How to create IPv6 firewall rules?
-
@Bob-Dig said in How to create IPv6 firewall rules?:
One last thing, you can use Static Mappings with the DHCPv6 Server & RA to create firewall rules for hostnames, like with ipv4, so at least incoming firewall rules will work just fine using aliases, even with dynamic IPv6-address-prefixes on that interface.
I'll look into that. Thanks.
But does this help creating a default outbound rule? Basically most of my VLANs have a rule stating “allow all outgoing traffic to the internet but not other vlans” (as mentioned in the OP). For that I use an alias “internal_nets”.
I fail to see how static mappings would help creating such a rule. Is there another approach creating such a rule? I need to allow outgoing traffic somehow.
-
@zjgn Have you tried something like that (for every vlan, probalbly a lot of work)?
Also, I am guessing here, had no demand for that myself and haven't tested it.
-
And if you want to go to the extreme, you could deploy private IPv6-addresses and then use NPt, which works flawlessly.

(Edit: But not with a dynamic prefix. )
) -
@Bob-Dig said in How to create IPv6 firewall rules?:
@zjgn Have you tried something like that (for every vlan, probalbly a lot of work)?
I just tried, and a test rule seems to work. That would be very verbose, though. But it's a solution after all.
The big question is if the NET-based rules are automatically updated when the prefix changes? Otherwise the rules invalidate themselves after a short while.
If this works, I could at least get outgoing traffic flowing. That doesn't solve creating rules for individual hosts, though. But it's a step forward, thanks.
-
@Bob-Dig said in How to create IPv6 firewall rules?:
And if you want to go to the extreme, you could deploy private IPv6-addresses and then use NPt, which works flawlessly.
NPt is basically NAT, right? If so: Nope. Just no.
That's why I started looking into IPv6 in the first place. I want to get rid of NAT.
Regarding extreme: I just want a simple IPv6 config for my home network. A few vlans, voip/sip, web server dmz, guest vlan, etc. Nothing fancy. Basic standard stuff, I suppose. But apparently it's not so simple to implement in pfsense.
Thanks for the quick responses so far.
-
You understand that pfsense creates its own aliases for any network its attached to be it IPv4 or IPv6.. Just the name of that network, ie LAN Net, or VLAN Net, etc. etc..
So you can just use those in your rules..
-
@johnpoz Thanks for confirming.
-
@Bob-Dig said in How to create IPv6 firewall rules?:
Unless you want to block connections from that host.
Then you'd have to block every address for the prefix. While you know the consistent address, the privacy addresses can be anywhere with the 18.4 billion, billion addresses a /64 provides. The only way around this would be to filter on MAC addresses, which pfSense doesn't do.
In the end, I created multiple interfaces to get back control, one of them has no IPv6 at all. If your gear supports vlans, you can go with that, but mine didn't.
What is it you're trying to do?
-
@johnpoz said in How to create IPv6 firewall rules?:
So you can just use those in your rules..
But you can't use these in an alias and stack them, right?
-
@JKnott said in How to create IPv6 firewall rules?:
@Bob-Dig said in How to create IPv6 firewall rules?:
Unless you want to block connections from that host.
Then you'd have to block every address for the prefix. While you know the consistent address, the privacy addresses can be anywhere with the 18.4 billion, billion addresses a /64 provides. The only way around this would be to filter on MAC addresses, which pfSense doesn't do.
Or you can disable privacy extensions on that host. My ubunt servers don't use it in the beginning.
In the end, I created multiple interfaces to get back control, one of them has no IPv6 at all. If your gear supports vlans, you can go with that, but mine didn't.
What is it you're trying to do?
Getting back control is what I did. Some has to do with using the vpn-clients and defeat any leaks.
-
@Bob-Dig said in How to create IPv6 firewall rules?:
But you can't use these in an alias and stack them, right?
No AFAIK you can not stack them... Or join them into a parent alias sort of thing..
Just create distinct rules would be one option... The whole nonsense that is dynamic space is the only reason this is an issue.. Or you could just create the rules with whatever blocks of space you wanted. I have a /48 from HE, so my IPv6 address space never changes.. Had that same space for like 10+ years now..
-
@johnpoz said in How to create IPv6 firewall rules?:
@Bob-Dig said in How to create IPv6 firewall rules?:
But you can't use these in an alias and stack them, right?
No AFAIK you can not stack them... Or join them into a parent alias sort of thing..
That's unfortunate. It would make for much cleaner rules and be quicker to implement if there are many VLANs.
-
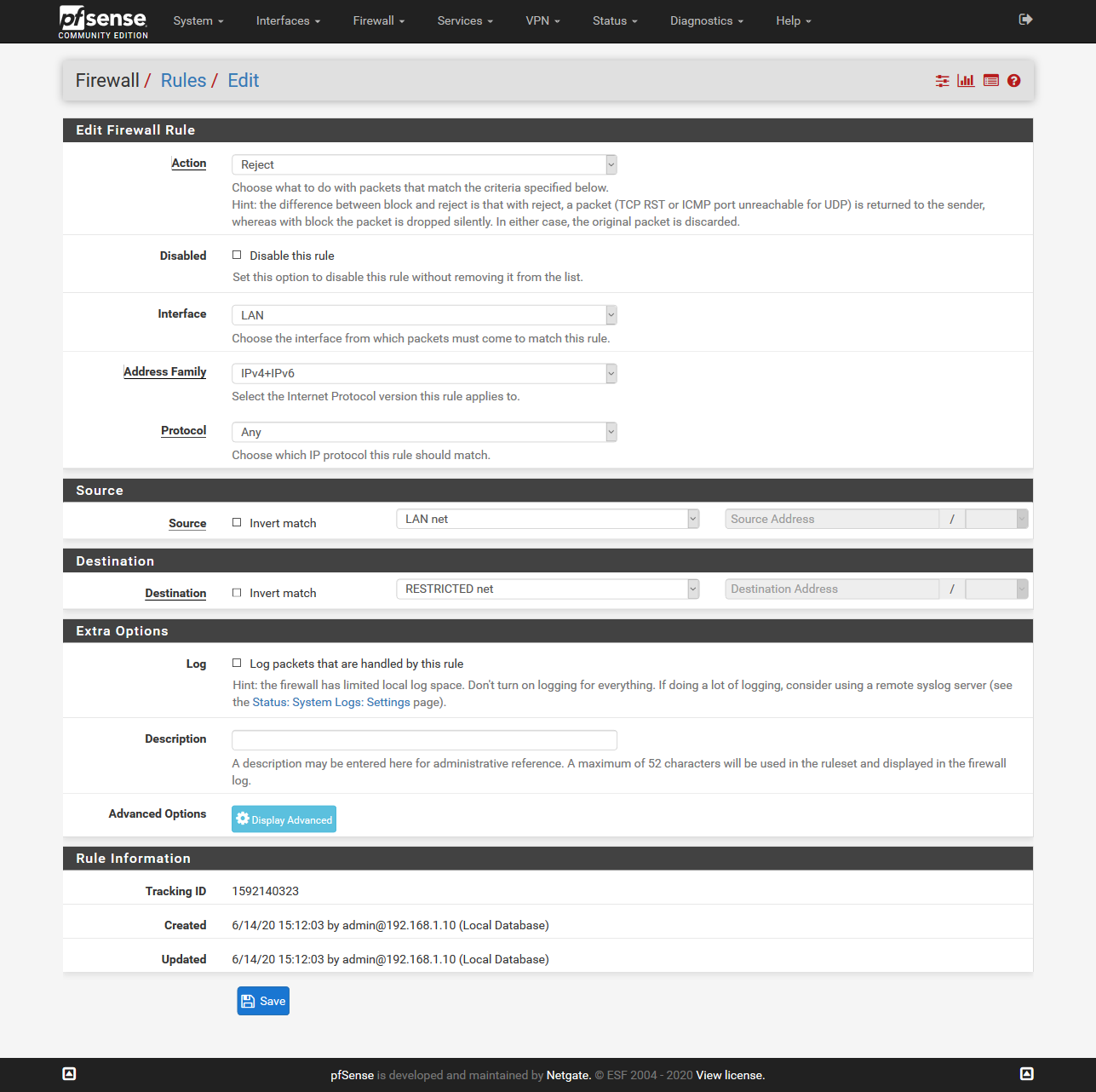
@zjgn I am just thinking about that: if the VLANs are more like DMZs, you could create one block rule for every VLAN (source = *, destination = vlan(x)) and then deploy those rules on all the vlans by using Interface Groups or floating rules. It should have no impact if the connection is on the same VLAN anyway.
Just some, maybe wrong, thoughts.
-
I have been trying out a lot with dynamic IPv6 and my conclusion was not to use IPv6 for internal communication for now (only for Internet communication), and only use IPv6 for one WAN of my Dual-WAN setup, there are just too many open topics for regarding dynamic IPv6 in pfSense. I currently mainly waiting for https://redmine.pfsense.org/issues/4881 and https://redmine.pfsense.org/issues/6880. Maybe also https://redmine.pfsense.org/issues/9536 and https://redmine.pfsense.org/issues/6626.
To prevent communication between my VLANs, I have basically done what @Bob-Dig suggested above, i.e. with block rules using "xxx net", as combined IPv4+IPv6 rules, so it blocks at least both.
My target scenario is going to be to use ULAs and (dynamic) NPt to be able use use fail-over between the WANs, but it also makes internal communication easier because the prefix stays static. In my opinion, NPt should not be directly compared with NAT in IPv4, because it works very very differently as the whole prefix is just translated 1:1 so you can still communicate directly without any port mapping or keeping any state. For incoming traffic the destination prefix is just mapped to the internal one and for outgoing traffic the source prefix is just mapped to the public one, but the host part, ports etc. stay the same.
For "DMZ stuff" and also for IPSec VPN from my iPhone, I have separate public IPv4 addresses and an IPv6 prefix independently of my ISPs from a dedicated "static IP provider", connected via OpenVPN, because this is crappy anyway with dynamic addresses.
-
Thanks for your input. Those bug reports confirm that IPv6 in pfSense isn't really usable as of now (at least on domestic connections), which is a great shame.
Those bug reports are many years old. So there doesn't really seem to be much interest in getting IPv6 to work for a wider audience.
-
@zjgn I've heard, it is in the works, but no ETA.
-
If the ISP is not respecting the Do not allow PD/Address release setting, how is that pfSense's fault?
Re. that 9536 problem. It mentions passing other blocks to another router. I have done that here, so it does work.
I use that setting and my prefix is solid. Prior to that setting being available, my prefix changed easily too.
-
@JKnott "Do not allow PD/Address release" is nothing the ISP can respect because it doesn't even notice. This setting just means that pfSense does not send a release: "dhcp6c will send a release to the ISP on exit, some ISPs then release the allocated address or prefix. This option prevents that signal ever being sent" There is no such thing as "prevent release" in DHCPv6, the DHCP server may assign new prefixes/addresses basically whenever it (or its administrator) likes, see https://tools.ietf.org/html/rfc3315#section-19. So even without reconnecting you might get a new IP addresses/prefixes, although ISPs usually don't do that.
As the name DHCP Dynamic Host Configuration Protocol already says, it's dynamic. That means you have to be able to react to these changes, otherwise you should not use DHCP to assign/get IP addresses/prefixes. Therefore all settings that cannot deal with this like the issues I mentioned above are not suitable for use with DHCP. If you do it and configure your dynamic prefix statically there, it will break sooner or later, even if the "Do not allow PD/Address release" workaround works for some time.
-
Well, that setting definitely works for me. When I first started using pfSense, that option was not available and my prefix frequently changed, for something as little as disconnecting/reconnecting the WAN cable. Then, when it was added, my prefix became solid. I can disconnect/reconnect that cable all I want, reboot, etc. and I still keep my prefix. The one and only occasion when it didn't work was when I had that problem with my ISP, about 1.5 years ago, where they weren't providing a valid prefix. Here's a packet capture from when I had that problem. It clearly shows an error and when they fixed that, IPv6 worked again and my prefix has been steady since then.
User Datagram Protocol, Src Port: 547, Dst Port: 546
DHCPv6
Message type: Reply (7)
Transaction ID: 0x18a8e9
Client Identifier
Option: Client Identifier (1)
Length: 14
Value: 0001000123eb5e12001617a7f2d3
DUID: 0001000123eb5e12001617a7f2d3
DUID Type: link-layer address plus time (1)
Hardware type: Ethernet (1)
DUID Time: Feb 4, 2019 15:33:22.000000000 EST
Link-layer address: 00:16:17:a7:f2:d3
Server Identifier
Option: Server Identifier (2)
Length: 14
Value: 00010001159bb6e50021285fd2b7
DUID: 00010001159bb6e50021285fd2b7
DUID Type: link-layer address plus time (1)
Hardware type: Ethernet (1)
DUID Time: Jun 27, 2011 17:47:17.000000000 EDT
Link-layer address: 00:21:28:5f:d2:b7
Identity Association for Prefix Delegation
Option: Identity Association for Prefix Delegation (25)
Length: 72
Value: 000000000000000000000000000d003800064e6f20707265...
IAID: 00000000
T1: 0
T2: 0
Status code
Option: Status code (13)
Length: 56
Value: 00064e6f2070726566697820617661696c61626c65206f6e...
Status Code: NoPrefixAvail (6)
Status Message: No prefix available on Link
'CMTS89.WLFDLE-BNDL1-GRP3'
DNS recursive name server
Option: DNS recursive name server (23)
Length: 32
Value: 2607f7980018001000000640712552042607f79800180010...
1 DNS server address: 2607:f798:18:10:0:640:7125:5204
2 DNS server address: 2607:f798:18:10:0:640:7125:5198One of the reasons for the DUID is to keep the prefix associated with a device, such as a firewall running pfSense.
-
@JKnott, yes I understand that, it definitely improves the situation in some cases, specifically in these cases where the ISP under normal circumstances only assigns new prefixes after the client explicitly sent a release. So for these ISPs you will only get new IP addresses very rarely if you never send a release (which is what this setting does), e.g. when their DHCP server crashes or when they are reorganizing their address space. But you are more or less just lucky when your ISPs implementation behaves like that. Many ISPs (like mine, too) just assign new IP addresses with each reconnection for whatever reason (implementation reasons, save resources, keep static IP addresses as a USP for the more expensive business tariffs, ...) and in my understanding this is perfectly fine from DHCP perspective.