Newbie question about LAN To WAN
-
I got double NAT situation. My PF sense setup is not routing traffic between LAN <> WAN (both direction)
ie. machine on 192.168.0.0/24 WAN can't see machines on 172.100.0.0/24 LAN. vice versa
LAN Net can ping to WAN static IP address though.
Could anyone help me please
-
Why would they, that is the whole point of a firewall ;)
Also 172.100 is that a typo? Are you running public space on your lan? The rfc1918 172 space is 172.16-31.x.x
If you want to access stuff from your wan into your lan you would have to port forward. To be honest there should not be any boxes on your "wan" even in a double nat setup where you can not put your isp device into bridge mode so that pfsense gets a public on its wan. This network should be a transit network and no hosts should really be on it in a typical setup.
Why do you want/have devices on this 192.168 network (pfsense wan)?
-
Thanks so much in responding my question Johnpoz. Could you please see my answers in bold.
Why would they, that is the whole point of a firewall ;)
Yes, agreed. In my environment , Pfsense is purely being used for OPEN VPN connection.Also 172.100 is that a typo? Are you running public space on your lan? The rfc1918 172 space is 172.16-31.x.x
**Oh.o.. stuipid mistake. :-[ :-[ DHCP was configured like that. I will change it to private IP 172.16/24 range. Thanks for pointing that out.
[/b]If you want to access stuff from your wan into your lan you would have to port forward.
I tried a few port forwarding WAN net <> LAN net etc, doesn't work. Would you mind showing me example how to.To be honest there should not be any boxes on your "wan" even in a double nat setup where you can not put your isp device into bridge mode so that pfsense gets a public on its wan. This network should be a transit network and no hosts should really be on it in a typical setup.
Again agreed but I have another hardware VPN box Cisco ASA5505 ( I don't have access to control panel) that connect to another remote site. Sorry to confuse you. I have two VPN in total.
Why do you want/have devices on this 192.168 network (pfsense wan)?
The remote user with 192.168.160/24 was previously configured to talk to machine on my network 192.168.170/24 through Cisco VPN box. Now we are adding PFsense behind Cisco VPN box to connect to 3rd remote site..Ideally I would like to be able to communicate both directions like below
Remote site 192.168.160/24 <–---Cisco VPN-----> My site 192.168.170/24 <---> PFSense FW <-----> 172.16/24 Pfsense LAN machines (is it even possible to do that?)** -
"PFsense behind Cisco VPN box to connect to 3rd remote site.."
What?
"Remote site 192.168.160/24 <–---Cisco VPN-----> My site 192.168.170/24 <---> PFSense FW <-----> 172.16/24 Pfsense LAN machines (is it even possible to do that?)"
As to possible have no idea?? Borked yeah that would be what I would say ;)
Dude draw up your networks and site and what you want to do and we can figure out best option. But connecting into a site via vpn, to then go to something behind another firewall that is also doing nat? Why??
As to how to port forward..
https://doc.pfsense.org/index.php/How_can_I_forward_ports_with_pfSense
https://doc.pfsense.org/index.php/Port_Forward_TroubleshootingI can tell you right now your vpn client trying to go to something behind pfsense would of failed unless you unchecked the block rfc1918 on your wan which is on by default.
-
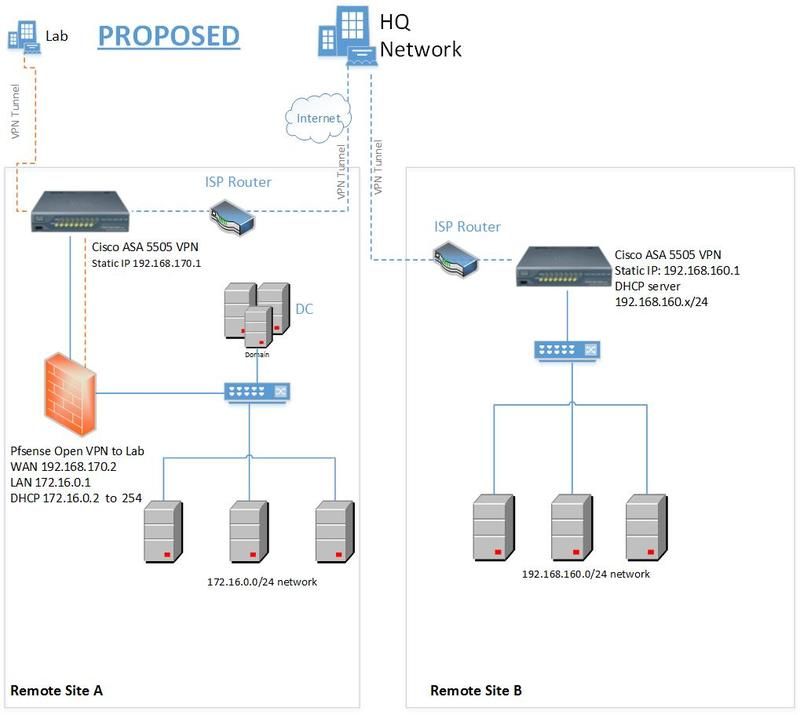
Sorry John. I am confused myself. Here is what I've just drawn up a diagram below to show what I'm trying to do. Probably the worst diagram you've ever seen. LOL.
The plan is all the machines on Site A to be able to access Lab machines as well as Site B machines.
Also Site B machines need to be able to access Site A and Lab vice versa (is it even possible?)
At present, without PfSense, Site B machines can authenticate to Site A's DC and access all resources.

-
any one please help.
-
why would you not just create a vpn with your asa to your lab?
Your site A machines gateway is what? Your asa or your isp router? Something in 172.16.0/24
How would they know to go down some tunnel you have created on some pfsense machine to some lab? Your trying to put your whole site A behind pfsense?? So there are no more machines on 192.168.170???
Yeah that drawing sucks ;)
Why does this lab not just create a vpn tunnel to your HQ network like your other sites?
-
why would you not just create a vpn with your asa to your lab? I don't have access to ASA box.
Your site A machines gateway is what? Your asa or your isp router? Something in 172.16.0/24 ASA are gateways.
How would they know to go down some tunnel you have created on some pfsense machine to some lab? Your trying to put your whole site A behind pfsense?? So there are no more machines on 192.168.170??? **Yes, I'm putting all machines behind pfsense. No more machine on 192.168.170. **
Yeah that drawing sucks ;) he he.. yep..
Why does this lab not just create a vpn tunnel to your HQ network like your other sites? That.. I don't know why.. sorry
-
You should be able to make client connections out from pfSense to Lab without needing access to the ASA. Unless they are blocking all but certain outgoing connections or being otherwise aggressive on outbound.
You will not be able to get a server running there without access to the ASA unless they are already forwarding a port to you from the outside that you can use instead. Preferably a UDP port.
Probably your best bet is to put pfSense at Lab and run the OpenVPN server there. Make 192.168.170.2 the OpenVPN client.
This seems like something that should be run by whomever is actually responsible for the security of these two sites though. Like the guy with the ASA credentials. Another IPsec tunnel from Lab with access to 192.168.170.0/24 seems like the way to go there.
-
No Problem accessing from Site A Pfsense 172.16. machines to Lab net at the moment as per Proposed Network diagram.
The problem is accessing from Site B to Site A Pfsense machines.
Am I correct in understanding your suggestion is to make OpenVPN client range 192.168.170 . Will this allow Site B 192.168.160 range to communicate with 172.16 range?
Sorry if it is a silly question.
-
For that you will probably have to add VIPs on pfSense WAN and 1:1 NAT then to the inside hosts and pass the traffic on pfSense WAN.
You might be able to get away with just 1:1 the whole /24 in that case.
Firewall, Virtual IPsType: Proxy ARP
Interface: WAN
Address Type: Network
Address(es): 192.168.170.0/24Firewall > NAT, 1:1
Interface: WAN
External subnet IP: 192.168.170.0/24
Internal IP: Network: 172.16.0.0/24
Destination: Not: Checked WAN addressOn WAN pass IPv4 port any source 192.168.160.0/24 dest 192.168.170.0/24
No idea what types of connections that NAT will break.
I am also unsure about the Not WAN address. Seems to make sense that you would need to bypass NAT for WAN address there.
-
Thank you. :) I will try it on Monday and report back to you guys.
-
In case it's not clear, they will still think they are talking to, say, 192.168.170.101 but they will really be going through NAT and talking to 172.16.0.101
-
Sorry. Being a bit thick here. So what shall I do now.
-
The same thing.