When creating self signed certificate, no prompts
-
^ exactly!! How are you going to be helping anyone while doing MITM ;) of their SSL traffic - so you can notify them something is down.. No thanks! Any of your customers that noticed this wouldn't be a customer for long..
-
@johnpoz Exactly. Well, I'm disappointed to learn this. Need some way of notifying why no internet so they aren't hard rebooting customer owned premises equipment blowing out the config then calling on me to fix when it's not my equipment. I suppose the best will have to be an unsigned cert with prompts. Hopefully most will figure it out.
Correction; self-signed cert
-
Welcome to the world of end to end encryption "everywhere" ;)
-
That's a very poor reason to hijack people's secure browsing sessions.
A $5 wrench and some well-delivered threats will be a better deterrent. Or a locking cage and good signage.
-
@johnpoz Thanks so much for all your help john, jimp, steven. Not quite the homecoming I was expecting.
-
@jimp Threats don't go over well either. I think hijack is a bit strong for what I'm trying to do. Redirecting a customer's planned session that has not yet been established.
-
You might argue a self signed cert is actually better in that situation as it's obviously not the site you were trying to reach.
Vs a cert from a known CA but with the wrong host name.
Both produce an alarming error if you're not used to it though
Steve
-
@stephenw10 I agree, probably the best. Probably good to deal an alarming site vs threats (just ribbing a bit jimp, I understand). I need to get their attention especially in the no-pay situation and perhaps even RIAA infractions. Was hoping to expand to outages to entire pool but doubtful I'll do that with cert prompts. I'll use it sparingly. Thanks again guys.
-
Well, the wrench is an old joke, but threats to the pocketbook also work. "If you unplug this device without authorization, it will result in a service charge of $$$$"
-
@jimp Funny! Tried to keep it simple...
-
@johnpoz Hey John, when I create a server CA and Cert within PfSense Certificate Manager I'm given the option of downloading a .crt and .key file but not a .pem. Can you instruct?
-
crt is just a pem file.. look at it..
-
@johnpoz Ahhh, so just rename. Thanks.
-
@johnpoz Unfortunately simply renaming doesn't fly.
root/: /usr/local/etc/rc.d/mini_httpd.sh start
34381057080:error:0906D06C:PEM routines:PEM_read_bio:no start line:/builder/pfsense-234/tmp/FreeBSD-src/secure/lib/libcrypto/../../../crypto/openssl/crypto/pem/pem_lib.c:696:Expecting: ANY PRIVATE KEY
34381057080:error:140B0009:SSL routines:SSL_CTX_use_PrivateKey_file:PEM lib:/builder/pfsense-234/tmp/FreeBSD-src/secure/lib/libssl/../../../crypto/openssl/ssl/ssl_rsa.c:635: -
I do not run that... But what I can tell you is the file you export is PEM... simple enough to test it with openssl.
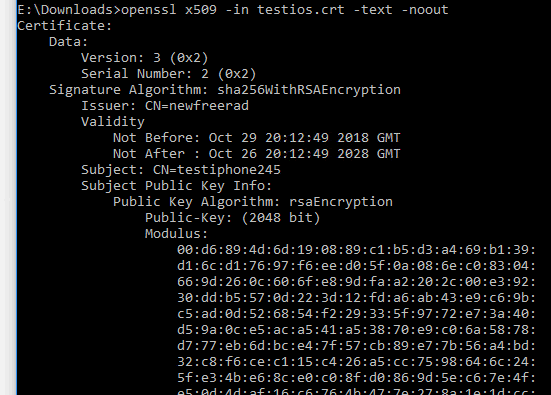
Here I just created a cert for another thread.. Tested it..
-
Combine the cert and key in one file:
-----BEGIN PRIVATE KEY----- keydatakeydatakeydatakeydatakeydatakeydatakeydatakeydata -----END PRIVATE KEY----- -----BEGIN CERTIFICATE----- certdatacertdatacertdatacertdatacertdatacertdatacertdatacertdata -----END CERTIFICATE-----At least that's what it looks like it's expecting.
Steve
-
@stephenw10 Thanks Steve, even tho freebsd “openssl verify ...” said the pem was bad that did the trick.
-
It's been a while since I tested this but co-incidentally did today and in fact every browser I tested is able to detect a captive portal redirect and trigger some alert to login without some huge error screen. It won't do that with a port forward lik you're doing here.
Kind of scary from a security view but makes it slick for end users.You would have to use it in some inverse way though. White-list all clients and remove those who need to see the redirect.
Steve
-
@markn6262 said in When creating self signed certificate, no prompts:
said the pem was bad that did the trick.
Then you got a bad copy or something in your download..
-
Maybe I wasn't clear enough in my last post. Combining the cert and key files into a pem file works with mini_httpd as stephen suggested. I'm golden! It's just that freebsd openssl verify reports the pem file as bad, oddly enough. I've never got a pem to report good creating from a freebsd comand line or from within PfSense GUI.