[Solved] Ooma not working
-
Ooma's not Voip the way Freepbs is.
its a box that plugs into network. Has a phone jack on the back next to lan port.If this doesnt matter, why did it matter with cisco router?
i dont have a VoIP tab up there, or routing, i only have, floating, wan, lan, and opt1 and 2. How do i get that up there ?
-
I showed you an example. You need to use a little logic. Whatever interface your phone thing is plugged into has to have access through the interface. The above example is how you do it.
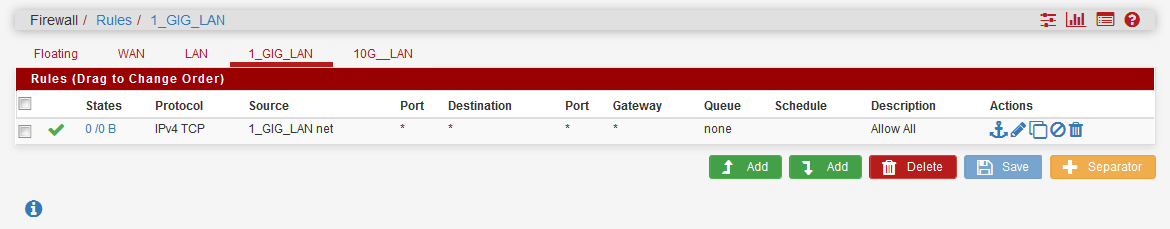
Can you show a screenshot of your interface rules?
-
-
saw my pic and went in to change protocol to any
-

-
didnt work.
Do i need the Voip tab with a rule for a half assed Voip ??
-
No. Devices do not care what you name your interface. Your device simply needs its internet access. If you plug in a computer into these ports does it get out to the internet?
-
5 port switch had Ooma, port 2 an 3 are Rokus and port 4 is FireTV. Already swappped devices in ports, everything connected exept ooma
-
Does the Ooma have to go out for a TFTP transfer in order to work? You may need to adjust and use the TFTP proxy..
-
not sure. Theres no real documentation on config other then plug into router, turn on, make calls 5 min later
It worked fine with dhcp from cisco router, i dont get it. Other then it not plugged into pfsense, but a switch first
-
Well- VOIP was never intended to be behind any kind of NAT when first implemented. It was hacked into the spec later when services like Vonage came around.
You are trying to double NAT right now. Im not sure why it works with some and not with others but that is the case.
But you could try putting some inbound firewall rules in place pointed at the Ooma device address. You need to find out what the device is trying to connect to by looking at your state table and watching firewall logs.
Who is your VOIP provider?
-
Also- go to System/Advanced.. /system_advanced_firewall.php on your firewall.
Down to "Network Address Translation"
"TFTP Proxy"
Select the interface your Ooma resides on.
Down to the bottom of the page and click "save"
I do not know if you need a reboot or not.
See if that helps.
-
OOma, theyre kinda like vonage
-
Ok..
I thought OOma was just the device.. Im a Voipo guy so know them best..
Let me see if I can find some server info..
-
This post is deleted! -
From system/logs/dhcp : the last 3 lines. Firewall logs have nothing about ooma 10.15.15.2
Jan 13 17:42:05 dhcpd reuse_lease: lease age 1514 (secs) under 25% threshold, reply with unaltered, existing lease for 10.15.15.2
Jan 13 17:42:05 dhcpd DHCPREQUEST for 10.15.15.2 from 00:18:61:2e:8e:7f (myx_0018612E8E7E) via igb1
Jan 13 17:42:05 dhcpd DHCPACK on 10.15.15.2 to 00:18:61:2e:8e:7f (myx_0018612E8E7E) via igb1I did turn on Nat
-
Did you have to make rules for Voipo ?
-
Yep
Inbound rules with the phone as the destination.
Server SIP and RTP ports. No port forwards only firewall rules. I do it with all my customers.
Otherwise SIP traffic can sometimes look like unsolicited traffic and get blocked.
-
ok, where do i dind those ??
-
Looks like the device connects via a VPN..
https://support.ooma.com/home/problems-connecting-to-setup-ooma-com/
Follow this and see. You have to plug into their port.