pfSense and meraki z3
-
I'm fairly new at doing all the settings with pfSense. How would I make changes in pfSense to let this "sneak" through.
Thanks again.
-
-
I find it very hard to believe anything that is intended as a work-from-home type device cannot connect from behind NAT.
Many, many IPSec connections work just fine behind NAT.However that doc site is just giving me a protocol error right now so I can't check it.
https://www.reddit.com/r/meraki/comments/bj24na/z3_behind_home_router/
Steve
-
I'm successfully using a Meraki Z3 at home behind pfsense with NAT. To get it working I needed to add a couple of outbound NAT rules to get around an "unfriendly NAT issue". If you have access to the Meraki dashboard for the organisation, you can see if you are getting the same unfriendly NAT issue on the VPN Status screen for your network.
The fix for me was to add these rules in pfsense:
- Firewall - NAT - Outbound
- I set my mode to Hybrid outbound.
- Add 2 Mappings
Interface WAN, source Z3_IP or *, udp/ * , Destination *, udp/9350, NAT address WAN Address, Nat port *, Static port Ticked.
Interface WAN, source Z3_IP or *, udp/ * , Destination *, udp/7001, NAT address WAN Address, Nat port *, Static port Ticked.
Further reading:
https://documentation.meraki.com/MX/Site-to-site_VPN/Troubleshooting_VPN_Registration_for_Meraki_Auto_VPN
https://docs.netgate.com/pfsense/en/latest/nat/static-port.html -
@chris147 said in pfSense and meraki z3:
I'm successfully using a Meraki Z3 at home behind pfsense with NAT. To get it working I needed to add a couple of outbound NAT rules to get around an "unfriendly NAT issue". If you have access to the Meraki dashboard for the organisation, you can see if you are getting the same unfriendly NAT issue on the VPN Status screen for your network.
The fix for me was to add these rules in pfsense:
- Firewall - NAT - Outbound
- I set my mode to Hybrid outbound.
- Add 2 Mappings
Interface WAN, source Z3_IP or *, udp/ * , Destination *, udp/9350, NAT address WAN Address, Nat port *, Static port Ticked.
Interface WAN, source Z3_IP or *, udp/ * , Destination *, udp/7001, NAT address WAN Address, Nat port *, Static port Ticked.
Further reading:
https://documentation.meraki.com/MX/Site-to-site_VPN/Troubleshooting_VPN_Registration_for_Meraki_Auto_VPN
https://docs.netgate.com/pfsense/en/latest/nat/static-port.htmlHi Chris.
I'm new at setting up rules. I have a few questions, if you don't mind:
- What option do I choose for source & destination (Any, this firewall or network)?
- Do I need to know the IP of the Z3?
- Will the source and destination ports be the same? In the further reading you provided it shows the source port as 60032 and the destination as 9350.
- Would the source port of 60032 be the same for the 7001 destination port?
- How would I determine/know what the destination network is?
Sorry for all the questions, but quite new at this.
Thanks for all your help
-
I'm with @stephenw10 on this. A device intended for use behind a home firewall shouldn't be so difficult to set up. However, in reading that info I provided, I get the impression it's supposed to be used in place of a home router/firewall. This would put it directly on the Internet, avoiding any problems with NAT. Several years ago, I set up something similar, for companies who moved employees to home offices. They had firewall/routers that were intended to be directly connected to the ISP. They also ran IPSec, as that box does. Does you're wife's employer provided VPN software on the computers, as many do?
-
Yes, you need to know the IP address on the Z3 because you will want to use the as the source IP in your new outbound NAT rules. So you will want to set it as a fixed dhcp lease:
https://docs.netgate.com/pfsense/en/latest/dhcp/dhcp-server.html#static-ip-mappingsReboot the Z3 so it pulls the new IP from your static mapping.
The destination IP can be 'any' or it could be the IP the VPN is connecting to if that is fixed (and you know what it is!)
The source and destination ports are almost never the same. Leave the source port as 'any' set the destination port to the two ports Meraki are using which seem to be 7001 and 9350.
You could use a ports alias here with both ports in it. Or you can just add two rules, one for each port.Steve
-
@wyzard said in pfSense and meraki z3:
Hi Chris.
I'm new at setting up rules. I have a few questions, if you don't mind:
- What option do I choose for source & destination (Any, this firewall or network)?
- Do I need to know the IP of the Z3?
- Will the source and destination ports be the same? In the further reading you provided it shows the source port as 60032 and the destination as 9350.
- Would the source port of 60032 be the same for the 7001 destination port?
- How would I determine/know what the destination network is?
Hi,
As I understand it, pfsense rewrites the source port for udp/9350 and udp/7001 as a security measure to mitigate fingerprinting the hosts behind it, in a way that ISP home routers don't. It doesn't do this for udp/500 by default to allow VPN to work. The two NAT mappings are to have pfsense not rewrite the source ports when NATing traffic on those destination ports.
- Source and destination I have set to Type: Any. I guess I shouldn't though, see 2.
- You should give your Z3 a reservation in DHCP. Then in the mappings for the source use Type Network and the IP address /32.
- I have the source port left blank in the mapping, and destination port as 9350 in one mapping, and 7001 in the other.
- I have blank for the source port. Looking at my current state table, the source port is not using 60032 so I guess it changes.
- I have the destination set to any. You could ask the IT department for the IPs of the devices the Z3 is connecting to at their end, to lock it down further.
One other thing, you might have to reset the pfsense states to re-establish everything. In pfsense, diagnostics - states - reset states.
I'm fairly new to pfsense too, so if anyone has advice on doing this better, please let me know.
Your wife could ask the IT department what they can see in her Meraki dashboard VPN Status screen. If it's partially working, any error there might help you get the Z3 on line.
-
Generally it's a bad idea to set outbound NAT rules with source 'any'. You can easily end up catching traffic you didn't want to like traffic from the firewall itself.
It's better to set the rule as tightly as possible, so only the VPN traffic from the Z3 in this case, but you should at least set the LAN subnet as source there. If you copy the existing IPSec port 500 rule changing only the destination port you should be good.Steve
-
My wife's IT department is refusing to help with the issue. So far I'm not able to get out past the pfSense. I know the Meraki is handing out an IP as I connected directly to my laptop (without it being connected to the internet) and got an IP.
Wondering if i should assign a static IP address to the computer they provided from my wife's work if that would get me around this issue, as that computer doesn't seem to be getting an IP from the Meraki (for whatever reason).
Any other thoughts and help would be appreciated.
Thanks.
-
@wyzard said in pfSense and meraki z3:
Any other thoughts and help would be appreciated.
If your ISP is like mine, you may have a 2nd IP address you can use. My cable modem is in bridge mode and I can get 2 IPv4 addresses. I normally use 1, but occasionally use the other for testing. Give it a try and see if that happens.
-
@stephenw10 Thanks for the advice, I've cleaned up my rules and combined them into to a single one using a fixed source IP for the Z3 and a port alias. I left the destination address as any because traffic to destination port 9350 goes to a couple of Meraki IPs, which I guess could change. Traffic to port 7001 goes to my workplace.
Anyway, it's working OK with the single tighter rule.@wyzard
Shame on that IT department.
As @JKnott said, perhaps it's time to try taking pfsense out of the mix. If you dig out your old ISP router and try that, will her IT department then support getting the PC and Z3 online? Once you have the PC working, then you can re-introduce pfsense. -
@wyzard Show us the outbound NAT rules you have right now, get a screenshot.
Adding the correct rule(s) should be you need there.
Steve
-
I know bypassing the pfSense box would more than likely get a connection. I appreciate all the help everyone has provided. Would really like to get this working without having to go through the bypassing. Especially since my equipment is in the basement, the house is wired and my wife's office is on the 2nd floor.
Chris, I entered your suggestions, but so far, no joy. One qestion, how did you clear up your rules and combine them into a single one? What were the settings and how did you do a port alias?
Thanks.
-
Using a ports alias allows you to use one rule for a number of ports. 9350, 7001 and 500 for example:
https://docs.netgate.com/pfsense/en/latest/book/firewall/aliases.html#port-aliasesIf you can give us a screenshot I'm sure we can get this working for you.
Steve
-
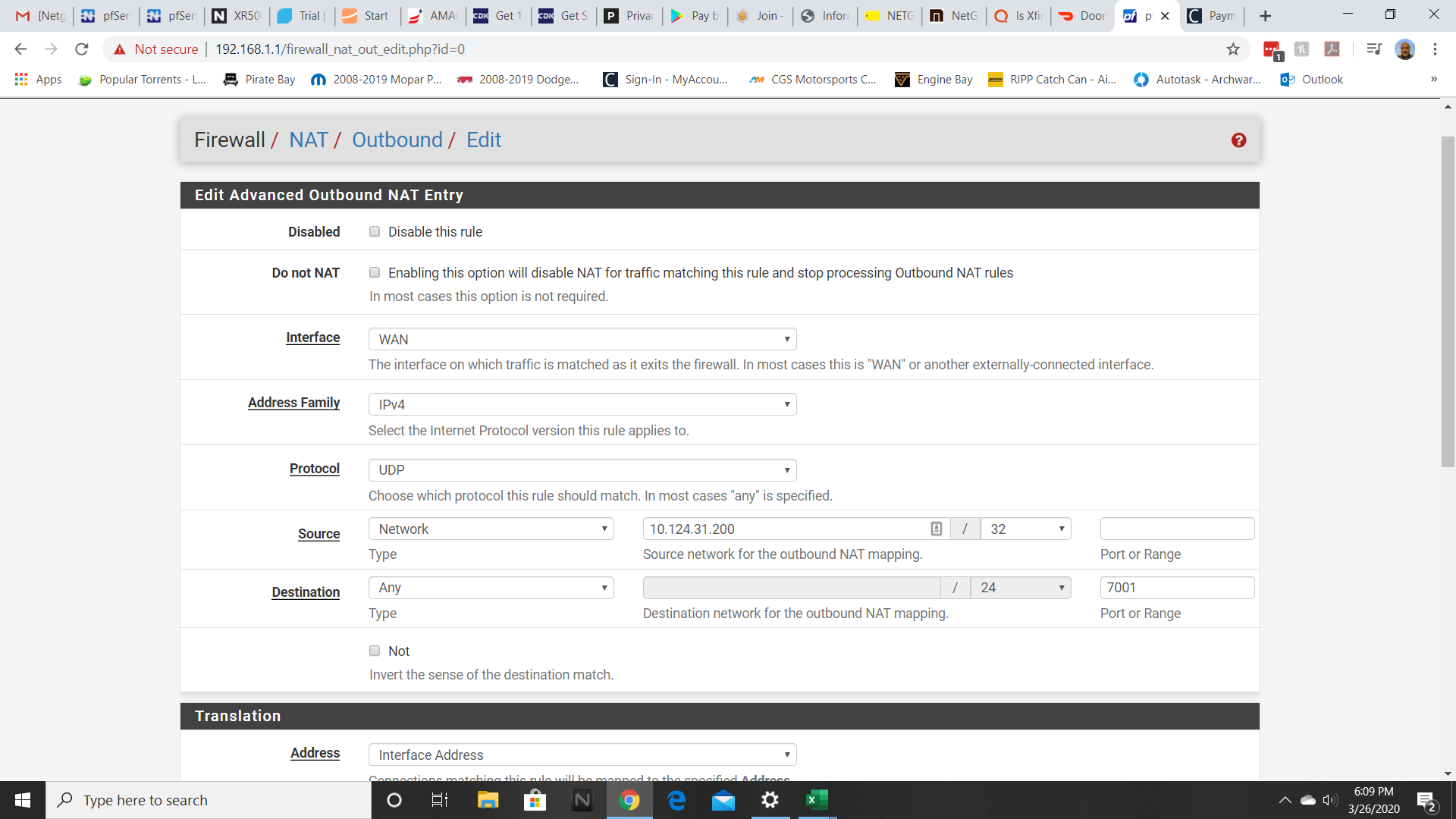
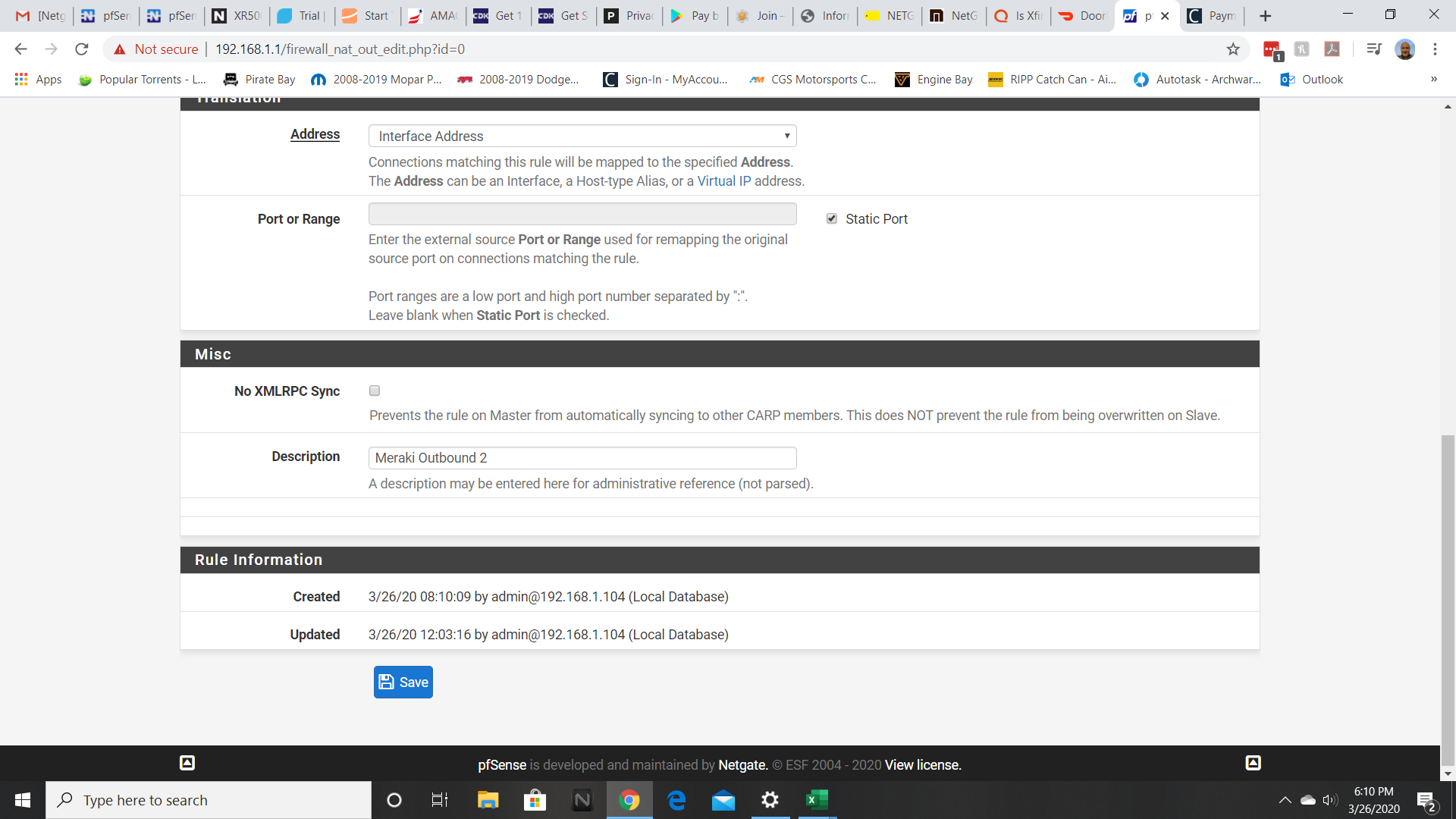
Both rules for 9350 and 7001 ports are the same.
Also, I'm 95% sure that is the ip address of the device.
Appreciate all the help.
-
That looks correct assuming that is the Z3 address.
Check Status > DHCP leases to be sure.You could just set the source as 10.124.31.0/24 to sure it's included. Assuming your internal subnet is a /24 that is.
We are also assuming they are using ports 7001 and 9350. Check the state table for states from 10.123.31.200 to be sure it is.
Steve
-
@stephenw10 said in pfSense and meraki z3:
...We are also assuming they are using ports 7001 and 9350. Check the state table for states from 10.123.31.200 to be sure it is.
@wyzard For reference, here's a sanitized version of what I'm seeing in my state table when filtered for WAN and ports 9350 and 7001. I see a couple of lines for both ports with different destination IP addresses. You can see that the source port is the same for the Z3 and WAN IPs. Before the NAT mapping was in place, those source ports were different.
2x
WAN udp WAN_IP:43830 (Z3_IP:43830) -> MERAKI_DEST_IP:9350
2x
WAN udp WAN_IP:43830 (Z3_IP:43830) -> BUSINESS_DEST_IP:7001 -
Ok, that looks correct. In terms of the ports at least. I would expect that to work as long as the Z3 is actually configured correctly. I assume it is not though?
Can you get any sort of connection status or logs from anywhere?
Steve
-
Still no luck. Verified the static IP of the Meraki. Also verified the ports. When I watch the activity it indicates that it's attempting to authenticate, the authentication failed. Still at a loss.
Again, I appreciate all the help.