I made a WireGuard package for pfSense
-
@Ascrod It looks like I'm almost there. But missing some routing.
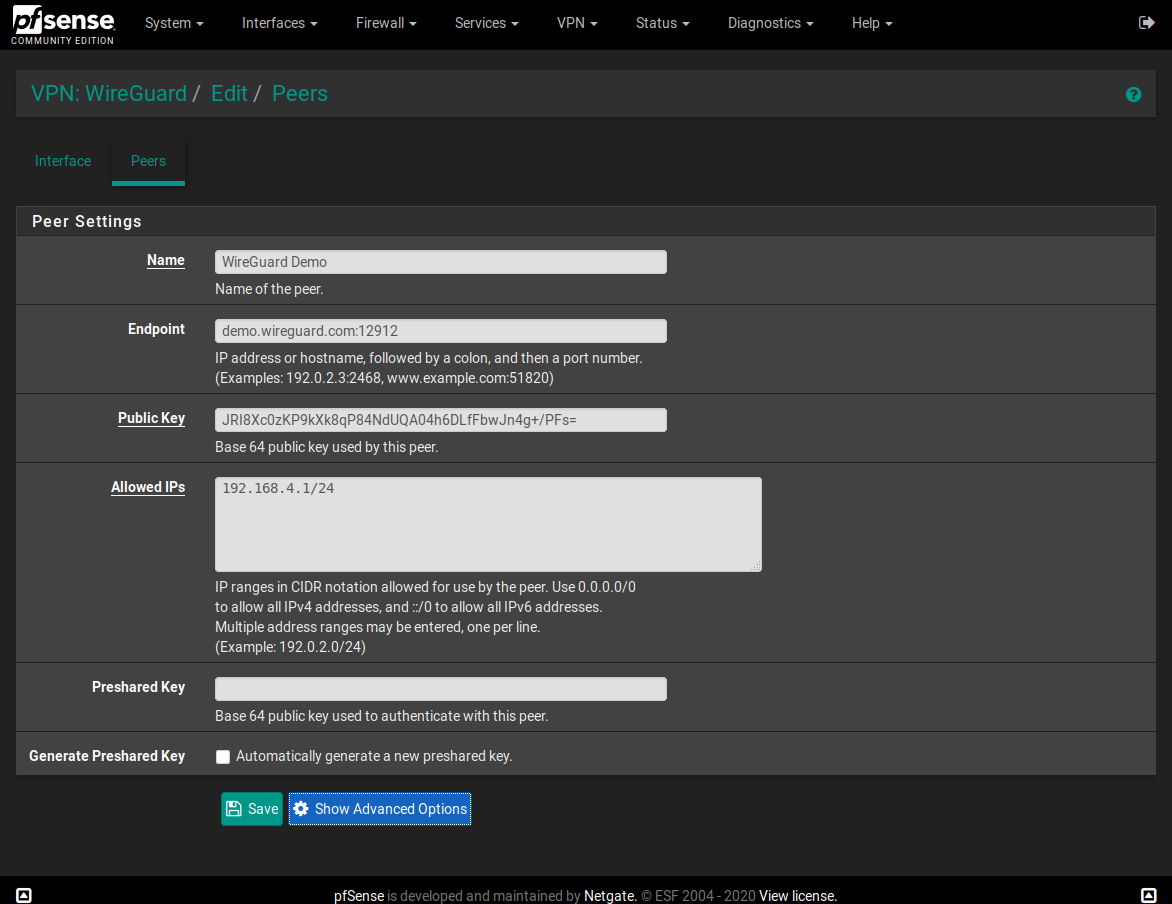
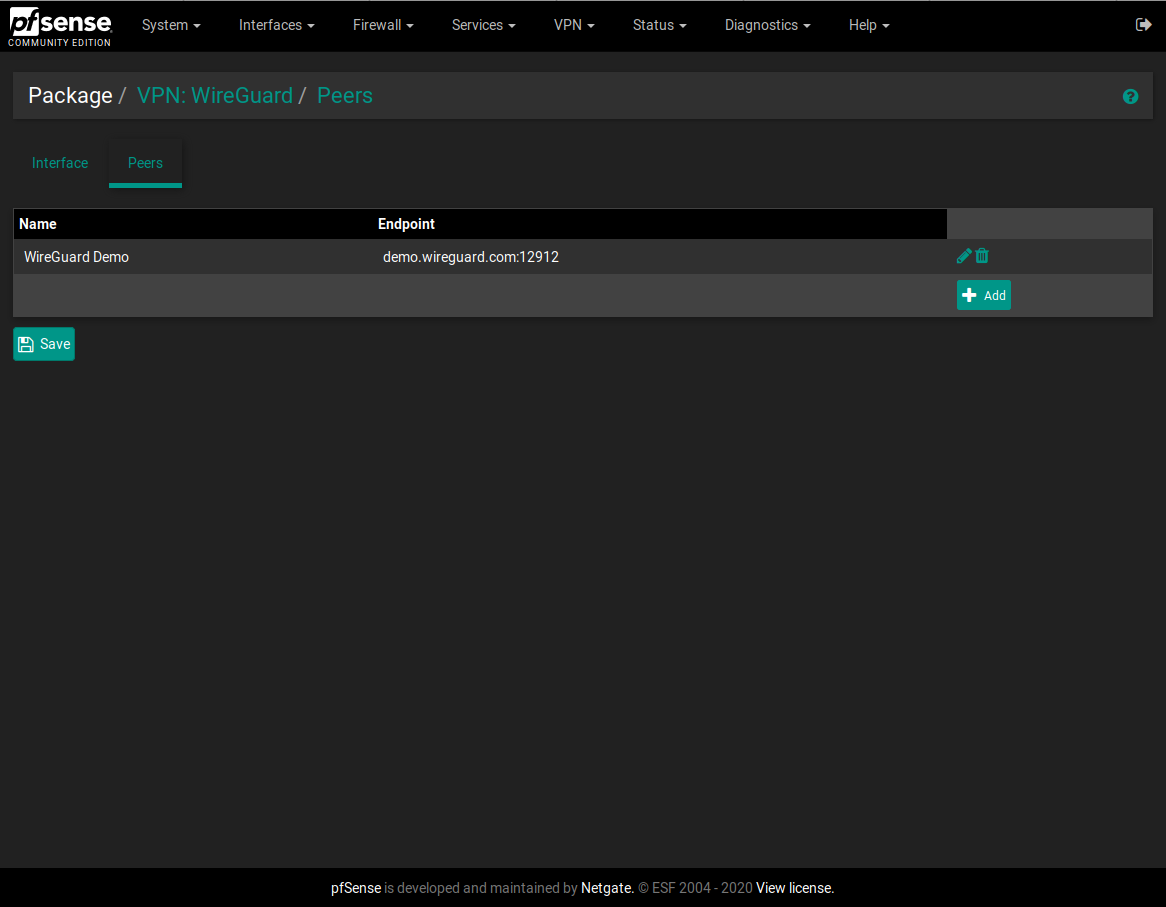
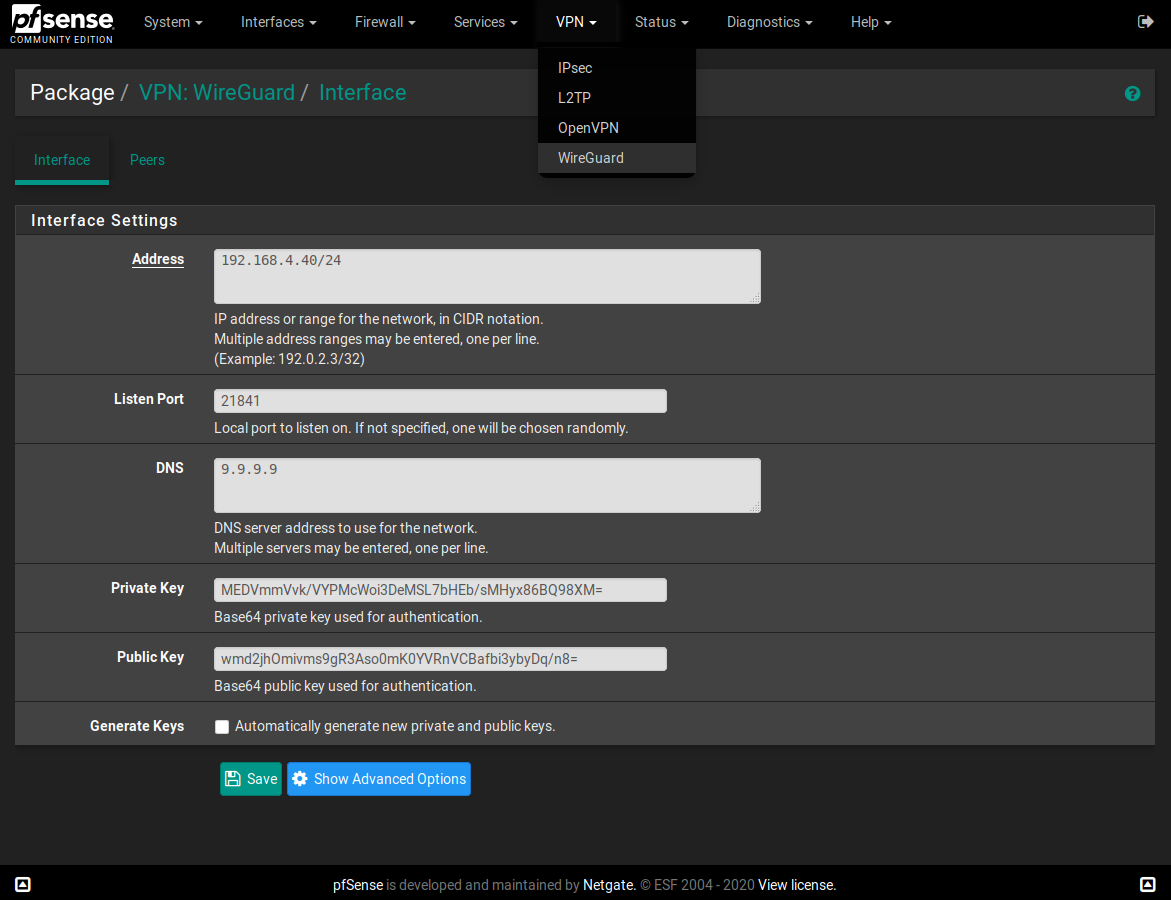
Here is my setup.Pfsense WG config: I've hidden real keys. But still showing which keys are used where
[Interface] # Generated by pfSense Address = 10.100.100.1/24 ListenPort = 51830 DNS = 10.0.0.1 <----- Pfsense local LAN IP PrivateKey = xxxxxxxxxxxxxxxx [Peer] # phone PublicKey = cccccccccccccccccc AllowedIPs = 10.100.100.2/32 [Peer] # IPAD PublicKey = vvvvvvvvvvvvvvvvv AllowedIPs = 10.100.100.3/32Client config of Android Phone
[Interface] Address = 10.100.100.2/32 DNS = 10.100.100.1 PrivateKey = dddddddddddddd [Peer] AllowedIPs = 0.0.0.0/0 Endpoint = my_ddns.com:51830 PersistentKeepalive = 21 PublicKey = ccccccccccccccccccNow im not sure which and where i need to add the rule for the vpn interface. Is it under NAT and port forward from WAN to OPT4 Address? OR is it under NAT> Outbound?
Note my above config works fine if i move that to my ubuntu wireguard server and simply forward UDP port 51830 from pfsense to my ubuntu machine IP.. NOTE: For testing purpose im using the same private and public keys on my ubuntu wireguard server and this one im trying to setup on the PF box. I believe that should not be an issue? Thanks for your helpI tried the following rule but i dont think thats correct
If i tcpdump on my pfsense internet side(WAN) interface, i see constant incoming connection attempts from phone and then the pfsense reponding back to the phone from the WAN interface.
But if I trace on the TUNWG0 interface i only 1 request from 10.100.100.2(Phones vpn ip) to the pf sense WAN inteface.
This is the furthest ive been able to get now. From the pfsense and from my LAN devices, i can ping the phone's vpn ip(10.100.100.2) but thats it. I cannot ping LAN IPs, lan DNS, 8.8.8.8 etc from the phone. -
Please help me to install on 2.5...
-
@murzik 2.5 or you mean 2.4.5?
-
2.5.0
file in repository built for FreeBSD 11, so I am getting an error trying to install on Pfsense 2.5.0 -
@alirz Your configs look all right. I can't see your NAT rule, but if you already have one set up for your server then the only modification you would need to make to it (or a copy of it) is to have it redirect to the VPN interface address instead of the server address and making sure the associated firewall rule updates accordingly.
-
@murzik As stated above, you need wireguard packages for the version of FreeBSD that corresponds to your pfSense version. 2.5.0 is based on FreeBSD 12.
-
@Ascrod I did attach the links to google photos for a screenshot of my interface page and one showing the port forward tule in my post above.
By the way, I’m using the packages listed above on my 2.4.5 pfsense. That should be ok right? I didn’t rebuild them or anything.i simply installed the ones listed above. Even though they are for 2.4.4. But seems as one poster mentioned, they work on 2.4.5 also? -
ok. i got it to work. Had to add two rules.
One on the WAN rule to allow inbound on the WG portStates Protocol Source Port Destination Port Gateway Queue Schedule Description Actions 0 /2.67 MiB IPv4 UDP * * WAN address 51830 * noneSecond FW rule for my WG interface(OPT4) in my case
Firewall >Rules >OPT4 States Protocol Source Port Destination Port Gateway Queue Schedule Description Actions 15 /9.99 MiB IPv4 * * * * * * none Wireguard vpnBased on DNS leak checks, looks like all traffic from my phone is now going through the home internet as it should. I can also access my Lan network devices etc.
-
@alirz Well After my brief success, something is not right again. DNS is not working. I can ping everything over the vpn via IPs but not my hostname.
perhaps at some point something was working and active sessions probably led me believe that everything was working. But eventually when either those states/sessions expired or when i rebooted the FW just to be sure, at some point DNS stopped working.
I really wish routing for this was simple. -
@alirz I've had some issues with DNS occasionally not working after a reboot. Try restarting the DNS service; I believe that's what I've had to do the last few times.
-
@Ascrod OK that fixed it..thats strange though. Ive done several reboots and it didnt do anything. So is there some sort of race condition going on here that the DNS service on pfsense needs to restarted once more after a reboot? Sucks as this kind of makes it a bit unreliable!!
i am also running openvpn server on the pfsense...Does that show affect this?
Any fix for this DNS issue? perhaps add a startup script to restart DNS shortly after a reboot is done? -
ok so i used the "shellcmd" package that can launch commands during/after boot.
I added the following command in there to run after reboot.sleep 30 && pfSsh.php playback svc restart unboundHad to put a sleep because restarting dns right after reboot doesnt fix the issue.
Wish this get resolved eventually when this whole thing makes it into PFsense officially. I dont like these patchy fixes that i lived with for years when i was suing dd-wrt/openwrt years ago. -
Do we know of the dns issue is related to the unbind DNS server or to the wireguard models? If later, is there a newer build of wireguard available?
-
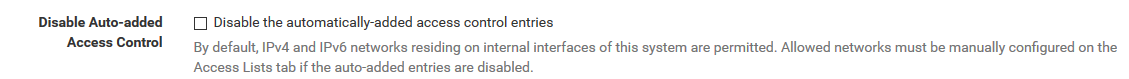
Thanks for your work on this @Ascrod !! I've just set it up and working nicely. I also had the DNS issue after reboot. I suspect it is because the wireguard interface IP address is not set when the DNS resolver is started. pfSense's Unbound defaults to only responding to internal subnets. See this setting;
I suspect adding the wiregaurd subnet on the Access list tab of the DNS resolver will work as a acceptable workaround (haven't tried this yet). -
@Ascrod echoing what @S762 said, suggest you add "pkg install bash" and reorder the above (wireguard-go needs to go before the wireguard package). Otherwise, these steps worked well for me to set up.
I wonder if we could auto-detect an unused (RFC1918) subnet, select a random port and generate server keys on first install. This would make the initial set up much easier :) -
@lucas_nz said in I made a WireGuard package for pfSense:
Thanks for your work on this @Ascrod !! I've just set it up and working nicely. I also had the DNS issue after reboot. I suspect it is because the wireguard interface IP address is not set when the DNS resolver is started. pfSense's Unbound defaults to only responding to internal subnets. See this setting;
I suspect adding the wiregaurd subnet on the Access list tab of the DNS resolver will work as a acceptable workaround (haven't tried this yet).Hi,
I tired your suggestion of adding the wireguard subnet in the dnsresolver access list. RebootEd, but still had no dns until I restarted the service.
I also thought and tried of assigning a static Ip to the wireguard interface under the interface assignment page to see if that made any difference. Nope. -
thanks @alirz. Good to know. Hmm - I wonder what the issue is then??
-
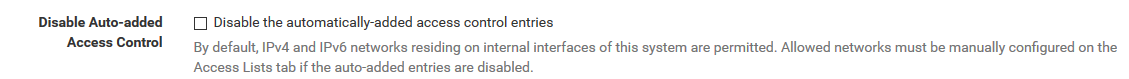
@alirz - hmm so, in the resolver config, I tried ticking the disable auto-added access control tick box and adding all RFC1918 (private) IP address ranges to the access tab then rebooted. This seemed to "fix" the DNS resolution issue. But My VPN firewall rule stopped working (it literally set to allow all IPv4). Editing the rule, and reapplying seemed to fix things. I wonder if this is still the same issue as the DNS issue, just another way of it occurring?
Following the rabbit down the hole (suspecting something funny happening with the interface), I tried adding a floating rule with my wiregaurd subnet as the source and anything as the destination. Rebooted (with the above DNS hack in place), and I have a working solution (sort of)... But it doesn't seem to source NAT my traffic out my WAN interface
 . I don't know if that helps us debug the issue or not, but I'm hopeful it points us in the right direction
. I don't know if that helps us debug the issue or not, but I'm hopeful it points us in the right direction 
-
@lucas_nz how do know that it doesn’t source not your traffic?
For me I’m only using a startup script to restart my dns after a 30 second delay after rebooting. That seems to fix the issue for me with no other hacks in place. -
@alirz, I could access LAN based resources but nothing on the internet and I see lots of TCP:S in the firewall log. I guess that isn't 100% confirmation that it's not NATing it, but it is a logical explanation given the lack of response from non-local IP ranges.
I just retested, I had both the floating rule and the VPN on in place, as soon as I disabled the floating one, everything sprung to life. In fact, as soon as I seem to commit any change, everything seems to come to life.