Setting reversed proxy
-
disable the 'ssl encryption' on all 3 servers (since you didnt decrypt the traffic on the frontend there is no need to encrypt it again before sending to the backend)
I wan't it to be encrypted traffic.
-
@varazir
Yes the client is sending encrypted traffic, the frontend as you configured it does NOT decrypt the traffic. So you can forward that traffic as-is to the webserver and it will still be encrypted.It shouldn't be encrypted twice, as the webserver will not understand the request then after decrypting it once..
-
I got one of the web servers to work but not the other one, the one I redirect to port 446.
It reports that server is down
Edit: I got Openvpn servar as online changing to Basic Health check.
But I get Transport error when I try to connect with my OpenVPN client.
TCP recv EOF -
ok got both of the web servers to work I had to change the Health checking to basic and enable SSL checks
-
@varazir
Though it works its probably better to change health-check's for the webservers back to http, and see what the LastChk column in stats says. Might be a forbidden method, or a authentication required, or it needs a sni indication in the check request, or a host header, or something. That is the thing to change and or fix to make health-checks pass on a webserver.As for the openvpn connection, i expect it is not actually sending a proper ssl encapsulated request.. As such you might need a 'special' acl where you could put the "!{ req.ssl_hello_type 1 } !{ req.len 0 }" in the acl for that use_backend action that might make it sellect the right backend, and allow it to connect.
Can you share the config as you got it now?
-
I have updated my Git https://gist.github.com/varazir/319b50bef3e4de1284ef52b38aaf5e23
The web2 keeps getting "active or backup DOWN for maintenance (MAINT) "
When I update the setting it works fine for a min or 2.Not sure where to add "!{ req.ssl_hello_type 1 } !{ req.len 0 }"
I guess there
-
I removed the check on web2
-
@varazir
What did stats page LastChk say when it was down? (hover over it with your mouse) -
@varazir
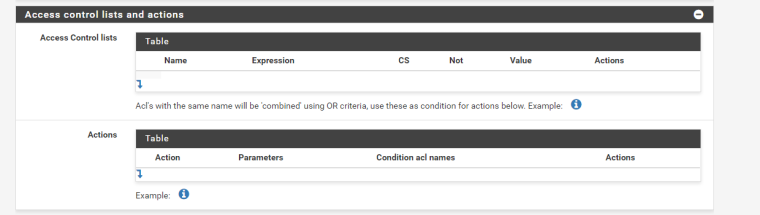
Instead of thisuse_backend Octoprint_ipvANY if Octoprintmake that like:
use_backend Octoprint_ipvANY if !{ req.ssl_hello_type 1 } !{ req.len 0 } -
That is from the config file trying to find how to set it in the GUI :P
-
@piba When it's working it say Layer7 check passed: OK
-
@varazir
You already wrote 'Octoprint' in that same textfield you can put the other acl text..As for above maint line it looks like the 'zwave' servername might not resolve DNS easily to a IP? That shouldnt depend on the type of check used anyhow.. Perhaps give it a few seconds more to resolve? And the check again? A L7 check that passes would be good..
-
@piba Well I have to look at the openVPN tomorrow, getting late.
Thanks for your help
-
Where should I place in the GUI this again ? Front or back end ?
use_backend Octoprint_ipvANY if !{ req.ssl_hello_type 1 } !{ req.len 0 } -
@varazir
Where in the gui did you write 'Octoprint'?( For a Frontend - action ? )
--Edit--
Though i think i got your backends mixed up.
Should use the special acl for the 'openvpn' action acl name. -
Word of warning: Make extra sure that you do not expose OctoPrint to the Internet. It is not designed to do that. Keep it locked behind a VPN.
Personally, I run haproxy directly on my OctoPrint Pis (and acme.sh to do the certs). It only takes a very small/simple config. Much more secure that way.
-
@piba said in Setting reversed proxy:
@varazir
Where in the gui did you write 'Octoprint'?( For a Frontend - action ? )
Front end but it's OpenVPN that is the issue. It's on the same port on pfSense.
Octoprint back/frontend works fine
I changed to IP and now the health check works much better. -
@jimp said in Setting reversed proxy:
Word of warning: Make extra sure that you do not expose OctoPrint to the Internet. It is not designed to do that. Keep it locked behind a VPN.
Personally, I run haproxy directly on my OctoPrint Pis (and acme.sh to do the certs). It only takes a very small/simple config. Much more secure that way.
ya I read that.
Octopi comes with HAProxy, I have setup a extra authentication. Using acl / http-request auth not sure if it's enoufe or there are other things that is not designed.How can you open port 80/443 to several hosts that using certbot ?
-
If it's protected by at least some kind of auth it may be OK, but I still would prefer to keep it behind a VPN.
As for certbot, that would probably just get routed based on the requested hostname. Should work with plain http and some ACLs. I use acme.sh and DNS-01 challenges though, I do not want any inbound web requests hitting my Pis.
-
@varazir
Yes sorry i mixed up your backends/acls.. Where i wrote octoprint i ment openvpn at least for the last few posts..use_backend Openvpn_ipvANY if !{ req.ssl_hello_type 1 } !{ req.len 0 }Anyhow still location to put that is the frontend/action acl-name.