0 [ SA V V V V V ]
Sep 27 14:02:27 charon 18669 08[NET] <con1|2> sending packet: from 190.13.88.176[500] to 190.106.82.252[500] (180 bytes)
Sep 27 14:02:27 charon 18669 08[NET] <con1|2> received packet: from 190.106.82.252[500] to 190.13.88.176[500] (104 bytes)
Sep 27 14:02:27 charon 18669 08[ENC] <con1|2> parsed ID_PROT response 0 [ SA V ]
Sep 27 14:02:27 charon 18669 08[IKE] <con1|2> received NAT-T (RFC 3947) vendor ID
Sep 27 14:02:27 charon 18669 08[CFG] <con1|2> selecting proposal:
Sep 27 14:02:27 charon 18669 08[CFG] <con1|2> proposal matches
Sep 27 14:02:27 charon 18669 08[CFG] <con1|2> received proposals: IKE:AES_CBC_128/HMAC_SHA1_96/PRF_HMAC_SHA1/MODP_1024
Sep 27 14:02:27 charon 18669 08[CFG] <con1|2> configured proposals: IKE:AES_CBC_128/HMAC_SHA1_96/PRF_HMAC_SHA1/MODP_1024
Sep 27 14:02:27 charon 18669 08[CFG] <con1|2> selected proposal: IKE:AES_CBC_128/HMAC_SHA1_96/PRF_HMAC_SHA1/MODP_1024
Sep 27 14:02:27 charon 18669 08[IKE] <con1|2> reinitiating already active tasks
Sep 27 14:02:27 charon 18669 08[IKE] <con1|2> ISAKMP_VENDOR task
Sep 27 14:02:27 charon 18669 08[IKE] <con1|2> MAIN_MODE task
Sep 27 14:02:27 charon 18669 08[ENC] <con1|2> generating ID_PROT request 0 [ KE No NAT-D NAT-D ]
Sep 27 14:02:27 charon 18669 08[NET] <con1|2> sending packet: from 190.13.88.176[500] to 190.106.82.252[500] (244 bytes)
Sep 27 14:02:27 charon 18669 08[NET] <con1|2> received packet: from 190.106.82.252[500] to 190.13.88.176[500] (304 bytes)
Sep 27 14:02:27 charon 18669 08[ENC] <con1|2> parsed ID_PROT response 0 [ KE No V V V V NAT-D NAT-D ]
Sep 27 14:02:27 charon 18669 08[IKE] <con1|2> received Cisco Unity vendor ID
Sep 27 14:02:27 charon 18669 08[IKE] <con1|2> received DPD vendor ID
Sep 27 14:02:27 charon 18669 08[ENC] <con1|2> received unknown vendor ID: 66:b8:7c:66:33:4d:e5:6f:8e:75:19:50:0a:be:07:71
Sep 27 14:02:27 charon 18669 08[IKE] <con1|2> received XAuth vendor ID
Sep 27 14:02:27 charon 18669 08[IKE] <con1|2> remote host is behind NAT
Sep 27 14:02:27 charon 18669 08[IKE] <con1|2> reinitiating already active tasks
Sep 27 14:02:27 charon 18669 08[IKE] <con1|2> ISAKMP_VENDOR task
Sep 27 14:02:27 charon 18669 08[IKE] <con1|2> MAIN_MODE task
Sep 27 14:02:27 charon 18669 08[ENC] <con1|2> generating ID_PROT request 0 [ ID HASH ]
Sep 27 14:02:27 charon 18669 08[NET] <con1|2> sending packet: from 190.13.88.176[4500] to 190.106.82.252[4500] (76 bytes)
Sep 27 14:02:27 charon 18669 08[NET] <con1|2> received packet: from 190.106.82.252[4500] to 190.13.88.176[4500] (76 bytes)
Sep 27 14:02:27 charon 18669 08[ENC] <con1|2> parsed ID_PROT response 0 [ ID HASH ]
Sep 27 14:02:27 charon 18669 08[IKE] <con1|2> IKE_SA con1[2] established between 190.13.88.176[190.13.88.176]...190.106.82.252[192.168.9.223]
Sep 27 14:02:27 charon 18669 08[IKE] <con1|2> IKE_SA con1[2] state change: CONNECTING => ESTABLISHED
Sep 27 14:02:27 charon 18669 08[IKE] <con1|2> scheduling reauthentication in 25466s
Sep 27 14:02:27 charon 18669 08[IKE] <con1|2> maximum IKE_SA lifetime 28346s
Sep 27 14:02:27 charon 18669 08[IKE] <con1|2> activating new tasks
Sep 27 14:02:27 charon 18669 08[IKE] <con1|2> activating QUICK_MODE task
Sep 27 14:02:27 charon 18669 08[CFG] <con1|2> configured proposals: ESP:AES_CBC_256/HMAC_SHA1_96/MODP_1024/NO_EXT_SEQ, ESP:AES_CBC_192/HMAC_SHA1_96/MODP_1024/NO_EXT_SEQ, ESP:AES_CBC_128/HMAC_SHA1_96/MODP_1024/NO_EXT_SEQ
Sep 27 14:02:27 charon 18669 08[CFG] <con1|2> configured proposals: ESP:AES_CBC_256/HMAC_SHA1_96/MODP_1024/NO_EXT_SEQ, ESP:AES_CBC_192/HMAC_SHA1_96/MODP_1024/NO_EXT_SEQ, ESP:AES_CBC_128/HMAC_SHA1_96/MODP_1024/NO_EXT_SEQ
Sep 27 14:02:27 charon 18669 08[CFG] <con1|2> proposing traffic selectors for us:
Sep 27 14:02:27 charon 18669 08[CFG] <con1|2> 192.168.1.0/24|/0
Sep 27 14:02:27 charon 18669 08[CFG] <con1|2> proposing traffic selectors for other:
Sep 27 14:02:27 charon 18669 08[CFG] <con1|2> 192.168.6.0/24|/0
Sep 27 14:02:27 charon 18669 08[ENC] <con1|2> generating QUICK_MODE request 2208581255 [ HASH SA No KE ID ID ]
Sep 27 14:02:27 charon 18669 08[NET] <con1|2> sending packet: from 190.13.88.176[4500] to 190.106.82.252[4500] (380 bytes)
Sep 27 14:02:27 charon 18669 08[NET] <con1|2> received packet: from 190.106.82.252[4500] to 190.13.88.176[4500] (332 bytes)
Sep 27 14:02:27 charon 18669 08[ENC] <con1|2> parsed QUICK_MODE response 2208581255 [ HASH SA No KE ID ID N((24576)) ]
Sep 27 14:02:27 charon 18669 08[CFG] <con1|2> selecting proposal:
Sep 27 14:02:27 charon 18669 08[CFG] <con1|2> no acceptable ENCRYPTION_ALGORITHM found
Sep 27 14:02:27 charon 18669 08[CFG] <con1|2> selecting proposal:
Sep 27 14:02:27 charon 18669 08[CFG] <con1|2> no acceptable ENCRYPTION_ALGORITHM found
Sep 27 14:02:27 charon 18669 08[CFG] <con1|2> selecting proposal:
Sep 27 14:02:27 charon 18669 08[CFG] <con1|2> proposal matches
Sep 27 14:02:27 charon 18669 08[CFG] <con1|2> received proposals: ESP:AES_CBC_128/HMAC_SHA1_96/MODP_1024/NO_EXT_SEQ
Sep 27 14:02:27 charon 18669 08[CFG] <con1|2> configured proposals: ESP:AES_CBC_256/HMAC_SHA1_96/MODP_1024/NO_EXT_SEQ, ESP:AES_CBC_192/HMAC_SHA1_96/MODP_1024/NO_EXT_SEQ, ESP:AES_CBC_128/HMAC_SHA1_96/MODP_1024/NO_EXT_SEQ
Sep 27 14:02:27 charon 18669 08[CFG] <con1|2> selected proposal: ESP:AES_CBC_128/HMAC_SHA1_96/MODP_1024/NO_EXT_SEQ
Sep 27 14:02:27 charon 18669 08[CHD] <con1|2> CHILD_SA con1_1{2} state change: CREATED => INSTALLING
Sep 27 14:02:27 charon 18669 08[CHD] <con1|2> using AES_CBC for encryption
Sep 27 14:02:27 charon 18669 08[CHD] <con1|2> using HMAC_SHA1_96 for integrity
Sep 27 14:02:27 charon 18669 08[CHD] <con1|2> adding inbound ESP SA
Sep 27 14:02:27 charon 18669 08[CHD] <con1|2> SPI 0xcbe9ee0a, src 190.106.82.252 dst 190.13.88.176
Sep 27 14:02:27 charon 18669 08[CHD] <con1|2> adding outbound ESP SA
Sep 27 14:02:27 charon 18669 08[CHD] <con1|2> SPI 0x1488dc67, src 190.13.88.176 dst 190.106.82.252
Sep 27 14:02:27 charon 18669 08[IKE] <con1|2> CHILD_SA con1_1{2} established with SPIs cbe9ee0a_i 1488dc67_o and TS 192.168.1.0/24|/0 === 192.168.6.0/24|/0
Sep 27 14:02:27 charon 18669 08[CHD] <con1|2> CHILD_SA con1_1{2} state change: INSTALLING => INSTALLED
Sep 27 14:02:27 charon 18669 08[IKE] <con1|2> reinitiating already active tasks
Sep 27 14:02:27 charon 18669 08[IKE] <con1|2> QUICK_MODE task
Sep 27 14:02:27 charon 18669 08[ENC] <con1|2> generating QUICK_MODE request 2208581255 [ HASH ]
Sep 27 14:02:27 charon 18669 08[NET] <con1|2> sending packet: from 190.13.88.176[4500] to 190.106.82.252[4500] (60 bytes)
Sep 27 14:02:27 charon 18669 08[IKE] <con1|2> activating new tasks
Sep 27 14:02:27 charon 18669 08[IKE] <con1|2> nothing to initiate
Sep 27 14:02:32 charon 18669 08[CFG] vici client 5 connected
Sep 27 14:02:32 charon 18669 08[CFG] vici client 5 registered for: list-sa
Sep 27 14:02:32 charon 18669 13[CFG] vici client 5 requests: list-sas
Sep 27 14:02:32 charon 18669 13[CFG] vici client 5 disconnected
Sep 27 14:02:33 charon 18669 08[CFG] vici client 6 connected
Sep 27 14:02:33 charon 18669 10[CFG] vici client 6 registered for: list-sa
Sep 27 14:02:33 charon 18669 10[CFG] vici client 6 requests: list-sas
Sep 27 14:02:33 charon 18669 10[CFG] vici client 6 disconnected
Sep 27 14:02:33 charon 18669 10[NET] <3> received packet: from 200.0.211.137[500] to 190.13.88.176[500] (168 bytes)
Sep 27 14:02:33 charon 18669 10[ENC] <3> parsed ID_PROT request 0 [ SA V V V V ]
Sep 27 14:02:33 charon 18669 10[CFG] <3> looking for an IKEv1 config for 190.13.88.176...200.0.211.137
Sep 27 14:02:33 charon 18669 10[IKE] <3> no IKE config found for 190.13.88.176...200.0.211.137, sending NO_PROPOSAL_CHOSEN
Sep 27 14:02:33 charon 18669 10[ENC] <3> generating INFORMATIONAL_V1 request 3044333982 [ N(NO_PROP) ]
Sep 27 14:02:33 charon 18669 10[NET] <3> sending packet: from 190.13.88.176[500] to 200.0.211.137[500] (40 bytes)
Sep 27 14:02:33 charon 18669 10[IKE] <3> IKE_SA (unnamed)[3] state change: CREATED => DESTROYING
Sep 27 14:02:37 charon 18669 10[CFG] vici client 7 connected
Sep 27 14:02:37 charon 18669 10[CFG] vici client 7 registered for: list-sa
Sep 27 14:02:37 charon 18669 10[CFG] vici client 7 requests: list-sas
Sep 27 14:02:37 charon 18669 05[CFG] vici client 7 disconnected
Sep 27 14:02:42 charon 18669 06[CFG] vici client 8 connected
Sep 27 14:02:42 charon 18669 06[CFG] vici client 8 registered for: list-sa
Sep 27 14:02:42 charon 18669 06[CFG] vici client 8 requests: list-sas
Sep 27 14:02:42 charon 18669 15[CFG] vici client 8 disconnected
Sep 27 14:02:43 charon 18669 16[NET] <4> received packet: from 200.0.211.137[500] to 190.13.88.176[500] (168 bytes)
Sep 27 14:02:43 charon 18669 16[ENC] <4> parsed ID_PROT request 0 [ SA V V V V ]
Sep 27 14:02:43 charon 18669 16[CFG] <4> looking for an IKEv1 config for 190.13.88.176...200.0.211.137
Sep 27 14:02:43 charon 18669 16[IKE] <4> no IKE config found for 190.13.88.176...200.0.211.137, sending NO_PROPOSAL_CHOSEN
Sep 27 14:02:43 charon 18669 16[ENC] <4> generating INFORMATIONAL_V1 request 1107779914 [ N(NO_PROP) ]
Sep 27 14:02:43 charon 18669 16[NET] <4> sending packet: from 190.13.88.176[500] to 200.0.211.137[500] (40 bytes)
Sep 27 14:02:43 charon 18669 16[IKE] <4> IKE_SA (unnamed)[4] state change: CREATED => DESTROYING
Sep 27 14:02:44 charon 18669 12[CFG] vici client 9 connected
Sep 27 14:02:44 charon 18669 16[CFG] vici client 9 registered for: list-sa
Sep 27 14:02:44 charon 18669 13[CFG] vici client 9 requests: list-sas
Sep 27 14:02:44 charon 18669 16[CFG] vici client 9 disconnected
Sep 27 14:02:46 charon 18669 09[CFG] vici client 10 connected
Sep 27 14:02:46 charon 18669 10[CFG] vici client 10 requests: reload-settings
Sep 27 14:02:46 charon 18669 10[CFG] ipseckey plugin is disabled
Sep 27 14:02:46 charon 18669 10[CFG] loaded 0 entries for attr plugin configuration
Sep 27 14:02:46 charon 18669 10[CFG] loaded 0 RADIUS server configurations
Sep 27 14:02:46 charon 18669 05[CFG] vici client 10 disconnected
Sep 27 14:02:46 charon 18669 10[CFG] vici client 11 connected
Sep 27 14:02:47 charon 18669 05[CFG] vici client 11 requests: get-keys
Sep 27 14:02:47 charon 18669 06[CFG] vici client 11 requests: get-shared
Sep 27 14:02:47 charon 18669 05[CFG] vici client 11 requests: load-shared
Sep 27 14:02:47 charon 18669 05[CFG] loaded IKE shared key with id 'ike-0' for: '%any', '%any'
Sep 27 14:02:47 charon 18669 15[CFG] vici client 11 requests: load-shared
Sep 27 14:02:47 charon 18669 15[CFG] loaded IKE shared key with id 'ike-1' for: '%any', '%any'
Sep 27 14:02:47 charon 18669 06[CFG] vici client 11 requests: get-authorities
Sep 27 14:02:47 charon 18669 12[CFG] vici client 11 requests: get-pools
Sep 27 14:02:47 charon 18669 06[CFG] vici client 11 requests: get-conns
Sep 27 14:02:47 charon 18669 16[CFG] vici client 11 requests: load-conn
Sep 27 14:02:47 charon 18669 16[CFG] conn bypass:
Sep 27 14:02:47 charon 18669 16[CFG] child bypasslan:
Sep 27 14:02:47 charon 18669 16[CFG] rekey_time = 3600
Sep 27 14:02:47 charon 18669 16[CFG] life_time = 3960
Sep 27 14:02:47 charon 18669 16[CFG] rand_time = 360
Sep 27 14:02:47 charon 18669 16[CFG] rekey_bytes = 0
Sep 27 14:02:47 charon 18669 16[CFG] life_bytes = 0
Sep 27 14:02:47 charon 18669 16[CFG] rand_bytes = 0
Sep 27 14:02:47 charon 18669 16[CFG] rekey_packets = 0
Sep 27 14:02:47 charon 18669 16[CFG] life_packets = 0
Sep 27 14:02:47 charon 18669 16[CFG] rand_packets = 0
Sep 27 14:02:47 charon 18669 16[CFG] updown = (null)
Sep 27 14:02:47 charon 18669 16[CFG] hostaccess = 0
Sep 27 14:02:47 charon 18669 16[CFG] ipcomp = 0
Sep 27 14:02:47 charon 18669 16[CFG] mode = PASS
Sep 27 14:02:47 charon 18669 16[CFG] policies = 1
Sep 27 14:02:47 charon 18669 16[CFG] policies_fwd_out = 0
Sep 27 14:02:47 charon 18669 16[CFG] dpd_action = none
Sep 27 14:02:47 charon 18669 16[CFG] start_action = trap
Sep 27 14:02:47 charon 18669 16[CFG] close_action = none
Sep 27 14:02:47 charon 18669 16[CFG] reqid = 0
Sep 27 14:02:47 charon 18669 16[CFG] tfc = 0
Sep 27 14:02:47 charon 18669 16[CFG] priority = 0
Sep 27 14:02:47 charon 18669 16[CFG] interface = (null)
Sep 27 14:02:47 charon 18669 16[CFG] if_id_in = 0
Sep 27 14:02:47 charon 18669 16[CFG] if_id_out = 0
Sep 27 14:02:47 charon 18669 16[CFG] mark_in = 0/0
Sep 27 14:02:47 charon 18669 16[CFG] mark_in_sa = 0
Sep 27 14:02:47 charon 18669 16[CFG] mark_out = 0/0
Sep 27 14:02:47 charon 18669 16[CFG] set_mark_in = 0/0
Sep 27 14:02:47 charon 18669 16[CFG] set_mark_out = 0/0
Sep 27 14:02:47 charon 18669 16[CFG] label = (null)
Sep 27 14:02:47 charon 18669 16[CFG] label_mode = system
Sep 27 14:02:47 charon 18669 16[CFG] inactivity = 0
Sep 27 14:02:47 charon 18669 16[CFG] proposals = ESP:AES_GCM_16_128/AES_GCM_16_192/AES_GCM_16_256/NO_EXT_SEQ, ESP:AES_CBC_128/AES_CBC_192/AES_CBC_256/HMAC_SHA2_256_128/HMAC_SHA2_384_192/HMAC_SHA2_512_256/HMAC_SHA1_96/AES_XCBC_96/NO_EXT_SEQ
Sep 27 14:02:47 charon 18669 16[CFG] local_ts = 192.168.1.0/24|/0
Sep 27 14:02:47 charon 18669 16[CFG] remote_ts = 192.168.1.0/24|/0
Sep 27 14:02:47 charon 18669 16[CFG] hw_offload = no
Sep 27 14:02:47 charon 18669 16[CFG] sha256_96 = 0
Sep 27 14:02:47 charon 18669 16[CFG] copy_df = 1
Sep 27 14:02:47 charon 18669 16[CFG] copy_ecn = 1
Sep 27 14:02:47 charon 18669 16[CFG] copy_dscp = out
Sep 27 14:02:47 charon 18669 16[CFG] version = 0
Sep 27 14:02:47 charon 18669 16[CFG] local_addrs = %any
Sep 27 14:02:47 charon 18669 16[CFG] remote_addrs = 127.0.0.1
Sep 27 14:02:47 charon 18669 16[CFG] local_port = 500
Sep 27 14:02:47 charon 18669 16[CFG] remote_port = 500
Sep 27 14:02:47 charon 18669 16[CFG] send_certreq = 1
Sep 27 14:02:47 charon 18669 16[CFG] send_cert = CERT_SEND_IF_ASKED
Sep 27 14:02:47 charon 18669 16[CFG] ppk_id = (null)
Sep 27 14:02:47 charon 18669 16[CFG] ppk_required = 0
Sep 27 14:02:47 charon 18669 16[CFG] mobike = 1
Sep 27 14:02:47 charon 18669 16[CFG] aggressive = 0
Sep 27 14:02:47 charon 18669 16[CFG] dscp = 0x00
Sep 27 14:02:47 charon 18669 16[CFG] encap = 0
Sep 27 14:02:47 charon 18669 16[CFG] dpd_delay = 0
Sep 27 14:02:47 charon 18669 16[CFG] dpd_timeout = 0
Sep 27 14:02:47 charon 18669 16[CFG] fragmentation = 2
Sep 27 14:02:47 charon 18669 16[CFG] childless = 0
Sep 27 14:02:47 charon 18669 16[CFG] unique = UNIQUE_NO
Sep 27 14:02:47 charon 18669 16[CFG] keyingtries = 1
Sep 27 14:02:47 charon 18669 16[CFG] reauth_time = 0
Sep 27 14:02:47 charon 18669 16[CFG] rekey_time = 14400
Sep 27 14:02:47 charon 18669 16[CFG] over_time = 1440
Sep 27 14:02:47 charon 18669 16[CFG] rand_time = 1440
Sep 27 14:02:47 charon 18669 16[CFG] proposals = IKE:AES_CBC_128/AES_CBC_192/AES_CBC_256/AES_CTR_128/AES_CTR_192/AES_CTR_256/CAMELLIA_CBC_128/CAMELLIA_CBC_192/CAMELLIA_CBC_256/CAMELLIA_CTR_128/CAMELLIA_CTR_192/CAMELLIA_CTR_256/3DES_CBC/HMAC_SHA2_256_128/HMAC_SHA2_384_192/HMAC_SHA2_512_256/HMAC_SHA1_96/AES_XCBC_96/AES_CMAC_96/PRF_HMAC_SHA2_256/PRF_HMAC_SHA2_384/PRF_HMAC_SHA2_512/PRF_AES128_XCBC/PRF_AES128_CMAC/PRF_HMAC_SHA1/ECP_256/ECP_384/ECP_521/ECP_256_BP/ECP_384_BP/ECP_512_BP/CURVE_25519/CURVE_448/MODP_3072/MODP_4096/MODP_6144/MODP_8192/MODP_2048, IKE:AES_GCM_16_128/AES_GCM_16_192/AES_GCM_16_256/AES_CCM_16_128/AES_CCM_16_192/AES_CCM_16_256/CHACHA20_POLY1305/AES_GCM_12_128/AES_GCM_12_192/AES_GCM_12_256/AES_GCM_8_128/AES_GCM_8_192/AES_GCM_8_256/AES_CCM_12_128/AES_CCM_12_192/AES_CCM_12_256/AES_CCM_8_128/AES_CCM_8_192/AES_CCM_8_256/PRF_HMAC_SHA2_256/PRF_HMAC_SHA2_384/PRF_HMAC_SHA2_512/PRF_AES128_XCBC/PRF_AES128_CMAC/PRF_HMAC_SHA1/ECP_256/ECP_384/ECP_521/ECP_256_BP/ECP_384_BP/ECP_512_BP/CURVE_25519/CURVE_448/MODP_3072/MODP_4096/MODP_6144/MODP_8192/MODP_2048 -
@rmainero said in VPN point to point:
Sep 27 14:02:43 charon 18669 16[NET] <4> received packet: from 200.0.211.137[500] to 190.13.88.176[500] (168 bytes)
Sep 27 14:02:43 charon 18669 16[ENC] <4> parsed ID_PROT request 0 [ SA V V V V ]
Sep 27 14:02:43 charon 18669 16[CFG] <4> looking for an IKEv1 config for 190.13.88.176...200.0.211.137
Sep 27 14:02:43 charon 18669 16[IKE] <4> no IKE config found for 190.13.88.176...200.0.211.137, sending NO_PROPOSAL_CHOSEN
Sep 27 14:02:43 charon 18669 16[ENC] <4> generating INFORMATIONAL_V1 request 1107779914 [ N(NO_PROP) ]
Sep 27 14:02:43 charon 18669 16[NET] <4> sending packet: from 190.13.88.176[500] to 200.0.211.137[500] (40 bytes)
Sep 27 14:02:43 charon 18669 16[IKE] <4> IKE_SA (unnamed)[4] state change: CREATED => DESTROYINGSo there it's failing from the other remote site. There is no matching P1. It looks like it doesn't exist or was disabled when that was logged.
But the connection from 190.106.82.252 connects correctly.