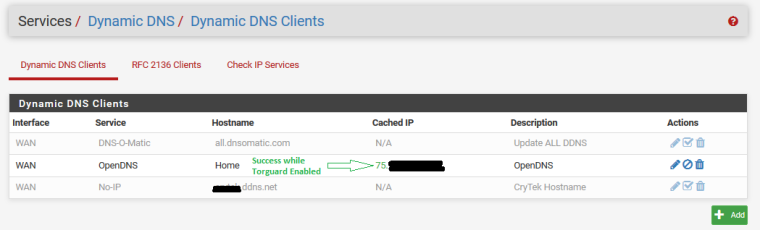
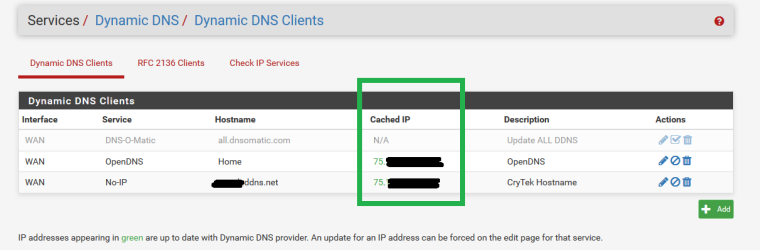
Dynamic DNS gets cached IP as VPN client IP
-
@teknikalcrysis said in Dynamic DNS gets cached IP as VPN client IP:
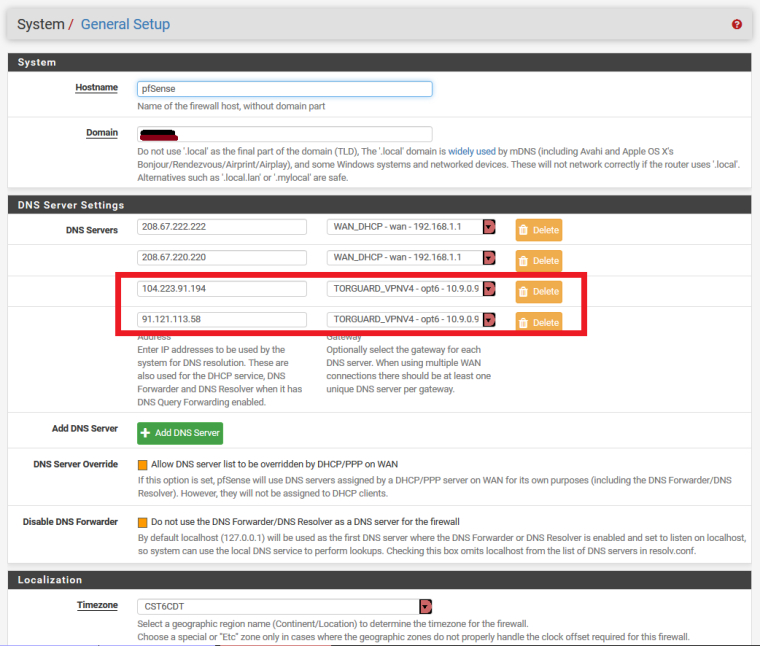
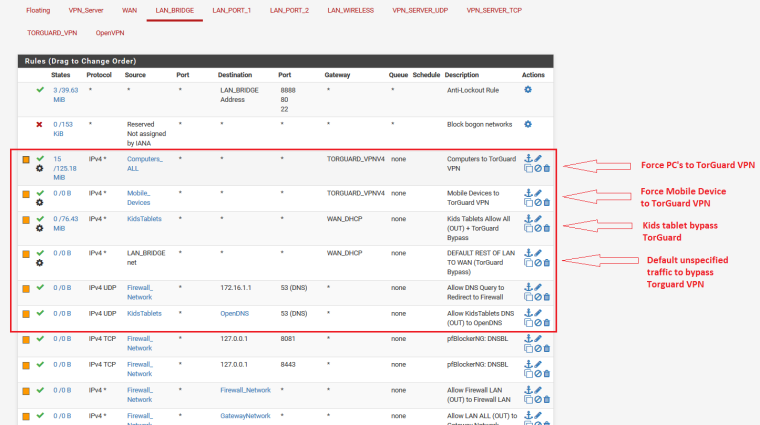
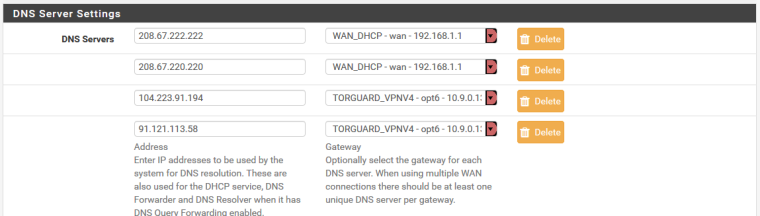
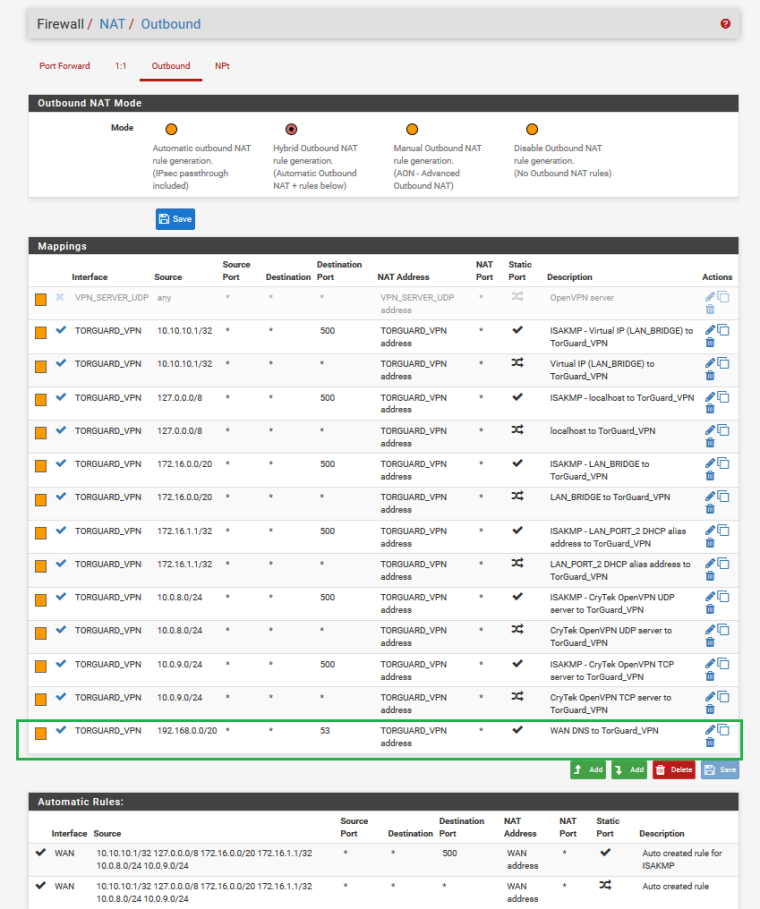
Here are some related settings
LAN Rules related to TorGuard
Have you tried a pass rule for source This Firewall(self) destination ?.ddns.net gateway WAN_DHCP
-
It won't matter because the dyndns session doesn't arrive into LAN where it can be policy routed. It is sourced from the firewall itself.
A dyndns client on the inside that updates that name and could be policy routed could perhaps solve the problem being seen when the VPN connection is active with def1 routes accepted.
-
@derelict said in Dynamic DNS gets cached IP as VPN client IP:
It won't matter because the dyndns session doesn't arrive into LAN where it can be policy routed. It is sourced from the firewall itself.
A dyndns client on the inside that updates that name and could be policy routed could perhaps solve the problem being seen when the VPN connection is active with def1 routes accepted.
Oops. How about outbound NAT on WAN interface source This Firewall(self) destination ?.ddns.net gateway WAN_DHCP?
It may be simpler just to run ddns client on the outside edge router if it has one.
-
Outbound NAT does not have anything to do with where traffic goes (routing). It only determines what NAT happens when traffic flows that way according to policy routing and the routing table.
-
@derelict said in Dynamic DNS gets cached IP as VPN client IP:
Outbound NAT does not have anything to do with where traffic goes (routing). It only determines what NAT happens when traffic flows that way according to policy routing and the routing table.
Oops again should be. How about outbound NAT on WAN interface source This Firewall(self) destination ?.ddns.net NAT address WAN address?
-
I have been trying a bit of everything...I was leaning on hope that there would be a way to create a rule somewhere that would route the dyndns traffic to a specific gateway like I have made with having my PC pushed trough the TorGuard VPN and simultaneously default traffic from the kids' tablets to bypass the TorGuard gateway and use the WAN directly...
While having the "Do Not Pull Routes" option checked in the TorGuard VPN config, I tried to make use of both the DNS Forwarder (dnsmasq) and DNS Resolver (Unbound) at the same time by creating a Virtual IP of 10.1.10.1 having Unbound listen on port 53 and dnsmasq listen on 5305 and then NAT Port-forward traffic DNS to the Virtual IP
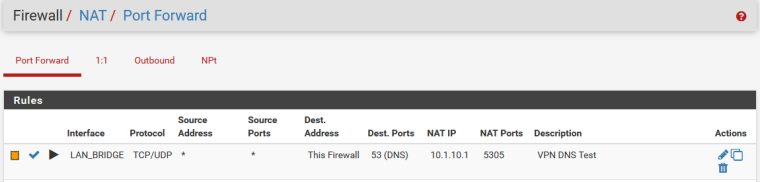
While this does make a change is the right direction by making use of the DNS server listed in General Setup
RESULT:
It tries to force all traffic to the DNS Forwarder (dnsmasq) even when the TorGuard VPN has been disabled/disconnected and it bypass the DNS Resolver (Unbound) all together
And then thing I dont like about using (dnsmasq) is that the DNSBL in pfBlockerNG is then circumvented is it not?I DID try to use the static DNS setting in the DHCP mapping as suggested, but it forces the PC to consistently use those specified DNS servers even when TorGuard has been disconnected, and again by having DHCP specify those servers, isn't DNSBL in pfBlockerNG getting bypassed at that point?
-
@gjaltemba said in Dynamic DNS gets cached IP as VPN client IP:
@derelict said in Dynamic DNS gets cached IP as VPN client IP:
Outbound NAT does not have anything to do with where traffic goes (routing). It only determines what NAT happens when traffic flows that way according to policy routing and the routing table.
Oops again should be. How about outbound NAT on WAN interface source This Firewall(self) destination ?.ddns.net NAT address WAN address?
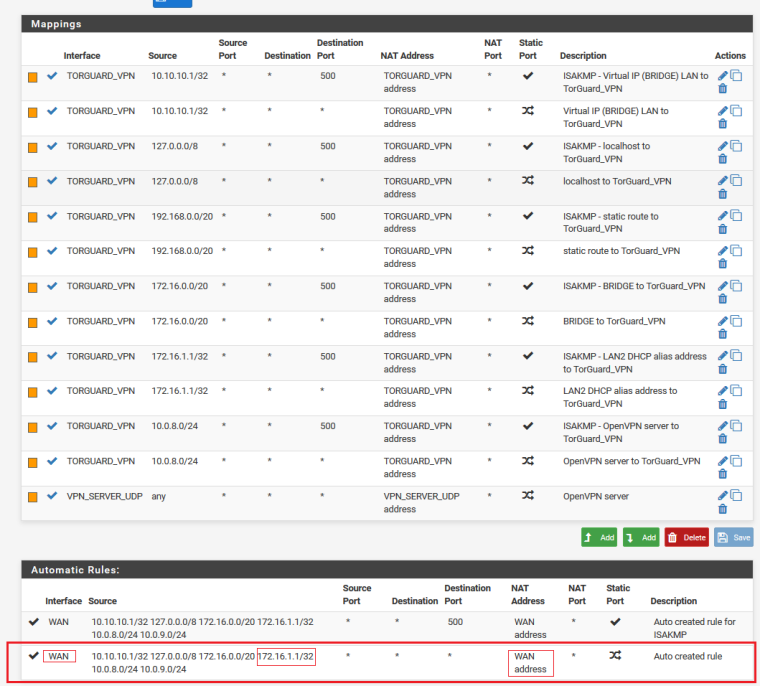
This has already been listed via autorule
-
Leave your original setup asis. Just put this at the top.
outbound NAT on WAN interface source This Firewall(self) destination ?.ddns.net NAT address WAN address
-
This post is deleted! -
@gjaltemba said in Dynamic DNS gets cached IP as VPN client IP:
Leave your original setup asis. Just put this at the top.
outbound NAT on WAN interface source This Firewall(self) destination ?.ddns.net NAT address WAN address
It wont let me type anything but an IP in the destination box
-
@gjaltemba Outbound NAT has ZERO to do with how traffic flows. If it is routed out the OpenVPN or policy routed out another interface, Outbound NAT will not change anything. It only determines what NAT occurs when traffic flows out an interface as the routing mechanism has already decided it should.
-
@derelict said in Dynamic DNS gets cached IP as VPN client IP:
@gjaltemba Outbound NAT has ZERO to do with how traffic flows. If it is routed out the OpenVPN or policy routed out another interface, Outbound NAT will not change anything. It only determines what NAT occurs when traffic flows our an interface as the routing mechanism has already decided it should.
I still think there is a way...I feel I am close... I went back and UNCHECKED the "Do Not Pull Routes" option in the TorGuard OpenVPN Client settings and I just disabled the following NAT OUTBOUND Mappings
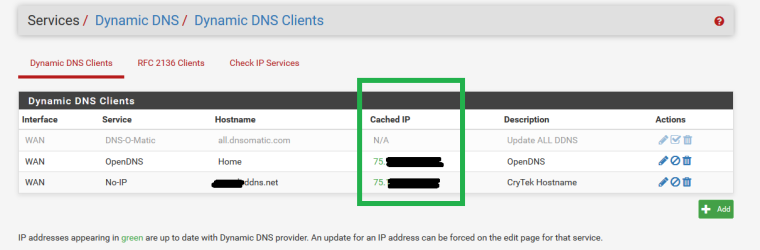
DynDNS Result is a SUCCESSFUL IP from ISP:
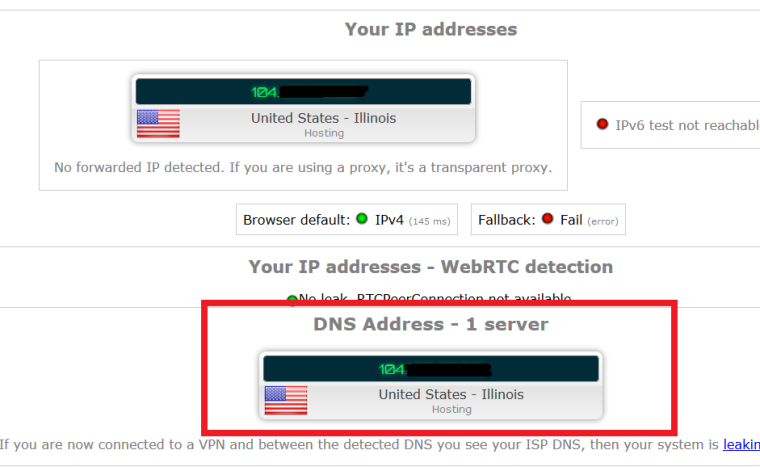
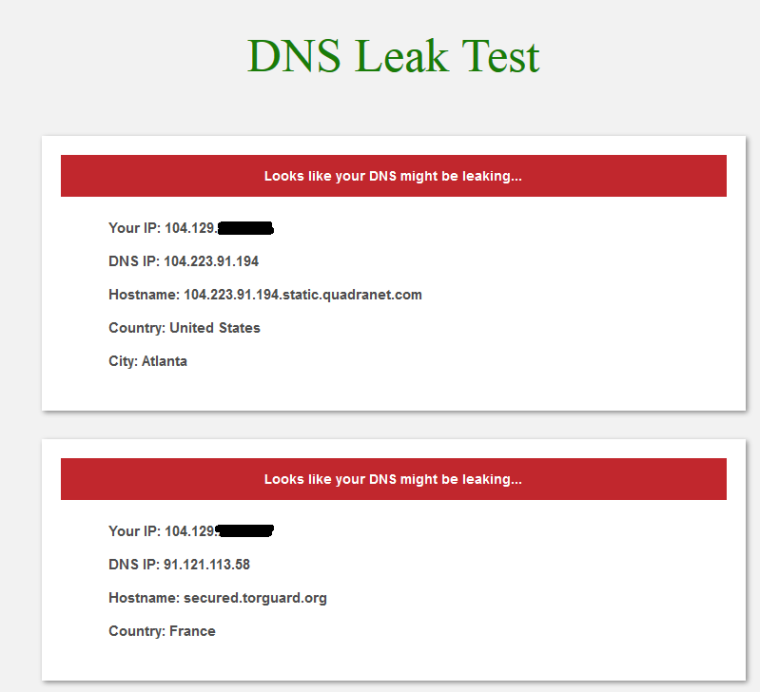
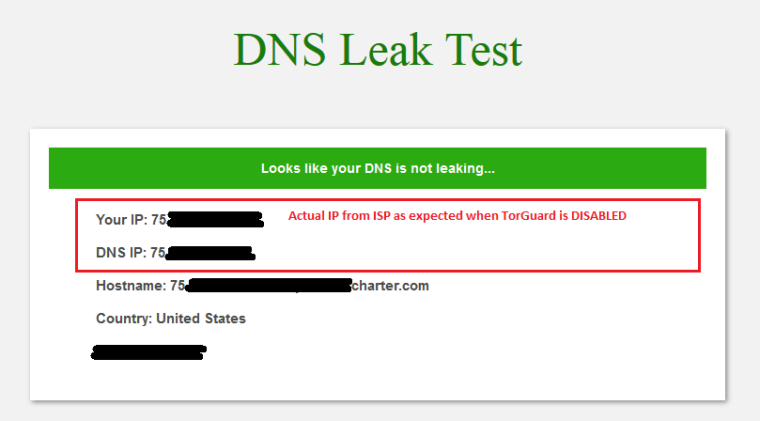
However there is still a bit of a DNS leak:
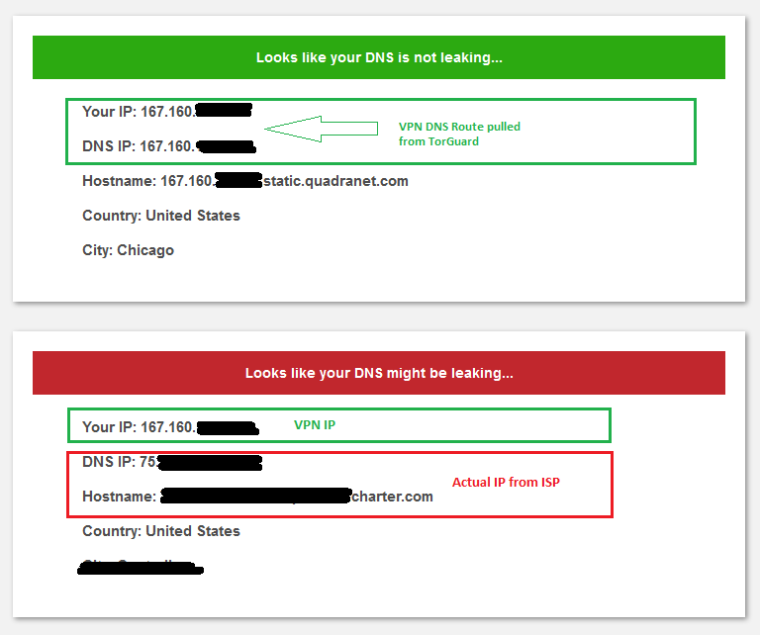
Before disabling those Outbound NAT mappings were disabled DynDNS would report the IP of the TorGuard VPN and would only have the top DNS result in green, it never listed two servers like this before when the Do Not Pull Routes option was unchecked...with the exception of the config I just tried above with (dnsmasq)
-
@teknikalcrysis said in Dynamic DNS gets cached IP as VPN client IP:
@gjaltemba said in Dynamic DNS gets cached IP as VPN client IP:
Leave your original setup asis. Just put this at the top.
outbound NAT on WAN interface source This Firewall(self) destination ?.ddns.net NAT address WAN address
It wont let me type anything but an IP in the destination box
I am able to type an alias for ***.ddns.net in the destination of outbound nat. The outbound NAT should register your ISP ip on ddns with openvpn client running.
To test, do a packet capture on WAN interface for traffic heading to ***.ddns.net. You see the pfSense WAN ip.
-
@gjaltemba said in Dynamic DNS gets cached IP as VPN client IP:
@teknikalcrysis said in Dynamic DNS gets cached IP as VPN client IP:
@gjaltemba said in Dynamic DNS gets cached IP as VPN client IP:
Leave your original setup asis. Just put this at the top.
outbound NAT on WAN interface source This Firewall(self) destination ?.ddns.net NAT address WAN address
It wont let me type anything but an IP in the destination box
I am able to type an alias for ***.ddns.net in the destination of outbound nat. The outbound NAT should register your ISP ip on ddns with openvpn client running.
But then at some point that alias would be obsolete, as my IP is not static and while not frequent (unless I force an ISP IP change by spoofing the MAC on the first router that is connected to the modem directly and then rebooting the modem) is does change from time to time if my power is out to long or in a few other scenarios.. when that happens, the alias would then be configured with an incorrect destination
-
@teknikalcrysis The alias can be dns name. To test include dnsleaktest.com in the alias browse to dnsleaktest.com and you will see your ISP ip. Remove dnsleaktest.com from the alias and you will see your vpn ip.
-
@gjaltemba I say again. Outbound NAT has nothing to do with which way traffic routes.
-
@derelict I get it but what is your point. Quick test from here tells me outbound NAT gives the desired result. To test, the source has to include the browser client ip because the firewall does not have a browser.
If for whatever reason outbound NAT does not work then there is always plan B. Setup a ddns client on the edge router outside pfSense.
-
This post is deleted! -
This post is deleted! -
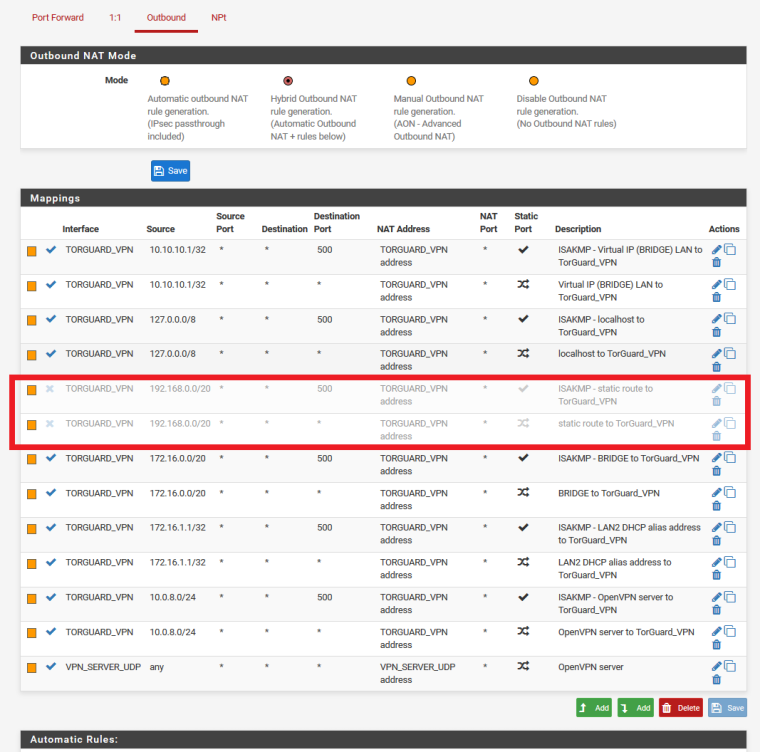
I think I fixed it....after playing around with some settings and getting close and talking about Outbound NAT and me disabling those Outbound NAT rules I highlighted earlier and managed to get DynDNS to update properly but still had it pulling two dns servers (the VPN and Unbound Resolver) causing a leak when those Outbound NAT mapping were disabled...it gave me an idea to Map Outbound NAT on TorGuard Interface from Source:WAN NET to Destination:ANY and NAT:TorGuard Address on Static Port:53 to push DNS queries back to TorGuard and stop the leak
NEW Outbound NAT Config:
Here is what happens when I DISABLED/DISCONNECT the TorGuard VPN
DynDNS updates correctly obviously:
And DNS result is as expected and desired:
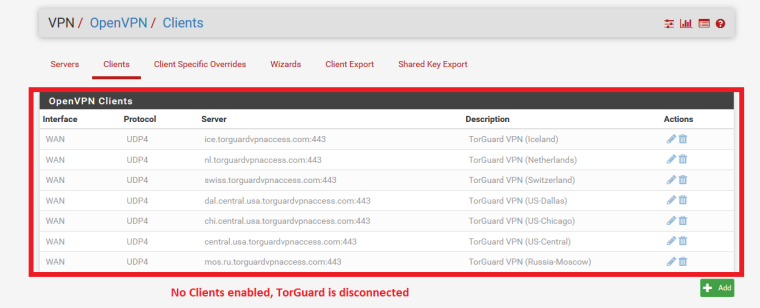
Now here is what happens when I ENABLED one of the TorGuard VPN Client connections...(drum roll please!)
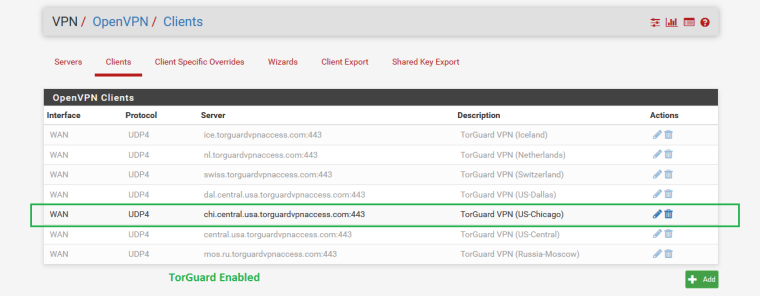
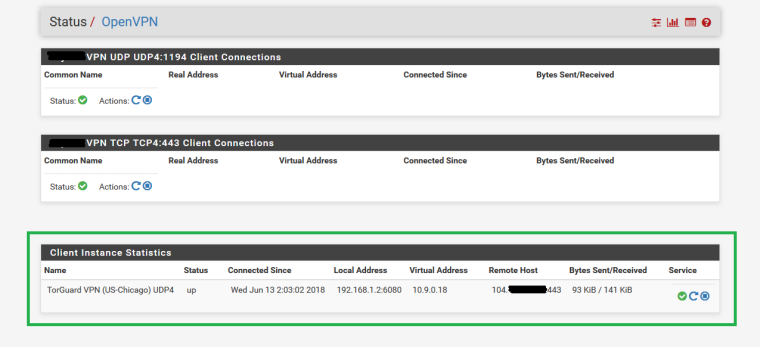
DynDNS Result is STILL actual IP as desired!!!
And NO DNS LEAK when TorGuard is Active!!!
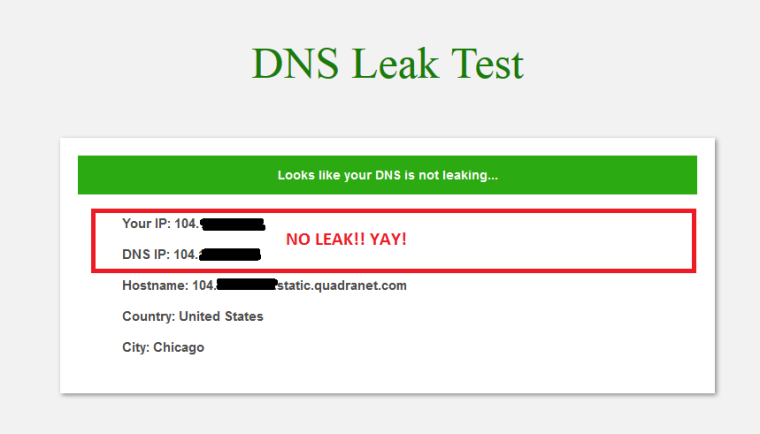
and just for a second opinion...Confirmed NO LEAKS