new pfSense install - immediate and numerous DoD (department of defense) "queries"? 255.255.255.255:68
-
This is my first post and first pfSense install
-fresh install of pfSense 2.4.3-RELEASE-p1
-bare metal (not virtualized)
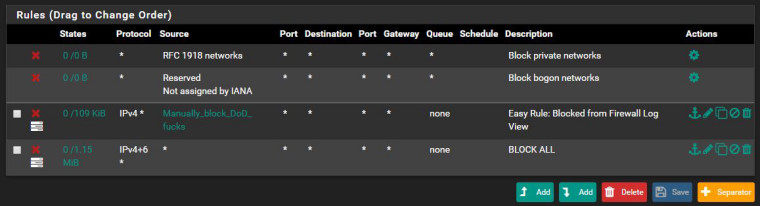
-default firewall rules PLUS
-added rule for block all WAN traffic, ip4 and ip6, all protocols, all sources
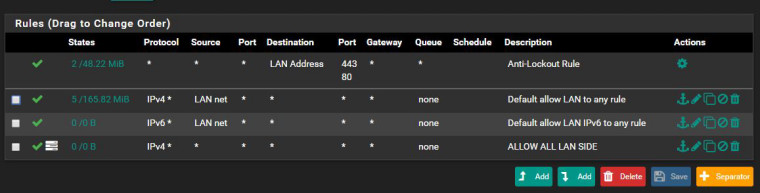
-added rule to allow all LAN traffic, ip4 and ip6, all protocols, all sources
-IP PASSTHROUGH from ISP router and separate public IP from the rest of the network
-only 1 machine serviced through the pfSense box (for testing)From the time I first booted and started watching the firewall logs, I noticed I'm getting hit with traffic from all over, on various ports. I assume this has always been happening, due to botnets scanning thousands of IP addresses for open port, but the one that caught my eye was this.
Jun 10 16:31:19 WAN 11.0.160.1:67 255.255.255.255:68 UDP
Jun 10 16:31:11 WAN 11.0.160.1:67 255.255.255.255:68 UDP
Jun 10 16:31:07 WAN 11.0.160.1:67 255.255.255.255:68 UDPThis shows the source and destination and the protocol. This is a blocked log entry in the firewall logs.
11.0.160.1 resolves to US DoD Network Information center in Columbus Ohio.
Umm..What?
This also Irks me because theres a Harvey Birdman episode called "blackwatch plaid" that predicts this .. except its cellular conversations and the monitoring station is in Iowa.
But alas ... WTF?
-
Draw how you have everything connected (Network Diagram)
Post screenshot of your FW Rules (WAN/LAN)
-
Internet coax -> ISP Modem/router -> IP PASSTHROUGH enabled for specific Ethernet port running to pfSense box (by pass internal routing) -> pfSence hardware (1u server) 2 seperate nics (one in one out) -> switch -> computer (only one on this switch)
-
That’s DHCP!
-
@xanadu said in new pfSense install - immediate and numerous DoD (department of defense) "queries"? 255.255.255.255:68:
-added rule for block all WAN traffic, ip4 and ip6, all protocols, all sources
Pointless - where did you add this.. Since out of the box all inbound traffic to the wan is blocked.
-added rule to allow all LAN traffic, ip4 and ip6, all protocols, all sources
Again pointless since out of the box lan rules are any any..
To your 11.x.x.x source for dhcp.. What is the wan of your pfsense actually connected too? Who is your ISP? Also what is this??
-IP PASSTHROUGH from ISP router and separate public IP from the rest of the network
As asked please post your rules... Out of the box you install pfsense and it will work.. There is no need for these rules you have added.
-
Firewall -> Rules -> Add
Block all sourcesWatched countless videos for initial setup that suggested to manually add a "block all" rule to WAN as a general rule of thumb.
Same process but for LAN traffic and "Pass" all traffic for the rule.
WAN of pfSence is connected to my cable modem-router. You don't need my ISP.
Ip Passthrough is how the modem-router bypassess the internal networking and provides a 2nd public ip to whatever device is connected to whatever ethernet port (eth port 2 as it is). So my pfSence box has an unmanaged external IP from my ISPS modem.
Rules were posted in my previous post.
-
@nogbadthebad I know its DHCP but why from the DoD?
-
Talk to your ISP and ask them, the destination is a broadcast address.
-
Not necessarily "is from DoD"
maybe your "ISP" is (mistakenly) using that network segment in "his" network
-
You would be surprised how often that happens to be honest... Company says oh we never need to go to xyz network.. We will just use it internally.
Also could just be some idiot user of the isp on the same layer 2 as you causing it.. Clearly its not a valid IP unless your ISP is the dod ;)
Do a packet capture on your wan, and load it into wireshark and you can see some more details and what the MAC address is of who is sending it.. Can tell from that what brand of device.
-
This post is deleted! -
ok ive captured some packets and opened them in wireshark
anything i should be looking for ? -
In the packet capture i notice Mac addresses with Arris and Cadant. Arris aquiried Cadant in like 2001 and they make cable modems and cable set top boxes.
-
http://www.dslreports.com/forum/r25679029-Why-is-my-first-hop-to-a-DoD-assigned-IP-address
http://www.dslreports.com/forum/r31748514-Connectivity-Why-is-comcast-xfinity-hosting-VoIP-servers-on-DOD-network
-
You have a cable modem I would take it... Yes arris and Cadant same and cable modem maker.
-
@johnpoz I dont have an Arris or a Cadant but yes I have a cable modem.
So take off my tinfoil hat then ?
My ISP basically said GTFO and won't even look into the DoD requests.
-
And what is your cable modem brand.. The nic is made arris/cadant ;)
Your tinfoil hat should never had been on - there is a shit ton of noise on the net.. Figuring out what it is the interesting fun stuff..
-
You cannot control what arrives on your WAN. That's why we run firewalls. All you can do is pass what you want and block the rest.
If you want to know why DHCP traffic from that address is out there you'll have to talk to your ISP.
pfSense is deny all traffic by default. If you put default deny rules in manually, expect to have to do things like manually pass IPsec too.
-
Ok I feel better. Thanks for putting my head on straight.
A question though. With all wan traffic blocked... why do services like teamviewer still work ?
-
because teamview creates a tunnel to their servers..