Tried everything port forwarding not working??
-
Yes what’s there?
If your saying your WAN address is a RFC1918 address your pfSense box is connected to another router, that’s probably why the port forward isn’t working and also why you don’t see any hits on the firewall rule / packet capture.
-
@nogbadthebad My pfsense is only router connected. no other router in the house.
-
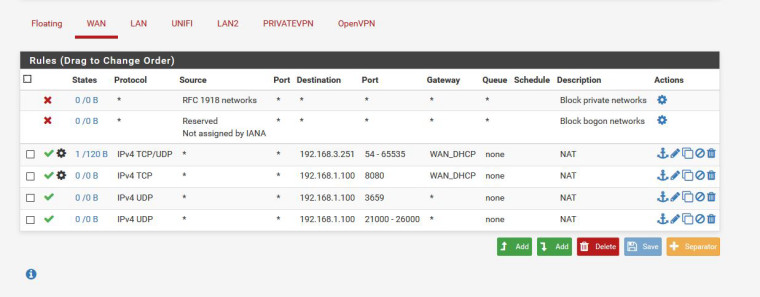
The order of the 3rd and 4th rule needs swapping round.
Firewall rules are read from top to bottom and why have you set a gateway
-
Not really. After the port forward translates the destination address the 54-65535 rule will not match.
-
@nogbadthebad Because I have a VPN on the other subnet.
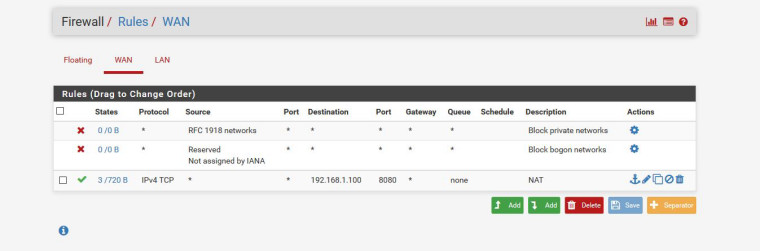
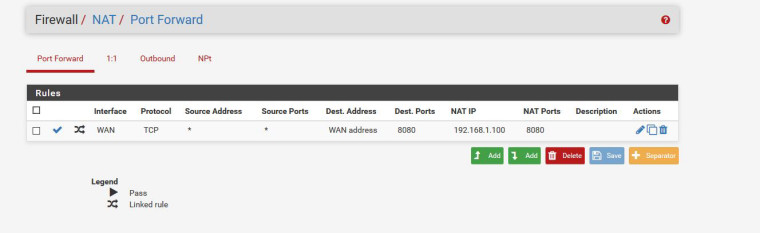
I have reset all my Pfsense box nothing installed and only port forward the 8080 an still not open.
-
@derelict That one is other subnet.
-
Packet capture on the INSIDE 192.168.1.0 interface for traffic to 192.168.1.100 port 8080 and test again. Is the traffic there?
-
@derelict how?
-
Diagnostics > Packet Capture
Interface: WAN
Protocol: TCP
Port: 8080
Count: 10000Start
Run your tests connecting to WAN:8080 from the outside.
Diagnostics > Packet Capture
Stop
What is displayed at the bottom?
THEN:
Diagnostics > Packet Capture
Interface: LAN
Host Address: 192.168.1.100
Protocol: TCP
Port: 8080
Count: 10000Start
Run your tests connecting to WAN:8080 from the outside.
Diagnostics > Packet Capture
Stop
What is displayed at the bottom?
-
@derelict Ok done that what is correct and whats not? Because my ip is there don´t want to share screen.
-
So copy and paste it into a text editor and search and replace for the first three octets of your WAN address substituting something like a.b.c and post the results.
-
@derelict
LAN
19:29:38.996655 IP ab.abc.6.228.56118 > 192.168.1.100.8080: tcp 0
19:29:38.996674 IP ab.abc.6.228.56120 > 192.168.1.100.8080: tcp 0
19:29:38.996908 IP 192.168.1.100.8080 > ab.abc.6.228.56118: tcp 0
19:29:38.996910 IP 192.168.1.100.8080 > ab.abc.6.228.56120: tcp 0
19:29:41.726274 IP ab.abc.6.228.56124 > 192.168.1.100.8080: tcp 0
19:29:41.726277 IP ab.abc.6.228.56126 > 192.168.1.100.8080: tcp 0
19:29:41.726443 IP 192.168.1.100.8080 > ab.abc.6.228.56126: tcp 0
19:29:41.727746 IP 192.168.1.100.8080 > ab.abc.6.228.56124: tcp 0WAN
19:36:45.017850 IP ab.abc.6.228.56158 > ab.abc.12.200.8080: tcp 0
19:36:45.017886 IP ab.abc.6.228.56160 > ab.abc.12.200.8080: tcp 0
19:36:45.018174 IP ab.abc.12.200.8080 > ab.abc.6.228.56158: tcp 0
19:36:45.018239 IP ab.abc.12.200.8080 > ab.abc.6.228.56160: tcp 0
19:36:46.470791 IP ab.abc.6.228.56164 > ab.abc.12.200.8080: tcp 0
19:36:46.470793 IP ab.abc.6.228.56162 > ab.abc.12.200.8080: tcp 0
19:36:46.471078 IP ab.abc.12.200.8080 > ab.abc.6.228.56162: tcp 0
19:36:46.471087 IP ab.abc.12.200.8080 > ab.abc.6.228.56164: tcp 0
19:36:47.605390 IP ab.abc.6.228.56168 > ab.abc.12.200.8080: tcp 0
19:36:47.605393 IP ab.abc.6.228.56166 > ab.abc.12.200.8080: tcp 0
19:36:47.605683 IP ab.abc.12.200.8080 > ab.abc.6.228.56166: tcp 0
19:36:47.605685 IP ab.abc.12.200.8080 > ab.abc.6.228.56168: tcp 0
19:36:48.731989 IP ab.abc.6.228.56172 > ab.abc.12.200.8080: tcp 0
19:36:48.731995 IP ab.abc.6.228.56170 > ab.abc.12.200.8080: tcp 0
19:36:48.732264 IP ab.abc.12.200.8080 > ab.abc.6.228.56170: tcp 0
19:36:48.732271 IP ab.abc.12.200.8080 > ab.abc.6.228.56172: tcp 0
19:36:49.240709 IP ab.abc.6.228.56174 > ab.abc.12.200.8080: tcp 0
19:36:49.240980 IP ab.abc.12.200.8080 > ab.abc.6.228.56174: tcp 0
19:36:49.240994 IP ab.abc.6.228.56176 > ab.abc.12.200.8080: tcp 0
19:36:49.241182 IP ab.abc.12.200.8080 > ab.abc.6.228.56176: tcp 0 -
OK. View the existing capture again but set Level of detail to full before pressing view, do the same substitution, and post that.
You don't have to capture again, just go to Diagnostics > Packet capture, set the level of detail, and press view to see the last capture taken again.
The LAN capture will be the most informative there.
-
WAN
19:36:45.017850 IP (tos 0x0, ttl 58, id 43787, offset 0, flags [DF], proto TCP (6), length 60)
ab.abc.6.228.56158 > ab.abc.12.200.8080: Flags [S], cksum 0x12ff (correct), seq 1259332011, win 65535, options [mss 1400,sackOK,TS val 20597408 ecr 0,nop,wscale 7], length 0
19:36:45.017886 IP (tos 0x0, ttl 58, id 12211, offset 0, flags [DF], proto TCP (6), length 60)
ab.abc.6.228.56160 > ab.abc.12.200.8080: Flags [S], cksum 0xd7ed (correct), seq 45573394, win 65535, options [mss 1400,sackOK,TS val 20597409 ecr 0,nop,wscale 7], length 0
19:36:45.018174 IP (tos 0x0, ttl 127, id 700, offset 0, flags [DF], proto TCP (6), length 40)
ab.abc.12.200.8080 > ab.abc.6.228.56158: Flags [R.], cksum 0xc66c (correct), seq 0, ack 1259332012, win 0, length 0
19:36:45.018239 IP (tos 0x0, ttl 127, id 701, offset 0, flags [DF], proto TCP (6), length 40)
ab.abc.12.200.8080 > ab.abc.6.228.56160: Flags [R.], cksum 0x8b5c (correct), seq 0, ack 45573395, win 0, length 0
19:36:46.470791 IP (tos 0x0, ttl 58, id 46133, offset 0, flags [DF], proto TCP (6), length 60)
ab.abc.6.228.56164 > ab.abc.12.200.8080: Flags [S], cksum 0xe53a (correct), seq 1625552932, win 65535, options [mss 1400,sackOK,TS val 20597777 ecr 0,nop,wscale 7], length 0
19:36:46.470793 IP (tos 0x0, ttl 58, id 9287, offset 0, flags [DF], proto TCP (6), length 60)
ab.abc.6.228.56162 > ab.abc.12.200.8080: Flags [S], cksum 0xc105 (correct), seq 350840918, win 65535, options [mss 1400,sackOK,TS val 20597777 ecr 0,nop,wscale 7], length 0
19:36:46.471078 IP (tos 0x0, ttl 127, id 702, offset 0, flags [DF], proto TCP (6), length 40)
ab.abc.12.200.8080 > ab.abc.6.228.56162: Flags [R.], cksum 0x75e4 (correct), seq 0, ack 350840919, win 0, length 0
19:36:46.471087 IP (tos 0x0, ttl 127, id 703, offset 0, flags [DF], proto TCP (6), length 40)
ab.abc.12.200.8080 > ab.abc.6.228.56164: Flags [R.], cksum 0x9a19 (correct), seq 0, ack 1625552933, win 0, length 0
19:36:47.605390 IP (tos 0x0, ttl 58, id 64686, offset 0, flags [DF], proto TCP (6), length 60)
ab.abc.6.228.56168 > ab.abc.12.200.8080: Flags [S], cksum 0x690f (correct), seq 579907979, win 65535, options [mss 1400,sackOK,TS val 20598053 ecr 0,nop,wscale 7], length 0
19:36:47.605393 IP (tos 0x0, ttl 58, id 37415, offset 0, flags [DF], proto TCP (6), length 60)
ab.abc.6.228.56166 > ab.abc.12.200.8080: Flags [S], cksum 0x2dde (correct), seq 810344195, win 65535, options [mss 1400,sackOK,TS val 20598052 ecr 0,nop,wscale 7], length 0
19:36:47.605683 IP (tos 0x0, ttl 127, id 704, offset 0, flags [DF], proto TCP (6), length 40)
ab.abc.12.200.8080 > ab.abc.6.228.56166: Flags [R.], cksum 0xe3cf (correct), seq 0, ack 810344196, win 0, length 0
19:36:47.605685 IP (tos 0x0, ttl 127, id 705, offset 0, flags [DF], proto TCP (6), length 40)
ab.abc.12.200.8080 > ab.abc.6.228.56168: Flags [R.], cksum 0x1f02 (correct), seq 0, ack 579907980, win 0, length 0
19:36:48.731989 IP (tos 0x0, ttl 58, id 2847, offset 0, flags [DF], proto TCP (6), length 60)
ab.abc.6.228.56172 > ab.abc.12.200.8080: Flags [S], cksum 0x7158 (correct), seq 2236892506, win 65535, options [mss 1400,sackOK,TS val 20598341 ecr 0,nop,wscale 7], length 0
19:36:48.731995 IP (tos 0x0, ttl 58, id 59432, offset 0, flags [DF], proto TCP (6), length 60)
ab.abc.6.228.56170 > ab.abc.12.200.8080: Flags [S], cksum 0x28f7 (correct), seq 1822729837, win 65535, options [mss 1400,sackOK,TS val 20598341 ecr 0,nop,wscale 7], length 0
19:36:48.732264 IP (tos 0x0, ttl 127, id 707, offset 0, flags [DF], proto TCP (6), length 40)
ab.abc.12.200.8080 > ab.abc.6.228.56170: Flags [R.], cksum 0xe009 (correct), seq 0, ack 1822729838, win 0, length 0
19:36:48.732271 IP (tos 0x0, ttl 127, id 706, offset 0, flags [DF], proto TCP (6), length 40)
ab.abc.12.200.8080 > ab.abc.6.228.56172: Flags [R.], cksum 0x286b (correct), seq 0, ack 2236892507, win 0, length 0
19:36:49.240709 IP (tos 0x0, ttl 58, id 9283, offset 0, flags [DF], proto TCP (6), length 60)
ab.abc.6.228.56174 > ab.abc.12.200.8080: Flags [S], cksum 0x907a (correct), seq 1082419845, win 65535, options [mss 1400,sackOK,TS val 20598470 ecr 0,nop,wscale 7], length 0
19:36:49.240980 IP (tos 0x0, ttl 127, id 708, offset 0, flags [DF], proto TCP (6), length 40)
ab.abc.12.200.8080 > ab.abc.6.228.56174: Flags [R.], cksum 0x480e (correct), seq 0, ack 1082419846, win 0, length 0
19:36:49.240994 IP (tos 0x0, ttl 58, id 19962, offset 0, flags [DF], proto TCP (6), length 60)
ab.abc.6.228.56176 > ab.abc.12.200.8080: Flags [S], cksum 0xe8b9 (correct), seq 1334444861, win 65535, options [mss 1400,sackOK,TS val 20598471 ecr 0,nop,wscale 7], length 0
19:36:49.241182 IP (tos 0x0, ttl 127, id 709, offset 0, flags [DF], proto TCP (6), length 40)
ab.abc.12.200.8080 > ab.abc.6.228.56176: Flags [R.], cksum 0xa04e (correct), seq 0, ack 1334444862, win 0, length 0LAN
19:43:54.971393 0c:c4:7a:ad:12:cd > 1c:1b:0d:e2:c4:a6, ethertype IPv4 (0x0800), length 74: (tos 0x0, ttl 57, id 14230, offset 0, flags [DF], proto TCP (6), length 60)
ab.abc.6.228.56182 > 192.168.1.100.8080: Flags [S], cksum 0x2ae0 (correct), seq 1086121736, win 65535, options [mss 1400,sackOK,TS val 20631710 ecr 0,nop,wscale 7], length 0
19:43:54.971410 0c:c4:7a:ad:12:cd > 1c:1b:0d:e2:c4:a6, ethertype IPv4 (0x0800), length 74: (tos 0x0, ttl 57, id 7781, offset 0, flags [DF], proto TCP (6), length 60)
ab.abc.6.228.56184 > 192.168.1.100.8080: Flags [S], cksum 0x6757 (correct), seq 475057915, win 65535, options [mss 1400,sackOK,TS val 20631710 ecr 0,nop,wscale 7], length 0
19:43:54.971634 1c:1b:0d:e2:c4:a6 > 0c:c4:7a:ad:12:cd, ethertype IPv4 (0x0800), length 60: (tos 0x0, ttl 128, id 727, offset 0, flags [DF], proto TCP (6), length 40)
192.168.1.100.8080 > ab.abc.6.228.56182: Flags [R.], cksum 0x644c (correct), seq 0, ack 1086121737, win 0, length 0
19:43:54.971638 1c:1b:0d:e2:c4:a6 > 0c:c4:7a:ad:12:cd, ethertype IPv4 (0x0800), length 60: (tos 0x0, ttl 128, id 726, offset 0, flags [DF], proto TCP (6), length 40)
192.168.1.100.8080 > ab.abc.6.228.56184: Flags [R.], cksum 0xa0c3 (correct), seq 0, ack 475057916, win 0, length 0
19:43:55.730943 0c:c4:7a:ad:12:cd > 1c:1b:0d:e2:c4:a6, ethertype IPv4 (0x0800), length 74: (tos 0x0, ttl 57, id 26287, offset 0, flags [DF], proto TCP (6), length 60)
ab.abc.6.228.56186 > 192.168.1.100.8080: Flags [S], cksum 0x527d (correct), seq 1198700509, win 65535, options [mss 1400,sackOK,TS val 20631922 ecr 0,nop,wscale 7], length 0
19:43:55.731135 1c:1b:0d:e2:c4:a6 > 0c:c4:7a:ad:12:cd, ethertype IPv4 (0x0800), length 60: (tos 0x0, ttl 128, id 728, offset 0, flags [DF], proto TCP (6), length 40)
192.168.1.100.8080 > ab.abc.6.228.56186: Flags [R.], cksum 0x8cbd (correct), seq 0, ack 1198700510, win 0, length 0
19:43:55.731219 0c:c4:7a:ad:12:cd > 1c:1b:0d:e2:c4:a6, ethertype IPv4 (0x0800), length 74: (tos 0x0, ttl 57, id 58580, offset 0, flags [DF], proto TCP (6), length 60)
ab.abc.6.228.56188 > 192.168.1.100.8080: Flags [S], cksum 0x2dc5 (correct), seq 3999085991, win 65535, options [mss 1400,sackOK,TS val 20631923 ecr 0,nop,wscale 7], length 0
19:43:55.731359 1c:1b:0d:e2:c4:a6 > 0c:c4:7a:ad:12:cd, ethertype IPv4 (0x0800), length 60: (tos 0x0, ttl 128, id 729, offset 0, flags [DF], proto TCP (6), length 40)
192.168.1.100.8080 > ab.abc.6.228.56188: Flags [R.], cksum 0x6806 (correct), seq 0, ack 3999085992, win 0, length 0
19:43:56.700229 0c:c4:7a:ad:12:cd > 1c:1b:0d:e2:c4:a6, ethertype IPv4 (0x0800), length 74: (tos 0x0, ttl 57, id 23624, offset 0, flags [DF], proto TCP (6), length 60)
ab.abc.6.228.56192 > 192.168.1.100.8080: Flags [S], cksum 0xbf33 (correct), seq 57904685, win 65535, options [mss 1400,sackOK,TS val 20632165 ecr 0,nop,wscale 7], length 0
19:43:56.700232 0c:c4:7a:ad:12:cd > 1c:1b:0d:e2:c4:a6, ethertype IPv4 (0x0800), length 74: (tos 0x0, ttl 57, id 21939, offset 0, flags [DF], proto TCP (6), length 60)
ab.abc.6.228.56190 > 192.168.1.100.8080: Flags [S], cksum 0x43fc (correct), seq 2231601110, win 65535, options [mss 1400,sackOK,TS val 20632165 ecr 0,nop,wscale 7], length 0
19:43:56.700460 1c:1b:0d:e2:c4:a6 > 0c:c4:7a:ad:12:cd, ethertype IPv4 (0x0800), length 60: (tos 0x0, ttl 128, id 730, offset 0, flags [DF], proto TCP (6), length 40)
192.168.1.100.8080 > ab.abc.6.228.56192: Flags [R.], cksum 0xfa66 (correct), seq 0, ack 57904686, win 0, length 0
19:43:56.700479 1c:1b:0d:e2:c4:a6 > 0c:c4:7a:ad:12:cd, ethertype IPv4 (0x0800), length 60: (tos 0x0, ttl 128, id 731, offset 0, flags [DF], proto TCP (6), length 40)
192.168.1.100.8080 > ab.abc.6.228.56190: Flags [R.], cksum 0x7f2f (correct), seq 0, ack 2231601111, win 0, length 0
19:43:57.479483 0c:c4:7a:ad:12:cd > 1c:1b:0d:e2:c4:a6, ethertype IPv4 (0x0800), length 74: (tos 0x0, ttl 57, id 47298, offset 0, flags [DF], proto TCP (6), length 60)
ab.abc.6.228.56196 > 192.168.1.100.8080: Flags [S], cksum 0x97b4 (correct), seq 1282305000, win 65535, options [mss 1400,sackOK,TS val 20632362 ecr 0,nop,wscale 7], length 0
19:43:57.479724 0c:c4:7a:ad:12:cd > 1c:1b:0d:e2:c4:a6, ethertype IPv4 (0x0800), length 74: (tos 0x0, ttl 57, id 42162, offset 0, flags [DF], proto TCP (6), length 60)
ab.abc.6.228.56194 > 192.168.1.100.8080: Flags [S], cksum 0xb391 (correct), seq 618887064, win 65535, options [mss 1400,sackOK,TS val 20632362 ecr 0,nop,wscale 7], length 0
19:43:57.479734 1c:1b:0d:e2:c4:a6 > 0c:c4:7a:ad:12:cd, ethertype IPv4 (0x0800), length 60: (tos 0x0, ttl 128, id 732, offset 0, flags [DF], proto TCP (6), length 40)
192.168.1.100.8080 > ab.abc.6.228.56196: Flags [R.], cksum 0xd3ac (correct), seq 0, ack 1282305001, win 0, length 0
19:43:57.479848 1c:1b:0d:e2:c4:a6 > 0c:c4:7a:ad:12:cd, ethertype IPv4 (0x0800), length 60: (tos 0x0, ttl 128, id 733, offset 0, flags [DF], proto TCP (6), length 40)
192.168.1.100.8080 > ab.abc.6.228.56194: Flags [R.], cksum 0xef89 (correct), seq 0, ack 618887065, win 0, length 0
19:43:58.077891 0c:c4:7a:ad:12:cd > 1c:1b:0d:e2:c4:a6, ethertype IPv4 (0x0800), length 74: (tos 0x0, ttl 57, id 37849, offset 0, flags [DF], proto TCP (6), length 60)
ab.abc.6.228.56198 > 192.168.1.100.8080: Flags [S], cksum 0xd0b8 (correct), seq 1050755097, win 65535, options [mss 1400,sackOK,TS val 20632512 ecr 0,nop,wscale 7], length 0
19:43:58.077894 0c:c4:7a:ad:12:cd > 1c:1b:0d:e2:c4:a6, ethertype IPv4 (0x0800), length 74: (tos 0x0, ttl 57, id 44968, offset 0, flags [DF], proto TCP (6), length 60)
ab.abc.6.228.56200 > 192.168.1.100.8080: Flags [S], cksum 0x2134 (correct), seq 2983492712, win 65535, options [mss 1400,sackOK,TS val 20632512 ecr 0,nop,wscale 7], length 0
19:43:58.078065 1c:1b:0d:e2:c4:a6 > 0c:c4:7a:ad:12:cd, ethertype IPv4 (0x0800), length 60: (tos 0x0, ttl 128, id 734, offset 0, flags [DF], proto TCP (6), length 40)
192.168.1.100.8080 > ab.abc.6.228.56200: Flags [R.], cksum 0x5dc2 (correct), seq 0, ack 2983492713, win 0, length 0
19:43:58.078069 1c:1b:0d:e2:c4:a6 > 0c:c4:7a:ad:12:cd, ethertype IPv4 (0x0800), length 60: (tos 0x0, ttl 128, id 735, offset 0, flags [DF], proto TCP (6), length 40)
192.168.1.100.8080 > ab.abc.6.228.56198: Flags [R.], cksum 0x0d47 (correct), seq 0, ack 1050755098, win 0, length 0
19:44:00.029110 0c:c4:7a:ad:12:cd > 1c:1b:0d:e2:c4:a6, ethertype IPv4 (0x0800), length 74: (tos 0x0, ttl 57, id 38396, offset 0, flags [DF], proto TCP (6), length 60)
ab.abc.6.228.56206 > 192.168.1.100.8080: Flags [S], cksum 0xed26 (correct), seq 537280605, win 65535, options [mss 1400,sackOK,TS val 20632993 ecr 0,nop,wscale 7], length 0
19:44:00.029118 0c:c4:7a:ad:12:cd > 1c:1b:0d:e2:c4:a6, ethertype IPv4 (0x0800), length 74: (tos 0x0, ttl 57, id 2757, offset 0, flags [DF], proto TCP (6), length 60)
ab.abc.6.228.56208 > 192.168.1.100.8080: Flags [S], cksum 0xe38e (correct), seq 2324750183, win 65535, options [mss 1400,sackOK,TS val 20632994 ecr 0,nop,wscale 7], length 0
19:44:00.029386 1c:1b:0d:e2:c4:a6 > 0c:c4:7a:ad:12:cd, ethertype IPv4 (0x0800), length 60: (tos 0x0, ttl 128, id 736, offset 0, flags [DF], proto TCP (6), length 40)
192.168.1.100.8080 > ab.abc.6.228.56206: Flags [R.], cksum 0x2b96 (correct), seq 0, ack 537280606, win 0, length 0
19:44:00.029393 1c:1b:0d:e2:c4:a6 > 0c:c4:7a:ad:12:cd, ethertype IPv4 (0x0800), length 60: (tos 0x0, ttl 128, id 737, offset 0, flags [DF], proto TCP (6), length 40) -
@djinn1 said in Tried everything port forwarding not working??:
ab.abc.6.228.56158: Flags [R.],
So that is where your box your sending too said F OFF!! with a RST [R].. So you need to check with the box your forwarding 8080 to why its not allowing the 8080 connection.
Has nothing to do with pfsense.
-
So you mean something blocking in my PC?
-
192.168.1.100 is REJECTING the connection attempts. You will need to look there.
-
Yes pfsense did exactly what it was told to do it forwarded the traffic to your box behind pfsense.. That device basically told the connection to F OFF!!
This is the SYN [S]
ab.abc.6.228.56182 > 192.168.1.100.8080: Flags [S]This is start of a tcp connection.. Answer back should of been SA, ie SYN ACK - say sure lets talk.. vs the RST that basically saying GO AWAY I don't want to talk on this port..
-
@johnpoz said in Tried everything port forwarding not working??:
s the RST that basically saying GO AWAY I don't want to talk on this port..
But i have disable antivirus and windows firewall how can the PC be blocking?
-
Doesn't have to be blocking - dpending on the OS if the port is not being listen for then it would send back a RST..
Check on the .100 machine that its actually listening on 8080, simple netstat command will show you what ports are being listened on.