WAN question
-
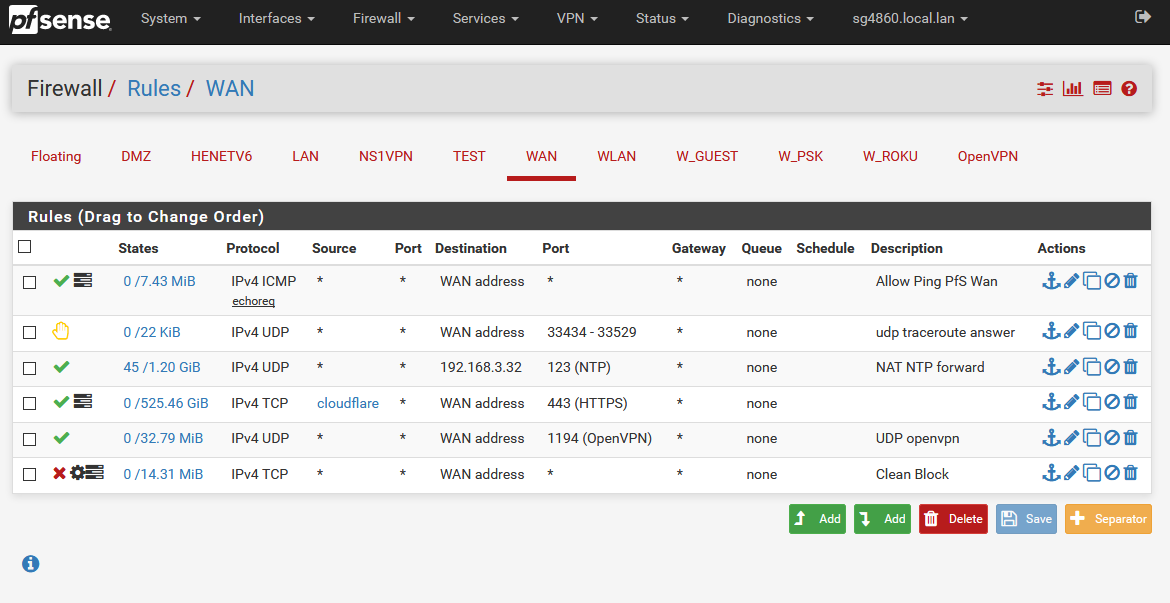
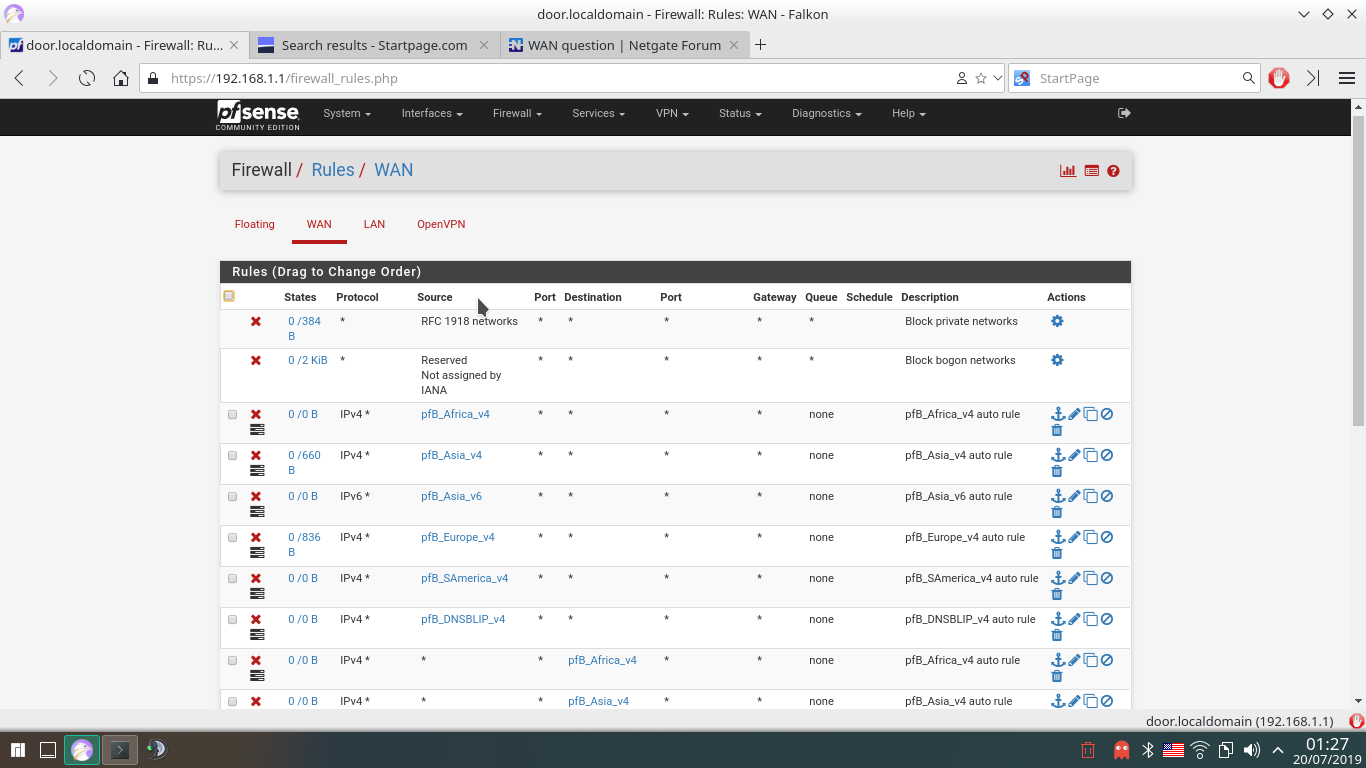
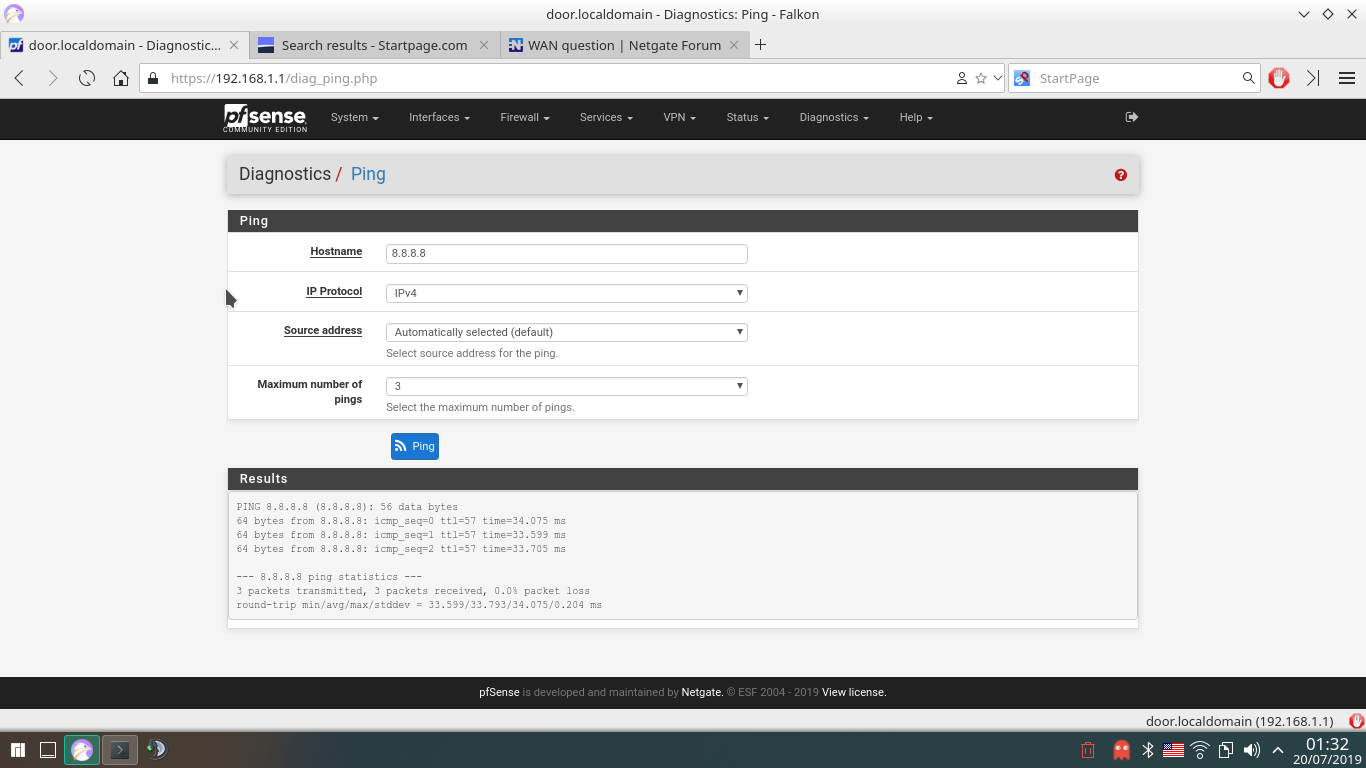
That's my rules. I don't want to stop the clients only. I want to stop clients and the router as well. And 8.8.8.8 is just example. In fact, the rules just dont work on WAN. I've got lot of addresses blocked in pfblocker, but there are not. Like 2.21.98.84 (In Africa ipv4 list) - blocked for clients, but is not for the router (pfblocker add rules in both interfaces with action "block"). I've got ping and i'm sure they have to me as well. -
Not sure what you think rules on the WAN are going to do??
Out of the box ALL unsolicited traffic to your wan IP is dropped.. You do not have to do ANYTHING for this to happen..
I can not even tell what interface those rules are on.. Just attach the images here.. How hard is it to show your rules?
and the router as well
You mean pfsense? You can not stop pfsense from talking to what it needs to talk to.. The only thing its going to talk to is checking for updates..
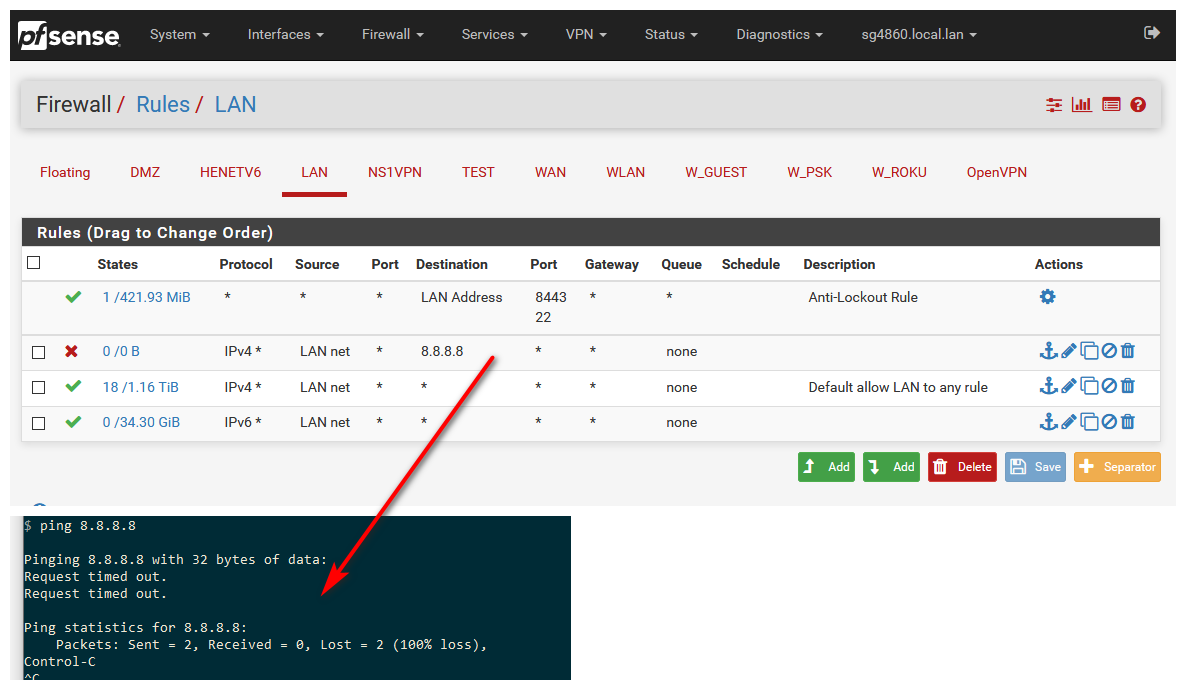
If you want to stop client from talking to ip 1.2.3.4 then those would go on your LAN.. Rules on your wan would only stop IP 4.5.6.7 from accessing some port forward you had open. If the block was above where your port forward rule was.
Since you have Zero port forwards - every single one of those rules on your WAN are 100 percent POINTLESS!!!
-

That's after states restart and computer restart."Since you have Zero port forwards - every single one of those rules on your WAN are 100 percent POINTLESS!!"
So, hot to fix it? What port to forward to where?
-
Not sure what your not understanding.. What are you wanting to stop.. Your clients from talking to Asia? Then those rules would go on your LAN, not your wan.
And again you can not stop pfsense from talking to the internet.. There are 2 rules that not shown in the gui
pass out inet all flags S/SA keep state allow-opts label "let out anything IPv4 from firewall host itself" pass out inet6 all flags S/SA keep state allow-opts label "let out anything IPv6 from firewall host itself"If users could stop firewall from talking to the internet - the forum would be flooded with users breaking their shit! ;) hehehe
If you want to stop a client on your lan from talking to 8.8.8.8 then put that on your LAN..
Rules are evaluated as traffic enters interface, top down, first rule to trigger wins, no other rules are evaluated.
https://docs.netgate.com/pfsense/en/latest/firewall/firewall-rule-processing-order.html
-
@johnpoz said in WAN question:
And again you can not stop pfsense from talking to the internet..
Tha's what i can not understand. I'm not able to control the traffic of my computer? Come on.. Come on.. Cannot be true... It's very simple. I want to block all my computers to the IP list. Not desktops, phone only - all of them including the router.
-
And I showed you the rules.. Pfsense is the your ROUTER!! It is your firewall!! Traffic "IT" creates you can not stop..
"IT" needs to create the nats for your client behind it to talk to 1.2.3.4 on the internet.. If the rules was not how would it do that, etc..
You can stop devices behind pfsense from doing whatever you want, but you can not block pfsense itself from talking to the internet.. It doesn't talk to the internet.. It ONLY checks for updates..
I showed you exactly how to block any computer on your network from talking to the internet - its simple rules you put on the LAN interface of pfsense.. Since this is were the traffic enters pfsense to "get" to the internet.. If you want to block something this is where it is done.. NOT on the internet side "wan"
-
Thank you for your answers! It's not just updates, but also NTP, packet downloads etc. . What's the idea of WAN rules? And, if i'm using encrypted DNS, how to block anything to not going outside WAN on port 53? Or... i wan't to block port 123 on pfsense?
-
Its only going to check ntp, if you enabled it.
Wan rules are to "allow" stuff ;) out of the box all interfaces DENY all unsolicited traffic.. You have to create rules to allow traffic. If you forward something, say you were running a web server on IP behind pfsense 192.168.1.100 for example, and you wanted allow all but IP 1.2.3.4 from talking to this server behind pfsense. You would create a port forward, and above that you would put a block for of 1.2.3.4.. Rules evaluated top down, first rule to trigger wins! Read the link I provided on order of firewall rules evaluation.
Out of the box all inbound to the wan is denied, since there are no rules.
If you want to block stuff behind pfsense from talking outbound on 53, then put the rule AGAIN on your LAN.. this is where clients behind pfsense are stopped from doing something past pfsense.
If you dont want clients to talk ntp, then block it again on the LAN.. If you don't want pfsense to set it time via ntp, then disable ntp.. Remove the ntp servers listed, by default it talks to pfsense pool.
Pretty shitty of firewall logs and any logs that time is not correct ;) If you don't want it to talk to internet for time - setup a local ntp server or use pps, etc. etc.
If users could stop pfsense from talking outbound, I know for a freaking fact the forum would be flooded - pfsense can not get an IP, client can not talk to the internet, etc. etc.. Because they didn't think it through and stop pfsense from creating outbound connection, you know like asking for an IP address from dhcp server for its wan.
-
Last question. How to protect all my network against port scans, ping etc. to .. let's say couple IPs? If i lake to be incognito? Like 100% incognito. No ping answers, nothing.
-
That is out of the box how it pfsense is - nothing to do for that.. Not sure what part your not understanding about the default deny.. All unsolicited traffic inbound to pfsense wan is just dropped.
