Under attack, anything I should do?
-
@AndyRH said in Under attack, anything I should do?:
My web server is getting many hits per second
Thanks for the reminder.
Look like my web server's port 80 has an issue : there are none
@AndyRH said in Under attack, anything I should do?:
Hotels likely do not block 1194 which is OpenVPN and frequently used by business travelers
Hotel here, that's what I use pfSense for, with the captive portal

I block just 1 (one) port : any destination, TCP 25. For, imho, obvious reasons.
And as Andy said, the real clients, not the tourists but the professional one, use some kind of VPN. I'm not going to block them as they are good for 75 % of the turnover. -
@revengineer said in Under attack, anything I should do?:
I have certainly stayed at hotels that block 1194.
Cycle through other VPN ports. Some will be open.
80, 443, 20 and 21 will always be scanned frequently. I am sure there are others that are favorites.
For those afraid of the
jungleinternet, check your logs, those popular ports will have been scanned in the last few seconds. -
@Gertjan said in Under attack, anything I should do?:
Hotel here
I have been to hotels where vpn is blocked on say 1194, because they want you to pay for the "special" internet package that allows for it ;)
So it is a thing ;) heheh
Its funny you stay at a budget hotel and you get wifi and breakfast for free, you stay at a higher end place and they charge you for wifi and breakfast ;) hehehe
-
@revengineer said in Under attack, anything I should do?:
Is there anything I should do other than waiting these attacks out?
That's most probably the only option you have.
A DOSS has just one goal : saturating your down-link thus saturating your uplink.
Even if there is a way to 'suck up' all the useless data, your 'pipe' to the net is bandwidth limited, and the goal is : filling it up.
It doesn't matter which port is focused, but an 'open' port will use a lot more 'firewall/router', so if there is one, it will be used, as the DOSser will get more bang for the buck.If a solution exist, it's the one that the ISP can give you :
As you've said : get another IP.
Or an active DOS protection system, ISP based.
So, next time when you switch ISP, make these criteria part of your selection-list.Or, solve the problem with pure 'Kevin style' : as DOS is a question of "who has the biggest", get that symmetrical 10 Gbit ISP connection.
Now, when a DOSser comes around, he has to bring in a lot of DOS power to fill up that pipe. And better : when you are DOSSed now, it will show up at the ISP-dashboard and as the ISP tends to protect that amount bandwidth avaible, they will act.
( and while doing so, they will also terminate your subscription as you're to hot to handle ^^) -
@revengineer said in Under attack, anything I should do?:
My home IP address has been under attack for a week. I opened port 443 to use with OpenVPN because it is a port that is not blocked in hotels. Over a week ago, I noticed that this port is being pounded by a range of different source IPs and ports at a rate of about 5 per second. There is no indication that anyone got through the firewall. Out of an abundance of caution I locked down port 443, so all requests are now blocked. However, the rate of attack remains the same. My cable provider does not provide a simple option to change the public IP address. Is there anything I should do other than waiting these attacks out?
Thanks for any advice in advance.
Opening port 443 to incoming connections on your firewall's WAN interface makes your setup appear to be a web server. As mentioned by others, web servers are favorite targets for all manner of vulnerability searches using various exploit kits. Nefarious folks are always searching for web servers to compromise.
The normal open port for OpenVPN is UDP port 1194. Most vulnerability scanners won't bother trying to get in via port 1194 because they know guessing the correct certificate key is darn near impossible. So, short answer there is that serious hackers usually don't waste their time scanning for an open UDP port 1194. HTTPS (port 443), on the otherhand, is often times a very attractive target as they are looking for unpatched web servers to try and gain access via an exploit kit.
But 5 hits per second is honestly nothing. A true DDoS attack would be thousands of attempts per second.
If I were you, I would reconsider opening port 443 on the WAN. All it would take is a slight configuration mistake on your end of the firewall to make your firewall's web GUI login available on the Internet. I'm sure you would not want that! If port 1194 access is giving you trouble from some locations (as in being blocked by the admin whose network you are currently using), then perhaps Tailscale is a viable workaround ??
-
@bmeeks said in Under attack, anything I should do?:
I would reconsider opening port 443 on the WAN
These days, for what, 50 €/$ a year ? you have a domain name, a cloud based web space, with a web server at your choice : nginx or apache2, that supports several PHP versions and extension, free snapshots and backups - 'minor' mail support and the likes.
And when it goes the phoenix way, it's easy to recover.
Already the electricity bill of a web server, each year, will be more as the 50 $.Btw : hosting company do have good DOS protection out of the box, as they have thousands of servers to protect. After all : if site goes down, the entire server goes with it, hosting hundreds or thousands other web sites as well. They will black hole the DOS traffic at their border routers.
But I get it : hosting a web server (any server) on your own premises, behind a soHO ISP line, on paper, it can work.
A boy's dream, as it was for me, back then, I admit.
And maybe you have your special reason to host stuff yourself, and if it's ok for you, it's ok for me.
But do get that big pipe
-
Yup 5 connections a second is not a DOS attack. Your IP has been flagged by scanners because port 443 was open at one time so you are seeing a higher that average number of connection attempts. Not much you can do other than wait for it to stop / ignore it or change your IP address.
-
@Gertjan said in Under attack, anything I should do?:
A boy's dream, as it was for me, back then, I admit.
Already forgotten that it is OpenVPN behind Port 443?

-
@elvisimprsntr said in Under attack, anything I should do?:
Does your public IP respond to ICMP pings? If so, figure out how to disable in your ISP kit and/or pfSense
While many people suppress ICMP echo for IPv4, attempting to imitate a black hole, suppressing echo responses really has no impact on security. Also of note is that suppression of echo response is specifically prohibited with IPv6.
If you monitor your WAN link for potential evildoers, you will find lots of various TCP or UDP attempts, but little or no ICMP echo. The reason for this is that it's simply not worth the time for the attacker, because the presence or absence of an echo response provides them with no useful information. In short, an attacker is going to try your ssh et al. ports regardless of whether you respond to ping or not.
-
@dennypage exactly I allow ping for my use, the monitoring tools that let me know if my internet connection is down, etc.
There is little reason not to allow for ping..
edit: also good for sanity checks... Out and about and trying to vpn in and not working, does ping work, if so then prob just a firewall block or vpn service issue vs connectivity issue.
Only sort of extra steps I take is I lock down the services I have open to my country IPs, and I also block known scanners from talking to any of my ports, no reason to be listed in some db that bad guys can access that lists my IPs and ports that answer, etc.
-
If you are not providing any services, then yes you are correct.
But if you are providing services and never open any ports, how would anyone reach the services you are providing?That was the context for my statement.
If google never opened any ports, no one could access gmail, google DNS, etc.
A HUGE difference between opening ports specifically for services and your statement.
OP obiviously opened 443 for an OpenVPN server INBOUND from the internet so he could access home stuff from a hotel.
-
@johnpoz said in Under attack, anything I should do?:
Only sort of extra steps I take is I lock down the services I have open to my country IPs
of note, i don't think this is working right now via pfblocker so finding all U.S. ranges (for example) is quite a task.
-
Thank you for all the response. Let me respond to various without quoting.
First, I have been a pfSense user for more than a decade. All has been working well so I never signed up for the new forum. This explains the low post number.
Having used pfSense for a long time, and having monitored my firewall logs, I can tell that the current activity is unusual. I am well accustomed to many opportunistic hits from various IPs htting various ports. But certain block of IPs trying to access a single common port is new. Hence my inquiry.
I am not running a web server on this port. I use it for openvpn access into my home network. So a server in the cloud does not help here.
Port 443 is a backup port because some hotels block port 1194. Many hotels do allow this port but I need a backup for those who do not. I am running wireguard only experimentally, so do not know about blocking of those ports which are in the 5 digit range.
I have not stated that I am suffering a DDOS attack. I agree that 5/s is low, and my connections are in no way affected. But the behavior is different from what I have observed in the past so its more than normal "noise". Thus, I wanted to check whether any action is required. Theoretically nobody should be able to get in, but I am not sure what the attacker is trying to accomplish. I did some packet captures but cannot interpret the content. I am an advanced home user but not a network export.
The worst case scenario seems to be someone getting in and encrypting my server for ransom. However, no body seems to be overly concerned so that I will simply let it be. The hits themselves do not bother my.
Thank you again for the discussion.
-
@michmoor said in Under attack, anything I should do?:
i don't think this is working right now via pfblocker so finding all U.S. ranges
Its working here.. yeah pfblocker.. why would you think that isn't working?
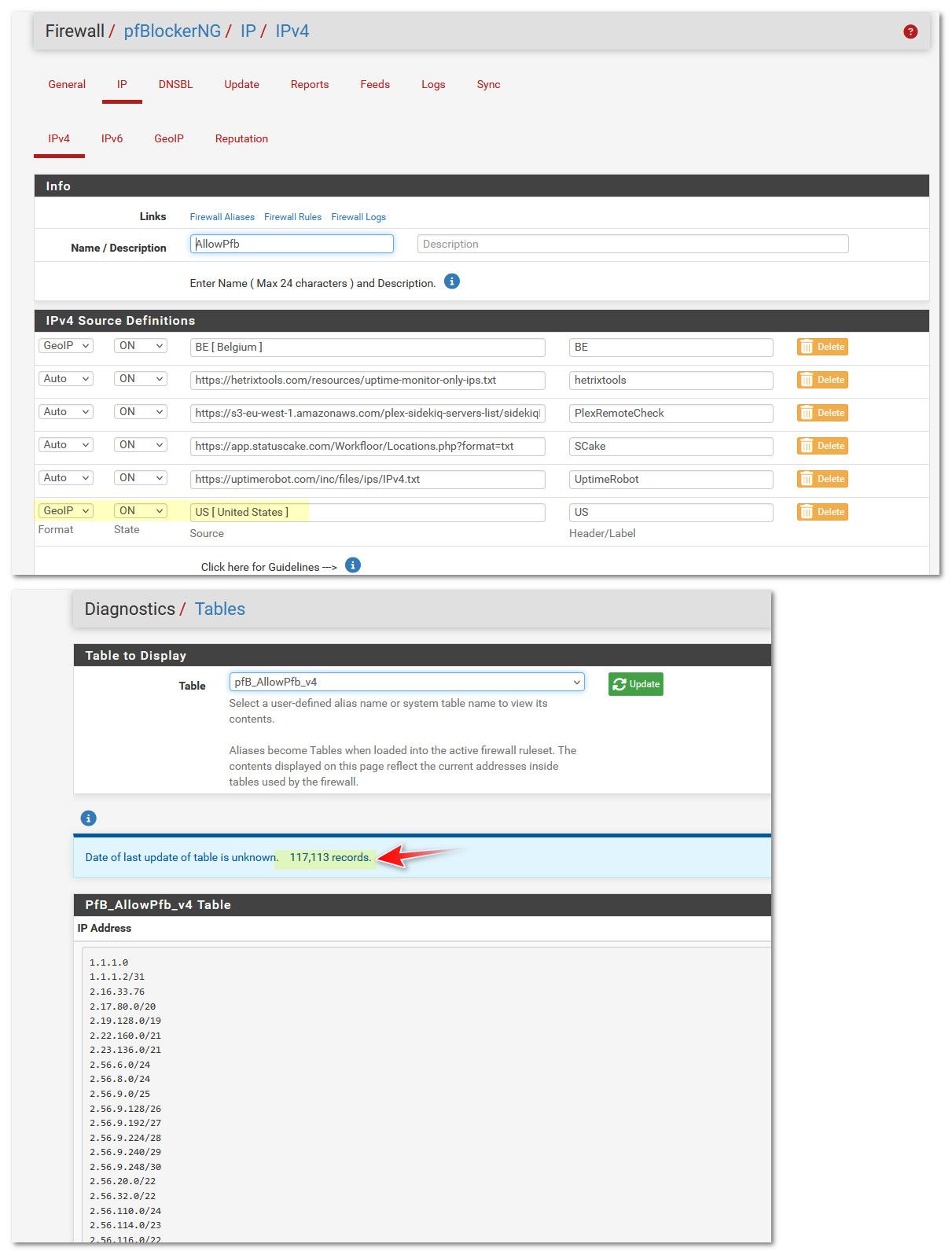
I also have a few other lists in there, some of which are non US Ips.. Beligum for example - have a family member living there currently, so they can access my plex server.
-
@revengineer some syn to 443 isn't going to get far.. since openvpn right away will see its not openvpn traffic, and you should be using tls keys, etc. so yeah openvpn would drop those pretty much instantly and not even attempt to start a openvpn connection - even if they wanted too..
-
@johnpoz pulling IP blocks from countries. Isnt there an intermittent issue with bgpview.io?
I think BBCan said he was looking into it and looking at other sites to pull that info from. -
@michmoor said in Under attack, anything I should do?:
pulling IP blocks from countries. Isnt there an intermittent issue with bgpview.io?
I think that was an issue with ASNs. I believe that the country info comes from Maxmind. [Edit: Specifically, the GeoLite2 City database,]
-
FWIW, I run my OpenVPN on a rando high port and NAT it. But is many moons since I traveled anywhere that offered WiFi over anything more sophisticated than a Netgear router. LOL
-
@dennypage said in Under attack, anything I should do?:
I think that was an issue with ASNs
Well I haven't validated that all the asn info is actually being pulled and correct, I do have some ASN aliases - and they sure seem to be pulling info..
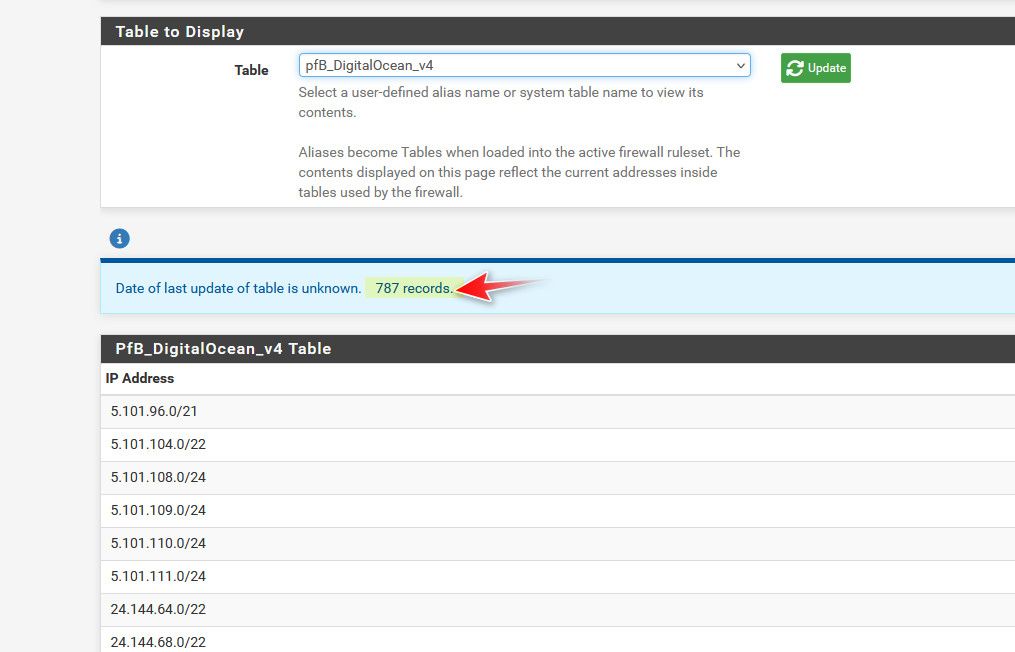
There is never anything good that will ever come unsolicited from DO, which is why I block all of their asns..
-
@johnpoz said in Under attack, anything I should do?:
Well I haven't validated that all the asn info is actually being pulled and correct, I do have some ASN aliases - and they sure seem to be pulling info..
Information available here.