[solved] backend server nginx down HAProxy
-
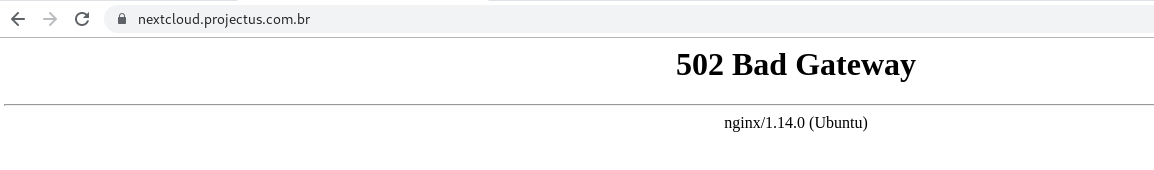
@dragoangel lol lol 502 Bad Gateway
-
@wesleylc1 Why at bottom writed Ubuntu...? You go to haproxy or to nginx and see this?.. In any case: go to nginx straight and check you backend first. It eork? If yes - then fix your healthcheck. If it still not work add header host on backend config of haproxy in case you have in nginx multiple domains on same port-cert
-
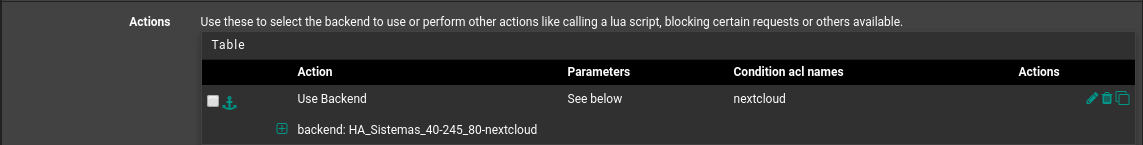
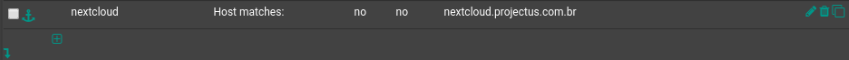
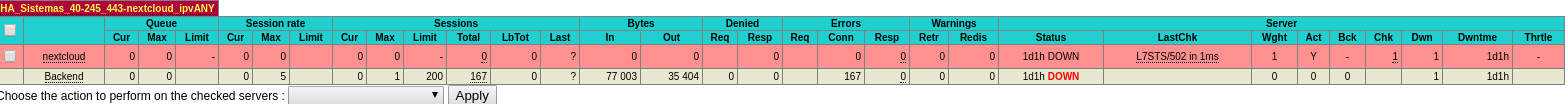
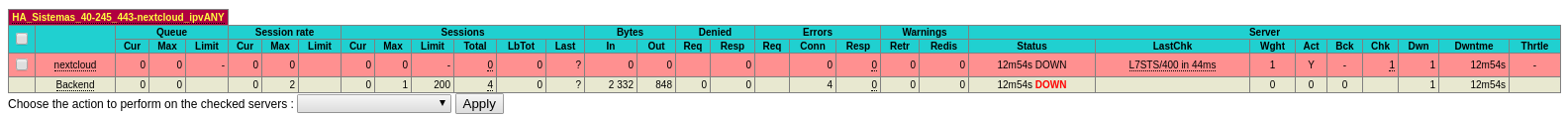
Hi guys, I set up https internally on the nginx server, already responding to https requests on nextcloud.projectus.com.br, now I'm trying to apply backend settings to my front end, which is already configured to use port 443, but my The backend displays the error "L7STS / 400 in 46ms".
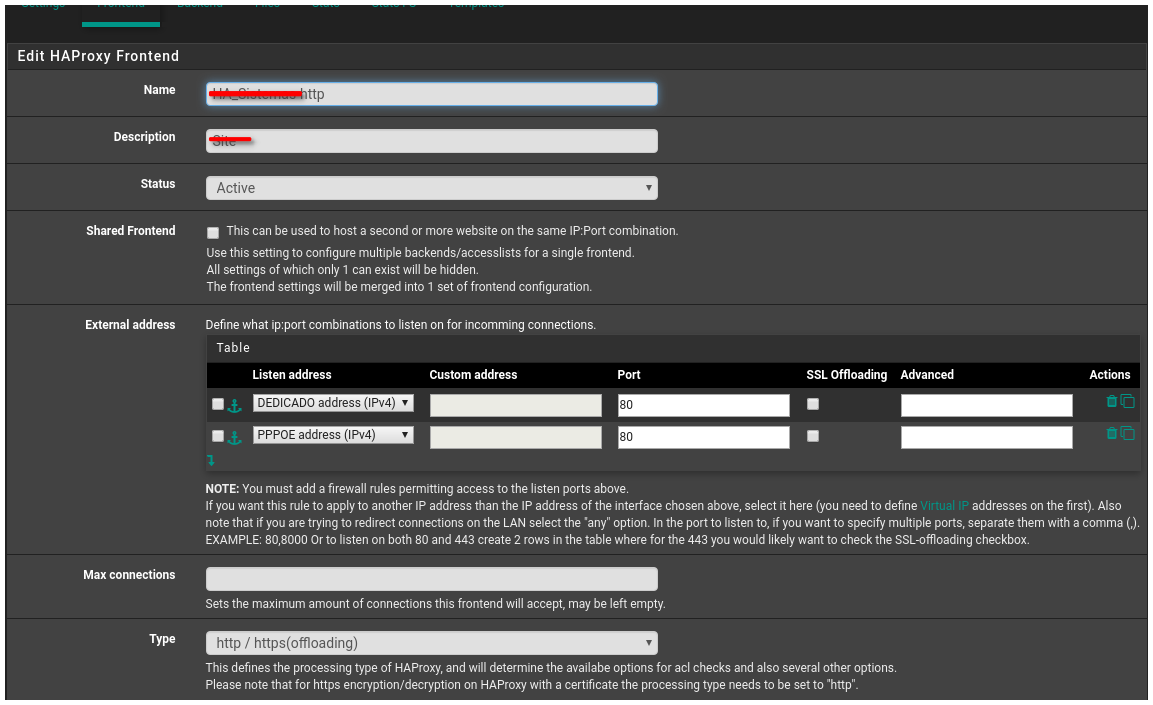
- front end settings
frontend HA_Sistemas-https bind 189.20.108.xx:443 name 189.20.108.xx:443 ssl crt-list /var/etc/haproxy/HA_Sistemas-https.crt_list bind 187.75.209.2xx:443 name 187.75.209.xx:443 ssl crt-list /var/etc/haproxy/HA_Sistemas-https.crt_list mode http log global option log-separate-errors option httplog option http-keep-alive timeout client 300000 acl rootrequested var(txn.txnpath) -m str -i / acl time-sheet var(txn.txnhost) -m str -i time-sheet.projectus.com.br acl qsms var(txn.txnhost) -m str -i qsms.projectus.com.br acl treinamento var(txn.txnhost) -m str -i treinamento.projectus.com.br acl proposta var(txn.txnhost) -m str -i proposta.projectus.com.br acl chamado var(txn.txnhost) -m str -i chamado.projectus.com.br acl pesquisa var(txn.txnhost) -m str -i pesquisa.projectus.com.br acl pesquisa-ce var(txn.txnhost) -m str -i pesquisa-ce.projectus.com.br acl nextcloud var(txn.txnhost) -m str -i nextcloud.projectus.com.br http-request set-var(txn.txnpath) path http-request set-var(txn.txnhost) hdr(host) http-request redirect location /TimeSheet/faces/login.xhtml if rootrequested time-sheet http-request redirect location /SistemaQSMS/ if rootrequested qsms http-request redirect location /Treinamento/ if rootrequested treinamento http-request redirect location /Proposta/ if rootrequested proposta http-request redirect location /Chamado/ if rootrequested chamado http-request redirect location /PesquisaClima/ if rootrequested pesquisa http-request redirect location /PesquisaClimaCE/ if rootrequested pesquisa-ce http-response add-header Content-Security-Policy upgrade-insecure-requests if !time-sheet !qsms !treinamento !proposta !chamado !pesquisa !pesquisa-ce use_backend HA_Sistemas-45-xx_80-www_ipvANY if !time-sheet !qsms !treinamento !proposta !chamado !pesquisa !pesquisa-ce default_backend HA_Sistemas_40-xxx_443-nextcloud_ipvANY default_backend HA_Sistemas_43-xxx_8443_ipvANY- backend settings
backend HA_Sistemas_40-xxx_443-nextcloud_ipvANY mode http id 109 log global timeout connect 30000 timeout server 30000 retries 3 option httpchk OPTIONS / server nextcloud 192.168.40.xxx:443 id 108 ssl check inter 1000 verify nonebest regards,
Wesley Santos -
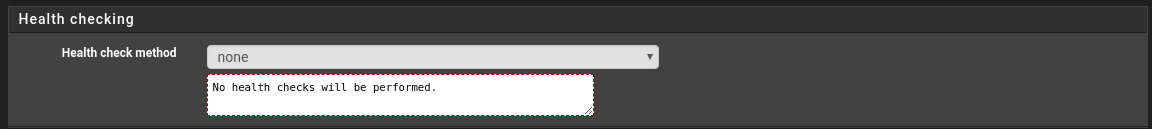
@wesleylc1 Try disable healthchecks for beginning
-
-
@wesleylc1 yes. That it. Try opening you frontend domain
-
@dragoangel No external access yet.
-
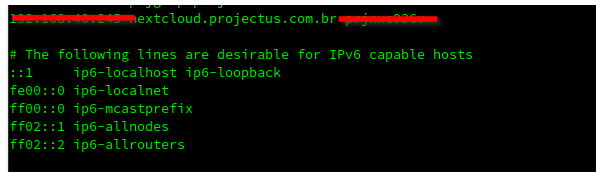
@wesleylc1 No big matter, open internal haproxy address. Align your pc /etc/hosts file to resolve domain for test, or use unbound for point to internal ip, or etc
-
@dragoangel internally it is accessible to the web page through the https protocol.
I even set the line below on my network gateway.
best regards,
Wesley Santos -
@wesleylc1 You accessing nginx or haproxy now? Print nslookup domain.com output plz
-
@dragoangel This access is being made from my LAN subnet, below the nslookup output.
nslookup nextcloud.projectus.com.br Server: 192.168.45.11 Address: 192.168.45.11#53 Non-authoritative answer: Name: nextcloud.projectus.com.br Address: 189.20.108.xxbest regards,
Wesley Santos -
hm... you said that you access it locally, but domain resolving goes to public IP
-
The resolution is pointing to the public IP, because my DNS provider is external.
-
@dragoangel said in backend server nginx down HAProxy:
You accessing nginx or haproxy now
You accessing nginx or haproxy now??
-
I do not understand, can you explain again?
-
 facepalm.
facepalm.@wesleylc1 said in backend server nginx down HAProxy:
@dragoangel internally it is accessible to the web page through the https protocol.
You opened connection to NGINX or HAproxy?? Try change healthchecks to GET /
-
@dragoangel My problem may be that my front end already uses another default backend?
I had already made changes from OPTIONS to GET and HEAD, for example, using https there was no success, already using http went well.
-
you musn't use "default backend". This bad practice. All time use only ACLs to assign backend.
-
I use a default backend for https systems and assign to these sites through acls.
-
@dragoangel @PiBa Hi guys !!
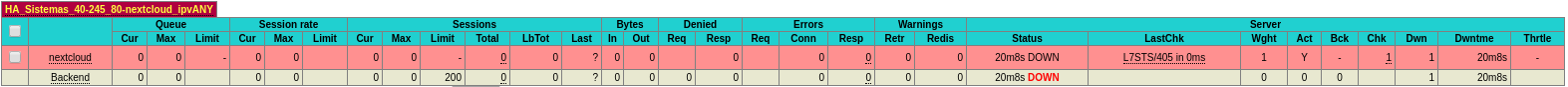
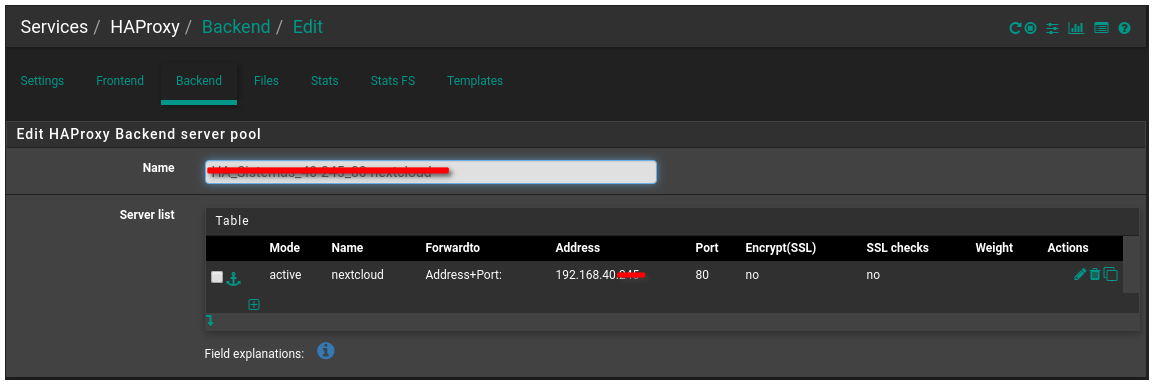
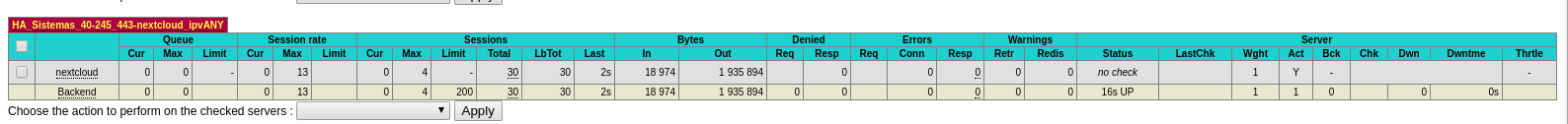
I deleted entries 443 from this backend and made new settings using 80, the image below the backend communicates successfully.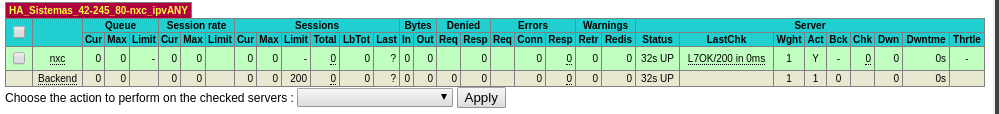
I really need to publish this site, I will be very grateful if you help me.
best regards,
Wesley Santos