Port Forwarding stopped working after upgrading to 2.8.0
-
@comet424 said in Port Forwarding stopped working after upgrading to 2.8.0:
i find my desktop pc still getting ISP dns but if i run a firefox Docker i will get it to goto teksav
....
ipconfig /release
ipconfig /flushdns
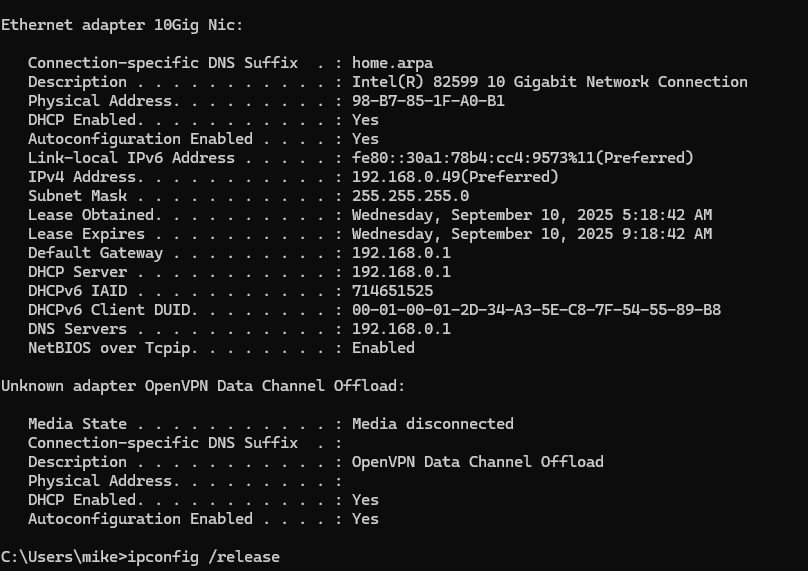
ipconfig /renewYour PC uses DHCP, right ? By default, it does.
Double check that you didn't set a DNS (statically) yourself on this PC.If DHCP : The DNS the PC got was given by the DHCP server - which is (should be !) pfSense.
Check that :
-> Use another PC to access the pfSense GUI !.
and hit Start.
Now, on the PC :ipconfig /release
ipconfig /renewand get back to pfSense.
You should seee the DHCP request from the PC, and the pfSEnse DHCP answer - with the gateway, DNS, etc etc.
What DNS was given by pfSense , By default it is the LAN I of pfSEnse.
If it isn't, that could be explained because you've selected :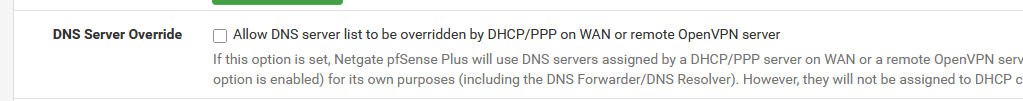
Or you've set (DHCP > LAN server) :
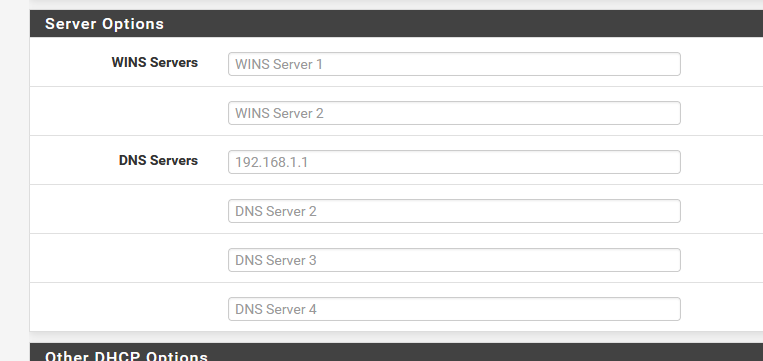
to something else ?
-
@Gertjan
ok so i tried that.. i also had googled about pia and pfsense and tried to go several google searches in.. as what i find is like the lawerance systems and couple others they dont touch that dns resolver.. they did what i did ips on the same lan so novpn and vpn clients and do the no wan egress.. but none of them ever talk about dns leakage,, but i find it leaks.. and i not 100% is it ok for the dns to leak on the vpn side if no traffic goes out the wanso here is the tests and i commented a bit too
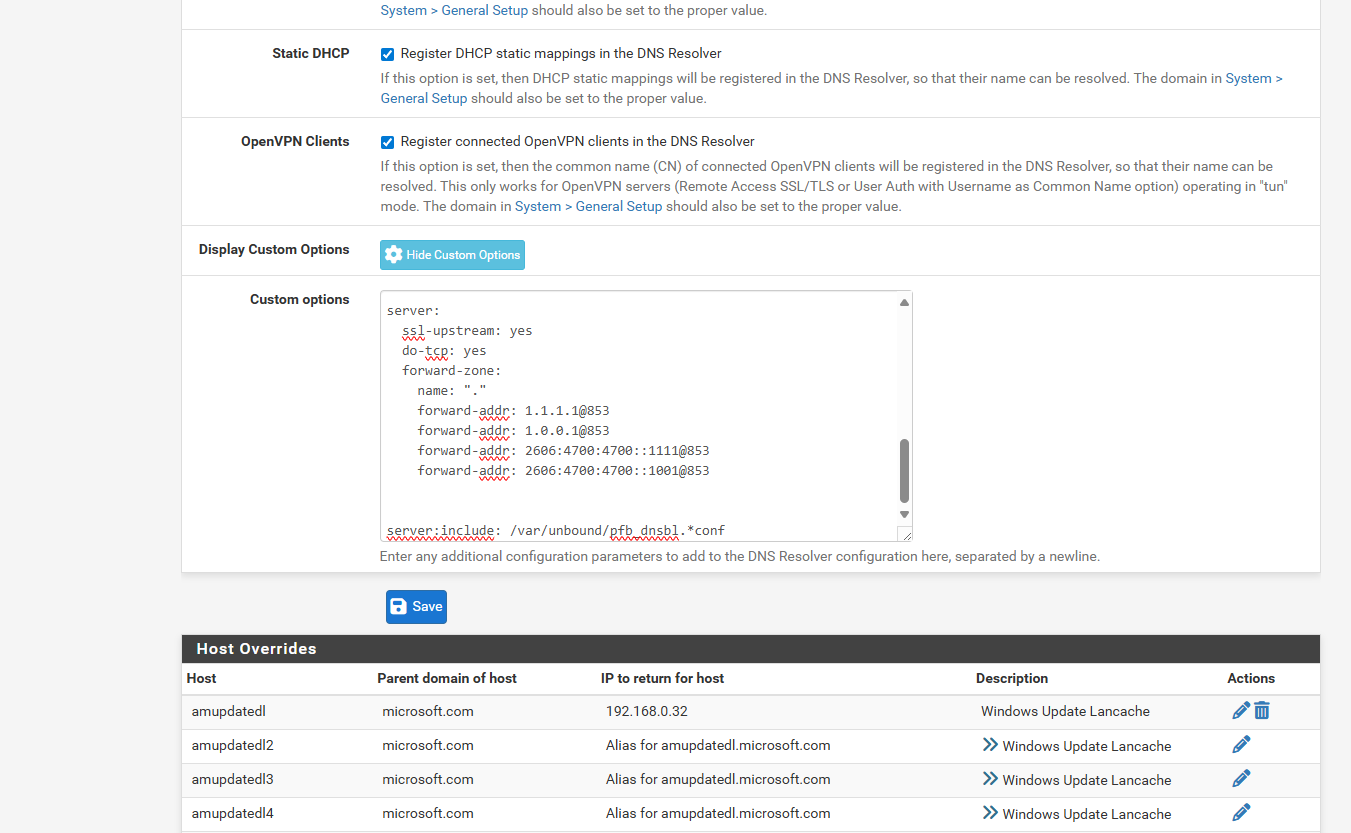
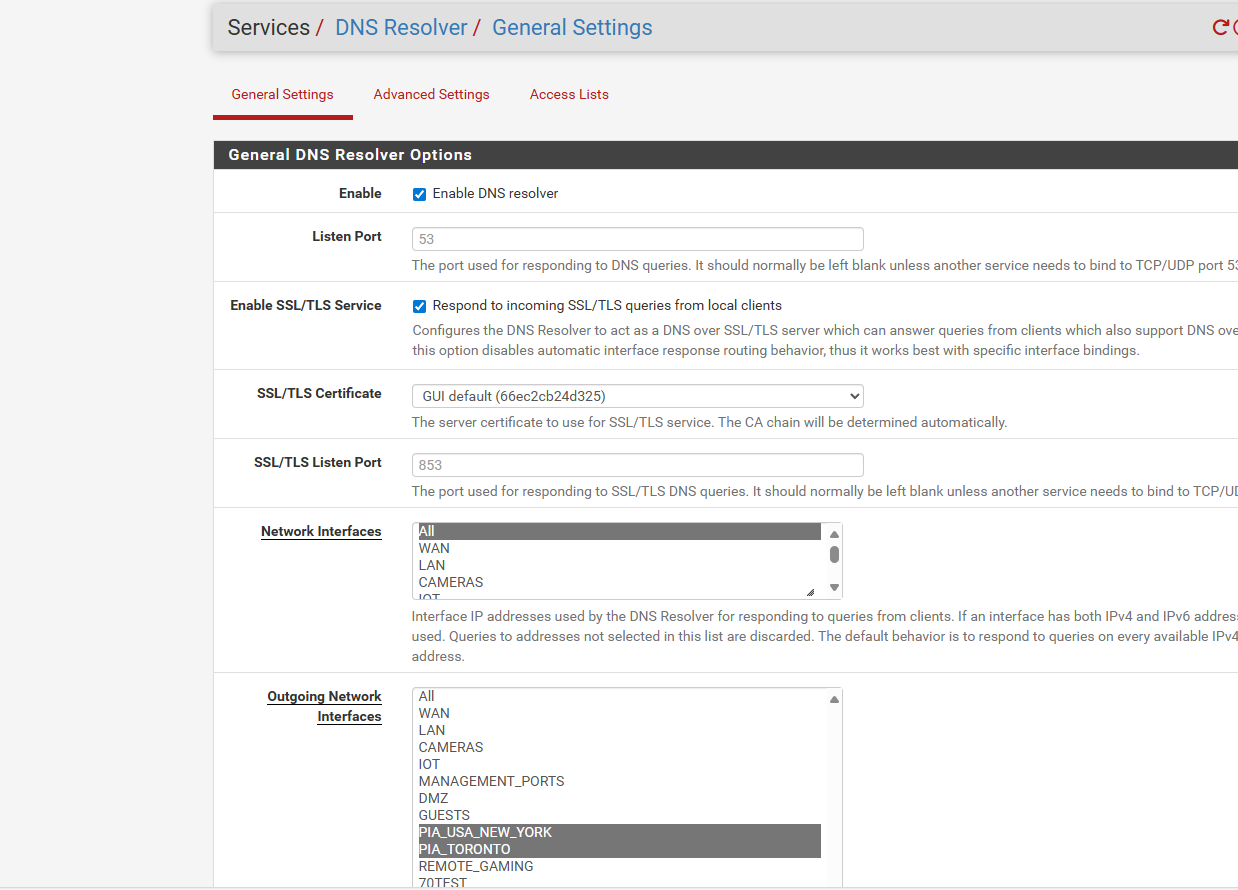
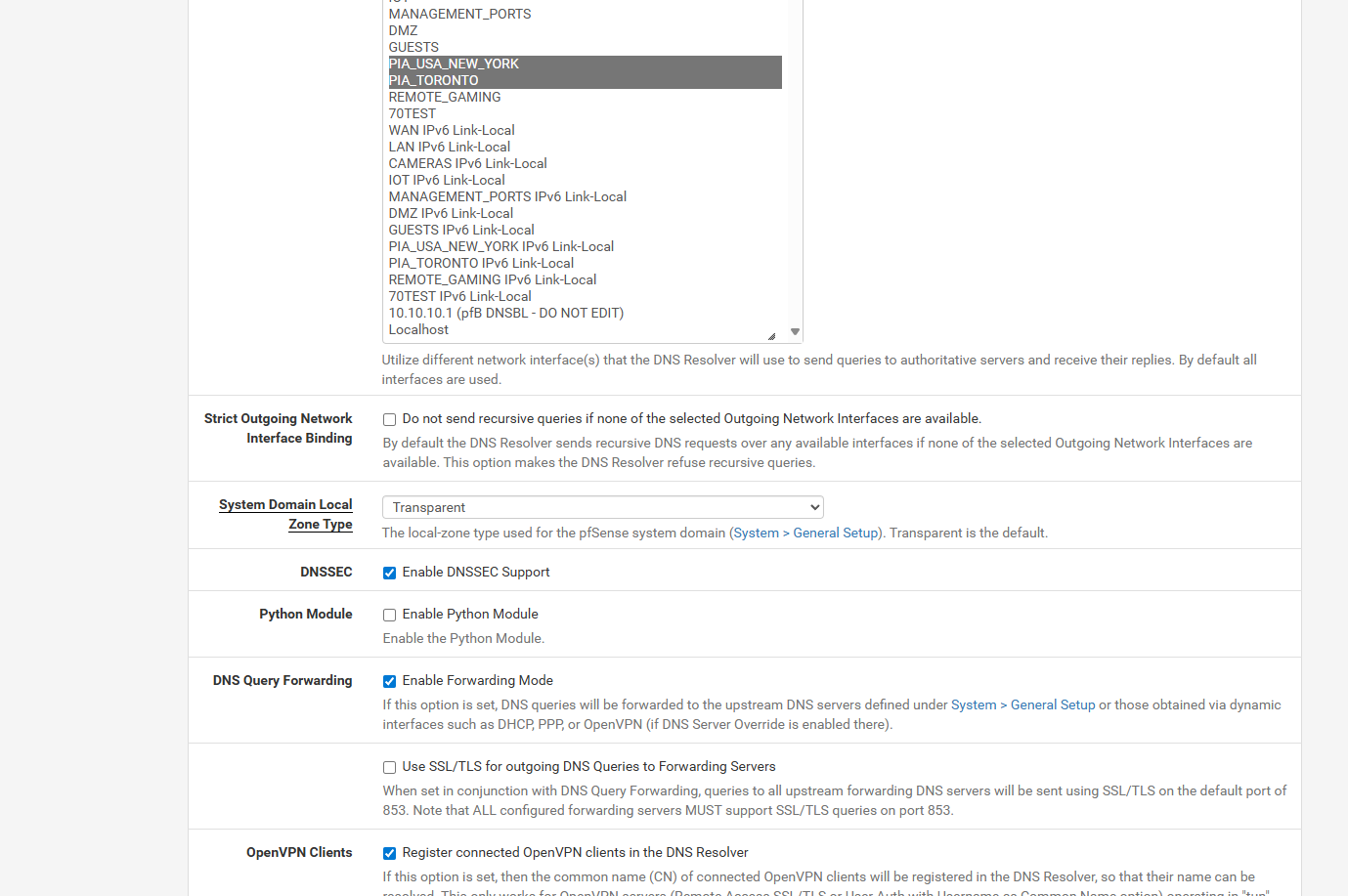
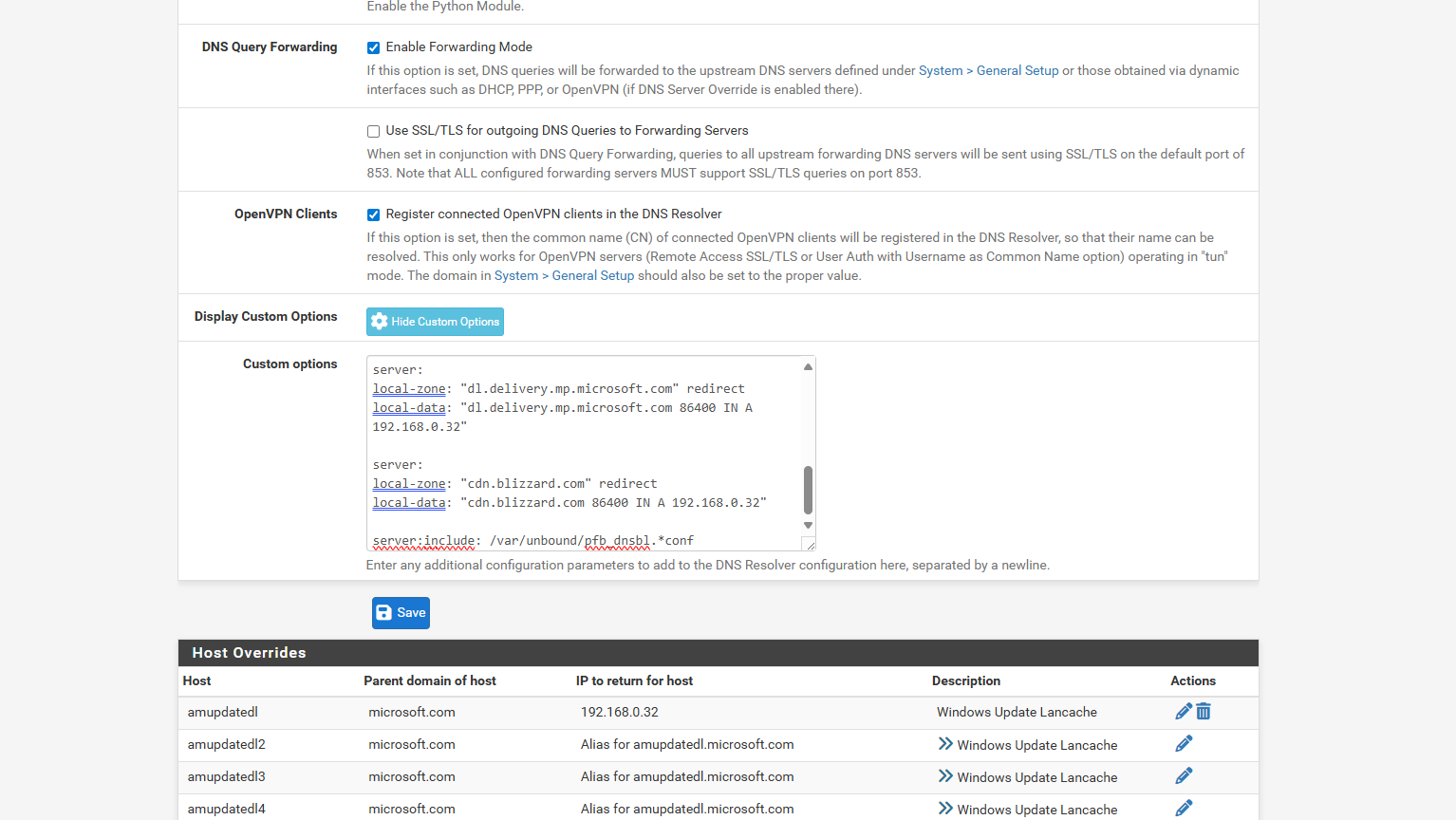
i also followed a couple other articles where they tell you to add custom options code in the dns resolver.. since i have it set All Inbound just 2 PIA VPns as outbound
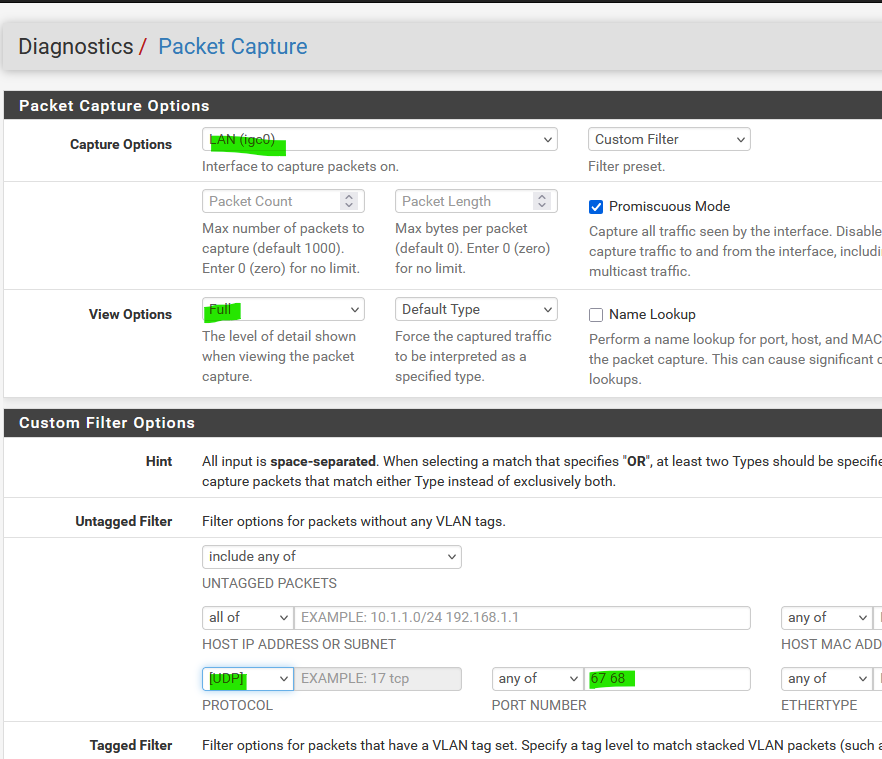
i in the dhcp settings for the desktop pc i had left the dns and gateway blank.. this time i entered in 192.168.0.1 but it didnt help i still got a dhcp for 192.168.0.1packet capture
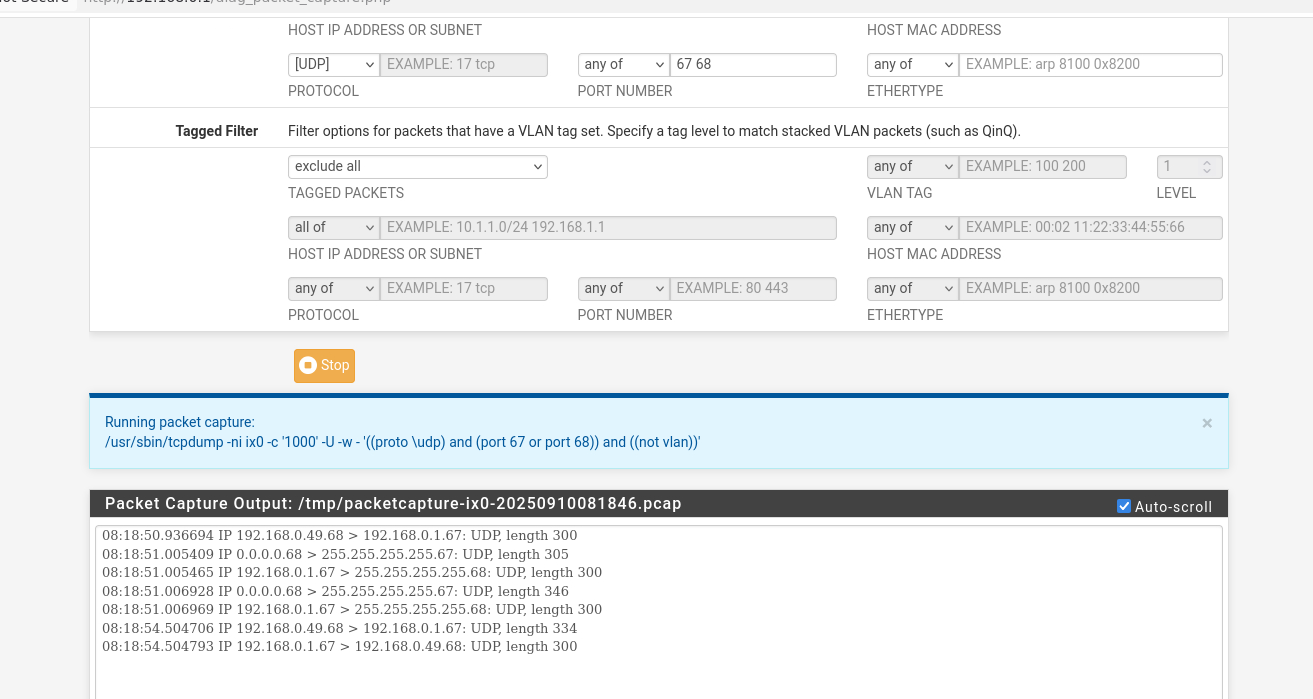
windows dhcp ipconfig /all
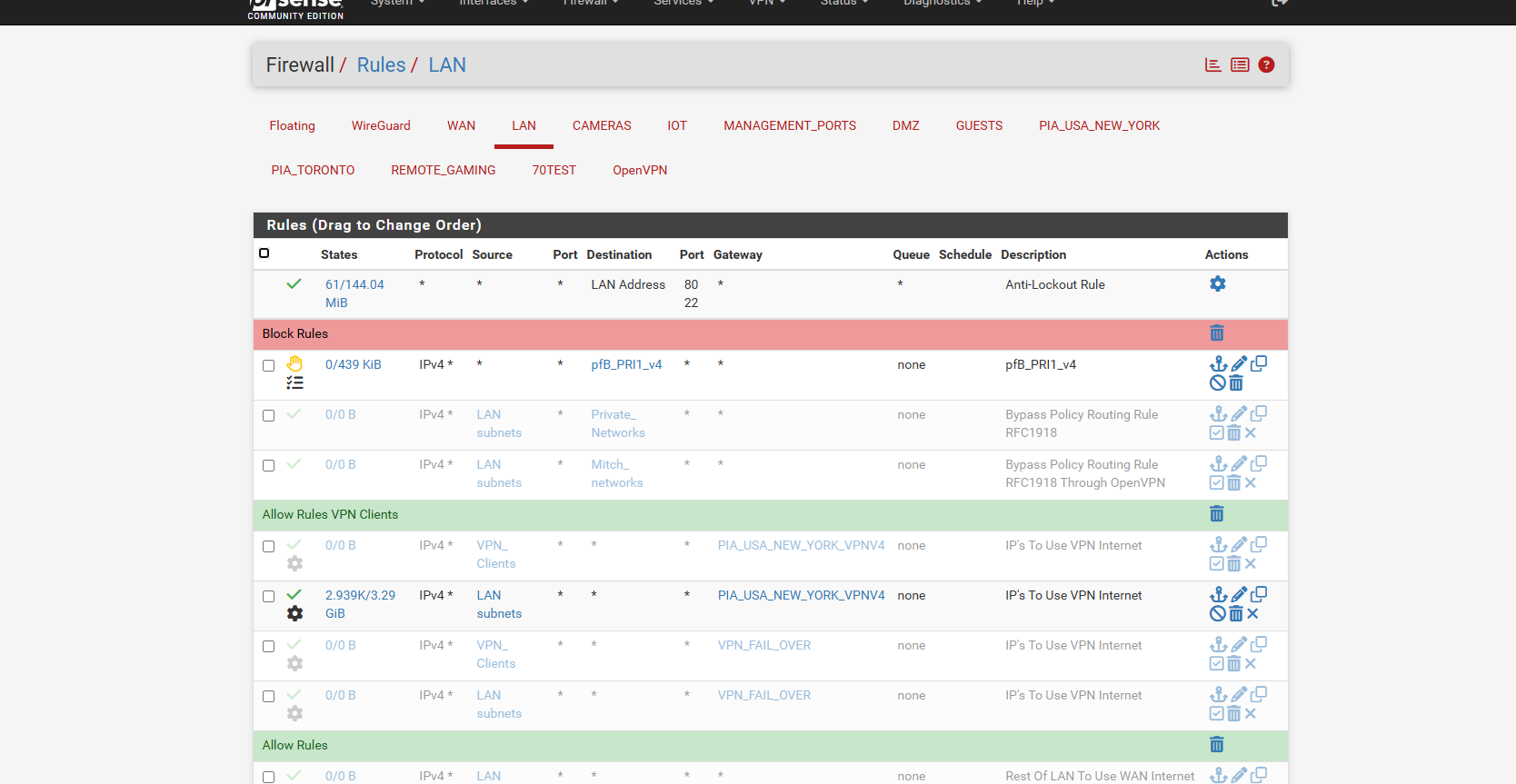
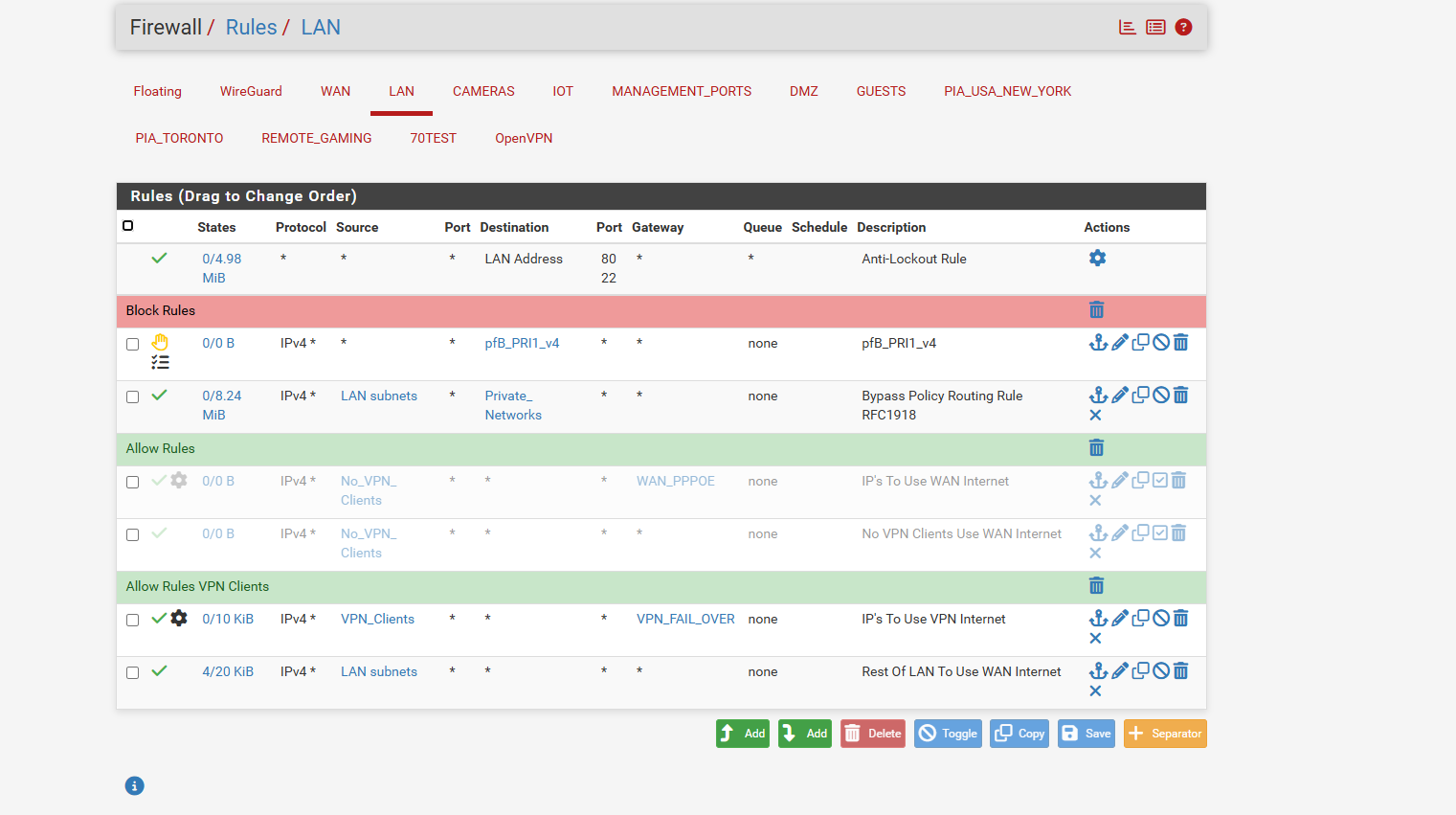
rules I set everything on the LAN to just go out the one VPN and not the 2 vpns or the WAN for now
DNS Resolver.. Inbound All, Outbound to the 2 PIA VPNS. and i followed couple sites they add the server: forwarding for custom options.. i guessing this is for the when the vpn goes down wan cant be resolved anymore and it fails to reconnect..
Fire Fox Docker Browser #1
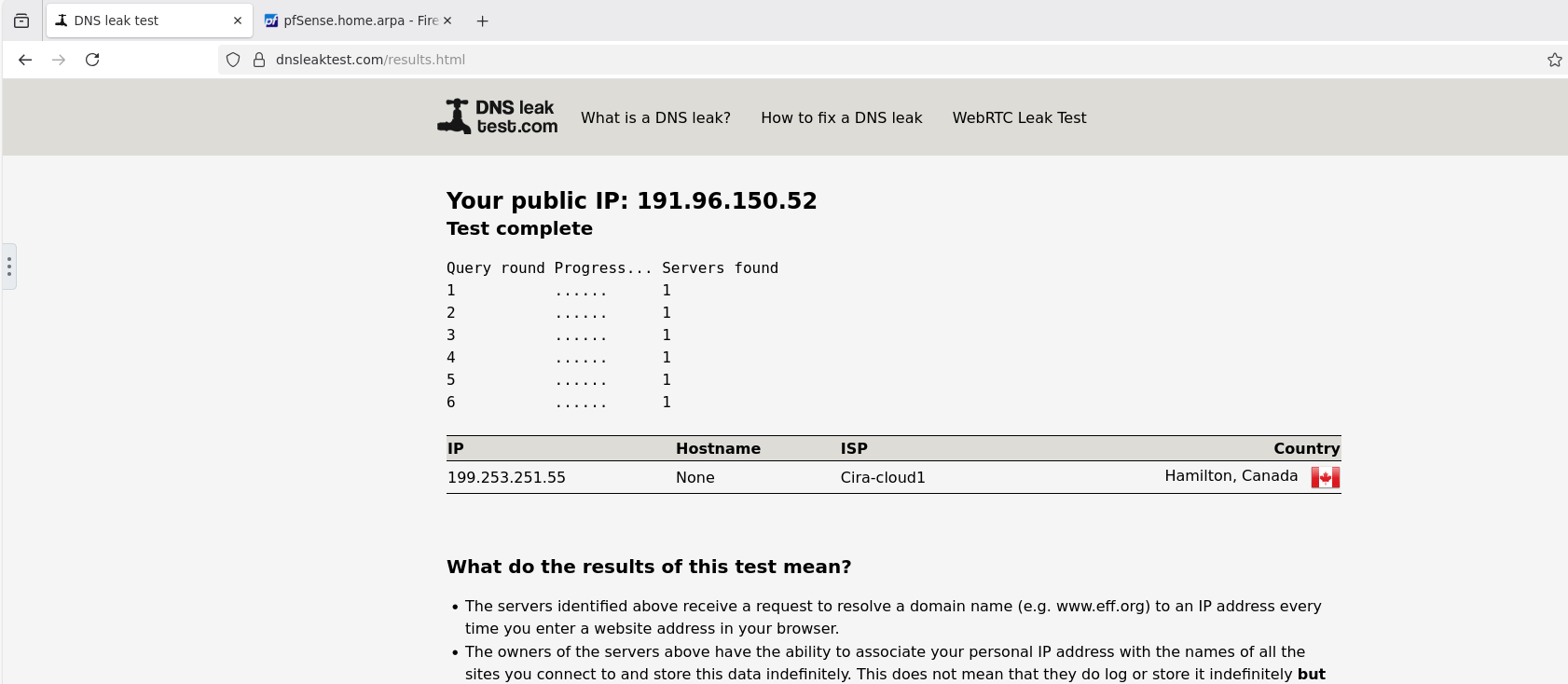
Fire Fox Docker Browser #2
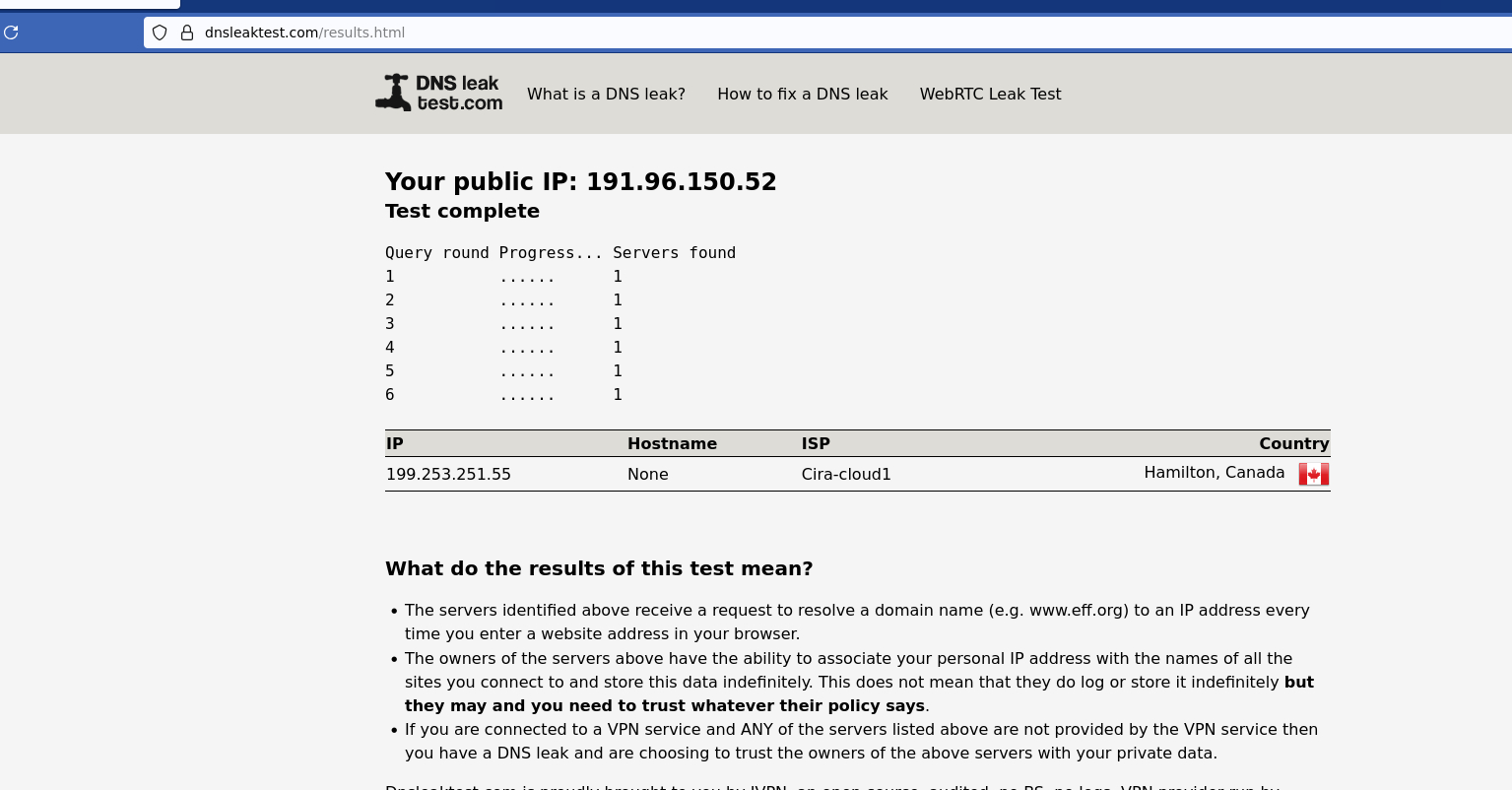
Windows Desktop IE Browswer
yet all are behind the same firewall.. this is probably why i cant seem to figure out why am i truly leaking or what not but seems the windows desktop says i am
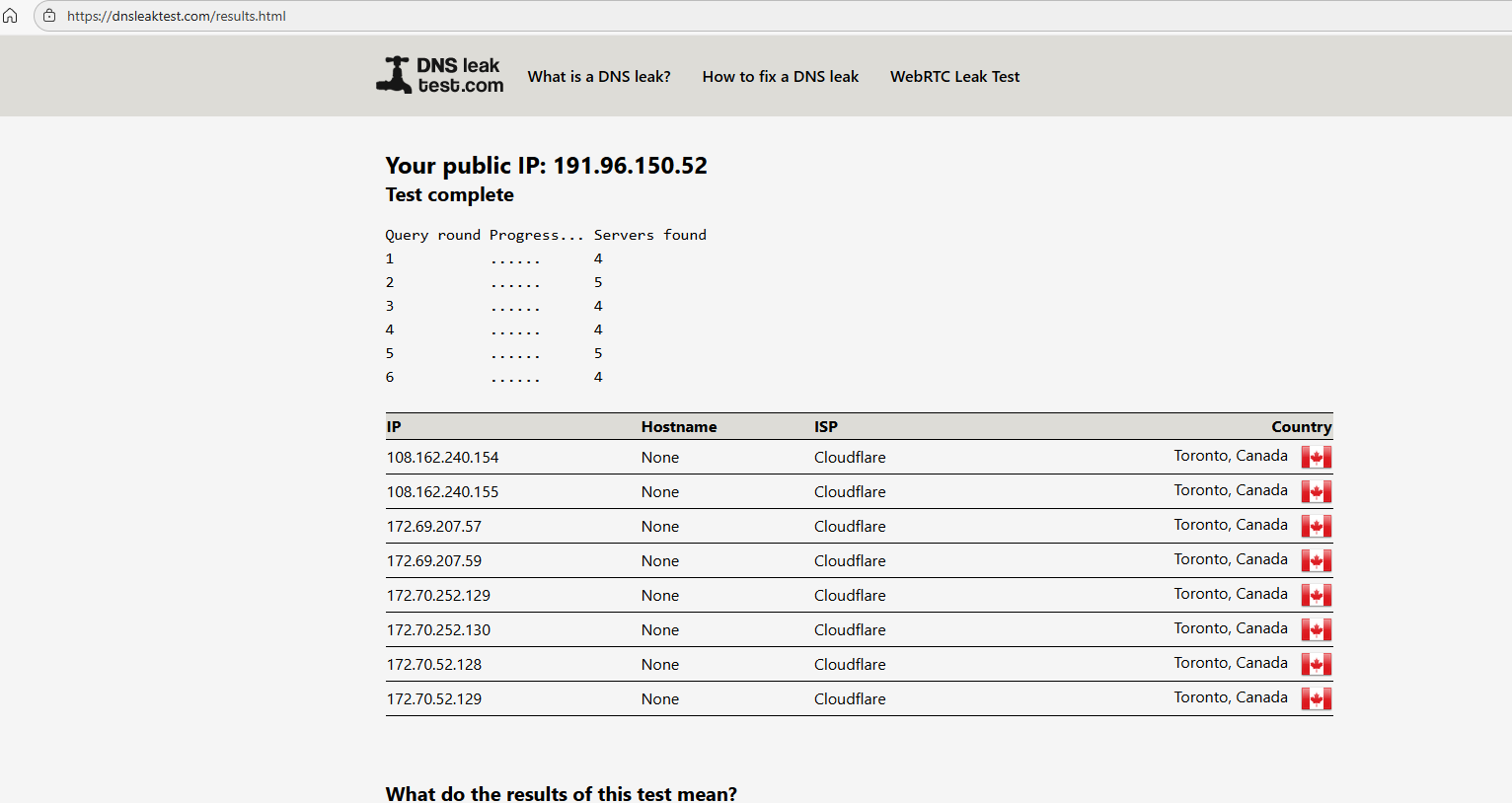
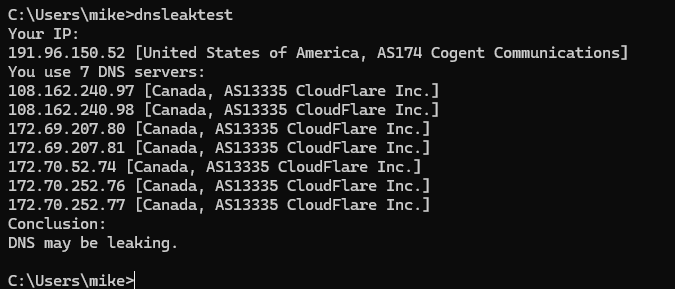
here is the github dnsleaktest you download and run on windows or linux here is the same desktop
so i been confused for months and thats probably why this question form i posted has gone on forever cuz i truly never figured whats going on or how to make wan lan ips and vpn lan ips seperated and secure.. and the videos and articles never address this..
and i confused why my desktop pc is always pulling dns even when it should be pulling vpn
and when you run the dnsleak.com website for PIA leak test.. on the 2 Firefox docker.. they tell you its leaking.. so its not even working like they supposed to be.. cuz it throws a whole bunch of ips of the cloudflare
so dnsleak.com sees the cloudflare ips the dnsleaktest.com doesnt see that but sees the cira one but should be i guess teksavy
so ive never figured out this rolling headache lol
-
There are many ways you could set this up. The way I outlined above is simplest for avoiding 'dns leaks' but you can do it other ways. Including some that include using the lancache.
Does the Lancache have it's own DNS server?
When you see a DNS leak reported it's because the client is using a DNS server that's resolving from an IP address local to the WAN and not the VPN. So that means either Unbound sending queries out of the WAN or forwarding to local servers like the ISP. So if you are going to have VPN client devices use Unbound in pfSense it must send queries over the VPN only. So either set Unbound to use the VPN interfaces for outbound queries or forwarding to the VPN DNS servers only.
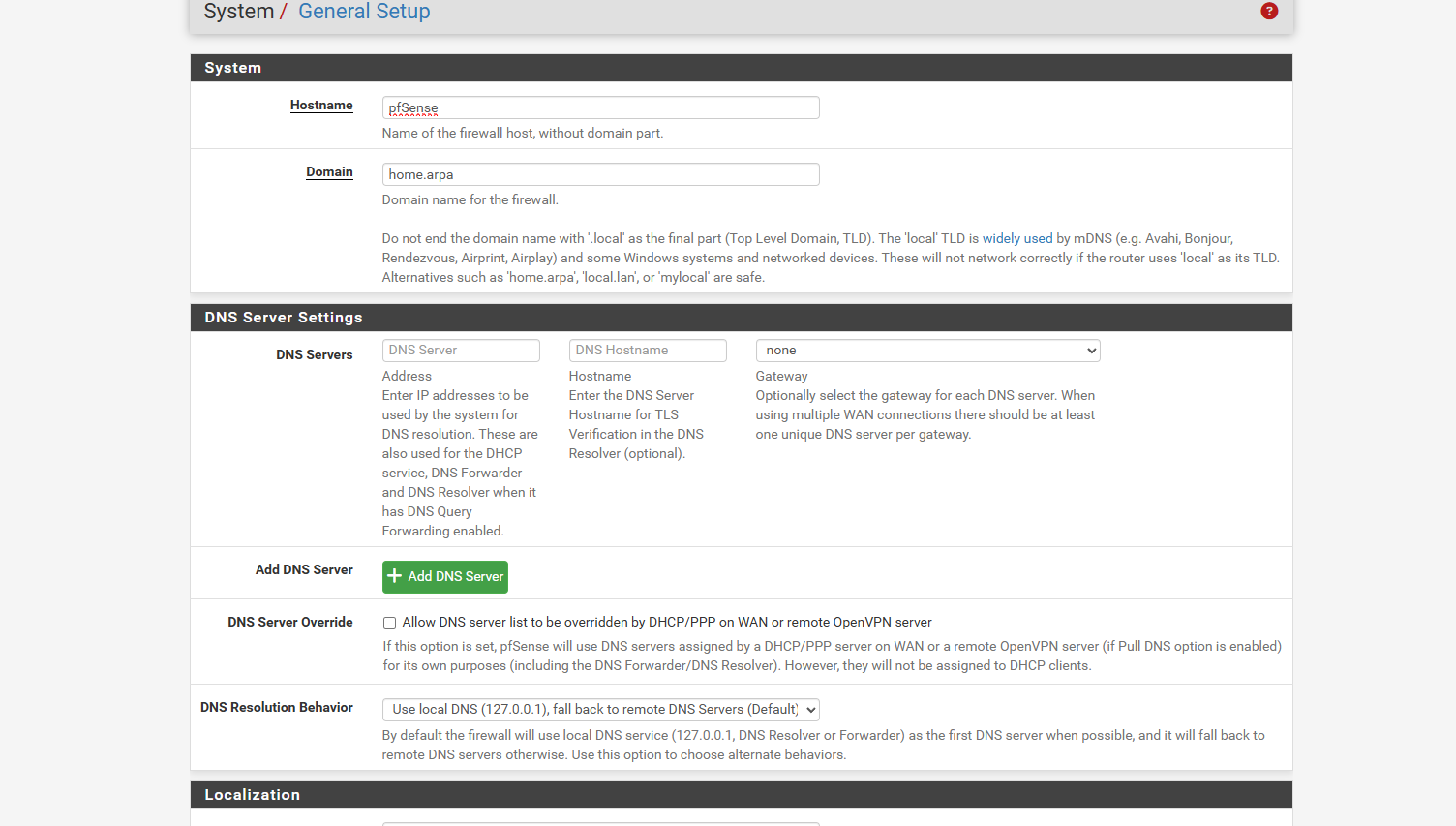
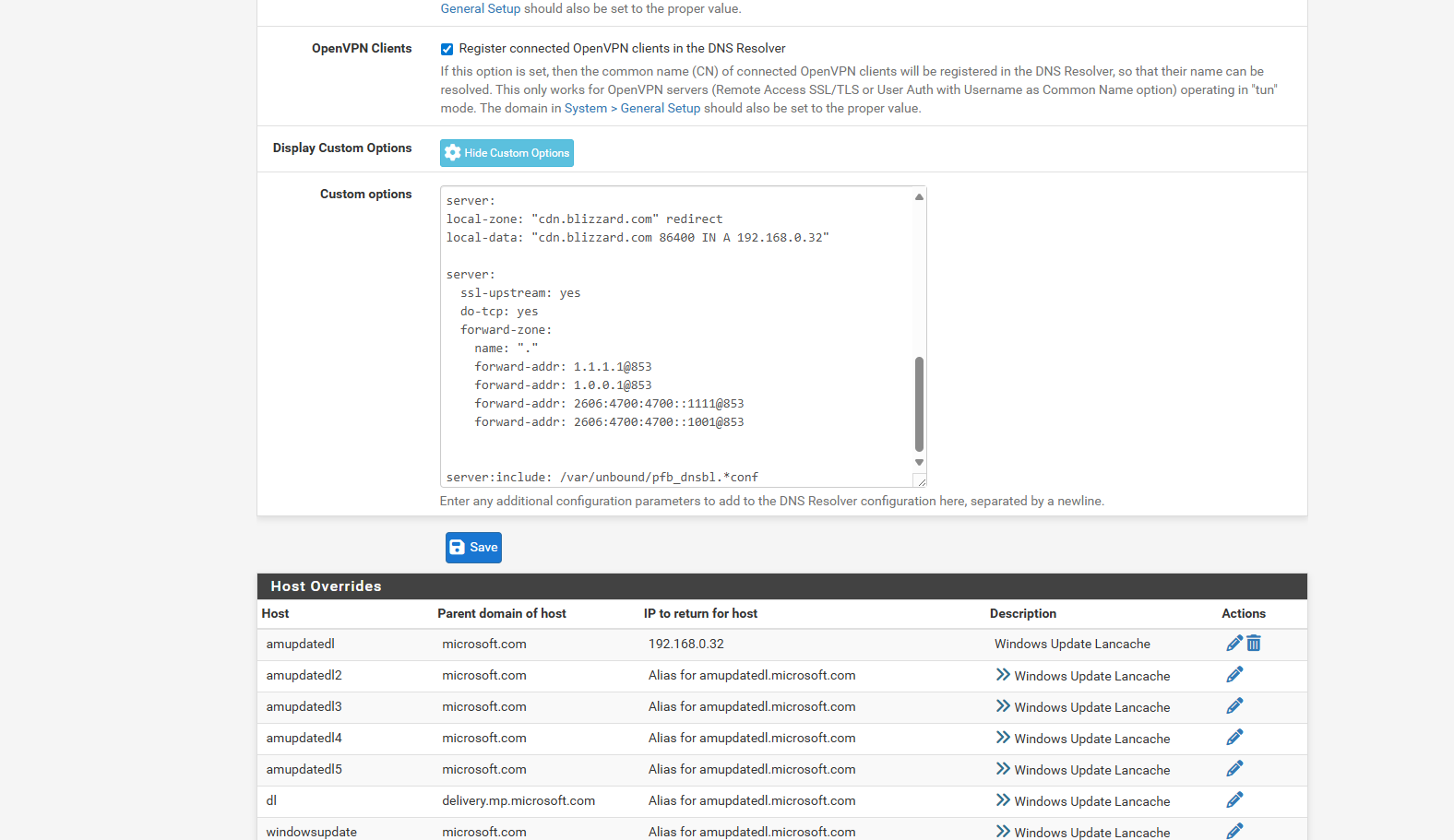
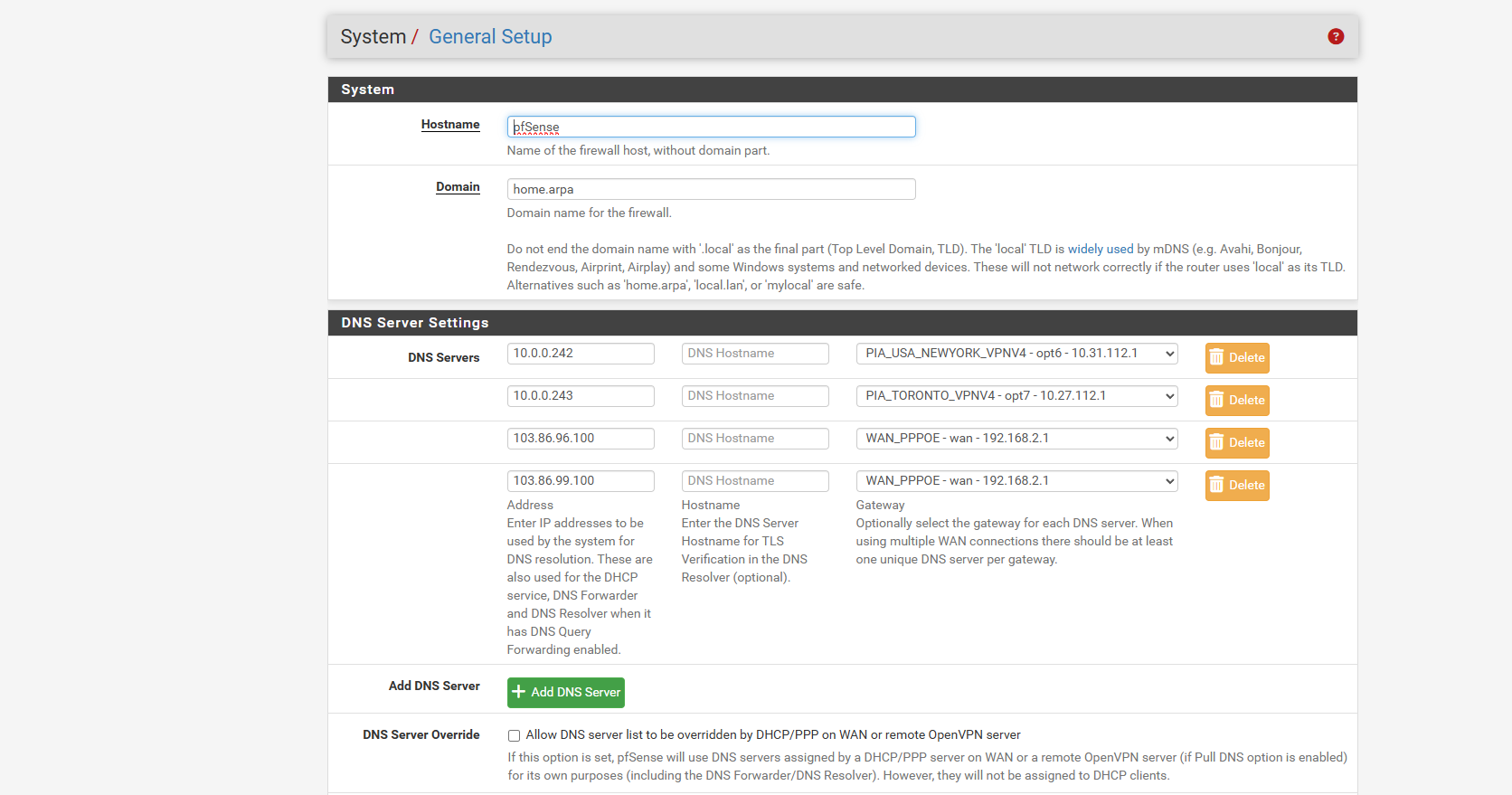
By default pfSense will be passed DNS servers to use by the ISP and adds them to the list in General Setup. You can disable that though by unsetting
DNS Server Override. -
@stephenw10 ok i understand i not sure how to do all that but i am learning things as i go too. learning experience and the simplets way is still getting cloudflare on a desktop pc even though its all going out the vpn and i guess that options i have is to keep the wan alive.. least that what i figured it does
so for lancache ya it has an upstream ip address i used 10.0.0.241 as the upstream
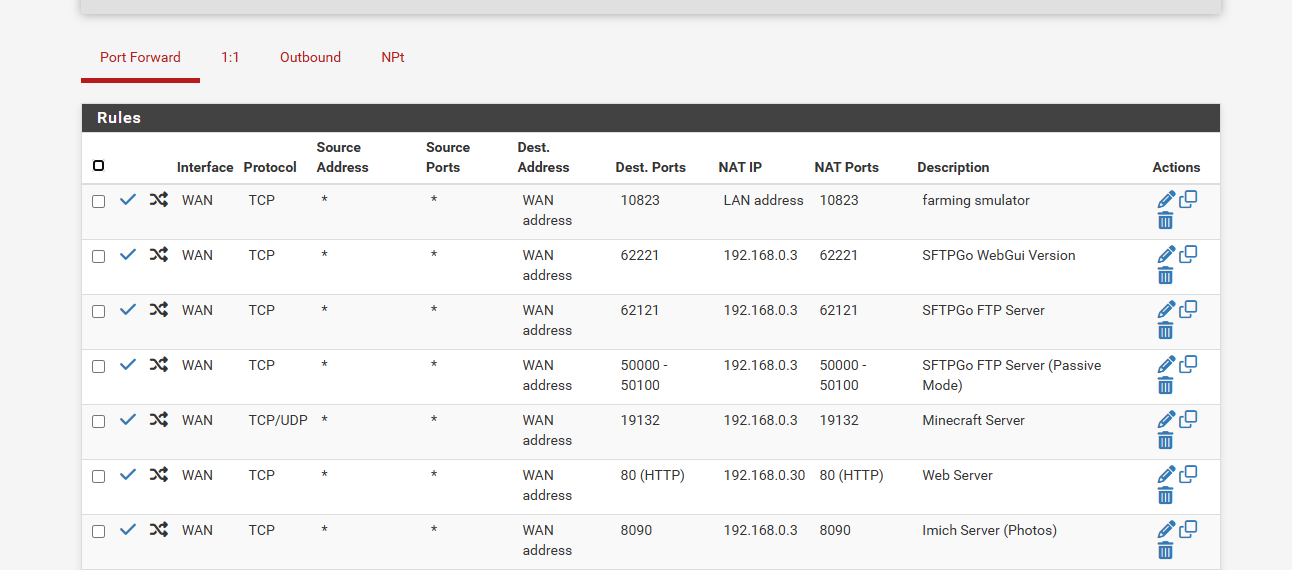
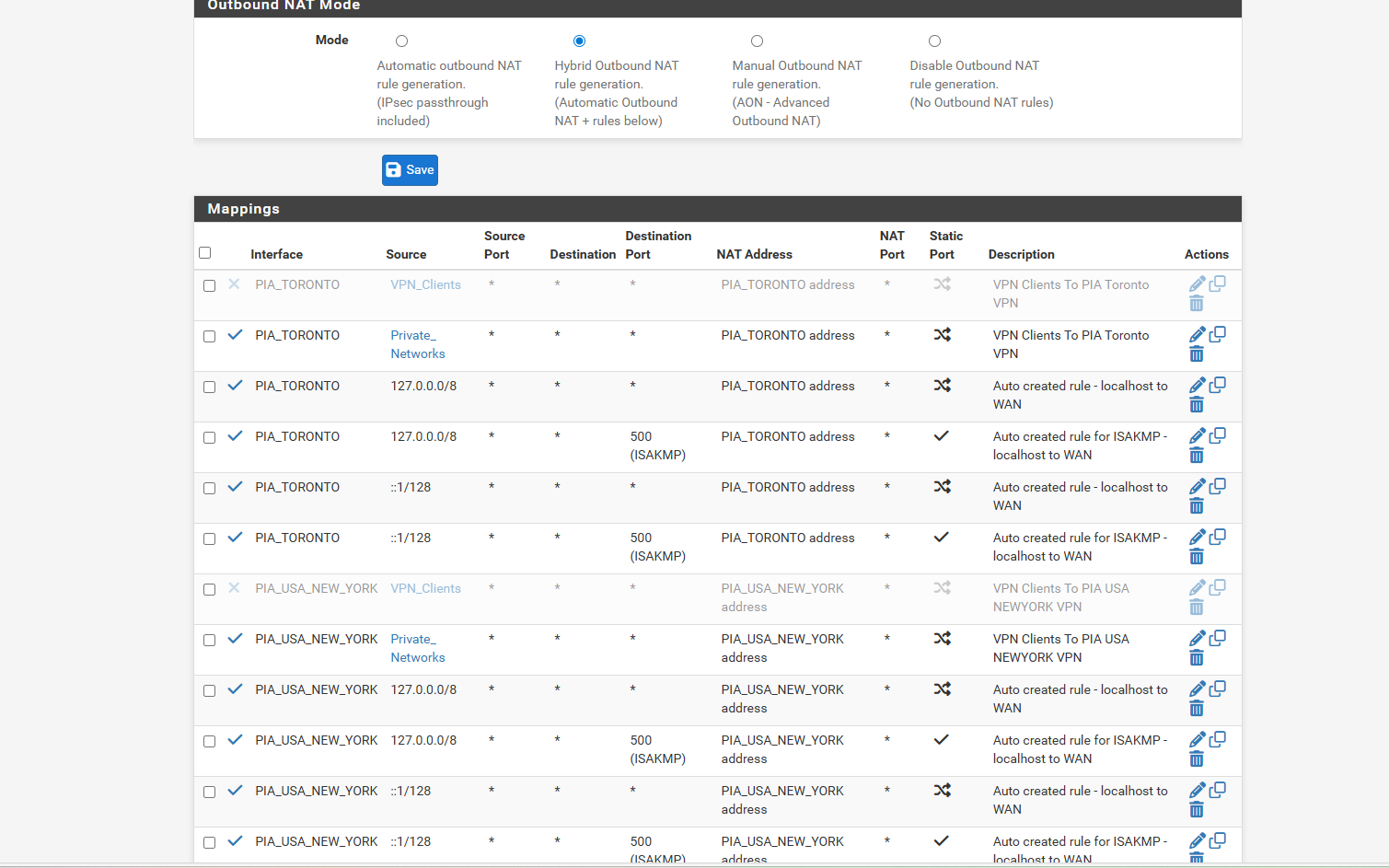
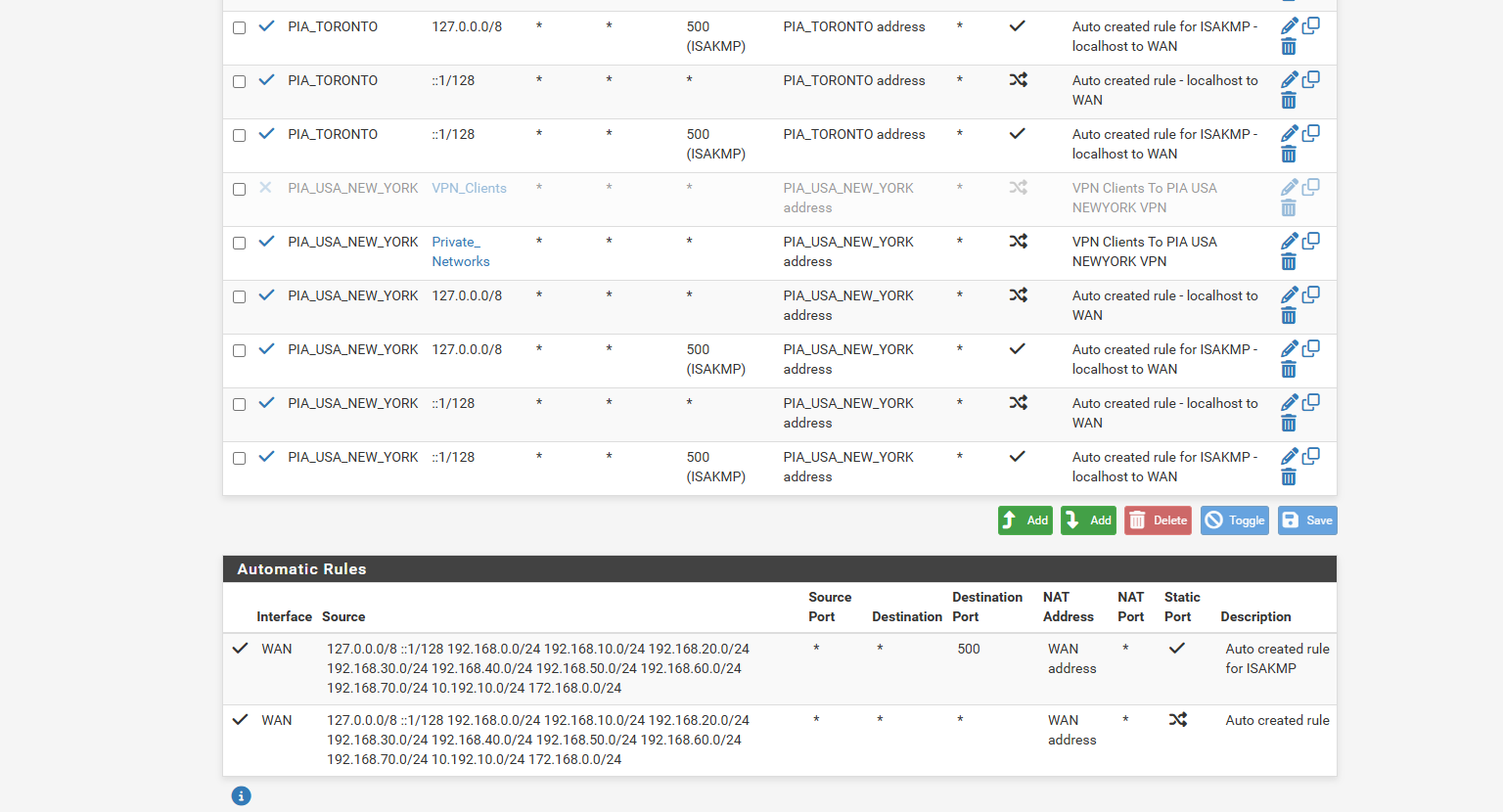
and the lancache is 192.168.0.32i had to re read what you wrote to try to understand things.. stupid dislexia and learning disabilities.. but also here is the NAT i did it in hybrid mode.. i also used to have nat to only go out vpn clients.. but disabled and did entire networks so all the interfaces get WAN and VPN as i saw another video doing that too.. not sure what one is the right way.. and seemed when i was with NordVPN how ever it worked.. it worked better then PIA.. i only went PIA cuz it was cheaper.. but it seems to been more issues as i didnt have these leak issues with the nordvpn that i do with the pia... as i even set it to all all inbound and outbound
so basiclly your saying when you want to use VPN and No VPN Clients... you gotta set All Inbound and just the 2 VPN for outbound..
and as for the Dns Server Override.. ya thats been unchecked for a long time.. havent checked that button
and i guess i confused cuz the videos of these people that setup the vpn and no vpn for pia.. dont touch the dns resolver.. so they leave it at default all/all inbound and outbound..
so thats where i getting also confused they dont talk about it ever.. or ever talk about dns leakage
only about the no wan egress kill switch.but currently my setup above is it only sends out the VPN and i get the cloudflare on my desktop pc but not the others... but i going to try a reboot of windows see if that does anything..
and this is my nat and general settings
-
if you happen to have any screen shots how to configure it to be secure even if i have split network
and better routing as these videos arent showing how to stop leaking or touch the dns resolver -
@stephenw10 and i know your too busy to watch or skim videos
but these were the videos i followed where i did like that but they dont talk about leakage or dns resolver.. and i never get there resultssyncbricks 1
Lawerence Systemsand i commented on there youtube videos about the setups not talking about dns leakage or dns resolver.. but they too busy to reply either
-
@comet424 said in Port Forwarding stopped working after upgrading to 2.8.0:
and i confused why my desktop pc is always pulling dns even when it should be pulling vpn
Normally, your PC, the OS, pulls the DNS from the gateway, which is pfSense.
pfSense centralized all local network ( your LAN devices ) DNS requests, and resolves from there.
Resolving means : it uses root DNS server, a TLD DNS server and a domain name server to obtain a DNS answer.
Or : Plan B : you forward to for example 1.1.1.1 : now the resolver send all traffic to this DNS resolver (= 1.1.1.1).
The resolver uses the outgoing connection, also called WAN.
Or, you could have two WAN's : the one going to your ISP, and a VPN-WAN connection. You could inform the resolver to forward to 1.1.1.1 over the VPN connection.If you use this last solution, you still leak DNS info to .... 1.1.1.1 ^^
When I see the result of dos command "dnsleaktest" shown above it says your DNS leaks to ...
the 7 DNS Cloudflare servers you have specified yourself (?).
So, is it really leaking ? It does what you asked it to do.I know, more questions then answer.
-
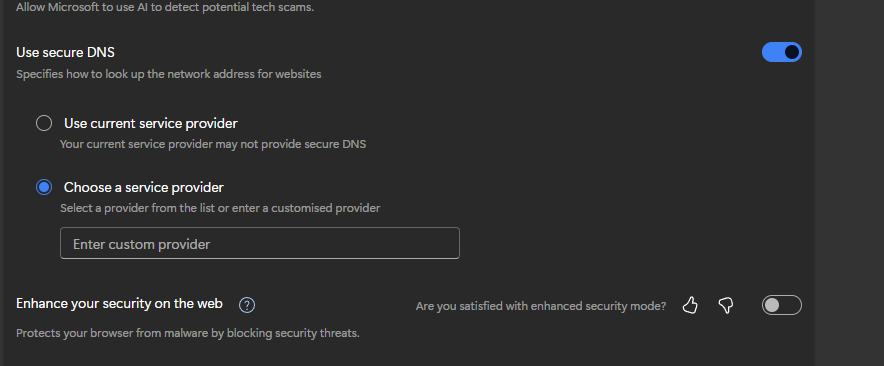
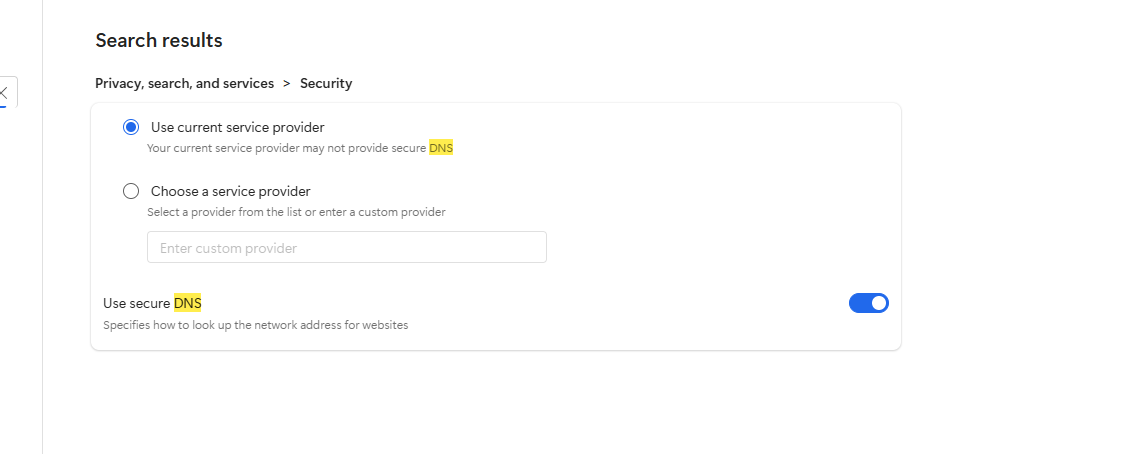
Maybe you are using DOH on your windows IE browser? Change it to static IP and add your DNS server IP.
-
@MoonKnight said in Port Forwarding stopped working after upgrading to 2.8.0:
Maybe you are using DOH on your windows IE browser?
True. Forgot about that one.
On any device, locally installed software can use the 'system DNS' (the one you see when typing ipconfig /all)
or
it can use any DNS other DNS is choses to use.These days, afaik, most application (browers and others) use their 'own' DNS, totally bypassing the pfSense Resolver/DNS.
They (the browser's author) say : for your own security, and that(s not false, but mostly because they want your DNS traffic as it has a value (for them).
This traffic will flows encrypt through pfSense to whatever destination it chose to use and you can't do anything about it.
Remember : this is TLS traffic so you can't route it to somewhere else.
I would consider this also as DNS leaking .... -
so those dnsleaktest from the command line.. is from wherever..
so first
i have the Inbound to All Outbound to 2 PIA
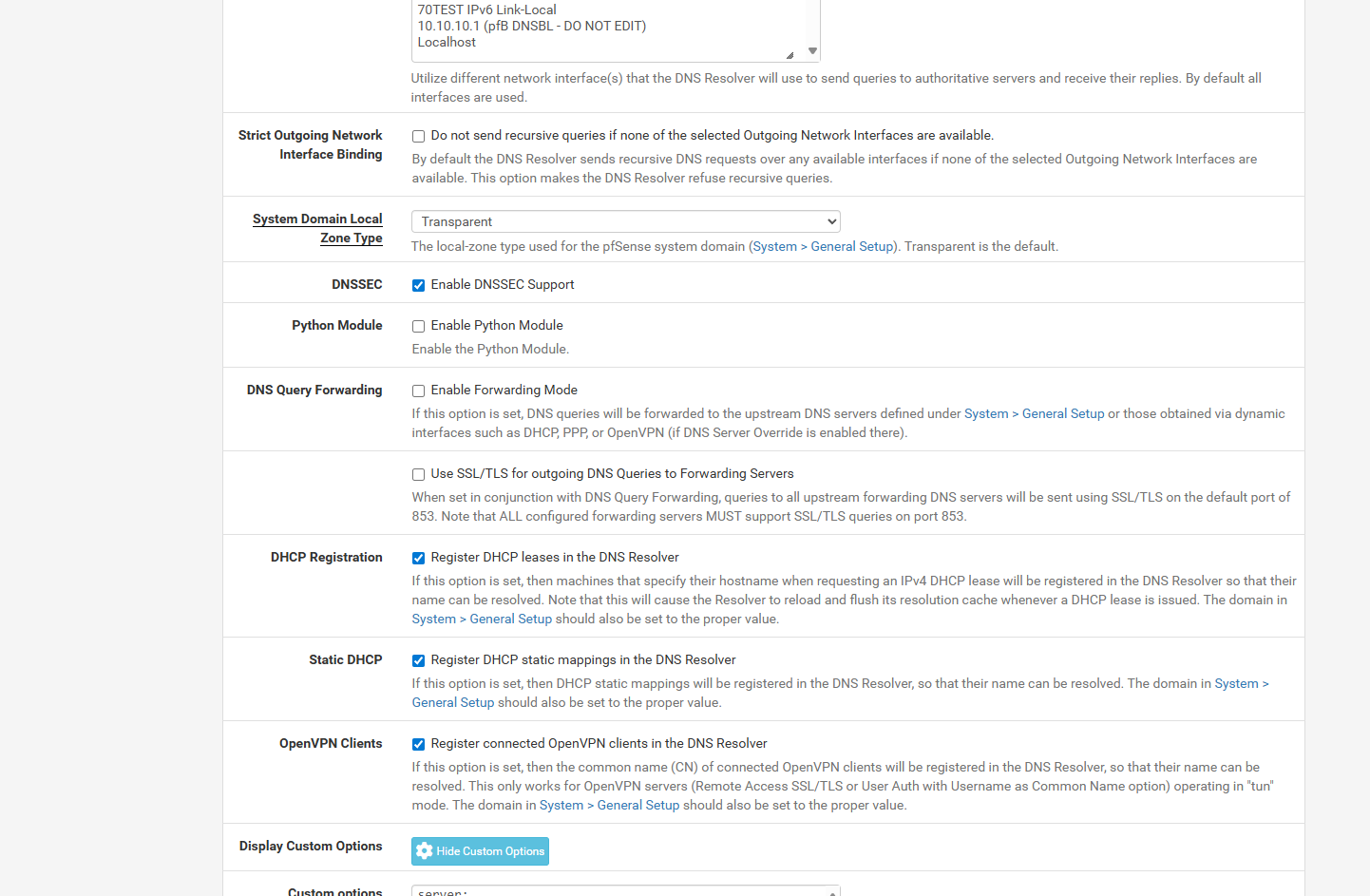
the dns resolver custom options i addedserver: ssl-upstream: yes do-tcp: yes forward-zone: name: "." forward-addr: 1.1.1.1@853 forward-addr: 1.0.0.1@853 forward-addr: 2606:4700:4700::1111@853 forward-addr: 2606:4700:4700::1001@853as per serval setups i guessing you do that for when pia goes down least WAN will stay up.. as i run in the problem if i dont set an ip address in at least general setup when i have it set for just PIA outbound when the pia vpn goes down it can no longer resolve WAN,, and WAN no vpn clients then loose the internet too so does pfsense itself
so i even removed the resveration of my deskop pc from the dhcp server so it just get a random port and still pulls cloudflare... i then rebooted all my network switchs in case they held any info... and that didnt help
i even dual booted from Windows 11 to Windows 10 to test.. and command line dnsleak test is still pulling damn cloudflare.. i tried looking through all the settings in pfsense incase i had something configure.. but it doesnt matter if i remove that custom options then i get my isp on my desktop pc which is behind the vpn or cira-cloud.. like u bang your head off this
and
resolv-retry infinite; persist-key; persist-tun; remote-cert-tls server; reneg-sec 0; auth-retry interact; dhcp-option DNS 10.0.0.242;thats the custom setting for PIA vpn now some offer the semi colon others dont add it i dunno if it makes a difference..
i had to look up with DOH in windows was
ii also get the cloudflare on Oprea and Google Chrome and command line dnsleaktest
and since pia customer service not willing to help just tells you find help else where basiclly it makes it also frustrating
as ever i switched from nordvpn to pia i have nothing but this leaking issue.. but frustrated for sure... i going to try and windows VM and see if i getting same cloudflare and not the vpnand here is the dns setting in microsoft edge
-
oh and seems now my firefox dockers now pull cloudflare behind the vpn
i guessing its because of that custom options... after i did a server reboot.. the firefoxs are now getting like 20 cloudflare and not just vpnthis is my current dns resolver
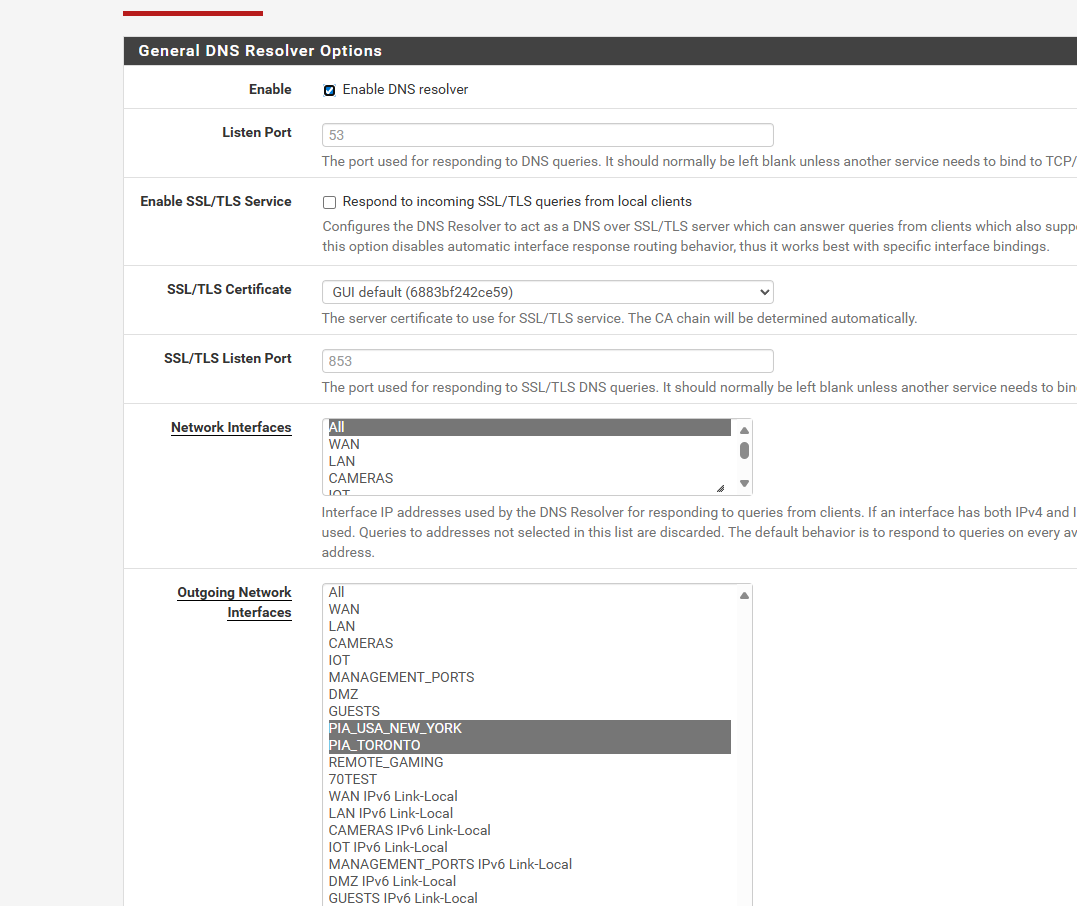
-
i cant find the 2 articles now that showed those server options
but here this article i read
https://undergroundmod.com/2023/07/15/private-internet-access-vpn-on-pfsense-last-updated-08-2023/talks about this
Important DNS Note If you are not using DNS over TLS to a trusted, privacy oriented DNS Resolver like CloudFlare’s 1.1.1.1, then you will leak your IP over DNS and this could be a problem To get around this, you should hard code PIA’s DNS servers on the system you are putting over the VPN. The DNS servers are 209.222.18.222 and 209.222.18.218 Be sure to check if your DNS requests are leaking your normal public IP: https://www.dnsleaktest.com/ Setting these DNS server will probably affect local DNS resolution, so you should really just use DNS over TLS… https://www.netgate.com/blog/dns-over-tls-with-pfsense.html You could create some NAT rules to intercept DNS requests and force them elsewhere, but it’s more work than just using DNS over TLS, which you REALLY should be doing anyway… Thats it!not 100% sure what that ment but i just tried enabling the Enable SSL/TLS Service in the dns resolver
i get confused cuz there isnt 1 straight setup for no leaking no issues lol makes you wanna drink
-
if you guys got screen shots how PIA or any VPN should be setup on the LAN like with 192.168.0.0 like i have grayed out . no_vpn_clients and vpn_clients
and what the dns resolver NAT should look like.. so i can just duplicate it.. so there is 0 dns leakage.. as these google searches arent helpingand or should i make a new post ask for anyone that has PIA and NonVPN Clients Have Screen shots for a secure network? i was hoping when i orginalyl started thread.. someone with PIA had this setup and secured and could supply screen shots..
if i ever get this solved. i going to make a thread with the right procedures so someone like me doesnt go through these headaches
-
OK adding those custom options in Unbound is forwarding all queries to Cloudflare. No matter what else you have set in the Unbound setup.
But without any DNS servers set in General setup then pfSense itself can only use Unbound. If that is configured to only use the VPN interfaces for outbound queries then it cannot resolve anything until the VPNs connect and that's a problem if the VPN servers are defined as an FQDN instead of an IP.
-
@stephenw10 so i running in circles..
currently this is what i got i took out those custom options
i can get it to say not leaking if i use 103 ip address which is a nordvpn dns on the WAN
but if i use 1.1.1.1 then it leaks like a ship with 20 holes in it.. i getting frustrated.. and this article at the bottom tells you to use dns over ttls.. and use like 1.1.1.1 for a secure dns leak free but its not making sense and it leaks using 1.1.1.1
this is the article
https://undergroundmod.com/2023/07/15/private-internet-access-vpn-on-pfsense-last-updated-08-2023/this is the bottom not.. and those ips dont work
Now we have done that, you should be done. Everything on those IP’s in the alias will go over the VPN. If the VPN disconnects, no internet traffic will pass and as long as the IP doesn’t change, traffic CAN NOT go over the normal gateway Important DNS Note If you are not using DNS over TLS to a trusted, privacy oriented DNS Resolver like CloudFlare’s 1.1.1.1, then you will leak your IP over DNS and this could be a problem To get around this, you should hard code PIA’s DNS servers on the system you are putting over the VPN. The DNS servers are 209.222.18.222 and 209.222.18.218 Be sure to check if your DNS requests are leaking your normal public IP: https://www.dnsleaktest.com/ Setting these DNS server will probably affect local DNS resolution, so you should really just use DNS over TLS… https://www.netgate.com/blog/dns-over-tls-with-pfsense.html You could create some NAT rules to intercept DNS requests and force them elsewhere, but it’s more work than just using DNS over TLS, which you REALLY should be doing anyway… Thats it!and here is my current setup what am i doing wrong
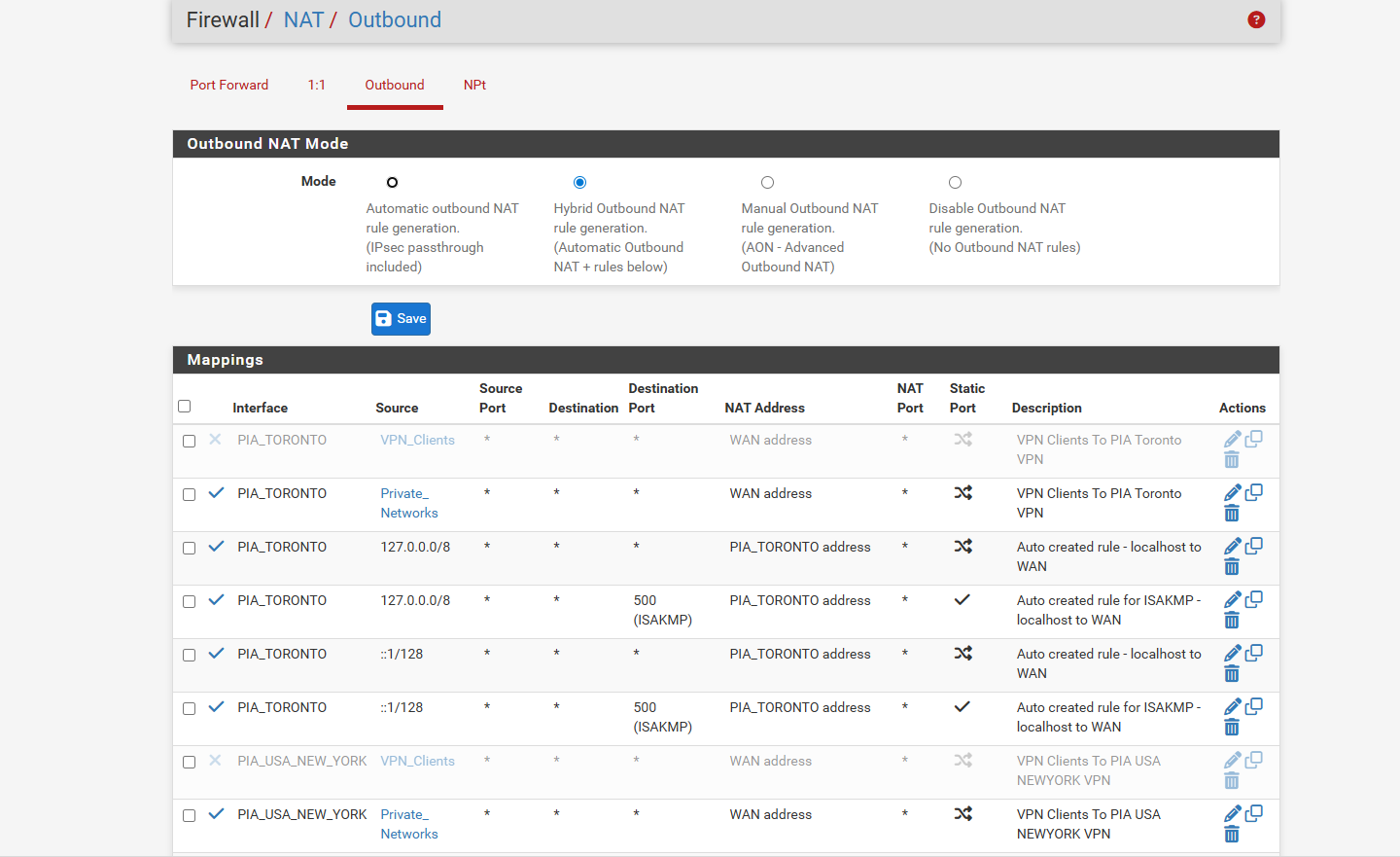
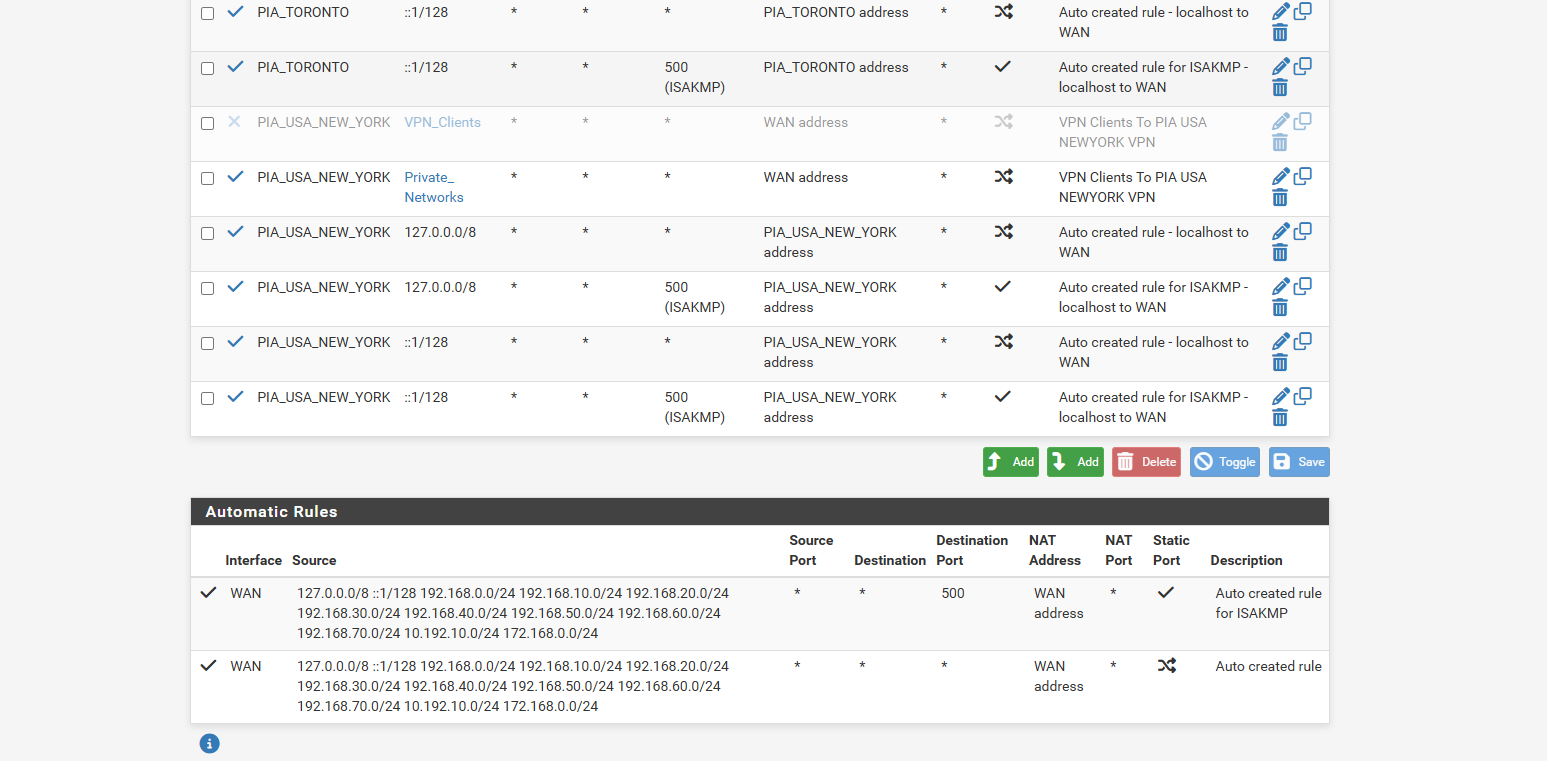
and the nat page ive done wan address and PIA address cuz in the 2 videos they go both directions one says use the wan address and the other says use the pia address
if you could provide pictures what i doing wrong would be good i know you probbably getting frustrated helping me on all this -
What exactly are you counting as a leak test failure?
If you're forwarding requests to Cloudflare then DNS tests will always show Cloudflare. It just might be local servers if the query isn't over the VPN.
-
@stephenw10 well when i run website dnsleak.com or dnsleaktest.com and it shows more then just the piavpn dns server thats what i consider leaking..
that the wan clients should only get 1.1.1.1 dns and all vpn clients should get the 10.0.0.242 say and that the 1.1.1.1 should never show up on any of the vpn clients when i run dnsleaktest.com
and then dnsleak.com keeps saying your leaking dns
and using the nordvpn 103.x.x.x failed providing dns after a few days.. i could ping from the pfsense but not from the windows..
i did google for not logging dns' and ai generated said 1.1.1.1 1.0.0.1. and 9.9.9.9 are non logging non data keeping dns
so then that should be safe right to use on the wan.. as i been trying so long to keep everything seperate and make the dnsleaktest.com say its not leaking but i havent been able to -
but i guess i wrong to figure what is ok for dns leaking and what isnt for dns leaking i just tried to make sure the tests showed i wasnt leaking
-
Well if you are forwarding queries to Cloudflare over the VPN you will still see Cloudflare as the resolver. It will just be an anycast endpoint local to the VPN server.
-
@stephenw10 and what is anycast? i thought using the cloudflare was bad cuz i tried to make sure 1 dns for wan clients and 1 dns for the vpn but its like its just not possible to have it split right...
and seems cloudflare is vpn safe as i googled and found this site
https://bitlaunch.io/blog/the-best-dns-servers-for-privacy/i was just trying to make it secure as possible and pia doesnt even reply ever might be ok service just really bad customer service