WAN question
-
Hello!
I have a question - how to block 8.8.8.8 in WAN?
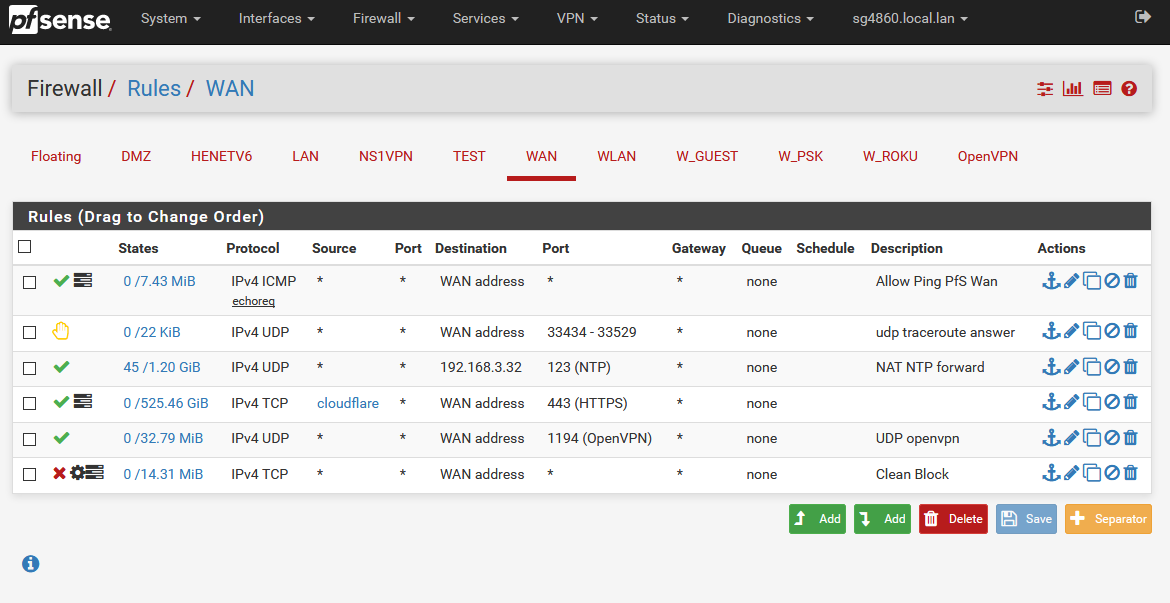
I've got pfsense 2.4.4-release-p3 (amd64). In LAN rules work, but in WAN - no. I can block 8.8.8.8 for all computers, but not for the router. I mean, Diagnostic - > Ping - a've got ping even two rules.
rule 1: destination 8.8.8.8, any protocol, ipv4, any sorce, action- block, interface - WAN
rule 2: source 8.8.8.8, any protocol, ipv4, any destination, action - block, interface - WANLAN re0 - 192.168.1.1
WAN ue0 - 192.168.0.12
Gateway 192.168.0.1
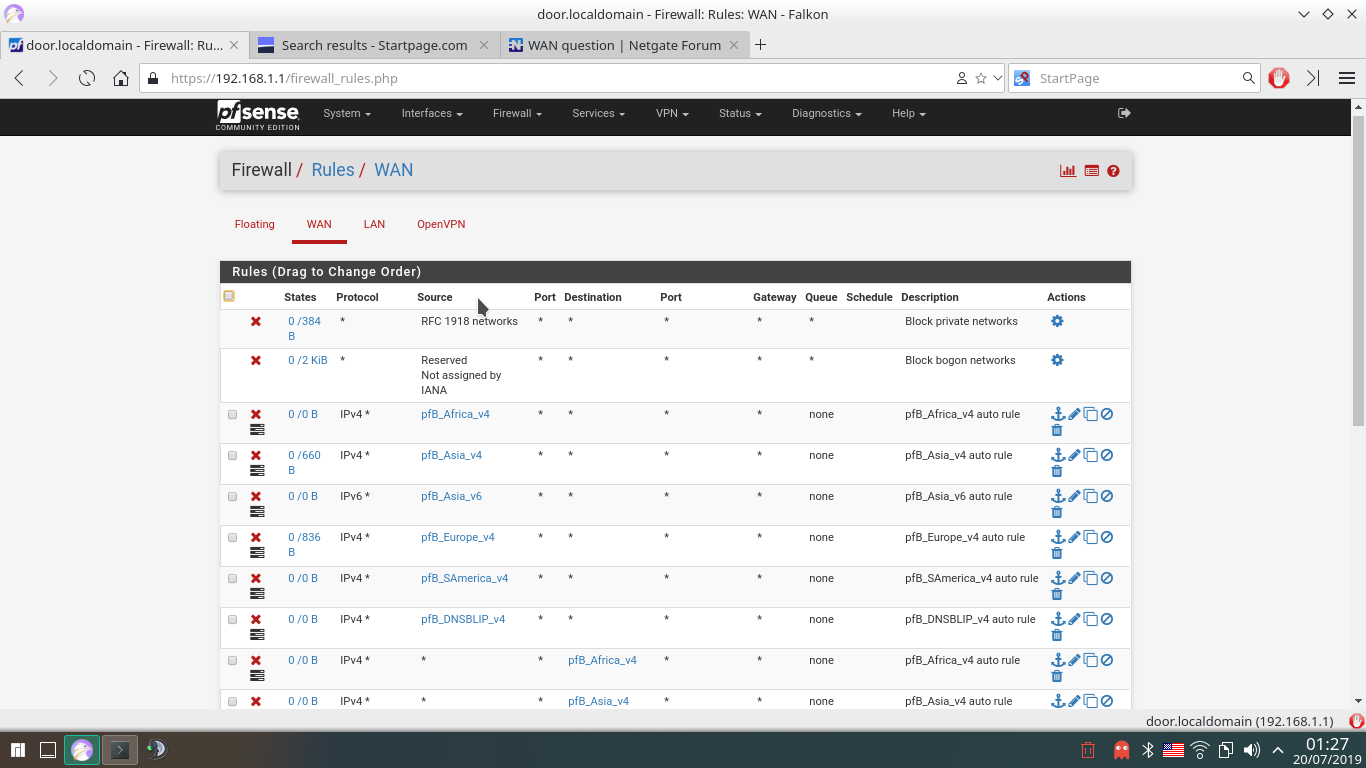
I don't have any "Pass" rule in my WAN Rules list, so it's not possible to be issue because wrong rules.Also, i've got installed pfblockerng-devel, OpenVPN (disabled), iperf
[2.4.4-RELEASE][root@door.localdomain]/root: pfctl -sa TRANSLATION RULES: no nat proto carp all nat-anchor "natearly/*" all nat-anchor "natrules/*" all nat on ue0 inet from 10.10.10.1 to any port = isakmp -> 192.168.0.12 static-port nat on ue0 inet from 127.0.0.0/8 to any port = isakmp -> 192.168.0.12 static-port nat on ue0 inet from 192.168.1.0/24 to any port = isakmp -> 192.168.0.12 static-port nat on ue0 inet6 from ::1 to any port = isakmp -> (ue0) round-robin static-port nat on ue0 inet from 10.10.10.1 to any -> 192.168.0.12 port 1024:65535 nat on ue0 inet from 127.0.0.0/8 to any -> 192.168.0.12 port 1024:65535 nat on ue0 inet from 192.168.1.0/24 to any -> 192.168.0.12 port 1024:65535 nat on ue0 inet6 from ::1 to any -> (ue0) port 1024:65535 round-robin no rdr proto carp all rdr-anchor "relayd/*" all rdr-anchor "tftp-proxy/*" all rdr on re0 inet proto tcp from any to ! 192.168.1.1 port = domain -> 127.0.0.1 rdr on re0 inet proto udp from any to ! 192.168.1.1 port = domain -> 127.0.0.1 rdr pass on re0 inet proto tcp from any to 10.10.10.1 port = http -> 127.0.0.1 port 8081 rdr pass on openvpn inet proto tcp from any to 10.10.10.1 port = http -> 127.0.0.1 port 8081 rdr pass on re0 inet proto tcp from any to 10.10.10.1 port = https -> 127.0.0.1 port 8443 rdr pass on openvpn inet proto tcp from any to 10.10.10.1 port = https -> 127.0.0.1 port 8443 rdr-anchor "miniupnpd" all FILTER RULES: scrub on ue0 all fragment reassemble scrub on re0 all fragment reassemble anchor "relayd/*" all anchor "openvpn/*" all anchor "ipsec/*" all block drop in log quick inet from 169.254.0.0/16 to any label "Block IPv4 link-local" block drop in log quick inet from any to 169.254.0.0/16 label "Block IPv4 link-local" block drop in log inet all label "Default deny rule IPv4" block drop out log inet all label "Default deny rule IPv4" block drop in log inet6 all label "Default deny rule IPv6" block drop out log inet6 all label "Default deny rule IPv6" pass quick inet6 proto ipv6-icmp all icmp6-type unreach keep state pass quick inet6 proto ipv6-icmp all icmp6-type toobig keep state pass quick inet6 proto ipv6-icmp all icmp6-type neighbrsol keep state pass quick inet6 proto ipv6-icmp all icmp6-type neighbradv keep state pass out quick inet6 proto ipv6-icmp from fe80::/10 to fe80::/10 icmp6-type echorep keep state pass out quick inet6 proto ipv6-icmp from fe80::/10 to fe80::/10 icmp6-type routersol keep state pass out quick inet6 proto ipv6-icmp from fe80::/10 to fe80::/10 icmp6-type routeradv keep state pass out quick inet6 proto ipv6-icmp from fe80::/10 to fe80::/10 icmp6-type neighbrsol keep state pass out quick inet6 proto ipv6-icmp from fe80::/10 to fe80::/10 icmp6-type neighbradv keep state pass out quick inet6 proto ipv6-icmp from fe80::/10 to ff02::/16 icmp6-type echorep keep state pass out quick inet6 proto ipv6-icmp from fe80::/10 to ff02::/16 icmp6-type routersol keep state pass out quick inet6 proto ipv6-icmp from fe80::/10 to ff02::/16 icmp6-type routeradv keep state pass out quick inet6 proto ipv6-icmp from fe80::/10 to ff02::/16 icmp6-type neighbrsol keep state pass out quick inet6 proto ipv6-icmp from fe80::/10 to ff02::/16 icmp6-type neighbradv keep state pass in quick inet6 proto ipv6-icmp from fe80::/10 to fe80::/10 icmp6-type echoreq keep state pass in quick inet6 proto ipv6-icmp from fe80::/10 to fe80::/10 icmp6-type routersol keep state pass in quick inet6 proto ipv6-icmp from fe80::/10 to fe80::/10 icmp6-type routeradv keep state pass in quick inet6 proto ipv6-icmp from fe80::/10 to fe80::/10 icmp6-type neighbrsol keep state pass in quick inet6 proto ipv6-icmp from fe80::/10 to fe80::/10 icmp6-type neighbradv keep state pass in quick inet6 proto ipv6-icmp from ff02::/16 to fe80::/10 icmp6-type echoreq keep state pass in quick inet6 proto ipv6-icmp from ff02::/16 to fe80::/10 icmp6-type routersol keep state pass in quick inet6 proto ipv6-icmp from ff02::/16 to fe80::/10 icmp6-type routeradv keep state pass in quick inet6 proto ipv6-icmp from ff02::/16 to fe80::/10 icmp6-type neighbrsol keep state pass in quick inet6 proto ipv6-icmp from ff02::/16 to fe80::/10 icmp6-type neighbradv keep state pass in quick inet6 proto ipv6-icmp from fe80::/10 to ff02::/16 icmp6-type echoreq keep state pass in quick inet6 proto ipv6-icmp from fe80::/10 to ff02::/16 icmp6-type routersol keep state pass in quick inet6 proto ipv6-icmp from fe80::/10 to ff02::/16 icmp6-type routeradv keep state pass in quick inet6 proto ipv6-icmp from fe80::/10 to ff02::/16 icmp6-type neighbrsol keep state pass in quick inet6 proto ipv6-icmp from fe80::/10 to ff02::/16 icmp6-type neighbradv keep state pass in quick inet6 proto ipv6-icmp from :: to ff02::/16 icmp6-type echoreq keep state pass in quick inet6 proto ipv6-icmp from :: to ff02::/16 icmp6-type routersol keep state pass in quick inet6 proto ipv6-icmp from :: to ff02::/16 icmp6-type routeradv keep state pass in quick inet6 proto ipv6-icmp from :: to ff02::/16 icmp6-type neighbrsol keep state pass in quick inet6 proto ipv6-icmp from :: to ff02::/16 icmp6-type neighbradv keep state block drop log quick inet proto tcp from any port = 0 to any label "Block traffic from port 0" block drop log quick inet proto udp from any port = 0 to any label "Block traffic from port 0" block drop log quick inet proto tcp from any to any port = 0 label "Block traffic to port 0" block drop log quick inet proto udp from any to any port = 0 label "Block traffic to port 0" block drop log quick inet6 proto tcp from any port = 0 to any label "Block traffic from port 0" block drop log quick inet6 proto udp from any port = 0 to any label "Block traffic from port 0" block drop log quick inet6 proto tcp from any to any port = 0 label "Block traffic to port 0" block drop log quick inet6 proto udp from any to any port = 0 label "Block traffic to port 0" block drop log quick from <snort2c> to any label "Block snort2c hosts" block drop log quick from any to <snort2c> label "Block snort2c hosts" block drop in log quick proto carp from (self) to any pass quick proto carp all no state block drop in log quick proto tcp from <sshguard> to (self) port = ssh label "sshguard" block drop in log quick proto tcp from <sshguard> to (self) port = https label "GUI Lockout" block drop in log quick from <virusprot> to any label "virusprot overload table" pass in quick on ue0 proto udp from any port = bootps to any port = bootpc keep state label "allow dhcp client out WAN" pass out quick on ue0 proto udp from any port = bootpc to any port = bootps keep state label "allow dhcp client out WAN" block drop in log quick on ue0 from <bogons> to any label "block bogon IPv4 networks from WAN" block drop in log quick on ue0 from <bogonsv6> to any label "block bogon IPv6 networks from WAN" block drop in log on ! ue0 inet from 192.168.0.0/24 to any block drop in log inet from 192.168.0.12 to any block drop in log on ue0 inet6 from fe80::8eae:4cff:fee9:bb0c to any block drop in log quick on ue0 inet from 10.0.0.0/8 to any label "Block private networks from WAN block 10/8" block drop in log quick on ue0 inet from 127.0.0.0/8 to any label "Block private networks from WAN block 127/8" block drop in log quick on ue0 inet from 172.16.0.0/12 to any label "Block private networks from WAN block 172.16/12" block drop in log quick on ue0 inet from 192.168.0.0/16 to any label "Block private networks from WAN block 192.168/16" block drop in log quick on ue0 inet6 from fc00::/7 to any label "Block ULA networks from WAN block fc00::/7" block drop in log on ! re0 inet from 192.168.1.0/24 to any block drop in log on ! re0 inet from 10.10.10.1 to any block drop in log inet from 192.168.1.1 to any block drop in log inet from 10.10.10.1 to any block drop in log on re0 inet6 from fe80::1ec1:deff:feb2:bbb9 to any pass in quick on re0 inet proto udp from any port = bootpc to 255.255.255.255 port = bootps keep state label "allow access to DHCP server" pass in quick on re0 inet proto udp from any port = bootpc to 192.168.1.1 port = bootps keep state label "allow access to DHCP server" pass out quick on re0 inet proto udp from 192.168.1.1 port = bootps to any port = bootpc keep state label "allow access to DHCP server" pass in on lo0 inet all flags S/SA keep state label "pass IPv4 loopback" pass out on lo0 inet all flags S/SA keep state label "pass IPv4 loopback" pass in on lo0 inet6 all flags S/SA keep state label "pass IPv6 loopback" pass out on lo0 inet6 all flags S/SA keep state label "pass IPv6 loopback" pass out inet all flags S/SA keep state allow-opts label "let out anything IPv4 from firewall host itself" pass out inet6 all flags S/SA keep state allow-opts label "let out anything IPv6 from firewall host itself" pass out route-to (ue0 192.168.0.1) inet from 192.168.0.12 to ! 192.168.0.0/24 flags S/SA keep state allow-opts label "let out anything from firewall host itself" pass in quick on re0 proto tcp from any to (re0) port = https flags S/SA keep state label "anti-lockout rule" pass in quick on re0 proto tcp from any to (re0) port = http flags S/SA keep state label "anti-lockout rule" pass in quick on re0 proto tcp from any to (re0) port = ssh flags S/SA keep state label "anti-lockout rule" anchor "userrules/*" all block drop in log quick on openvpn inet from <pfB_Africa_v4> to any label "USER_RULE: pfB_Africa_v4 auto rule" block drop in log quick on openvpn inet from <pfB_Asia_v4> to any label "USER_RULE: pfB_Asia_v4 auto rule" block drop in log quick on openvpn inet6 from <pfB_Asia_v6> to any label "USER_RULE: pfB_Asia_v6 auto rule" block drop in log quick on openvpn inet from <pfB_Europe_v4> to any label "USER_RULE: pfB_Europe_v4 auto rule" block drop in log quick on openvpn inet from <pfB_SAmerica_v4> to any label "USER_RULE: pfB_SAmerica_v4 auto rule" block drop in log quick on openvpn inet from <pfB_DNSBLIP_v4> to any label "USER_RULE: pfB_DNSBLIP_v4 auto rule" block drop in log quick on openvpn inet from any to <pfB_Africa_v4> label "USER_RULE: pfB_Africa_v4 auto rule" block drop in log quick on openvpn inet from any to <pfB_Asia_v4> label "USER_RULE: pfB_Asia_v4 auto rule" block drop in log quick on openvpn inet6 from any to <pfB_Asia_v6> label "USER_RULE: pfB_Asia_v6 auto rule" block drop in log quick on openvpn inet from any to <pfB_Europe_v4> label "USER_RULE: pfB_Europe_v4 auto rule" block drop in log quick on openvpn inet from any to <pfB_SAmerica_v4> label "USER_RULE: pfB_SAmerica_v4 auto rule" block drop in log quick on openvpn inet from any to <pfB_DNSBLIP_v4> label "USER_RULE: pfB_DNSBLIP_v4 auto rule" block drop in log quick on ue0 reply-to (ue0 192.168.0.1) inet from <pfB_Africa_v4> to any label "USER_RULE: pfB_Africa_v4 auto rule" block drop in log quick on ue0 reply-to (ue0 192.168.0.1) inet from <pfB_Asia_v4> to any label "USER_RULE: pfB_Asia_v4 auto rule" block drop in log quick on ue0 inet6 from <pfB_Asia_v6> to any label "USER_RULE: pfB_Asia_v6 auto rule" block drop in log quick on ue0 reply-to (ue0 192.168.0.1) inet from <pfB_Europe_v4> to any label "USER_RULE: pfB_Europe_v4 auto rule" block drop in log quick on ue0 reply-to (ue0 192.168.0.1) inet from <pfB_SAmerica_v4> to any label "USER_RULE: pfB_SAmerica_v4 auto rule" block drop in log quick on ue0 reply-to (ue0 192.168.0.1) inet from <pfB_DNSBLIP_v4> to any label "USER_RULE: pfB_DNSBLIP_v4 auto rule" block drop in log quick on re0 inet from <pfB_Africa_v4> to any label "USER_RULE: pfB_Africa_v4 auto rule" block drop in log quick on re0 inet from <pfB_Asia_v4> to any label "USER_RULE: pfB_Asia_v4 auto rule" block drop in log quick on re0 inet6 from <pfB_Asia_v6> to any label "USER_RULE: pfB_Asia_v6 auto rule" block drop in log quick on re0 inet from <pfB_Europe_v4> to any label "USER_RULE: pfB_Europe_v4 auto rule" block drop in log quick on re0 inet from <pfB_SAmerica_v4> to any label "USER_RULE: pfB_SAmerica_v4 auto rule" block drop in log quick on re0 inet from <pfB_DNSBLIP_v4> to any label "USER_RULE: pfB_DNSBLIP_v4 auto rule" block drop in log quick on ue0 reply-to (ue0 192.168.0.1) inet from any to <pfB_Africa_v4> label "USER_RULE: pfB_Africa_v4 auto rule" block drop in log quick on ue0 reply-to (ue0 192.168.0.1) inet from any to <pfB_Asia_v4> label "USER_RULE: pfB_Asia_v4 auto rule" block drop in log quick on ue0 inet6 from any to <pfB_Asia_v6> label "USER_RULE: pfB_Asia_v6 auto rule" block drop in log quick on ue0 reply-to (ue0 192.168.0.1) inet from any to <pfB_Europe_v4> label "USER_RULE: pfB_Europe_v4 auto rule" block drop in log quick on ue0 reply-to (ue0 192.168.0.1) inet from any to <pfB_SAmerica_v4> label "USER_RULE: pfB_SAmerica_v4 auto rule" block drop in log quick on ue0 reply-to (ue0 192.168.0.1) inet from any to <pfB_DNSBLIP_v4> label "USER_RULE: pfB_DNSBLIP_v4 auto rule" block drop in log quick on re0 inet from any to <pfB_Africa_v4> label "USER_RULE: pfB_Africa_v4 auto rule" block drop in log quick on re0 inet from any to <pfB_Asia_v4> label "USER_RULE: pfB_Asia_v4 auto rule" block drop in log quick on re0 inet6 from any to <pfB_Asia_v6> label "USER_RULE: pfB_Asia_v6 auto rule" block drop in log quick on re0 inet from any to <pfB_Europe_v4> label "USER_RULE: pfB_Europe_v4 auto rule" block drop in log quick on re0 inet from any to <pfB_SAmerica_v4> label "USER_RULE: pfB_SAmerica_v4 auto rule" block drop in log quick on re0 inet from any to <pfB_DNSBLIP_v4> label "USER_RULE: pfB_DNSBLIP_v4 auto rule" block drop in quick on ue0 inet6 all label "USER_RULE: Block all IPv6" block drop in quick on ue0 reply-to (ue0 192.168.0.1) inet from any to 8.8.8.8 label "USER_RULE" block drop in quick on ue0 reply-to (ue0 192.168.0.1) inet from 8.8.8.8 to any label "USER_RULE" block drop in quick on ue0 reply-to (ue0 192.168.0.1) inet proto tcp from any to any port = domain label "USER_RULE: Block all non-encrypted DNS" block drop in quick on ue0 reply-to (ue0 192.168.0.1) inet proto udp from any to any port = domain label "USER_RULE: Block all non-encrypted DNS" block drop in quick on re0 inet proto tcp from any to 192.168.0.0/24 port = telnet label "USER_RULE: Block23" block drop in quick on re0 inet proto udp from any to 192.168.0.0/24 port = telnet label "USER_RULE: Block23" block drop in quick on re0 inet from 192.168.1.20 to any label "USER_RULE" pass in quick on re0 inet from 192.168.1.0/24 to any flags S/SA keep state label "USER_RULE: Default allow LAN to any rule" pass in quick on re0 inet from 10.10.10.1 to any flags S/SA keep state label "USER_RULE: Default allow LAN to any rule" pass in quick on re0 inet proto tcp from any to 127.0.0.1 port = domain flags S/SA keep state label "USER_RULE: NAT All DNS to pfsense" pass in quick on re0 inet proto udp from any to 127.0.0.1 port = domain keep state label "USER_RULE: NAT All DNS to pfsense" anchor "tftp-proxy/*" all anchor "miniupnpd" all No queue in use STATES: ue0 icmp 192.168.0.12:24183 -> 192.168.0.1:24183 0:0 re0 tcp 208.123.73.199:443 <- 192.168.1.41:50560 ESTABLISHED:ESTABLISHED re0 tcp 34.249.72.44:443 <- 192.168.1.41:50562 TIME_WAIT:TIME_WAIT ue0 tcp 192.168.0.12:26990 (192.168.1.41:50560) -> 208.123.73.199:443 ESTABLISHED:ESTABLISHED re0 tcp 104.27.142.143:443 <- 192.168.1.41:50566 ESTABLISHED:ESTABLISHED ue0 tcp 192.168.0.12:44510 (192.168.1.41:50566) -> 104.27.142.143:443 ESTABLISHED:ESTABLISHED ue0 tcp 192.168.0.12:1324 (192.168.1.41:50562) -> 34.249.72.44:443 TIME_WAIT:TIME_WAIT re0 tcp 74.208.232.36:443 <- 192.168.1.40:42842 FIN_WAIT_2:FIN_WAIT_2 ue0 tcp 192.168.0.12:44825 (192.168.1.40:42842) -> 74.208.232.36:443 FIN_WAIT_2:FIN_WAIT_2 re0 udp 192.168.1.1:62857 -> 239.255.255.250:1900 SINGLE:NO_TRAFFIC ue0 tcp 192.168.0.12:32854 -> 1.1.1.1:853 FIN_WAIT_2:FIN_WAIT_2 re0 tcp 18.203.181.12:443 <- 192.168.1.41:50567 TIME_WAIT:TIME_WAIT ue0 tcp 192.168.0.12:16282 (192.168.1.41:50567) -> 18.203.181.12:443 TIME_WAIT:TIME_WAIT lo0 tcp 127.0.0.1:953 <- 127.0.0.1:32855 FIN_WAIT_2:FIN_WAIT_2 lo0 tcp 127.0.0.1:953 <- 127.0.0.1:32856 FIN_WAIT_2:FIN_WAIT_2 lo0 tcp 127.0.0.1:32857 -> 127.0.0.1:953 FIN_WAIT_2:FIN_WAIT_2 re0 tcp 192.168.1.1:22 <- 192.168.1.41:50568 TIME_WAIT:TIME_WAIT lo0 tcp 127.0.0.1:32858 -> 127.0.0.1:953 FIN_WAIT_2:FIN_WAIT_2 lo0 tcp 127.0.0.1:953 <- 127.0.0.1:32859 FIN_WAIT_2:FIN_WAIT_2 lo0 tcp 127.0.0.1:953 <- 127.0.0.1:32860 FIN_WAIT_2:FIN_WAIT_2 lo0 tcp 127.0.0.1:32861 -> 127.0.0.1:953 FIN_WAIT_2:FIN_WAIT_2 lo0 tcp 127.0.0.1:32862 -> 127.0.0.1:953 FIN_WAIT_2:FIN_WAIT_2 re0 tcp 18.203.181.12:443 <- 192.168.1.41:50569 TIME_WAIT:TIME_WAIT ue0 tcp 192.168.0.12:3158 (192.168.1.41:50569) -> 18.203.181.12:443 TIME_WAIT:TIME_WAIT lo0 tcp 127.0.0.1:57722 -> 127.0.0.1:953 FIN_WAIT_2:FIN_WAIT_2 lo0 tcp 127.0.0.1:18780 -> 127.0.0.1:953 FIN_WAIT_2:FIN_WAIT_2 lo0 tcp 127.0.0.1:24561 -> 127.0.0.1:953 FIN_WAIT_2:FIN_WAIT_2 re0 tcp 192.168.1.1:22 <- 192.168.1.41:50570 ESTABLISHED:ESTABLISHED lo0 tcp 127.0.0.1:953 <- 127.0.0.1:42093 FIN_WAIT_2:FIN_WAIT_2 lo0 tcp 127.0.0.1:25672 -> 127.0.0.1:953 FIN_WAIT_2:FIN_WAIT_2 lo0 udp 127.0.0.1:37093 -> 127.0.0.1:53 MULTIPLE:SINGLE ue0 tcp 192.168.0.12:35566 -> 1.1.1.1:853 TIME_WAIT:TIME_WAIT lo0 tcp 127.0.0.1:32855 -> 127.0.0.1:953 FIN_WAIT_2:FIN_WAIT_2 ue0 tcp 192.168.0.12:24940 -> 1.1.1.1:853 FIN_WAIT_2:FIN_WAIT_2 lo0 tcp 127.0.0.1:32856 -> 127.0.0.1:953 FIN_WAIT_2:FIN_WAIT_2 ue0 tcp 192.168.0.12:45958 -> 1.1.1.1:853 FIN_WAIT_2:FIN_WAIT_2 ue0 tcp 192.168.0.12:25088 -> 1.1.1.1:853 FIN_WAIT_2:FIN_WAIT_2 lo0 tcp 127.0.0.1:953 <- 127.0.0.1:32857 FIN_WAIT_2:FIN_WAIT_2 ue0 tcp 192.168.0.12:10416 -> 1.1.1.1:853 FIN_WAIT_2:FIN_WAIT_2 lo0 tcp 127.0.0.1:953 <- 127.0.0.1:32858 FIN_WAIT_2:FIN_WAIT_2 ue0 tcp 192.168.0.12:10419 -> 1.1.1.1:853 FIN_WAIT_2:FIN_WAIT_2 lo0 tcp 127.0.0.1:32859 -> 127.0.0.1:953 FIN_WAIT_2:FIN_WAIT_2 ue0 tcp 192.168.0.12:10423 -> 1.1.1.1:853 FIN_WAIT_2:FIN_WAIT_2 lo0 tcp 127.0.0.1:32860 -> 127.0.0.1:953 FIN_WAIT_2:FIN_WAIT_2 ue0 tcp 192.168.0.12:10425 -> 1.1.1.1:853 FIN_WAIT_2:FIN_WAIT_2 lo0 tcp 127.0.0.1:953 <- 127.0.0.1:32861 FIN_WAIT_2:FIN_WAIT_2 ue0 tcp 192.168.0.12:10426 -> 1.1.1.1:853 FIN_WAIT_2:FIN_WAIT_2 lo0 tcp 127.0.0.1:953 <- 127.0.0.1:32862 FIN_WAIT_2:FIN_WAIT_2 ue0 tcp 192.168.0.12:10428 -> 1.1.1.1:853 FIN_WAIT_2:FIN_WAIT_2 lo0 tcp 127.0.0.1:953 <- 127.0.0.1:57722 FIN_WAIT_2:FIN_WAIT_2 ue0 tcp 192.168.0.12:10431 -> 1.1.1.1:853 FIN_WAIT_2:FIN_WAIT_2 lo0 tcp 127.0.0.1:953 <- 127.0.0.1:18780 FIN_WAIT_2:FIN_WAIT_2 lo0 tcp 127.0.0.1:953 <- 127.0.0.1:10443 FIN_WAIT_2:FIN_WAIT_2 lo0 tcp 127.0.0.1:953 <- 127.0.0.1:24561 FIN_WAIT_2:FIN_WAIT_2 lo0 tcp 127.0.0.1:953 <- 127.0.0.1:10444 FIN_WAIT_2:FIN_WAIT_2 lo0 tcp 127.0.0.1:42093 -> 127.0.0.1:953 FIN_WAIT_2:FIN_WAIT_2 re0 udp 192.168.1.1:53 <- 192.168.1.40:39860 SINGLE:MULTIPLE lo0 tcp 127.0.0.1:953 <- 127.0.0.1:25672 FIN_WAIT_2:FIN_WAIT_2 ue0 tcp 192.168.0.12:10455 -> 1.1.1.1:853 FIN_WAIT_2:FIN_WAIT_2 lo0 udp 127.0.0.1:28049 -> 127.0.0.1:53 MULTIPLE:SINGLE re0 tcp 74.208.232.61:443 <- 192.168.1.40:34472 FIN_WAIT_2:FIN_WAIT_2 lo0 udp 127.0.0.1:53 <- 127.0.0.1:28049 SINGLE:MULTIPLE ue0 tcp 192.168.0.12:59584 (192.168.1.40:34472) -> 74.208.232.61:443 FIN_WAIT_2:FIN_WAIT_2 lo0 udp 127.0.0.1:53 <- 127.0.0.1:37093 SINGLE:MULTIPLE re0 tcp 74.208.232.61:443 <- 192.168.1.40:34474 ESTABLISHED:ESTABLISHED ue0 tcp 192.168.0.12:9073 -> 1.1.1.1:853 FIN_WAIT_2:FIN_WAIT_2 ue0 tcp 192.168.0.12:29519 (192.168.1.40:34474) -> 74.208.232.61:443 ESTABLISHED:ESTABLISHED ue0 tcp 192.168.0.12:54628 -> 1.1.1.1:853 FIN_WAIT_2:FIN_WAIT_2 lo0 tcp 127.0.0.1:10456 -> 127.0.0.1:953 FIN_WAIT_2:FIN_WAIT_2 ue0 tcp 192.168.0.12:10421 -> 1.1.1.1:853 FIN_WAIT_2:FIN_WAIT_2 re0 udp 192.168.1.1:53 <- 192.168.1.41:60245 SINGLE:MULTIPLE ue0 tcp 192.168.0.12:10430 -> 1.1.1.1:853 FIN_WAIT_2:FIN_WAIT_2 re0 tcp 52.212.14.221:443 <- 192.168.1.41:50571 ESTABLISHED:ESTABLISHED ue0 tcp 192.168.0.12:10436 -> 1.1.1.1:853 FIN_WAIT_2:FIN_WAIT_2 ue0 tcp 192.168.0.12:32270 (192.168.1.41:50571) -> 52.212.14.221:443 ESTABLISHED:ESTABLISHED ue0 tcp 192.168.0.12:10439 -> 1.1.1.1:853 FIN_WAIT_2:FIN_WAIT_2 lo0 udp 127.0.0.1:16185 -> 127.0.0.1:53 MULTIPLE:SINGLE ue0 tcp 192.168.0.12:10442 -> 1.1.1.1:853 FIN_WAIT_2:FIN_WAIT_2 lo0 udp 127.0.0.1:53 <- 127.0.0.1:16185 SINGLE:MULTIPLE lo0 tcp 127.0.0.1:10443 -> 127.0.0.1:953 FIN_WAIT_2:FIN_WAIT_2 lo0 udp 127.0.0.1:53 <- 127.0.0.1:60106 SINGLE:MULTIPLE lo0 tcp 127.0.0.1:10444 -> 127.0.0.1:953 FIN_WAIT_2:FIN_WAIT_2 ue0 tcp 192.168.0.12:10461 -> 1.1.1.1:853 FIN_WAIT_2:FIN_WAIT_2 lo0 tcp 127.0.0.1:953 <- 127.0.0.1:10456 FIN_WAIT_2:FIN_WAIT_2 ue0 tcp 192.168.0.12:10465 -> 1.1.1.1:853 FIN_WAIT_2:FIN_WAIT_2 ue0 tcp 192.168.0.12:10457 -> 1.1.1.1:853 FIN_WAIT_2:FIN_WAIT_2 ue0 tcp 192.168.0.12:10469 -> 1.1.1.1:853 FIN_WAIT_2:FIN_WAIT_2 lo0 udp 127.0.0.1:60106 -> 127.0.0.1:53 MULTIPLE:SINGLE ue0 tcp 192.168.0.12:10475 -> 1.1.1.1:853 FIN_WAIT_2:FIN_WAIT_2 ue0 tcp 192.168.0.12:10459 -> 1.1.1.1:853 FIN_WAIT_2:FIN_WAIT_2 re0 tcp 208.123.73.199:443 <- 192.168.1.41:50572 FIN_WAIT_2:FIN_WAIT_2 ue0 tcp 192.168.0.12:10472 -> 1.1.1.1:853 FIN_WAIT_2:FIN_WAIT_2 lo0 tcp 127.0.0.1:10476 -> 127.0.0.1:953 FIN_WAIT_2:FIN_WAIT_2 ue0 tcp 192.168.0.12:7242 (192.168.1.41:50572) -> 208.123.73.199:443 FIN_WAIT_2:FIN_WAIT_2 lo0 udp 127.0.0.1:47688 -> 127.0.0.1:53 MULTIPLE:SINGLE lo0 tcp 127.0.0.1:953 <- 127.0.0.1:10476 FIN_WAIT_2:FIN_WAIT_2 ue0 tcp 192.168.0.12:10477 -> 1.1.1.1:853 FIN_WAIT_2:FIN_WAIT_2 lo0 udp 127.0.0.1:53 <- 127.0.0.1:47688 SINGLE:MULTIPLE lo0 tcp 127.0.0.1:953 <- 127.0.0.1:10478 FIN_WAIT_2:FIN_WAIT_2 lo0 udp 127.0.0.1:27045 -> 127.0.0.1:53 MULTIPLE:SINGLE ue0 tcp 192.168.0.12:10483 -> 1.1.1.1:853 FIN_WAIT_2:FIN_WAIT_2 lo0 udp 127.0.0.1:53 <- 127.0.0.1:27045 SINGLE:MULTIPLE ue0 tcp 192.168.0.12:10487 -> 1.1.1.1:853 FIN_WAIT_2:FIN_WAIT_2 lo0 tcp 127.0.0.1:10478 -> 127.0.0.1:953 FIN_WAIT_2:FIN_WAIT_2 ue0 tcp 192.168.0.12:10488 -> 1.1.1.1:853 FIN_WAIT_2:FIN_WAIT_2 ue0 tcp 192.168.0.12:10482 -> 1.1.1.1:853 FIN_WAIT_2:FIN_WAIT_2 ue0 udp 192.168.0.12:123 -> 83.170.75.28:123 MULTIPLE:SINGLE ue0 tcp 192.168.0.12:10486 -> 1.1.1.1:853 FIN_WAIT_2:FIN_WAIT_2 lo0 tcp 127.0.0.1:953 <- 127.0.0.1:10489 FIN_WAIT_2:FIN_WAIT_2 lo0 tcp 127.0.0.1:10489 -> 127.0.0.1:953 FIN_WAIT_2:FIN_WAIT_2 lo0 udp 127.0.0.1:54796 -> 127.0.0.1:53 MULTIPLE:SINGLE lo0 udp 127.0.0.1:58269 -> 127.0.0.1:53 MULTIPLE:SINGLE ue0 tcp 192.168.0.12:10492 -> 1.1.1.1:853 FIN_WAIT_2:FIN_WAIT_2 lo0 udp 127.0.0.1:53 <- 127.0.0.1:58269 SINGLE:MULTIPLE lo0 udp 127.0.0.1:53 <- 127.0.0.1:54796 SINGLE:MULTIPLE ue0 tcp 192.168.0.12:10497 -> 1.1.1.1:853 FIN_WAIT_2:FIN_WAIT_2 INFO: Status: Enabled for 0 days 00:02:27 Debug: Urgent Interface Stats for re0 IPv4 IPv6 Bytes In 53580 0 Bytes Out 157851 416 Packets In Passed 474 0 Blocked 49 0 Packets Out Passed 597 5 Blocked 0 0 State Table Total Rate current entries 116 searches 18189 123.7/s inserts 248 1.7/s removals 132 0.9/s Counters match 339 2.3/s bad-offset 0 0.0/s fragment 0 0.0/s short 0 0.0/s normalize 0 0.0/s memory 0 0.0/s bad-timestamp 0 0.0/s congestion 0 0.0/s ip-option 1 0.0/s proto-cksum 0 0.0/s state-mismatch 0 0.0/s state-insert 0 0.0/s state-limit 0 0.0/s src-limit 0 0.0/s synproxy 0 0.0/s map-failed 0 0.0/s LABEL COUNTERS: Block IPv4 link-local 259 0 0 0 0 0 0 0 Block IPv4 link-local 141 0 0 0 0 0 0 0 Default deny rule IPv4 141 66 6433 66 6433 0 0 0 Default deny rule IPv4 258 0 0 0 0 0 0 0 Default deny rule IPv6 259 0 0 0 0 0 0 0 Default deny rule IPv6 117 0 0 0 0 0 0 0 Block traffic from port 0 259 0 0 0 0 0 0 0 Block traffic from port 0 55 0 0 0 0 0 0 0 Block traffic to port 0 259 0 0 0 0 0 0 0 Block traffic to port 0 56 0 0 0 0 0 0 0 Block traffic from port 0 259 0 0 0 0 0 0 0 Block traffic from port 0 0 0 0 0 0 0 0 0 Block traffic to port 0 0 0 0 0 0 0 0 0 Block traffic to port 0 0 0 0 0 0 0 0 0 Block snort2c hosts 257 0 0 0 0 0 0 0 Block snort2c hosts 257 0 0 0 0 0 0 0 sshguard 260 0 0 0 0 0 0 0 GUI Lockout 0 0 0 0 0 0 0 0 virusprot overload table 158 0 0 0 0 0 0 0 allow dhcp client out WAN 141 0 0 0 0 0 0 0 allow dhcp client out WAN 120 0 0 0 0 0 0 0 block bogon IPv4 networks from WAN 156 4 1424 4 1424 0 0 0 block bogon IPv6 networks from WAN 79 1 356 1 356 0 0 0 Block private networks from WAN block 10/8 29 0 0 0 0 0 0 0 Block private networks from WAN block 127/8 29 0 0 0 0 0 0 0 Block private networks from WAN block 172.16/12 29 0 0 0 0 0 0 0 Block private networks from WAN block 192.168/16 29 1 32 1 32 0 0 0 Block ULA networks from WAN block fc00::/7 28 0 0 0 0 0 0 0 allow access to DHCP server 70 0 0 0 0 0 0 0 allow access to DHCP server 0 0 0 0 0 0 0 0 allow access to DHCP server 129 0 0 0 0 0 0 0 pass IPv4 loopback 254 7168 706687 3596 256070 3572 450617 43 pass IPv4 loopback 83 0 0 0 0 0 0 0 pass IPv6 loopback 84 0 0 0 0 0 0 0 pass IPv6 loopback 42 0 0 0 0 0 0 0 let out anything IPv4 from firewall host itself 255 7279 759144 3572 450617 3707 308527 45 let out anything IPv6 from firewall host itself 117 0 0 0 0 0 0 0 let out anything from firewall host itself 116 1743 535017 731 436324 1012 98693 74 anti-lockout rule 323 1 48 1 48 0 0 0 anti-lockout rule 85 1 48 1 48 0 0 0 anti-lockout rule 85 567 76504 233 16770 334 59734 2 USER_RULE: pfB_Africa_v4 auto rule 320 0 0 0 0 0 0 0 USER_RULE: pfB_Asia_v4 auto rule 0 0 0 0 0 0 0 0 USER_RULE: pfB_Asia_v6 auto rule 0 0 0 0 0 0 0 0 USER_RULE: pfB_Europe_v4 auto rule 0 0 0 0 0 0 0 0 USER_RULE: pfB_SAmerica_v4 auto rule 0 0 0 0 0 0 0 0 USER_RULE: pfB_DNSBLIP_v4 auto rule 0 0 0 0 0 0 0 0 USER_RULE: pfB_Africa_v4 auto rule 0 0 0 0 0 0 0 0 USER_RULE: pfB_Asia_v4 auto rule 0 0 0 0 0 0 0 0 USER_RULE: pfB_Asia_v6 auto rule 0 0 0 0 0 0 0 0 USER_RULE: pfB_Europe_v4 auto rule 0 0 0 0 0 0 0 0 USER_RULE: pfB_SAmerica_v4 auto rule 0 0 0 0 0 0 0 0 USER_RULE: pfB_DNSBLIP_v4 auto rule 0 0 0 0 0 0 0 0 USER_RULE: pfB_Africa_v4 auto rule 320 0 0 0 0 0 0 0 USER_RULE: pfB_Asia_v4 auto rule 28 2 88 2 88 0 0 0 USER_RULE: pfB_Asia_v6 auto rule 26 0 0 0 0 0 0 0 USER_RULE: pfB_Europe_v4 auto rule 26 2 88 2 88 0 0 0 USER_RULE: pfB_SAmerica_v4 auto rule 24 0 0 0 0 0 0 0 USER_RULE: pfB_DNSBLIP_v4 auto rule 24 0 0 0 0 0 0 0 USER_RULE: pfB_Africa_v4 auto rule 193 0 0 0 0 0 0 0 USER_RULE: pfB_Asia_v4 auto rule 76 0 0 0 0 0 0 0 USER_RULE: pfB_Asia_v6 auto rule 76 0 0 0 0 0 0 0 USER_RULE: pfB_Europe_v4 auto rule 76 0 0 0 0 0 0 0 USER_RULE: pfB_SAmerica_v4 auto rule 76 0 0 0 0 0 0 0 USER_RULE: pfB_DNSBLIP_v4 auto rule 76 0 0 0 0 0 0 0 USER_RULE: pfB_Africa_v4 auto rule 190 0 0 0 0 0 0 0 USER_RULE: pfB_Asia_v4 auto rule 24 0 0 0 0 0 0 0 USER_RULE: pfB_Asia_v6 auto rule 24 0 0 0 0 0 0 0 USER_RULE: pfB_Europe_v4 auto rule 24 0 0 0 0 0 0 0 USER_RULE: pfB_SAmerica_v4 auto rule 24 0 0 0 0 0 0 0 USER_RULE: pfB_DNSBLIP_v4 auto rule 24 0 0 0 0 0 0 0 USER_RULE: pfB_Africa_v4 auto rule 189 0 0 0 0 0 0 0 USER_RULE: pfB_Asia_v4 auto rule 76 0 0 0 0 0 0 0 USER_RULE: pfB_Asia_v6 auto rule 76 0 0 0 0 0 0 0 USER_RULE: pfB_Europe_v4 auto rule 76 0 0 0 0 0 0 0 USER_RULE: pfB_SAmerica_v4 auto rule 76 0 0 0 0 0 0 0 USER_RULE: pfB_DNSBLIP_v4 auto rule 76 0 0 0 0 0 0 0 USER_RULE: Block all IPv6 189 0 0 0 0 0 0 0 USER_RULE 24 0 0 0 0 0 0 0 USER_RULE 24 0 0 0 0 0 0 0 USER_RULE: Block all non-encrypted DNS 24 0 0 0 0 0 0 0 USER_RULE: Block all non-encrypted DNS 4 0 0 0 0 0 0 0 USER_RULE: Block23 189 0 0 0 0 0 0 0 USER_RULE: Block23 30 0 0 0 0 0 0 0 USER_RULE 76 0 0 0 0 0 0 0 USER_RULE: Default allow LAN to any rule 76 262 59533 154 24328 108 35205 22 USER_RULE: Default allow LAN to any rule 54 27 7075 19 3131 8 3944 0 USER_RULE: NAT All DNS to pfsense 49 0 0 0 0 0 0 0 USER_RULE: NAT All DNS to pfsense 3 0 0 0 0 0 0 0 TIMEOUTS: tcp.first 120s tcp.opening 30s tcp.established 86400s tcp.closing 900s tcp.finwait 45s tcp.closed 90s tcp.tsdiff 30s udp.first 60s udp.single 30s udp.multiple 60s icmp.first 20s icmp.error 10s other.first 60s other.single 30s other.multiple 60s frag 30s interval 10s adaptive.start 115200 states adaptive.end 230400 states src.track 0s LIMITS: states hard limit 192000 src-nodes hard limit 192000 frags hard limit 5000 table-entries hard limit 400000 TABLES: bogons bogonsv6 pfB_Africa_v4 pfB_Asia_v4 pfB_Asia_v6 pfB_DNSBLIP_v4 pfB_Europe_v4 pfB_SAmerica_v4 snort2c sshguard virusprot OS FINGERPRINTS: 762 fingerprints loaded [2.4.4-RELEASE][root@door.localdomain]/root:What is this
block drop in quick on ue0 reply-to (ue0 192.168.0.1) inet from any to 8.8.8.8 label "USER_RULE" block drop in quick on ue0 reply-to (ue0 192.168.0.1) inet from 8.8.8.8 to any label "USER_RULE"ue0 must be 192.168.0.12 not 192.168.0.1
In fact, 192.168.0.1 is my Sky Hub router/modem.
-
@ArtGirl19 said in WAN question:
I have a question - how to block 8.8.8.8 in WAN?
Huh? 8.8.8.8 would never be creating traffic to you.. And even if it did the default deny rule would just drop the traffic.. Unless you had a port forward.
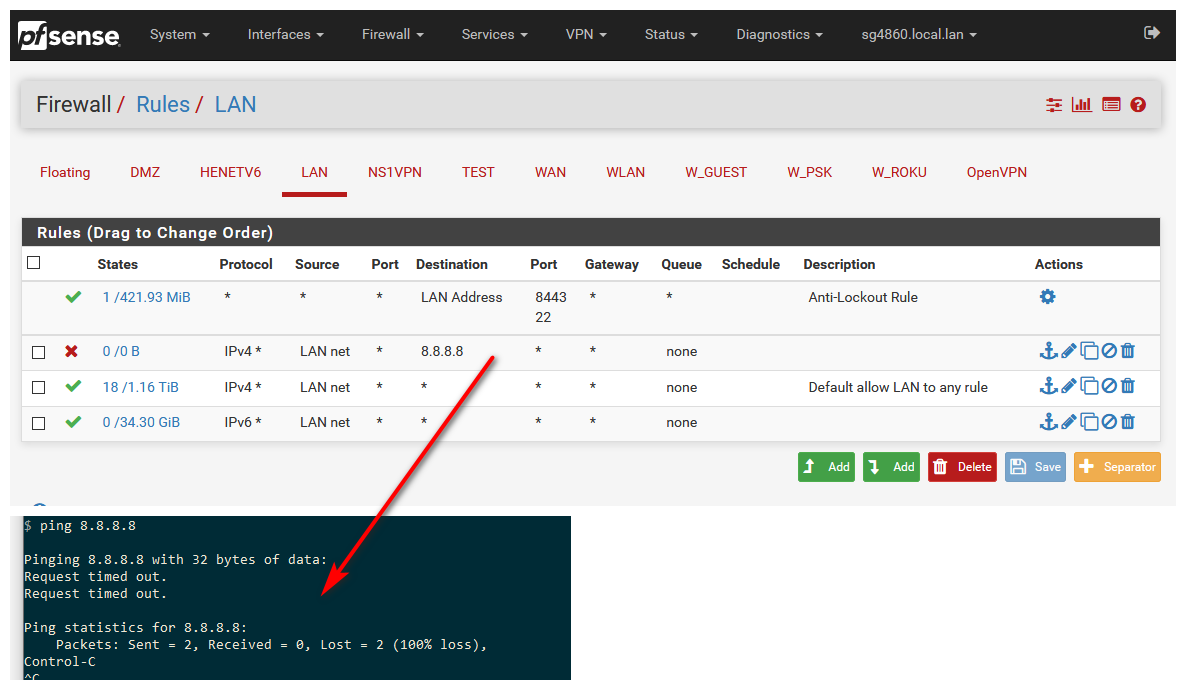
If you want stop your client from talking to an IP, you would put that rule on your LAN, not your wan.. Once you let a client talk to something, then the state would allow the answer.
If you want to show your rules its just easier to post a screen shot, then its a 2 second view on our part to understand what you have done.
-
That's my rules. I don't want to stop the clients only. I want to stop clients and the router as well. And 8.8.8.8 is just example. In fact, the rules just dont work on WAN. I've got lot of addresses blocked in pfblocker, but there are not. Like 2.21.98.84 (In Africa ipv4 list) - blocked for clients, but is not for the router (pfblocker add rules in both interfaces with action "block"). I've got ping and i'm sure they have to me as well. -
Not sure what you think rules on the WAN are going to do??
Out of the box ALL unsolicited traffic to your wan IP is dropped.. You do not have to do ANYTHING for this to happen..
I can not even tell what interface those rules are on.. Just attach the images here.. How hard is it to show your rules?
and the router as well
You mean pfsense? You can not stop pfsense from talking to what it needs to talk to.. The only thing its going to talk to is checking for updates..
If you want to stop client from talking to ip 1.2.3.4 then those would go on your LAN.. Rules on your wan would only stop IP 4.5.6.7 from accessing some port forward you had open. If the block was above where your port forward rule was.
Since you have Zero port forwards - every single one of those rules on your WAN are 100 percent POINTLESS!!!
-

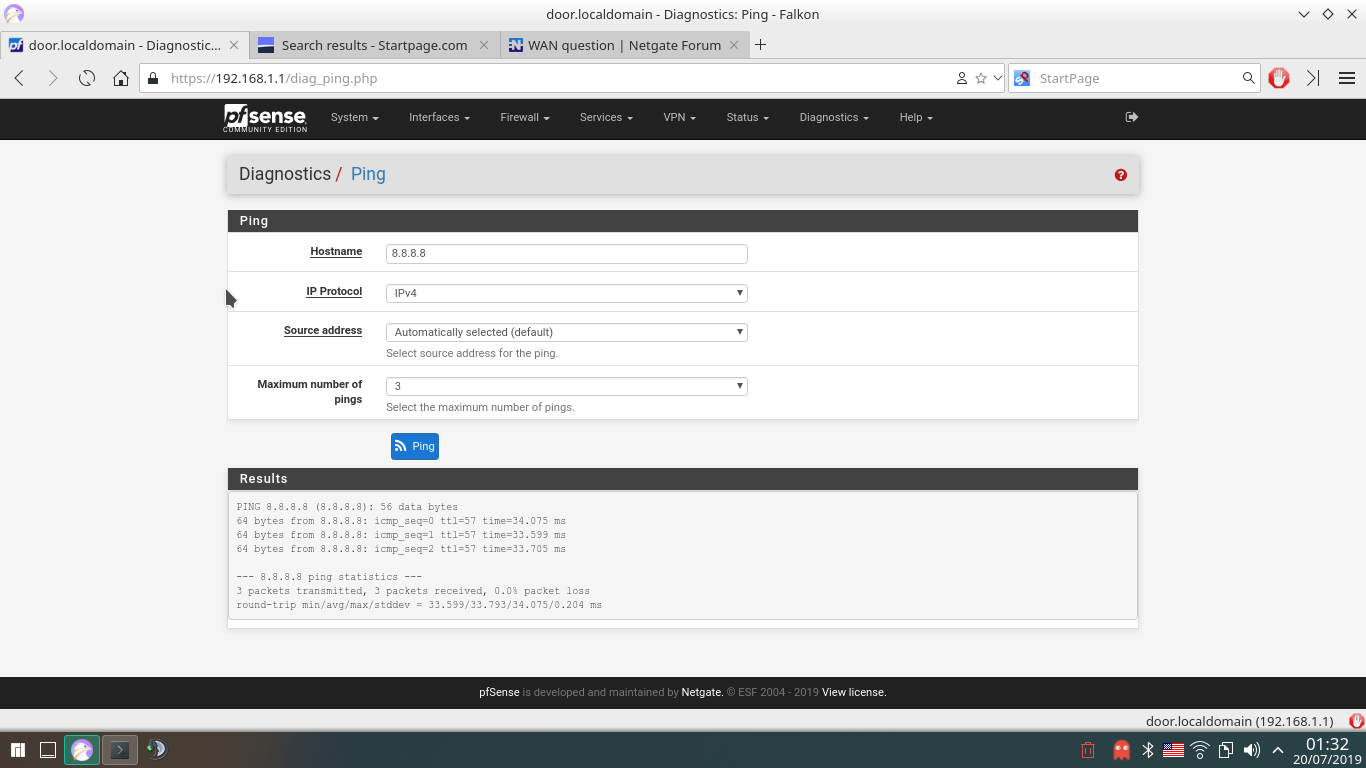
That's after states restart and computer restart."Since you have Zero port forwards - every single one of those rules on your WAN are 100 percent POINTLESS!!"
So, hot to fix it? What port to forward to where?
-
Not sure what your not understanding.. What are you wanting to stop.. Your clients from talking to Asia? Then those rules would go on your LAN, not your wan.
And again you can not stop pfsense from talking to the internet.. There are 2 rules that not shown in the gui
pass out inet all flags S/SA keep state allow-opts label "let out anything IPv4 from firewall host itself" pass out inet6 all flags S/SA keep state allow-opts label "let out anything IPv6 from firewall host itself"If users could stop firewall from talking to the internet - the forum would be flooded with users breaking their shit! ;) hehehe
If you want to stop a client on your lan from talking to 8.8.8.8 then put that on your LAN..
Rules are evaluated as traffic enters interface, top down, first rule to trigger wins, no other rules are evaluated.
https://docs.netgate.com/pfsense/en/latest/firewall/firewall-rule-processing-order.html
-
@johnpoz said in WAN question:
And again you can not stop pfsense from talking to the internet..
Tha's what i can not understand. I'm not able to control the traffic of my computer? Come on.. Come on.. Cannot be true... It's very simple. I want to block all my computers to the IP list. Not desktops, phone only - all of them including the router.
-
And I showed you the rules.. Pfsense is the your ROUTER!! It is your firewall!! Traffic "IT" creates you can not stop..
"IT" needs to create the nats for your client behind it to talk to 1.2.3.4 on the internet.. If the rules was not how would it do that, etc..
You can stop devices behind pfsense from doing whatever you want, but you can not block pfsense itself from talking to the internet.. It doesn't talk to the internet.. It ONLY checks for updates..
I showed you exactly how to block any computer on your network from talking to the internet - its simple rules you put on the LAN interface of pfsense.. Since this is were the traffic enters pfsense to "get" to the internet.. If you want to block something this is where it is done.. NOT on the internet side "wan"
-
Thank you for your answers! It's not just updates, but also NTP, packet downloads etc. . What's the idea of WAN rules? And, if i'm using encrypted DNS, how to block anything to not going outside WAN on port 53? Or... i wan't to block port 123 on pfsense?
-
Its only going to check ntp, if you enabled it.
Wan rules are to "allow" stuff ;) out of the box all interfaces DENY all unsolicited traffic.. You have to create rules to allow traffic. If you forward something, say you were running a web server on IP behind pfsense 192.168.1.100 for example, and you wanted allow all but IP 1.2.3.4 from talking to this server behind pfsense. You would create a port forward, and above that you would put a block for of 1.2.3.4.. Rules evaluated top down, first rule to trigger wins! Read the link I provided on order of firewall rules evaluation.
Out of the box all inbound to the wan is denied, since there are no rules.
If you want to block stuff behind pfsense from talking outbound on 53, then put the rule AGAIN on your LAN.. this is where clients behind pfsense are stopped from doing something past pfsense.
If you dont want clients to talk ntp, then block it again on the LAN.. If you don't want pfsense to set it time via ntp, then disable ntp.. Remove the ntp servers listed, by default it talks to pfsense pool.
Pretty shitty of firewall logs and any logs that time is not correct ;) If you don't want it to talk to internet for time - setup a local ntp server or use pps, etc. etc.
If users could stop pfsense from talking outbound, I know for a freaking fact the forum would be flooded - pfsense can not get an IP, client can not talk to the internet, etc. etc.. Because they didn't think it through and stop pfsense from creating outbound connection, you know like asking for an IP address from dhcp server for its wan.
-
Last question. How to protect all my network against port scans, ping etc. to .. let's say couple IPs? If i lake to be incognito? Like 100% incognito. No ping answers, nothing.
-
That is out of the box how it pfsense is - nothing to do for that.. Not sure what part your not understanding about the default deny.. All unsolicited traffic inbound to pfsense wan is just dropped.
